2271:'s AES encryption. The attack required over 200 million chosen plaintexts. The custom server was designed to give out as much timing information as possible (the server reports back the number of machine cycles taken by the encryption operation). However, as Bernstein pointed out, "reducing the precision of the server's timestamps, or eliminating them from the server's responses, does not stop the attack: the client simply uses round-trip timings based on its local clock, and compensates for the increased noise by averaging over a larger number of samples."
29:
5527:
2367:) validated at the same time. Therefore, it is rare to find cryptographic modules that are uniquely FIPS 197 validated and NIST itself does not generally take the time to list FIPS 197 validated modules separately on its public web site. Instead, FIPS 197 validation is typically just listed as an "FIPS approved: AES" notation (with a specific FIPS 197 certificate number) in the current list of FIPS 140 validated cryptographic modules.
1988:
1117:
1074:
769:
1507:
2375:(e.g., well over $ 30,000 US) and does not include the time it takes to write, test, document and prepare a module for validation. After validation, modules must be re-submitted and re-evaluated if they are changed in any way. This can vary from simple paperwork updates if the security functionality did not change to a more substantial set of re-testing if the security functionality was impacted by the change.
1192:
632:
2118:. A break can thus include results that are infeasible with current technology. Despite being impractical, theoretical breaks can sometimes provide insight into vulnerability patterns. The largest successful publicly known brute-force attack against a widely implemented block-cipher encryption algorithm was against a 64-bit
2203:, is against AES-256 that uses only two related keys and 2 time to recover the complete 256-bit key of a 9-round version, or 2 time for a 10-round version with a stronger type of related subkey attack, or 2 time for an 11-round version. 256-bit AES uses 14 rounds, so these attacks are not effective against full AES.
2349:(SBU) or above. From NSTISSP #11, National Policy Governing the Acquisition of Information Assurance: "Encryption products for protecting classified information will be certified by NSA, and encryption products intended for protecting sensitive information will be certified in accordance with NIST FIPS 140-2."
2230:
This is a very small gain, as a 126-bit key (instead of 128 bits) would still take billions of years to brute force on current and foreseeable hardware. Also, the authors calculate the best attack using their technique on AES with a 128-bit key requires storing 2 bits of data. That works out to about
2297:
In March 2016, Ashokkumar C., Ravi
Prakash Giri and Bernard Menezes presented a side-channel attack on AES implementations that can recover the complete 128-bit AES key in just 6–7 blocks of plaintext/ciphertext, which is a substantial improvement over previous works that require between 100 and a
2129:
The key space increases by a factor of 2 for each additional bit of key length, and if every possible value of the key is equiprobable; this translates into a doubling of the average brute-force key search time with every additional bit of key length. This implies that the effort of a brute-force
2079:
The design and strength of all key lengths of the AES algorithm (i.e., 128, 192 and 256) are sufficient to protect classified information up to the SECRET level. TOP SECRET information will require use of either the 192 or 256 key lengths. The implementation of AES in products intended to protect
2374:
FIPS 140-2 validation is challenging to achieve both technically and fiscally. There is a standardized battery of tests as well as an element of source code review that must be passed over a period of a few weeks. The cost to perform these tests through an approved laboratory can be significant
2226:
and is faster than brute force by a factor of about four. It requires 2 operations to recover an AES-128 key. For AES-192 and AES-256, 2 and 2 operations are needed, respectively. This result has been further improved to 2 for AES-128, 2 for AES-192 and 2 for AES-256, which are the current best
2370:
The
Cryptographic Algorithm Validation Program (CAVP) allows for independent validation of the correct implementation of the AES algorithm. Successful validation results in being listed on the NIST validations page. This testing is a pre-requisite for the FIPS 140-2 module validation. However,
2293:
In
November 2010 Endre Bangerter, David Gullasch and Stephan Krenn published a paper which described a practical approach to a "near real time" recovery of secret keys from AES-128 without the need for either cipher text or plaintext. The approach also works on AES-128 implementations that use
2214:
against a reduced 8-round version of AES-128 was released as a preprint. This known-key distinguishing attack is an improvement of the rebound, or the start-from-the-middle attack, against AES-like permutations, which view two consecutive rounds of permutation as the application of a so-called
2180:, and Ivica Nikolić, with a complexity of 2 for one out of every 2 keys. However, related-key attacks are not of concern in any properly designed cryptographic protocol, as a properly designed protocol (i.e., implementational software) will take care not to allow related keys, essentially by
2039:
step by transforming them into a sequence of table lookups. This requires four 256-entry 32-bit tables (together occupying 4096 bytes). A round can then be performed with 16 table lookup operations and 12 32-bit exclusive-or operations, followed by four 32-bit exclusive-or operations in the
2260:, and thus are not related to cipher security as defined in the classical context, but are important in practice. They attack implementations of the cipher on hardware or software systems that inadvertently leak data. There are several such known attacks on various implementations of AES.
2371:
successful CAVP validation in no way implies that the cryptographic module implementing the algorithm is secure. A cryptographic module lacking FIPS 140-2 validation or specific approval by the NSA is not deemed secure by the US Government and cannot be used to protect government data.
2282:
partition encryption function. One attack was able to obtain an entire AES key after only 800 operations triggering encryptions, in a total of 65 milliseconds. This attack requires the attacker to be able to run programs on the same system or platform that is performing AES.
1502:{\displaystyle {\begin{bmatrix}b_{0,j}\\b_{1,j}\\b_{2,j}\\b_{3,j}\end{bmatrix}}={\begin{bmatrix}2&3&1&1\\1&2&3&1\\1&1&2&3\\3&1&1&2\end{bmatrix}}{\begin{bmatrix}a_{0,j}\\a_{1,j}\\a_{2,j}\\a_{3,j}\end{bmatrix}}\qquad 0\leq j\leq 3}
408:
2574:
bytes. For a 256-bit block, the first row is unchanged and the shifting for the second, third and fourth row is 1 byte, 3 bytes and 4 bytes respectively—this change only applies for the
Rijndael cipher when used with a 256-bit block, as AES does not use 256-bit
2294:
compression tables, such as OpenSSL. Like some earlier attacks, this one requires the ability to run unprivileged code on the system performing the AES encryption, which may be achieved by malware infection far more easily than commandeering the root account.
2231:
38 trillion terabytes of data, which was more than all the data stored on all the computers on the planet in 2016. A paper in 2015 later improved the space complexity to 2 bits, which is 9007 terabytes (while still keeping a time complexity of 2).
189:
in 2009. This attack is against AES-256 that uses only two related keys and 2 time to recover the complete 256-bit key of a 9-round version, or 2 time for a 10-round version with a stronger type of related subkey attack, or 2 time for an 11-round
1093:. For AES, the first row is left unchanged. Each byte of the second row is shifted one to the left. Similarly, the third and fourth rows are shifted by offsets of two and three respectively. In this way, each column of the output state of the
2321:. AES-192 and AES-128 are not considered quantum resistant due to their smaller key sizes. AES-192 has a strength of 96 bits against quantum attacks and AES-128 has 64 bits of strength against quantum attacks, making them both insecure.
2152:
During the AES selection process, developers of competing algorithms wrote of
Rijndael's algorithm "we are concerned about use ... in security-critical applications." In October 2000, however, at the end of the AES selection process,
1875:
270:
PUB 197 (FIPS 197) on
November 26, 2001. This announcement followed a five-year standardization process in which fifteen competing designs were presented and evaluated, before the Rijndael cipher was selected as the most suitable.
661:
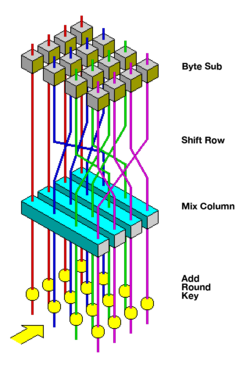
Each round consists of several processing steps, including one that depends on the encryption key itself. A set of reverse rounds are applied to transform ciphertext back into the original plaintext using the same encryption key.
2071:(NSA) reviewed all the AES finalists, including Rijndael, and stated that all of them were secure enough for U.S. Government non-classified data. In June 2003, the U.S. Government announced that AES could be used to protect
248:. Rijndael is a family of ciphers with different key and block sizes. For AES, NIST selected three members of the Rijndael family, each with a block size of 128 bits, but three different key lengths: 128, 192 and 256 bits.
1097:
step is composed of bytes from each column of the input state. The importance of this step is to avoid the columns being encrypted independently, in which case AES would degenerate into four independent block ciphers.
2145:, purporting to show a weakness in the AES algorithm, partially due to the low complexity of its nonlinear components. Since then, other papers have shown that the attack, as originally presented, is unworkable; see
2161:, wrote that while he thought successful academic attacks on Rijndael would be developed someday, he "did not believe that anyone will ever discover an attack that will allow someone to read Rijndael traffic."
282:
1051:
2206:
The practicality of these attacks with stronger related keys has been criticized, for instance, by the paper on chosen-key-relations-in-the-middle attacks on AES-128 authored by
Vincent Rijmen in 2010.
2215:
Super-S-box. It works on the 8-round version of AES-128, with a time complexity of 2, and a memory complexity of 2. 128-bit AES uses 10 rounds, so this attack is not effective against full AES-128.
627:{\displaystyle {\begin{bmatrix}b_{0}&b_{4}&b_{8}&b_{12}\\b_{1}&b_{5}&b_{9}&b_{13}\\b_{2}&b_{6}&b_{10}&b_{14}\\b_{3}&b_{7}&b_{11}&b_{15}\end{bmatrix}}}
4010:
Advances in
Cryptology – ASIACRYPT 2002: 8th International Conference on the Theory and Application of Cryptology and Information Security, Queenstown, New Zealand, December 1–5, 2002, Proceedings
2172:
was discovered that exploits the simplicity of AES's key schedule and has a complexity of 2. In
December 2009 it was improved to 2. This is a follow-up to an attack discovered earlier in 2009 by
2130:
search increases exponentially with key length. Key length in itself does not imply security against attacks, since there are ciphers with very long keys that have been found to be vulnerable.
2359:
Although NIST publication 197 ("FIPS 197") is the unique document that covers the AES algorithm, vendors typically approach the CMVP under FIPS 140 and ask to have several algorithms (such as
1754:
1970:
1697:
1655:
1920:
975:
1604:
908:, known to have good non-linearity properties. To avoid attacks based on simple algebraic properties, the S-box is constructed by combining the inverse function with an invertible
3466:
2391:
High speed and low RAM requirements were some of the criteria of the AES selection process. As the chosen algorithm, AES performed well on a wide variety of hardware, from 8-bit
4148:– AES deeply explained and animated using Flash (by Enrique Zabala / University ORT / Montevideo / Uruguay). This animation (in English, Spanish, and German) is also part of
2849:
2484:
Block sizes of 128, 160, 192, 224, and 256 bits are supported by the
Rijndael algorithm for each key size, but only the 128-bit block size is specified in the AES standard.
352:
is specified with block and key sizes that may be any multiple of 32 bits, with a minimum of 128 and a maximum of 256 bits. Most AES calculations are done in a particular
883:
3758:
2044:
step. Alternatively, the table lookup operation can be performed with a single 256-entry 32-bit table (occupying 1024 bytes) followed by circular rotation operations.
2475:
Key sizes of 128, 160, 192, 224, and 256 bits are supported by the Rijndael algorithm, but only the 128, 192, and 256-bit key sizes are specified in the AES standard.
834:
2890:
1539:
1151:
2572:
2546:
5507:
5337:
2245:
At present, there is no known practical attack that would allow someone without knowledge of the key to read data encrypted by AES when correctly implemented.
1759:
2383:
Test vectors are a set of known ciphers for a given input and key. NIST distributes the reference of AES test vectors as AES Known Answer Test (KAT) Vectors.
2528:
Rijndael variants with a larger block size have slightly different offsets. For blocks of sizes 128 bits and 192 bits, the shifting pattern is the same. Row
2864:
1081:
step, bytes in each row of the state are shifted cyclically to the left. The number of places each byte is shifted differs incrementally for each row.
2749:
2015:; each subkey is the same size as the state. The subkey is added by combining of the state with the corresponding byte of the subkey using bitwise
3521:
3370:
2614:
1514:
Matrix multiplication is composed of multiplication and addition of the entries. Entries are bytes treated as coefficients of polynomial of order
1184:
During this operation, each column is transformed using a fixed matrix (matrix left-multiplied by column gives new value of column in the state):
3886:
2196:
4135:
3986:
3431:
2691:
3042:
2999:
2457:
2334:
275:
222:
5175:
3085:
2993:"National Policy on the Use of the Advanced Encryption Standard (AES) to Protect National Security Systems and National Security Information"
2278:
and Eran Tromer presented a paper demonstrating several cache-timing attacks against the implementations in AES found in OpenSSL and Linux's
2588:
5110:
4191:
2816:
2790:
2402:, AES encryption requires 18 clock cycles per byte (cpb), equivalent to a throughput of about 11 MiB/s for a 200 MHz processor.
3728:
3562:
3034:
3458:
279:
2841:
2239:
980:
4937:
4293:
267:
252:
2222:
on full AES were by Andrey Bogdanov, Dmitry Khovratovich, and Christian Rechberger, and were published in 2011. The attack is a
722: – a linear mixing operation which operates on the columns of the state, combining the four bytes in each column.
3948:
716: – a transposition step where the last three rows of the state are shifted cyclically a certain number of steps.
3830:
3745:
2904:
Bruce Schneier; John Kelsey; Doug Whiting; David Wagner; Chris Hall; Niels Ferguson; Tadayoshi Kohno; et al. (May 2000).
1169:
function takes four bytes as input and outputs four bytes, where each input byte affects all four output bytes. Together with
5560:
4927:
4421:
4060:
4039:
4018:
3915:
3865:
3693:
3414:
3253:
2950:
2338:
2087:
By 2006, the best known attacks were on 7 rounds for 128-bit keys, 8 rounds for 192-bit keys, and 9 rounds for 256-bit keys.
1618:(overflow must be corrected by subtraction of generating polynomial). These are special cases of the usual multiplication in
1061:) is used, which requires first taking the inverse of the affine transformation and then finding the multiplicative inverse.
5090:
5064:
4932:
4828:
4155:
3219:
3137:
2494:
2298:
million encryptions. The proposed attack requires standard user privilege and key-retrieval algorithms run under a minute.
329:
245:
144:
97:
4067:
2886:
3655:
3059:
2970:
2912:
2317:
resistant, as it has similar quantum resistance to AES-128's resistance against traditional, non-quantum, attacks at 128
286:
4905:
4145:
3166:
2181:
2080:
national security systems and/or information must be reviewed and certified by NSA prior to their acquisition and use.
5168:
4087:
Cryptography – 256 bit Ciphers: Reference source code and submissions to international cryptographic designs contests
3495:
639:
The key size used for an AES cipher specifies the number of transformation rounds that convert the input, called the
1702:
5074:
4184:
2872:
4953:
3802:
3634:
3598:
3322:
2211:
1936:
1663:
1621:
5386:
5317:
5131:
2887:"ISO/IEC 18033-3: Information technology – Security techniques – Encryption algorithms – Part 3: Block ciphers"
2441:
3111:
2113:
285:
standard. AES became effective as a U.S. federal government standard on May 26, 2002, after approval by U.S.
3348:
3274:
2717:
2658:
2027:
On systems with 32-bit or larger words, it is possible to speed up execution of this cipher by combining the
179:. For biclique attacks on AES-192 and AES-256, the computational complexities of 2 and 2 respectively apply.
1884:
919:
5161:
2418:
1544:
292:. AES is available in many different encryption packages, and is the first (and only) publicly accessible
5502:
5457:
5260:
5017:
4177:
2742:
2287:
3972:
3940:
Schneier, Bruce; Kelsey, John; Whiting, Doug; Wagner, David; Hall, Chris; Ferguson, Niels (1999-02-01).
2235:
5381:
5034:
4944:
4922:
4235:
3517:
3377:
3022:
2967:"byte-oriented-aes – A public domain byte-oriented implementation of AES in C – Google Project Hosting"
2621:
2346:
4124:
3890:
2929:
Bertoni, Guido; Breveglieri, Luca; Fragneto, Pasqualina; MacChetti, Marco; Marchesin, Stefano (2003).
5497:
5039:
4895:
4848:
4323:
3435:
3240:. Lecture Notes in Computer Science. Vol. 5677. Springer Berlin / Heidelberg. pp. 231–249.
2683:
2451:
1090:
337:
131:
2992:
2345:
is required by the United States Government for encryption of all data that has a classification of
2146:
5487:
5477:
5332:
5105:
4987:
4862:
4231:
3183:
3050:
2068:
1178:
297:
256:
109:
5482:
5472:
5265:
5225:
5218:
5203:
5198:
5044:
4833:
4204:
2585:
353:
332:, and is efficient in both software and hardware. Unlike its predecessor DES, AES does not use a
260:
4094:
3081:
2779:
2084:
AES has 10 rounds for 128-bit keys, 12 rounds for 192-bit keys, and 14 rounds for 256-bit keys.
1089:
step operates on the rows of the state; it cyclically shifts the bytes in each row by a certain
846:
5555:
5270:
5213:
5136:
5012:
5007:
4959:
3717:
3178:
2823:
2072:
2007:
step, the subkey is combined with the state. For each round, a subkey is derived from the main
898:
301:
4004:
5565:
5530:
5376:
5322:
5126:
4949:
4808:
4386:
4050:
2012:
1162:
909:
806:
183:
can break AES-256 and AES-192 with complexities 2 and 2 in both time and data, respectively.
4029:
3543:
2519:
Large-block variants of Rijndael use an array with additional columns, but always four rows.
5492:
5416:
5029:
4912:
4838:
4521:
4501:
3269:
Alex Biryukov; Orr Dunkelman; Nathan Keller; Dmitry Khovratovich; Adi Shamir (2009-08-19).
2712:
Alex Biryukov; Orr Dunkelman; Nathan Keller; Dmitry Khovratovich; Adi Shamir (2009-08-19).
1517:
151:
4118:
3268:
2789:. United States National Institute of Standards and Technology (NIST). November 26, 2001.
2711:
2421:
CPU, AES encryption using AES-NI takes about 1.3 cpb for AES-128 and 1.8 cpb for AES-256.
1127:
8:
5245:
4992:
4969:
4288:
2584:
The AES Known Answer Test (KAT) Vectors are available in Zip format within the NIST site
2551:
2430:
2414:
2302:
2264:
2253:
2219:
2177:
2165:
1973:
1870:{\displaystyle c(z)={03}_{16}\cdot z^{3}+{01}_{16}\cdot z^{2}+{01}_{16}\cdot z+{02}_{16}}
1111:
687: – each byte of the state is combined with a byte of the round key using
5361:
5345:
5287:
4977:
4885:
4597:
4526:
4496:
4441:
3831:"NSTISSP No. 11, Revised Fact Sheet, National Information Assurance Acquisition Policy"
3699:
3162:
2531:
2169:
2133:
AES has a fairly simple algebraic framework. In 2002, a theoretical attack, named the "
2100:
2008:
776:
step, each byte in the state is replaced with its entry in a fixed 8-bit lookup table,
360:
180:
170:
83:
3397:
Biaoshuai Tao & Hongjun Wu (2015). "Improving the Biclique Cryptanalysis of AES".
3368:
3171:
Proceedings of Selected Areas in Cryptography, 2001, Lecture Notes in Computer Science
2341:(CSE) of the Government of Canada. The use of cryptographic modules validated to NIST
893:
array is simply the plaintext/input. This operation provides the non-linearity in the
5421:
5411:
5277:
4697:
4396:
4356:
4351:
4318:
4278:
4226:
4056:
4035:
4014:
3753:
3689:
3410:
3249:
2946:
2314:
175:
For AES-128, the key can be recovered with a computational complexity of 2 using the
3941:
3782:
Bonnetain, Xavier; Naya-Plasencia, María; Schrottenloher, André (December 6, 2019).
3703:
2286:
In December 2009 an attack on some hardware implementations was published that used
5356:
5208:
5069:
4964:
4843:
4702:
4582:
4551:
4245:
4105:
4082:
3837:
3681:
3554:
3402:
3271:"Key Recovery Attacks of Practical Complexity on AES Variants With Up To 10 Rounds"
3241:
3236:
Nikolić, Ivica (2009). "Distinguisher and Related-Key Attack on the Full AES-256".
2938:
2714:"Key Recovery Attacks of Practical Complexity on AES Variants With Up To 10 Rounds"
2318:
2138:
1995:
step, each byte of the state is combined with a byte of the round subkey using the
886:
675:
3861:
3783:
2905:
1161:
step, the four bytes of each column of the state are combined using an invertible
4916:
4900:
4889:
4823:
4782:
4747:
4677:
4657:
4531:
4411:
4406:
4361:
3585:
3245:
3223:
3174:
3038:
2903:
2592:
2446:
2356:
validated cryptographic modules in unclassified applications of its departments.
2223:
2187:
Another attack was blogged by Bruce Schneier on July 30, 2009, and released as a
2123:
333:
176:
87:
79:
69:
3406:
3216:
3133:
2267:
announced a cache-timing attack that he used to break a custom server that used
2164:
Until May 2009, the only successful published attacks against the full AES were
28:
5431:
5351:
5307:
5250:
5235:
5054:
5002:
4813:
4798:
4737:
4732:
4617:
4366:
3919:
3158:
3030:
2154:
2142:
763:
707:
678:. AES requires a separate 128-bit round key block for each round plus one more.
241:
213:
51:
3651:
3055:
2966:
5549:
5512:
5467:
5426:
5406:
5297:
5255:
5230:
5049:
4997:
4876:
4858:
4647:
4622:
4612:
4436:
4426:
4273:
3675:
2942:
2930:
2192:
2173:
2096:
162:
3188:
3157:
263:, meaning the same key is used for both encrypting and decrypting the data.
5462:
5302:
5292:
5282:
5240:
5184:
4982:
4803:
4767:
4632:
4511:
4466:
4298:
4250:
4200:
3862:"NIST.gov – Computer Security Division – Computer Security Resource Center"
3685:
3026:
2016:
1996:
1931:
1607:
903:
289:
229:
4110:
3621:
3491:
1541:. Addition is simply XOR. Multiplication is modulo irreducible polynomial
706:
substitution step where each byte is replaced with another according to a
5441:
4592:
4587:
4471:
2869:
Journal of Research of the National Institute of Standards and Technology
2399:
1878:
913:
688:
237:
47:
3369:
Andrey Bogdanov; Dmitry Khovratovich & Christian Rechberger (2011).
2110:
i.e., performing one trial decryption for each possible key in sequence
259:(DES), which was published in 1977. The algorithm described by AES is a
169:
Attacks have been published that are computationally faster than a full
5401:
5371:
5366:
5327:
5024:
4742:
4682:
4566:
4561:
4506:
4376:
4239:
3558:
3193:
2937:. Lecture Notes in Computer Science. Vol. 2523. pp. 159–171.
2406:
2392:
2360:
2342:
2275:
2238:, the NSA is doing research on whether a cryptographic attack based on
2200:
2134:
1927:
703:
674: – round keys are derived from the cipher key using the
644:
218:
4005:"Cryptanalysis of Block Ciphers with Overdefined Systems of Equations"
3624:"Cache Games – Bringing Access-Based Cache Attacks on AES to Practice"
3623:
3587:
3341:"Super-Sbox Cryptanalysis: Improved Attacks for AES-like permutations"
3311:
2688:
Schneier on Security, A blog covering security and security technology
5391:
4757:
4752:
4642:
4556:
4451:
4431:
4052:
Understanding Cryptography: A Textbook for Students and Practitioners
4008:
3781:
3401:. Lecture Notes in Computer Science. Vol. 9144. pp. 39–56.
3056:"Academic: Improved Cryptanalysis of Rijndael - Schneier on Security"
2410:
2257:
1124:
step, each column of the state is multiplied with a fixed polynomial
640:
4132:
Information technology – Security techniques – Encryption algorithms
2454:– hash function created by Vincent Rijmen and Paulo S. L. M. Barreto
1926:
step can also be viewed as a multiplication by the shown particular
5436:
5396:
5095:
5059:
4853:
4516:
4391:
4371:
4283:
4149:
3541:
3107:
2928:
2713:
2654:
2353:
2188:
1660:
In more general sense, each column is treated as a polynomial over
345:
186:
121:
101:
3678:
2016 IEEE European Symposium on Security and Privacy (EuroS&P)
3340:
3270:
1987:
912:. The S-box is also chosen to avoid any fixed points (and so is a
4762:
4712:
4672:
4662:
4607:
4602:
4446:
4255:
3987:"Intel ® Advanced Encryption Standard (AES) New Instructions Set"
2865:"NIST reports measurable success of Advanced Encryption Standard"
2268:
2158:
1116:
233:
3456:
3312:"Practical-Titled Attack on AES-128 Using Chosen-Text Relations"
1881:
equivalent of the binary representation of bit polynomials from
1073:
5312:
5100:
4722:
4717:
4652:
4637:
4627:
4572:
4546:
4541:
4536:
4416:
4401:
1606:. If processed bit by bit, then, after shifting, a conditional
894:
768:
304:
information when used in an NSA approved cryptographic module.
293:
105:
4031:
The Design of Rijndael: AES – The Advanced Encryption Standard
2931:"Efficient Software Implementation of AES on 32-Bit Platforms"
2814:
2047:
Using a byte-oriented approach, it is possible to combine the
312:
The Advanced Encryption Standard (AES) is defined in each of:
4818:
4777:
4727:
4707:
4692:
4481:
4461:
4381:
4346:
4152:(menu Indiv. Procedures → Visualization of Algorithms → AES).
3588:"A Diagonal Fault Attack on the Advanced Encryption Standard"
2748:. National Institute of Standards and Technology. p. 1.
2333:(CMVP) is operated jointly by the United States Government's
2305:, which protect against timing-related side-channel attacks.
1046:{\displaystyle S(a_{i,j})\oplus a_{i,j}\neq {\text{FF}}_{16}}
3622:
Endre Bangerter; David Gullasch & Stephan Krenn (2010).
266:
In the United States, AES was announced by the NIST as U.S.
4667:
4576:
4491:
4486:
4476:
4456:
4328:
4313:
3939:
3887:"Validated FIPS 140-1 and FIPS 140-2 Cryptographic Modules"
3586:
Dhiman Saha; Debdeep Mukhopadhyay; Dipanwita RoyChowdhury.
2655:"Related-key Cryptanalysis of the Full AES-192 and AES-256"
2364:
2330:
4134:(2nd ed.). ISO. 2010-12-15. ISO/IEC 18033-3:2010(E).
3676:
Ashokkumar C.; Ravi Prakash Giri; Bernard Menezes (2016).
3338:
2417:
extensions, throughput can be multiple GiB/s. On an Intel
1614:
should be performed if the shifted value is larger than FF
665:
4772:
4687:
4308:
4303:
2650:
Related-key Cryptanalysis of the Full AES-192 and AES-256
2119:
341:
3913:
2787:
Federal Information Processing Standards Publication 197
4119:
AES algorithm archive information – (old, unmaintained)
3396:
2935:
Cryptographic Hardware and Embedded Systems - CHES 2002
2736:
2734:
2184:
an attacker's means of selecting keys for relatedness.
173:, though none as of 2023 are computationally feasible.
5338:
Cryptographically secure pseudorandom number generator
3652:"Breaking AES-128 in realtime, no ciphertext required"
3542:
Dag Arne Osvik; Adi Shamir; Eran Tromer (2005-11-20).
3134:"AES News, Crypto-Gram Newsletter, September 15, 2002"
2191:
on August 3, 2009. This new attack, by Alex Biryukov,
1396:
1296:
1201:
417:
3457:
SPIEGEL ONLINE, Hamburg, Germany (28 December 2014).
2554:
2534:
2290:
and allows recovery of a key with a complexity of 2.
2114:
Cryptanalysis § Computational resources required
1939:
1887:
1762:
1705:
1666:
1624:
1547:
1520:
1195:
1130:
983:
922:
849:
809:
411:
4199:
4161:
4070:(companion web site contains online lectures on AES)
3544:"Cache Attacks and Countermeasures: the Case of AES"
2906:"The Twofish Team's Final Comments on AES Selection"
2815:
Joan Daemen and Vincent Rijmen (September 3, 1999).
2731:
2352:
The Government of Canada also recommends the use of
3486:
3484:
3297:
On Some Symmetric Lightweight Cryptographic Designs
2780:"Announcing the ADVANCED ENCRYPTION STANDARD (AES)"
1972:. This process is described further in the article
732:Final round (making 10, 12 or 14 rounds in total):
3718:"Are AES x86 Cache Timing Attacks Still Feasible?"
3151:
2566:
2540:
1964:
1914:
1869:
1748:
1691:
1649:
1598:
1533:
1501:
1145:
1045:
969:
877:
828:
626:
2168:on some specific implementations. In 2009, a new
5547:
4002:
3942:"Performance Comparisons of the AES submissions"
3551:The Cryptographer's Track at RSA Conference 2006
3481:
3429:
3299:. Dissertation, Lund University. pp. 38–39.
2677:
2675:
348:of 128, 192, or 256 bits. By contrast, Rijndael
316:FIPS PUB 197: Advanced Encryption Standard (AES)
3167:"A simple algebraic representation of Rijndael"
2741:Daemen, Joan; Rijmen, Vincent (March 9, 2003).
3309:
2681:
2458:List of free and open-source software packages
2335:National Institute of Standards and Technology
1749:{\displaystyle {01}_{16}\cdot z^{4}+{01}_{16}}
328:AES is based on a design principle known as a
244:, who submitted a proposal to NIST during the
223:National Institute of Standards and Technology
16:Standard for the encryption of electronic data
5169:
4185:
2990:
2839:
2672:
2022:
336:. AES is a variant of Rijndael, with a fixed
323:
185:Another attack was blogged and released as a
4027:
2740:
2227:results in key recovery attack against AES.
977:, and also any opposite fixed points, i.e.,
4003:Courtois, Nicolas; Pieprzyk, Josef (2003).
3825:
3823:
3746:"Securing the Enterprise with Intel AES-NI"
3459:"Inside the NSA's War on Internet Security"
3339:Henri Gilbert; Thomas Peyrin (2009-11-09).
2879:
221:of electronic data established by the U.S.
5176:
5162:
4192:
4178:
3916:"OpenSSL's Notes about FIPS certification"
3909:
3907:
3800:
3515:
3131:
3073:
2774:
2772:
2770:
2337:(NIST) Computer Security Division and the
1965:{\displaystyle \operatorname {GF} (2^{8})}
1877:. The coefficients are displayed in their
1692:{\displaystyle \operatorname {GF} (2^{8})}
1650:{\displaystyle \operatorname {GF} (2^{8})}
4109:
4048:
3182:
2842:"U.S. Selects a New Encryption Technique"
2808:
2157:, a developer of the competing algorithm
4158:– Same Animation as above made in HTML5.
4102:Federal Information Processing Standards
3820:
3371:"Biclique Cryptanalysis of the Full AES"
3016:
2862:
2644:
2642:
2615:"Biclique Cryptanalysis of the Full AES"
2478:
1986:
1115:
1072:
767:
3904:
3235:
2767:
2648:Alex Biryukov and Dmitry Khovratovich,
2331:Cryptographic Module Validation Program
2324:
2248:
1053:. While performing the decryption, the
666:High-level description of the algorithm
647:. The number of rounds are as follows:
307:
33:Visualization of the AES round function
5548:
4028:Daemen, Joan; Rijmen, Vincent (2002).
3803:"AES-256 joins the quantum resistance"
2469:
1915:{\displaystyle \operatorname {GF} (2)}
1101:
970:{\displaystyle S(a_{i,j})\neq a_{i,j}}
5157:
4173:
3604:from the original on 22 December 2009
3524:from the original on 12 February 2007
3392:
3390:
3294:
2639:
2339:Communications Security Establishment
2059:steps into a single round operation.
1599:{\displaystyle x^{8}+x^{4}+x^{3}+x+1}
1064:
897:. The S-box used is derived from the
212:
4095:"Advanced Encryption Standard (AES)"
3469:from the original on 24 January 2015
3277:from the original on 28 January 2010
3238:Advances in Cryptology - CRYPTO 2009
2852:from the original on March 28, 2017.
2796:from the original on August 23, 2024
2720:from the original on 28 January 2010
2607:
2495:Advanced Encryption Standard process
753:
643:, into the final output, called the
156:10, 12 or 14 (depending on key size)
4049:Paar, Christof; Pelzl, Jan (2009).
3492:"Index of formal scientific papers"
3088:from the original on August 8, 2010
204:), also known by its original name
13:
3784:"Quantum Security Analysis of AES"
3387:
3079:
3047:Improved Cryptanalysis of Rijndael
2424:
2308:
2099:"break" is anything faster than a
1979:
14:
5577:
4083:"256bit key – 128bit block – AES"
4075:
3082:"Is encryption really crackable?"
2840:John Schwartz (October 3, 2000).
2755:from the original on 5 March 2013
2274:In October 2005, Dag Arne Osvik,
228:AES is a variant of the Rijndael
5526:
5525:
5183:
4141:from the original on 2022-10-09.
3734:from the original on 2017-08-09.
3640:from the original on 2010-12-14.
3399:Information Security and Privacy
3328:from the original on 2010-07-02.
3140:from the original on 7 July 2007
2918:from the original on 2010-01-02.
2893:from the original on 2013-12-03.
2090:
330:substitution–permutation network
145:Substitution–permutation network
27:
3979:
3965:
3954:from the original on 2011-06-22
3933:
3879:
3868:from the original on 2013-01-02
3854:
3794:
3775:
3764:from the original on 2013-03-31
3738:
3710:
3669:
3658:from the original on 2011-10-03
3644:
3615:
3579:
3568:from the original on 2006-06-19
3535:
3509:
3498:from the original on 2008-09-17
3450:
3430:Jeffrey Goldberg (2011-08-18).
3423:
3362:
3351:from the original on 2010-06-04
3332:
3303:
3288:
3262:
3229:
3209:
3125:
3114:from the original on 2009-01-31
3100:
3062:from the original on 2007-02-23
3005:from the original on 2010-11-06
2984:
2973:from the original on 2013-07-20
2959:
2922:
2897:
2856:
2833:
2694:from the original on 2009-10-05
2661:from the original on 2009-09-28
2578:
2522:
2513:
2500:
2487:
2395:to high-performance computers.
2378:
2301:Many modern CPUs have built-in
2212:known-key distinguishing attack
1483:
5387:Information-theoretic security
4013:. Springer. pp. 268–287.
3914:OpenSSL, openssl@openssl.org.
3801:O'Shea, Dan (April 26, 2022).
3631:IACR Cryptology ePrint Archive
3595:IACR Cryptology ePrint Archive
3432:"AES Encryption isn't Cracked"
3345:IACR Cryptology ePrint Archive
3319:IACR Cryptology ePrint Archive
2705:
2386:
2256:do not attack the cipher as a
1959:
1946:
1909:
1903:
1900:
1894:
1772:
1766:
1699:and is then multiplied modulo
1686:
1673:
1644:
1631:
1140:
1134:
1006:
987:
945:
926:
872:
853:
319:ISO/IEC 18033-3: Block ciphers
217:), is a specification for the
1:
4055:. Springer. pp. 87–122.
3918:. Openssl.org. Archived from
3080:Ou, George (April 30, 2006).
2682:Bruce Schneier (2009-07-30).
2600:
2507:
2303:hardware instructions for AES
5561:Advanced Encryption Standard
3246:10.1007/978-3-642-03356-8_14
2863:Westlund, Harold B. (2002).
2548:is shifted left circular by
2313:AES-256 is considered to be
2210:In November 2009, the first
681:Initial round key addition:
251:AES has been adopted by the
198:Advanced Encryption Standard
20:Advanced Encryption Standard
7:
5503:Message authentication code
5458:Cryptographic hash function
5261:Cryptographic hash function
4156:HTML5 Animation of Rijndael
4007:. In Zheng, Yuliang (ed.).
3407:10.1007/978-3-319-19962-7_3
2991:Lynn Hathaway (June 2003).
2435:
2288:differential fault analysis
2199:, Dmitry Khovratovich, and
2147:XSL attack on block ciphers
2111:
2062:
657:14 rounds for 256-bit keys.
654:12 rounds for 192-bit keys.
651:10 rounds for 128-bit keys.
10:
5582:
5382:Harvest now, decrypt later
3973:"AMD Ryzen 7 1700X Review"
2428:
2347:Sensitive but Unclassified
2023:Optimization of the cipher
1109:
878:{\displaystyle S(a_{i,j})}
761:
324:Description of the ciphers
5521:
5498:Post-quantum cryptography
5450:
5191:
5153:
5119:
5083:
5075:Time/memory/data tradeoff
4872:
4791:
4337:
4264:
4212:
4169:
4165:
840:array is replaced with a
168:
160:
150:
140:
130:
120:
115:
93:
75:
65:
57:
43:
38:
26:
5488:Quantum key distribution
5478:Authenticated encryption
5333:Random number generation
4863:Whitening transformation
3110:. University of London.
3051:Fast Software Encryption
2943:10.1007/3-540-36400-5_13
2817:"AES Proposal: Rijndael"
2743:"AES Proposal: Rijndael"
2684:"Another New AES Attack"
2463:
2069:National Security Agency
1756:with a fixed polynomial
359:AES operates on a 4 × 4
298:National Security Agency
257:Data Encryption Standard
5483:Public-key cryptography
5473:Symmetric-key algorithm
5266:Key derivation function
5226:Cryptographic primitive
5219:Authentication protocol
5204:Outline of cryptography
5199:History of cryptography
4834:Confusion and diffusion
4125:"Part 3: Block ciphers"
3310:Vincent Rijmen (2010).
3165:; Doug Whiting (2001).
2242:may help to break AES.
2013:Rijndael's key schedule
829:{\displaystyle a_{i,j}}
274:AES is included in the
261:symmetric-key algorithm
5271:Secure Hash Algorithms
5214:Cryptographic protocol
3686:10.1109/EuroSP.2016.29
3295:Agren, Martin (2012).
2568:
2542:
2442:AES modes of operation
2415:AES-NI instruction set
2095:For cryptographers, a
2082:
2073:classified information
2000:
1966:
1916:
1871:
1750:
1693:
1651:
1600:
1535:
1503:
1154:
1147:
1082:
1047:
971:
899:multiplicative inverse
889:. Before round 0, the
879:
830:
796:
628:
5377:End-to-end encryption
5323:Cryptojacking malware
5127:Initialization vector
4146:Animation of Rijndael
4111:10.6028/NIST.FIPS.197
2569:
2543:
2077:
1990:
1967:
1917:
1872:
1751:
1694:
1652:
1601:
1536:
1534:{\displaystyle x^{7}}
1504:
1163:linear transformation
1148:
1119:
1076:
1057:step (the inverse of
1048:
972:
910:affine transformation
880:
831:
771:
629:
296:approved by the U.S.
287:Secretary of Commerce
246:AES selection process
5493:Quantum cryptography
5417:Trusted timestamping
4906:3-subset MITM attack
4522:Intel Cascade Cipher
4502:Hasty Pudding cipher
4104:. 26 November 2001.
3680:. pp. 261–275.
3177:. pp. 103–111.
2829:on February 3, 2007.
2552:
2532:
2325:NIST/CSEC validation
2265:D. J. Bernstein
2254:Side-channel attacks
2249:Side-channel attacks
2220:key-recovery attacks
2166:side-channel attacks
2137:", was announced by
1937:
1885:
1760:
1703:
1664:
1622:
1545:
1518:
1193:
1146:{\displaystyle c(x)}
1128:
981:
920:
847:
807:
702: – a
696:9, 11 or 13 rounds:
409:
308:Definitive standards
255:. It supersedes the
210:Dutch pronunciation:
126:128, 192 or 256 bits
5246:Cryptographic nonce
4945:Differential-linear
3518:"AES Timing Attack"
2567:{\displaystyle n-1}
2431:AES implementations
2178:Dmitry Khovratovich
1974:Rijndael MixColumns
1112:Rijndael MixColumns
214:[ˈrɛindaːl]
181:Related-key attacks
23:
5362:Subliminal channel
5346:Pseudorandom noise
5288:Key (cryptography)
5018:Differential-fault
4236:internal mechanics
3807:Fierce Electronics
3559:10.1007/11605805_1
3226:, October 15, 2000
3222:2009-02-01 at the
3198:on 4 November 2006
3163:Richard Schroeppel
2591:2009-10-23 at the
2564:
2538:
2170:related-key attack
2101:brute-force attack
2001:
1962:
1912:
1867:
1746:
1689:
1647:
1596:
1531:
1499:
1477:
1385:
1282:
1155:
1143:
1083:
1043:
967:
875:
826:
797:
624:
618:
363:array of 16 bytes
361:column-major order
171:brute-force attack
19:
5543:
5542:
5539:
5538:
5422:Key-based routing
5412:Trapdoor function
5278:Digital signature
5149:
5148:
5145:
5144:
5132:Mode of operation
4809:Lai–Massey scheme
4062:978-3-642-04101-3
4041:978-3-540-42580-9
4020:978-3-540-36178-7
3864:. Csrc.nist.gov.
3754:Intel Corporation
3695:978-1-5090-1751-5
3438:on 8 January 2015
3416:978-3-319-19961-0
3255:978-3-642-03355-1
3053:, 2000 pp213–230
2952:978-3-540-00409-7
2541:{\displaystyle n}
2497:for more details.
2236:Snowden documents
2234:According to the
1035:
232:developed by two
194:
193:
5573:
5529:
5528:
5357:Insecure channel
5209:Classical cipher
5178:
5171:
5164:
5155:
5154:
5003:Power-monitoring
4844:Avalanche effect
4552:Khufu and Khafre
4205:security summary
4194:
4187:
4180:
4171:
4170:
4167:
4166:
4163:
4162:
4142:
4140:
4129:
4115:
4113:
4099:
4090:
4066:
4045:
4024:
3994:
3993:
3991:
3983:
3977:
3976:
3969:
3963:
3962:
3960:
3959:
3953:
3946:
3937:
3931:
3930:
3928:
3927:
3911:
3902:
3901:
3899:
3898:
3889:. Archived from
3883:
3877:
3876:
3874:
3873:
3858:
3852:
3851:
3849:
3848:
3842:
3836:. Archived from
3835:
3827:
3818:
3817:
3815:
3813:
3798:
3792:
3791:
3779:
3773:
3772:
3770:
3769:
3763:
3750:
3742:
3736:
3735:
3733:
3722:
3714:
3708:
3707:
3673:
3667:
3666:
3664:
3663:
3648:
3642:
3641:
3639:
3628:
3619:
3613:
3612:
3610:
3609:
3603:
3592:
3583:
3577:
3576:
3574:
3573:
3567:
3548:
3539:
3533:
3532:
3530:
3529:
3516:Bruce Schneier.
3513:
3507:
3506:
3504:
3503:
3488:
3479:
3478:
3476:
3474:
3454:
3448:
3447:
3445:
3443:
3434:. Archived from
3427:
3421:
3420:
3394:
3385:
3384:
3382:
3376:. Archived from
3375:
3366:
3360:
3359:
3357:
3356:
3336:
3330:
3329:
3327:
3316:
3307:
3301:
3300:
3292:
3286:
3285:
3283:
3282:
3266:
3260:
3259:
3233:
3227:
3215:Bruce Schneier,
3213:
3207:
3206:
3204:
3203:
3197:
3187:. Archived from
3186:
3155:
3149:
3148:
3146:
3145:
3132:Bruce Schneier.
3129:
3123:
3122:
3120:
3119:
3104:
3098:
3097:
3095:
3093:
3077:
3071:
3070:
3068:
3067:
3020:
3014:
3013:
3011:
3010:
3004:
2997:
2988:
2982:
2981:
2979:
2978:
2963:
2957:
2956:
2926:
2920:
2919:
2917:
2910:
2901:
2895:
2894:
2883:
2877:
2876:
2871:. Archived from
2860:
2854:
2853:
2837:
2831:
2830:
2828:
2822:. Archived from
2821:
2812:
2806:
2805:
2803:
2801:
2795:
2784:
2776:
2765:
2764:
2762:
2760:
2754:
2747:
2738:
2729:
2728:
2726:
2725:
2709:
2703:
2702:
2700:
2699:
2679:
2670:
2669:
2667:
2666:
2646:
2637:
2636:
2634:
2632:
2627:on March 6, 2016
2626:
2620:. Archived from
2619:
2611:
2595:
2582:
2576:
2573:
2571:
2570:
2565:
2547:
2545:
2544:
2539:
2526:
2520:
2517:
2511:
2504:
2498:
2491:
2485:
2482:
2476:
2473:
2413:CPUs supporting
2319:bits of security
2281:
2139:Nicolas Courtois
2117:
2109:
2105:
2058:
2054:
2050:
2043:
2038:
2034:
2030:
2006:
1994:
1983:
1971:
1969:
1968:
1963:
1958:
1957:
1925:
1921:
1919:
1918:
1913:
1876:
1874:
1873:
1868:
1866:
1865:
1860:
1845:
1844:
1839:
1830:
1829:
1817:
1816:
1811:
1802:
1801:
1789:
1788:
1783:
1755:
1753:
1752:
1747:
1745:
1744:
1739:
1730:
1729:
1717:
1716:
1711:
1698:
1696:
1695:
1690:
1685:
1684:
1656:
1654:
1653:
1648:
1643:
1642:
1605:
1603:
1602:
1597:
1583:
1582:
1570:
1569:
1557:
1556:
1540:
1538:
1537:
1532:
1530:
1529:
1508:
1506:
1505:
1500:
1482:
1481:
1474:
1473:
1454:
1453:
1434:
1433:
1414:
1413:
1390:
1389:
1287:
1286:
1279:
1278:
1259:
1258:
1239:
1238:
1219:
1218:
1176:
1172:
1168:
1160:
1152:
1150:
1149:
1144:
1123:
1105:
1096:
1088:
1080:
1068:
1060:
1056:
1052:
1050:
1049:
1044:
1042:
1041:
1036:
1033:
1027:
1026:
1005:
1004:
976:
974:
973:
968:
966:
965:
944:
943:
907:
887:substitution box
884:
882:
881:
876:
871:
870:
843:
835:
833:
832:
827:
825:
824:
803:step, each byte
802:
775:
757:
747:
742:
737:
727:
721:
715:
701:
686:
676:AES key schedule
673:
633:
631:
630:
625:
623:
622:
615:
614:
603:
602:
591:
590:
579:
578:
565:
564:
553:
552:
541:
540:
529:
528:
515:
514:
503:
502:
491:
490:
479:
478:
465:
464:
453:
452:
441:
440:
429:
428:
395:
388:
384:
374:
236:cryptographers,
225:(NIST) in 2001.
216:
211:
31:
24:
18:
5581:
5580:
5576:
5575:
5574:
5572:
5571:
5570:
5546:
5545:
5544:
5535:
5517:
5446:
5187:
5182:
5141:
5115:
5084:Standardization
5079:
5008:Electromagnetic
4960:Integral/Square
4917:Piling-up lemma
4901:Biclique attack
4890:EFF DES cracker
4874:
4868:
4799:Feistel network
4787:
4412:CIPHERUNICORN-E
4407:CIPHERUNICORN-A
4339:
4333:
4266:
4260:
4214:
4208:
4198:
4138:
4127:
4123:
4097:
4093:
4081:
4078:
4073:
4063:
4042:
4021:
3998:
3997:
3989:
3985:
3984:
3980:
3971:
3970:
3966:
3957:
3955:
3951:
3944:
3938:
3934:
3925:
3923:
3912:
3905:
3896:
3894:
3885:
3884:
3880:
3871:
3869:
3860:
3859:
3855:
3846:
3844:
3840:
3833:
3829:
3828:
3821:
3811:
3809:
3799:
3795:
3780:
3776:
3767:
3765:
3761:
3748:
3744:
3743:
3739:
3731:
3725:cseweb.ucsd.edu
3720:
3716:
3715:
3711:
3696:
3674:
3670:
3661:
3659:
3654:. Hacker News.
3650:
3649:
3645:
3637:
3626:
3620:
3616:
3607:
3605:
3601:
3590:
3584:
3580:
3571:
3569:
3565:
3546:
3540:
3536:
3527:
3525:
3514:
3510:
3501:
3499:
3490:
3489:
3482:
3472:
3470:
3455:
3451:
3441:
3439:
3428:
3424:
3417:
3395:
3388:
3380:
3373:
3367:
3363:
3354:
3352:
3337:
3333:
3325:
3314:
3308:
3304:
3293:
3289:
3280:
3278:
3267:
3263:
3256:
3234:
3230:
3224:Wayback Machine
3214:
3210:
3201:
3199:
3191:
3175:Springer-Verlag
3156:
3152:
3143:
3141:
3130:
3126:
3117:
3115:
3106:
3105:
3101:
3091:
3089:
3078:
3074:
3065:
3063:
3054:
3021:
3017:
3008:
3006:
3002:
2995:
2989:
2985:
2976:
2974:
2965:
2964:
2960:
2953:
2927:
2923:
2915:
2908:
2902:
2898:
2885:
2884:
2880:
2861:
2857:
2838:
2834:
2826:
2819:
2813:
2809:
2799:
2797:
2793:
2782:
2778:
2777:
2768:
2758:
2756:
2752:
2745:
2739:
2732:
2723:
2721:
2710:
2706:
2697:
2695:
2680:
2673:
2664:
2662:
2653:
2647:
2640:
2630:
2628:
2624:
2617:
2613:
2612:
2608:
2603:
2598:
2593:Wayback Machine
2583:
2579:
2553:
2550:
2549:
2533:
2530:
2529:
2527:
2523:
2518:
2514:
2508:Security of AES
2505:
2501:
2492:
2488:
2483:
2479:
2474:
2470:
2466:
2447:Disk encryption
2438:
2433:
2427:
2425:Implementations
2389:
2381:
2361:Triple DES
2327:
2311:
2309:Quantum attacks
2279:
2263:In April 2005,
2251:
2224:biclique attack
2124:distributed.net
2107:
2103:
2093:
2065:
2056:
2052:
2048:
2041:
2036:
2035:steps with the
2032:
2028:
2025:
2004:
1992:
1985:
1981:
1953:
1949:
1938:
1935:
1934:
1923:
1886:
1883:
1882:
1861:
1856:
1855:
1840:
1835:
1834:
1825:
1821:
1812:
1807:
1806:
1797:
1793:
1784:
1779:
1778:
1761:
1758:
1757:
1740:
1735:
1734:
1725:
1721:
1712:
1707:
1706:
1704:
1701:
1700:
1680:
1676:
1665:
1662:
1661:
1638:
1634:
1623:
1620:
1619:
1617:
1613:
1578:
1574:
1565:
1561:
1552:
1548:
1546:
1543:
1542:
1525:
1521:
1519:
1516:
1515:
1476:
1475:
1463:
1459:
1456:
1455:
1443:
1439:
1436:
1435:
1423:
1419:
1416:
1415:
1403:
1399:
1392:
1391:
1384:
1383:
1378:
1373:
1368:
1362:
1361:
1356:
1351:
1346:
1340:
1339:
1334:
1329:
1324:
1318:
1317:
1312:
1307:
1302:
1292:
1291:
1281:
1280:
1268:
1264:
1261:
1260:
1248:
1244:
1241:
1240:
1228:
1224:
1221:
1220:
1208:
1204:
1197:
1196:
1194:
1191:
1190:
1181:in the cipher.
1174:
1170:
1166:
1158:
1129:
1126:
1125:
1121:
1114:
1108:
1103:
1094:
1086:
1078:
1071:
1066:
1058:
1054:
1037:
1032:
1031:
1016:
1012:
994:
990:
982:
979:
978:
955:
951:
933:
929:
921:
918:
917:
902:
885:using an 8-bit
860:
856:
848:
845:
844:
841:
814:
810:
808:
805:
804:
800:
792:
785:
773:
766:
760:
755:
745:
740:
735:
725:
719:
713:
699:
684:
671:
668:
617:
616:
610:
606:
604:
598:
594:
592:
586:
582:
580:
574:
570:
567:
566:
560:
556:
554:
548:
544:
542:
536:
532:
530:
524:
520:
517:
516:
510:
506:
504:
498:
494:
492:
486:
482:
480:
474:
470:
467:
466:
460:
456:
454:
448:
444:
442:
436:
432:
430:
424:
420:
413:
412:
410:
407:
406:
394:
391:
386:
382:
380:
377:
372:
370:
367:
364:
334:Feistel network
326:
310:
253:U.S. government
209:
177:biclique attack
58:First published
34:
21:
17:
12:
11:
5:
5579:
5569:
5568:
5563:
5558:
5541:
5540:
5537:
5536:
5534:
5533:
5522:
5519:
5518:
5516:
5515:
5510:
5508:Random numbers
5505:
5500:
5495:
5490:
5485:
5480:
5475:
5470:
5465:
5460:
5454:
5452:
5448:
5447:
5445:
5444:
5439:
5434:
5432:Garlic routing
5429:
5424:
5419:
5414:
5409:
5404:
5399:
5394:
5389:
5384:
5379:
5374:
5369:
5364:
5359:
5354:
5352:Secure channel
5349:
5343:
5342:
5341:
5330:
5325:
5320:
5315:
5310:
5308:Key stretching
5305:
5300:
5295:
5290:
5285:
5280:
5275:
5274:
5273:
5268:
5263:
5253:
5251:Cryptovirology
5248:
5243:
5238:
5236:Cryptocurrency
5233:
5228:
5223:
5222:
5221:
5211:
5206:
5201:
5195:
5193:
5189:
5188:
5181:
5180:
5173:
5166:
5158:
5151:
5150:
5147:
5146:
5143:
5142:
5140:
5139:
5134:
5129:
5123:
5121:
5117:
5116:
5114:
5113:
5108:
5103:
5098:
5093:
5087:
5085:
5081:
5080:
5078:
5077:
5072:
5067:
5062:
5057:
5052:
5047:
5042:
5037:
5032:
5027:
5022:
5021:
5020:
5015:
5010:
5005:
5000:
4990:
4985:
4980:
4975:
4967:
4962:
4957:
4950:Distinguishing
4947:
4942:
4941:
4940:
4935:
4930:
4920:
4910:
4909:
4908:
4903:
4893:
4882:
4880:
4870:
4869:
4867:
4866:
4856:
4851:
4846:
4841:
4836:
4831:
4826:
4821:
4816:
4814:Product cipher
4811:
4806:
4801:
4795:
4793:
4789:
4788:
4786:
4785:
4780:
4775:
4770:
4765:
4760:
4755:
4750:
4745:
4740:
4735:
4730:
4725:
4720:
4715:
4710:
4705:
4700:
4695:
4690:
4685:
4680:
4675:
4670:
4665:
4660:
4655:
4650:
4645:
4640:
4635:
4630:
4625:
4620:
4615:
4610:
4605:
4600:
4595:
4590:
4585:
4580:
4569:
4564:
4559:
4554:
4549:
4544:
4539:
4534:
4529:
4524:
4519:
4514:
4509:
4504:
4499:
4494:
4489:
4484:
4479:
4474:
4469:
4464:
4459:
4454:
4449:
4444:
4442:Cryptomeria/C2
4439:
4434:
4429:
4424:
4419:
4414:
4409:
4404:
4399:
4394:
4389:
4384:
4379:
4374:
4369:
4364:
4359:
4354:
4349:
4343:
4341:
4335:
4334:
4332:
4331:
4326:
4321:
4316:
4311:
4306:
4301:
4296:
4291:
4286:
4281:
4276:
4270:
4268:
4262:
4261:
4259:
4258:
4253:
4248:
4243:
4229:
4224:
4218:
4216:
4210:
4209:
4197:
4196:
4189:
4182:
4174:
4160:
4159:
4153:
4143:
4121:
4116:
4091:
4077:
4076:External links
4074:
4072:
4071:
4068:alternate link
4061:
4046:
4040:
4025:
4019:
3999:
3996:
3995:
3978:
3964:
3932:
3903:
3878:
3853:
3819:
3793:
3774:
3737:
3709:
3694:
3668:
3643:
3614:
3578:
3534:
3508:
3480:
3463:SPIEGEL ONLINE
3449:
3422:
3415:
3386:
3383:on 2012-09-05.
3361:
3331:
3302:
3287:
3261:
3254:
3228:
3208:
3184:10.1.1.28.4921
3159:Niels Ferguson
3150:
3124:
3099:
3084:. Ziff-Davis.
3072:
3031:Bruce Schneier
3015:
2983:
2958:
2951:
2921:
2896:
2878:
2875:on 2007-11-03.
2855:
2846:New York Times
2832:
2807:
2766:
2730:
2704:
2671:
2638:
2605:
2604:
2602:
2599:
2597:
2596:
2577:
2563:
2560:
2557:
2537:
2521:
2512:
2499:
2486:
2477:
2467:
2465:
2462:
2461:
2460:
2455:
2449:
2444:
2437:
2434:
2429:Main article:
2426:
2423:
2388:
2385:
2380:
2377:
2326:
2323:
2310:
2307:
2250:
2247:
2155:Bruce Schneier
2143:Josef Pieprzyk
2108:
2092:
2089:
2064:
2061:
2024:
2021:
1999:operation (⊕).
1984:
1978:
1961:
1956:
1952:
1948:
1945:
1942:
1911:
1908:
1905:
1902:
1899:
1896:
1893:
1890:
1864:
1859:
1854:
1851:
1848:
1843:
1838:
1833:
1828:
1824:
1820:
1815:
1810:
1805:
1800:
1796:
1792:
1787:
1782:
1777:
1774:
1771:
1768:
1765:
1743:
1738:
1733:
1728:
1724:
1720:
1715:
1710:
1688:
1683:
1679:
1675:
1672:
1669:
1646:
1641:
1637:
1633:
1630:
1627:
1615:
1611:
1595:
1592:
1589:
1586:
1581:
1577:
1573:
1568:
1564:
1560:
1555:
1551:
1528:
1524:
1512:
1511:
1510:
1509:
1498:
1495:
1492:
1489:
1486:
1480:
1472:
1469:
1466:
1462:
1458:
1457:
1452:
1449:
1446:
1442:
1438:
1437:
1432:
1429:
1426:
1422:
1418:
1417:
1412:
1409:
1406:
1402:
1398:
1397:
1395:
1388:
1382:
1379:
1377:
1374:
1372:
1369:
1367:
1364:
1363:
1360:
1357:
1355:
1352:
1350:
1347:
1345:
1342:
1341:
1338:
1335:
1333:
1330:
1328:
1325:
1323:
1320:
1319:
1316:
1313:
1311:
1308:
1306:
1303:
1301:
1298:
1297:
1295:
1290:
1285:
1277:
1274:
1271:
1267:
1263:
1262:
1257:
1254:
1251:
1247:
1243:
1242:
1237:
1234:
1231:
1227:
1223:
1222:
1217:
1214:
1211:
1207:
1203:
1202:
1200:
1142:
1139:
1136:
1133:
1110:Main article:
1107:
1100:
1070:
1063:
1040:
1030:
1025:
1022:
1019:
1015:
1011:
1008:
1003:
1000:
997:
993:
989:
986:
964:
961:
958:
954:
950:
947:
942:
939:
936:
932:
928:
925:
874:
869:
866:
863:
859:
855:
852:
823:
820:
817:
813:
790:
783:
764:Rijndael S-box
762:Main article:
759:
752:
751:
750:
749:
748:
743:
738:
730:
729:
728:
723:
717:
711:
694:
693:
692:
679:
667:
664:
659:
658:
655:
652:
637:
636:
635:
634:
621:
613:
609:
605:
601:
597:
593:
589:
585:
581:
577:
573:
569:
568:
563:
559:
555:
551:
547:
543:
539:
535:
531:
527:
523:
519:
518:
513:
509:
505:
501:
497:
493:
489:
485:
481:
477:
473:
469:
468:
463:
459:
455:
451:
447:
443:
439:
435:
431:
427:
423:
419:
418:
416:
392:
389:
378:
375:
368:
365:
325:
322:
321:
320:
317:
309:
306:
242:Vincent Rijmen
192:
191:
166:
165:
158:
157:
154:
148:
147:
142:
138:
137:
134:
128:
127:
124:
118:
117:
113:
112:
95:
91:
90:
77:
73:
72:
67:
63:
62:
59:
55:
54:
52:Vincent Rijmen
45:
41:
40:
36:
35:
32:
15:
9:
6:
4:
3:
2:
5578:
5567:
5564:
5562:
5559:
5557:
5556:Block ciphers
5554:
5553:
5551:
5532:
5524:
5523:
5520:
5514:
5513:Steganography
5511:
5509:
5506:
5504:
5501:
5499:
5496:
5494:
5491:
5489:
5486:
5484:
5481:
5479:
5476:
5474:
5471:
5469:
5468:Stream cipher
5466:
5464:
5461:
5459:
5456:
5455:
5453:
5449:
5443:
5440:
5438:
5435:
5433:
5430:
5428:
5427:Onion routing
5425:
5423:
5420:
5418:
5415:
5413:
5410:
5408:
5407:Shared secret
5405:
5403:
5400:
5398:
5395:
5393:
5390:
5388:
5385:
5383:
5380:
5378:
5375:
5373:
5370:
5368:
5365:
5363:
5360:
5358:
5355:
5353:
5350:
5347:
5344:
5339:
5336:
5335:
5334:
5331:
5329:
5326:
5324:
5321:
5319:
5316:
5314:
5311:
5309:
5306:
5304:
5301:
5299:
5298:Key generator
5296:
5294:
5291:
5289:
5286:
5284:
5281:
5279:
5276:
5272:
5269:
5267:
5264:
5262:
5259:
5258:
5257:
5256:Hash function
5254:
5252:
5249:
5247:
5244:
5242:
5239:
5237:
5234:
5232:
5231:Cryptanalysis
5229:
5227:
5224:
5220:
5217:
5216:
5215:
5212:
5210:
5207:
5205:
5202:
5200:
5197:
5196:
5194:
5190:
5186:
5179:
5174:
5172:
5167:
5165:
5160:
5159:
5156:
5152:
5138:
5135:
5133:
5130:
5128:
5125:
5124:
5122:
5118:
5112:
5109:
5107:
5104:
5102:
5099:
5097:
5094:
5092:
5089:
5088:
5086:
5082:
5076:
5073:
5071:
5068:
5066:
5063:
5061:
5058:
5056:
5053:
5051:
5048:
5046:
5043:
5041:
5038:
5036:
5033:
5031:
5030:Interpolation
5028:
5026:
5023:
5019:
5016:
5014:
5011:
5009:
5006:
5004:
5001:
4999:
4996:
4995:
4994:
4991:
4989:
4986:
4984:
4981:
4979:
4976:
4974:
4973:
4968:
4966:
4963:
4961:
4958:
4955:
4951:
4948:
4946:
4943:
4939:
4936:
4934:
4931:
4929:
4926:
4925:
4924:
4921:
4918:
4914:
4911:
4907:
4904:
4902:
4899:
4898:
4897:
4894:
4891:
4887:
4884:
4883:
4881:
4878:
4877:cryptanalysis
4871:
4864:
4860:
4859:Key whitening
4857:
4855:
4852:
4850:
4847:
4845:
4842:
4840:
4837:
4835:
4832:
4830:
4827:
4825:
4822:
4820:
4817:
4815:
4812:
4810:
4807:
4805:
4802:
4800:
4797:
4796:
4794:
4790:
4784:
4781:
4779:
4776:
4774:
4771:
4769:
4766:
4764:
4761:
4759:
4756:
4754:
4751:
4749:
4746:
4744:
4741:
4739:
4736:
4734:
4731:
4729:
4726:
4724:
4721:
4719:
4716:
4714:
4711:
4709:
4706:
4704:
4701:
4699:
4696:
4694:
4691:
4689:
4686:
4684:
4681:
4679:
4676:
4674:
4671:
4669:
4666:
4664:
4661:
4659:
4656:
4654:
4651:
4649:
4648:New Data Seal
4646:
4644:
4641:
4639:
4636:
4634:
4631:
4629:
4626:
4624:
4621:
4619:
4616:
4614:
4611:
4609:
4606:
4604:
4601:
4599:
4596:
4594:
4591:
4589:
4586:
4584:
4581:
4578:
4574:
4570:
4568:
4565:
4563:
4560:
4558:
4555:
4553:
4550:
4548:
4545:
4543:
4540:
4538:
4535:
4533:
4530:
4528:
4525:
4523:
4520:
4518:
4515:
4513:
4510:
4508:
4505:
4503:
4500:
4498:
4495:
4493:
4490:
4488:
4485:
4483:
4480:
4478:
4475:
4473:
4470:
4468:
4465:
4463:
4460:
4458:
4455:
4453:
4450:
4448:
4445:
4443:
4440:
4438:
4435:
4433:
4430:
4428:
4425:
4423:
4420:
4418:
4415:
4413:
4410:
4408:
4405:
4403:
4400:
4398:
4395:
4393:
4390:
4388:
4387:BEAR and LION
4385:
4383:
4380:
4378:
4375:
4373:
4370:
4368:
4365:
4363:
4360:
4358:
4355:
4353:
4350:
4348:
4345:
4344:
4342:
4336:
4330:
4327:
4325:
4322:
4320:
4317:
4315:
4312:
4310:
4307:
4305:
4302:
4300:
4297:
4295:
4292:
4290:
4287:
4285:
4282:
4280:
4277:
4275:
4272:
4271:
4269:
4263:
4257:
4254:
4252:
4249:
4247:
4244:
4241:
4237:
4233:
4230:
4228:
4225:
4223:
4220:
4219:
4217:
4211:
4206:
4202:
4201:Block ciphers
4195:
4190:
4188:
4183:
4181:
4176:
4175:
4172:
4168:
4164:
4157:
4154:
4151:
4147:
4144:
4137:
4133:
4126:
4122:
4120:
4117:
4112:
4107:
4103:
4096:
4092:
4089:. EmbeddedSW.
4088:
4084:
4080:
4079:
4069:
4064:
4058:
4054:
4053:
4047:
4043:
4037:
4033:
4032:
4026:
4022:
4016:
4012:
4011:
4006:
4001:
4000:
3988:
3982:
3974:
3968:
3950:
3943:
3936:
3922:on 2013-01-02
3921:
3917:
3910:
3908:
3893:on 2014-12-26
3892:
3888:
3882:
3867:
3863:
3857:
3843:on 2012-04-21
3839:
3832:
3826:
3824:
3812:September 26,
3808:
3804:
3797:
3789:
3785:
3778:
3760:
3756:
3755:
3747:
3741:
3730:
3726:
3719:
3713:
3705:
3701:
3697:
3691:
3687:
3683:
3679:
3672:
3657:
3653:
3647:
3636:
3632:
3625:
3618:
3600:
3596:
3589:
3582:
3564:
3560:
3556:
3552:
3545:
3538:
3523:
3519:
3512:
3497:
3493:
3487:
3485:
3468:
3464:
3460:
3453:
3437:
3433:
3426:
3418:
3412:
3408:
3404:
3400:
3393:
3391:
3379:
3372:
3365:
3350:
3346:
3342:
3335:
3324:
3320:
3313:
3306:
3298:
3291:
3276:
3272:
3265:
3257:
3251:
3247:
3243:
3239:
3232:
3225:
3221:
3218:
3217:AES Announced
3212:
3195:
3190:
3185:
3180:
3176:
3172:
3168:
3164:
3160:
3154:
3139:
3135:
3128:
3113:
3109:
3108:"Sean Murphy"
3103:
3087:
3083:
3076:
3061:
3057:
3052:
3048:
3044:
3040:
3036:
3032:
3028:
3024:
3019:
3001:
2994:
2987:
2972:
2968:
2962:
2954:
2948:
2944:
2940:
2936:
2932:
2925:
2914:
2907:
2900:
2892:
2888:
2882:
2874:
2870:
2866:
2859:
2851:
2847:
2843:
2836:
2825:
2818:
2811:
2792:
2788:
2781:
2775:
2773:
2771:
2751:
2744:
2737:
2735:
2719:
2715:
2708:
2693:
2689:
2685:
2678:
2676:
2660:
2656:
2651:
2645:
2643:
2623:
2616:
2610:
2606:
2594:
2590:
2587:
2581:
2561:
2558:
2555:
2535:
2525:
2516:
2509:
2503:
2496:
2490:
2481:
2472:
2468:
2459:
2456:
2453:
2450:
2448:
2445:
2443:
2440:
2439:
2432:
2422:
2420:
2416:
2412:
2408:
2403:
2401:
2396:
2394:
2384:
2376:
2372:
2368:
2366:
2362:
2357:
2355:
2350:
2348:
2344:
2340:
2336:
2332:
2322:
2320:
2316:
2306:
2304:
2299:
2295:
2291:
2289:
2284:
2277:
2272:
2270:
2266:
2261:
2259:
2255:
2246:
2243:
2241:
2240:tau statistic
2237:
2232:
2228:
2225:
2221:
2216:
2213:
2208:
2204:
2202:
2198:
2197:Nathan Keller
2194:
2193:Orr Dunkelman
2190:
2185:
2183:
2179:
2175:
2174:Alex Biryukov
2171:
2167:
2162:
2160:
2156:
2150:
2148:
2144:
2140:
2136:
2131:
2127:
2125:
2121:
2115:
2102:
2098:
2097:cryptographic
2091:Known attacks
2088:
2085:
2081:
2076:
2074:
2070:
2060:
2045:
2020:
2018:
2014:
2010:
1998:
1989:
1977:
1975:
1954:
1950:
1943:
1940:
1933:
1929:
1906:
1897:
1891:
1888:
1880:
1862:
1857:
1852:
1849:
1846:
1841:
1836:
1831:
1826:
1822:
1818:
1813:
1808:
1803:
1798:
1794:
1790:
1785:
1780:
1775:
1769:
1763:
1741:
1736:
1731:
1726:
1722:
1718:
1713:
1708:
1681:
1677:
1670:
1667:
1658:
1639:
1635:
1628:
1625:
1609:
1593:
1590:
1587:
1584:
1579:
1575:
1571:
1566:
1562:
1558:
1553:
1549:
1526:
1522:
1496:
1493:
1490:
1487:
1484:
1478:
1470:
1467:
1464:
1460:
1450:
1447:
1444:
1440:
1430:
1427:
1424:
1420:
1410:
1407:
1404:
1400:
1393:
1386:
1380:
1375:
1370:
1365:
1358:
1353:
1348:
1343:
1336:
1331:
1326:
1321:
1314:
1309:
1304:
1299:
1293:
1288:
1283:
1275:
1272:
1269:
1265:
1255:
1252:
1249:
1245:
1235:
1232:
1229:
1225:
1215:
1212:
1209:
1205:
1198:
1189:
1188:
1187:
1186:
1185:
1182:
1180:
1164:
1137:
1131:
1118:
1113:
1099:
1092:
1075:
1062:
1038:
1028:
1023:
1020:
1017:
1013:
1009:
1001:
998:
995:
991:
984:
962:
959:
956:
952:
948:
940:
937:
934:
930:
923:
915:
911:
905:
900:
896:
892:
888:
867:
864:
861:
857:
850:
839:
821:
818:
815:
811:
794:
786:
779:
770:
765:
744:
739:
734:
733:
731:
724:
718:
712:
709:
705:
698:
697:
695:
690:
683:
682:
680:
677:
670:
669:
663:
656:
653:
650:
649:
648:
646:
642:
619:
611:
607:
599:
595:
587:
583:
575:
571:
561:
557:
549:
545:
537:
533:
525:
521:
511:
507:
499:
495:
487:
483:
475:
471:
461:
457:
449:
445:
437:
433:
425:
421:
414:
405:
404:
403:
402:
401:
399:
362:
357:
355:
351:
347:
343:
339:
335:
331:
318:
315:
314:
313:
305:
303:
299:
295:
291:
288:
284:
281:
277:
272:
269:
264:
262:
258:
254:
249:
247:
243:
239:
235:
231:
226:
224:
220:
215:
207:
203:
199:
188:
184:
182:
178:
172:
167:
164:
163:cryptanalysis
159:
155:
153:
149:
146:
143:
139:
135:
133:
129:
125:
123:
119:
116:Cipher detail
114:
111:
107:
103:
99:
96:
94:Certification
92:
89:
85:
81:
78:
74:
71:
68:
64:
60:
56:
53:
49:
46:
42:
37:
30:
25:
5566:Cryptography
5463:Block cipher
5303:Key schedule
5293:Key exchange
5283:Kleptography
5241:Cryptosystem
5185:Cryptography
5035:Partitioning
4993:Side-channel
4971:
4938:Higher-order
4923:Differential
4804:Key schedule
4221:
4131:
4101:
4086:
4051:
4034:. Springer.
4030:
4009:
3981:
3967:
3956:. Retrieved
3935:
3924:. Retrieved
3920:the original
3895:. Retrieved
3891:the original
3881:
3870:. Retrieved
3856:
3845:. Retrieved
3838:the original
3810:. Retrieved
3806:
3796:
3787:
3777:
3766:. Retrieved
3752:
3740:
3724:
3712:
3677:
3671:
3660:. Retrieved
3646:
3630:
3617:
3606:. Retrieved
3594:
3581:
3570:. Retrieved
3550:
3537:
3526:. Retrieved
3511:
3500:. Retrieved
3494:. Cr.yp.to.
3471:. Retrieved
3462:
3452:
3440:. Retrieved
3436:the original
3425:
3398:
3378:the original
3364:
3353:. Retrieved
3344:
3334:
3318:
3305:
3296:
3290:
3279:. Retrieved
3264:
3237:
3231:
3211:
3200:. Retrieved
3189:the original
3170:
3153:
3142:. Retrieved
3127:
3116:. Retrieved
3102:
3090:. Retrieved
3075:
3064:. Retrieved
3046:
3043:Doug Whiting
3039:David Wagner
3027:Stefan Lucks
3018:
3007:. Retrieved
2986:
2975:. Retrieved
2961:
2934:
2924:
2899:
2881:
2873:the original
2868:
2858:
2845:
2835:
2824:the original
2810:
2798:. Retrieved
2786:
2757:. Retrieved
2722:. Retrieved
2707:
2696:. Retrieved
2687:
2663:. Retrieved
2649:
2629:. Retrieved
2622:the original
2609:
2580:
2524:
2515:
2502:
2489:
2480:
2471:
2404:
2397:
2390:
2382:
2379:Test vectors
2373:
2369:
2358:
2351:
2328:
2312:
2300:
2296:
2292:
2285:
2273:
2262:
2252:
2244:
2233:
2229:
2217:
2209:
2205:
2186:
2182:constraining
2163:
2151:
2132:
2128:
2094:
2086:
2083:
2078:
2066:
2046:
2026:
2002:
1932:finite field
1659:
1513:
1183:
1156:
1084:
890:
837:
798:
788:
781:
777:
708:lookup table
672:KeyExpansion
660:
638:
397:
358:
354:finite field
349:
327:
311:
290:Donald Evans
273:
265:
250:
230:block cipher
227:
205:
201:
197:
195:
174:
161:Best public
66:Derived from
5451:Mathematics
5442:Mix network
5120:Utilization
5106:NSA Suite B
5091:AES process
5040:Rubber-hose
4978:Related-key
4886:Brute-force
4265:Less common
3992:. May 2010.
3473:4 September
3442:30 December
3023:John Kelsey
2759:21 February
2657:. Table 1.
2400:Pentium Pro
2393:smart cards
2387:Performance
2042:AddRoundKey
2005:AddRoundKey
1993:AddRoundKey
1982:AddRoundKey
1879:hexadecimal
1055:InvSubBytes
914:derangement
746:AddRoundKey
726:AddRoundKey
689:bitwise xor
685:AddRoundKey
396:termed the
238:Joan Daemen
132:Block sizes
48:Joan Daemen
5550:Categories
5402:Ciphertext
5372:Decryption
5367:Encryption
5328:Ransomware
5070:Chi-square
4988:Rotational
4928:Impossible
4849:Block size
4743:Spectr-H64
4567:Ladder-DES
4562:Kuznyechik
4507:Hierocrypt
4377:BassOmatic
4340:algorithms
4267:algorithms
4240:Triple DES
4215:algorithms
4150:CrypTool 1
3958:2010-12-28
3926:2012-12-23
3897:2014-06-26
3872:2012-12-23
3847:2012-05-29
3768:2017-07-26
3662:2012-12-23
3608:2009-12-08
3572:2008-11-02
3528:2007-03-17
3502:2008-11-02
3355:2010-03-11
3281:2010-03-11
3202:2006-10-06
3194:PostScript
3144:2007-07-27
3118:2008-11-02
3066:2007-03-06
3009:2011-02-15
2977:2012-12-23
2800:August 26,
2724:2010-03-11
2698:2010-03-11
2665:2010-02-16
2601:References
2407:Intel Core
2343:FIPS 140-2
2276:Adi Shamir
2218:The first
2201:Adi Shamir
2135:XSL attack
2057:MixColumns
2037:MixColumns
1928:MDS matrix
1924:MixColumns
1175:MixColumns
1167:MixColumns
1159:MixColumns
1122:MixColumns
1104:MixColumns
720:MixColumns
704:non-linear
645:ciphertext
338:block size
302:top secret
300:(NSA) for
219:encryption
76:Successors
22:(Rijndael)
5392:Plaintext
5045:Black-bag
4965:Boomerang
4954:Known-key
4933:Truncated
4758:Threefish
4753:SXAL/MBAL
4643:MultiSwap
4598:MacGuffin
4557:KN-Cipher
4497:Grand Cru
4452:CS-Cipher
4432:COCONUT98
3179:CiteSeerX
3092:August 7,
3035:Mike Stay
2559:−
2452:Whirlpool
2411:AMD Ryzen
2258:black box
2126:in 2006.
2053:ShiftRows
2033:ShiftRows
1944:
1892:
1847:⋅
1819:⋅
1791:⋅
1719:⋅
1671:
1629:
1494:≤
1488:≤
1179:diffusion
1177:provides
1171:ShiftRows
1095:ShiftRows
1087:ShiftRows
1079:ShiftRows
1067:ShiftRows
1029:≠
1010:⊕
949:≠
916:), i.e.,
741:ShiftRows
714:ShiftRows
641:plaintext
141:Structure
122:Key sizes
84:Grand Cru
44:Designers
5531:Category
5437:Kademlia
5397:Codetext
5340:(CSPRNG)
5318:Machines
5096:CRYPTREC
5060:Weak key
5013:Acoustic
4854:Key size
4698:Red Pike
4517:IDEA NXT
4397:Chiasmus
4392:CAST-256
4372:BaseKing
4357:Akelarre
4352:Adiantum
4319:Skipjack
4284:CAST-128
4279:Camellia
4227:Blowfish
4136:Archived
3949:Archived
3866:Archived
3759:Archived
3729:Archived
3704:11251391
3656:Archived
3635:Archived
3599:Archived
3563:Archived
3522:Archived
3496:Archived
3467:Archived
3349:Archived
3323:Archived
3275:Archived
3220:Archived
3138:Archived
3112:Archived
3086:Archived
3060:Archived
3000:Archived
2971:Archived
2913:Archived
2891:Archived
2850:Archived
2791:Archived
2750:Archived
2718:Archived
2692:Archived
2659:Archived
2589:Archived
2436:See also
2419:Westmere
2354:FIPS 140
2280:dm-crypt
2189:preprint
2063:Security
2049:SubBytes
2029:SubBytes
1059:SubBytes
801:SubBytes
774:SubBytes
756:SubBytes
736:SubBytes
700:SubBytes
346:key size
344:, and a
206:Rijndael
190:version.
187:preprint
136:128 bits
102:CRYPTREC
100:winner,
5192:General
5137:Padding
5055:Rebound
4763:Treyfer
4713:SAVILLE
4673:PRESENT
4663:NOEKEON
4608:MAGENTA
4603:Madryga
4583:Lucifer
4447:CRYPTON
4256:Twofish
4246:Serpent
2575:blocks.
2315:quantum
2269:OpenSSL
2159:Twofish
2122:key by
2104:
2003:In the
1991:In the
1930:in the
1610:with 1B
1157:In the
1120:In the
1077:In the
842:SubByte
836:in the
799:In the
772:In the
387:
383:
373:
340:of 128
283:18033-3
234:Belgian
39:General
5313:Keygen
5101:NESSIE
5050:Davies
4998:Timing
4913:Linear
4873:Attack
4792:Design
4783:Zodiac
4748:Square
4723:SHACAL
4718:SC2000
4678:Prince
4658:Nimbus
4653:NewDES
4638:MULTI2
4628:MISTY1
4571:LOKI (
4547:KHAZAD
4542:KeeLoq
4537:KASUMI
4532:Kalyna
4417:CLEFIA
4402:CIKS-1
4362:Anubis
4213:Common
4114:. 197.
4059:
4038:
4017:
3702:
3692:
3413:
3252:
3181:
3041:, and
2949:
2631:May 1,
2510:below.
2055:, and
2011:using
1922:. The
1165:. The
1091:offset
895:cipher
350:per se
294:cipher
152:Rounds
106:NESSIE
88:Kalyna
80:Anubis
70:Square
5348:(PRN)
4983:Slide
4839:Round
4824:P-box
4819:S-box
4778:XXTEA
4738:Speck
4733:Simon
4728:SHARK
4708:SAFER
4693:REDOC
4618:Mercy
4577:89/91
4527:Iraqi
4492:G-DES
4482:FEA-M
4462:DES-X
4427:Cobra
4382:BATON
4367:Ascon
4347:3-Way
4338:Other
4139:(PDF)
4128:(PDF)
4098:(PDF)
3990:(PDF)
3952:(PDF)
3945:(PDF)
3841:(PDF)
3834:(PDF)
3790:: 40.
3762:(PDF)
3749:(PDF)
3732:(PDF)
3721:(PDF)
3700:S2CID
3638:(PDF)
3627:(PDF)
3602:(PDF)
3591:(PDF)
3566:(PDF)
3547:(PDF)
3381:(PDF)
3374:(PDF)
3326:(PDF)
3315:(PDF)
3192:(PDF/
3003:(PDF)
2996:(PDF)
2916:(PDF)
2909:(PDF)
2827:(PDF)
2820:(PDF)
2794:(PDF)
2783:(PDF)
2753:(PDF)
2746:(PDF)
2625:(PDF)
2618:(PDF)
2464:Notes
2398:On a
2112:(see
901:over
891:state
838:state
398:state
5111:CNSA
4970:Mod
4896:MITM
4668:NUSH
4623:MESH
4613:MARS
4487:FROG
4477:FEAL
4457:DEAL
4437:Crab
4422:CMEA
4329:XTEA
4314:SEED
4294:IDEA
4289:GOST
4274:ARIA
4057:ISBN
4036:ISBN
4015:ISBN
3814:2023
3690:ISBN
3475:2015
3444:2014
3411:ISBN
3250:ISBN
3094:2010
2947:ISBN
2802:2024
2761:2013
2633:2019
2586:here
2506:See
2493:See
2409:and
2365:SHA1
2329:The
2141:and
2067:The
2031:and
1980:The
1106:step
1102:The
1085:The
1069:step
1065:The
758:step
754:The
385:...,
342:bits
268:FIPS
240:and
196:The
61:1998
5065:Tau
5025:XSL
4829:SPN
4773:xmx
4768:UES
4703:S-1
4688:RC2
4633:MMB
4512:ICE
4467:DFC
4324:TEA
4309:RC6
4304:RC5
4299:LEA
4251:SM4
4232:DES
4222:AES
4106:doi
3788:HAL
3682:doi
3555:doi
3403:doi
3242:doi
2939:doi
2405:On
2363:or
2120:RC5
2017:XOR
2009:key
1997:XOR
1608:XOR
906:(2)
789:S(a
280:IEC
276:ISO
202:AES
110:NSA
98:AES
5552::
4593:M8
4588:M6
4575:,
4573:97
4472:E2
4238:,
4130:.
4100:.
4085:.
3947:.
3906:^
3822:^
3805:.
3786:.
3757:.
3751:.
3727:.
3723:.
3698:.
3688:.
3633:.
3629:.
3597:.
3593:.
3561:.
3553:.
3549:.
3520:.
3483:^
3465:.
3461:.
3409:.
3389:^
3347:.
3343:.
3321:.
3317:.
3273:.
3248:.
3173:.
3169:.
3161:;
3136:.
3058:.
3049:,
3045:,
3037:,
3033:,
3029:,
3025:,
2998:.
2969:.
2945:.
2933:.
2911:.
2889:.
2867:.
2848:.
2844:.
2785:.
2769:^
2733:^
2716:.
2690:.
2686:.
2674:^
2652:,
2641:^
2195:,
2176:,
2149:.
2075::
2051:,
2019:.
1976:.
1941:GF
1889:GF
1863:16
1858:02
1842:16
1837:01
1814:16
1809:01
1786:16
1781:03
1742:16
1737:01
1714:16
1709:01
1668:GF
1657:.
1626:GF
1616:16
1612:16
1173:,
1039:16
1034:FF
904:GF
791:ij
787:=
784:ij
780:;
612:15
600:11
562:14
550:10
512:13
462:12
400::
393:15
356:.
108:,
104:,
86:,
82:,
50:,
5177:e
5170:t
5163:v
4972:n
4956:)
4952:(
4919:)
4915:(
4892:)
4888:(
4879:)
4875:(
4865:)
4861:(
4683:Q
4579:)
4242:)
4234:(
4207:)
4203:(
4193:e
4186:t
4179:v
4108::
4065:.
4044:.
4023:.
3975:.
3961:.
3929:.
3900:.
3875:.
3850:.
3816:.
3771:.
3706:.
3684::
3665:.
3611:.
3575:.
3557::
3531:.
3505:.
3477:.
3446:.
3419:.
3405::
3358:.
3284:.
3258:.
3244::
3205:.
3196:)
3147:.
3121:.
3096:.
3069:.
3012:.
2980:.
2955:.
2941::
2804:.
2763:.
2727:.
2701:.
2668:.
2635:.
2562:1
2556:n
2536:n
2116:)
2106:—
1960:)
1955:8
1951:2
1947:(
1910:]
1907:x
1904:[
1901:)
1898:2
1895:(
1853:+
1850:z
1832:+
1827:2
1823:z
1804:+
1799:3
1795:z
1776:=
1773:)
1770:z
1767:(
1764:c
1732:+
1727:4
1723:z
1687:)
1682:8
1678:2
1674:(
1645:)
1640:8
1636:2
1632:(
1594:1
1591:+
1588:x
1585:+
1580:3
1576:x
1572:+
1567:4
1563:x
1559:+
1554:8
1550:x
1527:7
1523:x
1497:3
1491:j
1485:0
1479:]
1471:j
1468:,
1465:3
1461:a
1451:j
1448:,
1445:2
1441:a
1431:j
1428:,
1425:1
1421:a
1411:j
1408:,
1405:0
1401:a
1394:[
1387:]
1381:2
1376:1
1371:1
1366:3
1359:3
1354:2
1349:1
1344:1
1337:1
1332:3
1327:2
1322:1
1315:1
1310:1
1305:3
1300:2
1294:[
1289:=
1284:]
1276:j
1273:,
1270:3
1266:b
1256:j
1253:,
1250:2
1246:b
1236:j
1233:,
1230:1
1226:b
1216:j
1213:,
1210:0
1206:b
1199:[
1153:.
1141:)
1138:x
1135:(
1132:c
1024:j
1021:,
1018:i
1014:a
1007:)
1002:j
999:,
996:i
992:a
988:(
985:S
963:j
960:,
957:i
953:a
946:)
941:j
938:,
935:i
931:a
927:(
924:S
873:)
868:j
865:,
862:i
858:a
854:(
851:S
822:j
819:,
816:i
812:a
795:.
793:)
782:b
778:S
710:.
691:.
620:]
608:b
596:b
588:7
584:b
576:3
572:b
558:b
546:b
538:6
534:b
526:2
522:b
508:b
500:9
496:b
488:5
484:b
476:1
472:b
458:b
450:8
446:b
438:4
434:b
426:0
422:b
415:[
390:b
381:,
379:1
376:b
371:,
369:0
366:b
278:/
208:(
200:(
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.