181:
1696:
4714:
770:
1438:
1453:
441:
1111:
1058:
1691:{\displaystyle \mathrm {Counter0} ={\begin{cases}IV\parallel 0^{31}\parallel 1&{\text{for }}\operatorname {len} (IV)=96\\\operatorname {GHASH} \left(IV\parallel 0^{s}\parallel 0^{64}\parallel \operatorname {len} _{64}(IV)\right){\text{ with }}s=128-\operatorname {len} (IV)\mod 128&{\text{otherwise}}\end{cases}}}
765:{\displaystyle S_{i}={\begin{cases}A_{i}&{\text{for }}i=1,\ldots ,m-1\\A_{m}^{*}\parallel 0^{128-v}&{\text{for }}i=m\\C_{i-m}&{\text{for }}i=m+1,\ldots ,m+n-1\\C_{n}^{*}\parallel 0^{128-u}&{\text{for }}i=m+n\\\operatorname {len} (A)\parallel \operatorname {len} (C)&{\text{for }}i=m+n+1\end{cases}}}
1976:
Independent of this attack, an adversary may attempt to systematically guess many different tags for a given input to authenticated decryption and thereby increase the probability that one (or more) of them, eventually, will be considered valid. For this reason, the system or protocol that implements
1847:
by interleaving operations. This process is called function stitching, and while in principle it can be applied to any combination of cryptographic algorithms, GCM is especially suitable. Manley and Gregg show the ease of optimizing when using function stitching with GCM. They present a program
61:
methods. This means that as input it takes a key K, some plaintext P, and some associated data AD; it then encrypts the plaintext using the key to produce ciphertext C, and computes an authentication tag T from the ciphertext and the associated data (which remains unencrypted). A recipient with
1851:
GCM has been criticized in the embedded world (for example by
Silicon Labs) because the parallel processing is not suited for performant use of cryptographic hardware engines. As a result, GCM reduces the performance of encryption for some of the most performance-sensitive devices. Specialized
1433:{\displaystyle {\begin{aligned}X_{i}^{'}&={\begin{cases}0&{\text{for }}i\leq 0\\\left(X_{i-k}^{'}\oplus S_{i}\right)\cdot H^{k}&{\text{for }}i=1,\ldots ,m+n+1-k\\\end{cases}}\\X_{i}&=\sum _{j=1}^{k}\left(X_{i+j-2k}^{'}\oplus S_{i+j-k}\right)\cdot H^{k-j+1}\end{aligned}}}
1799:
per each block (128 bit) of encrypted and authenticated data. The block cipher operations are easily pipelined or parallelized; the multiplication operations are easily pipelined and can be parallelized with some modest effort (either by parallelizing the actual operation, by adapting
1815:. In 2015, SPARC added the XMPMUL instruction, which performs XOR multiplication of much larger values, up to 2048 × 2048 bit input values producing a 4096-bit result. These instructions enable fast multiplication over GF(2), and can be used with any field representation.
851:
2458:
Pfau, Johannes; Reuter, Maximilian; Harbaum, Tanja; Hofmann, Klaus; Becker, Jurgen (September 2019). "A Hardware
Perspective on the ChaCha Ciphers: Scalable Chacha8/12/20 Implementations Ranging from 476 Slices to Bitrates of 175 Gbit/s": 294–299.
1984:. This work gives some valuable insights into how polynomial hash-based authentication works. More precisely, this work describes a particular way of forging a GCM message, given a valid GCM message, that works with probability of about
1822:
Resistant AES-GCM" that achieves 10.68 cycles per byte AES-GCM authenticated encryption on 64-bit Intel processors. Dai et al. report 3.5 cycles per byte for the same algorithm when using Intel's AES-NI and PCLMULQDQ instructions.
1894:
The authentication strength depends on the length of the authentication tag, like with all symmetric message authentication codes. The use of shorter authentication tags with GCM is discouraged. The bit-length of the tag, denoted
186:
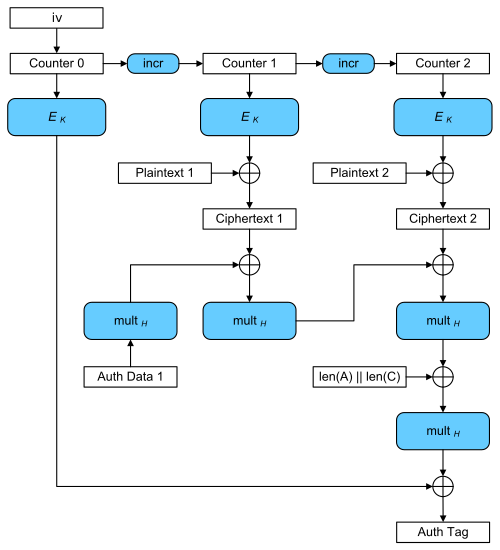
Encryption: A series of 128-bit counters is encrypted using the block cipher E with key K; this can occur in parallel. The results are combined using bitwise XOR with 128-bit plaintext blocks, producing a series of ciphertext
1907:
may be 64 or 32, but the use of these two tag lengths constrains the length of the input data and the lifetime of the key. Appendix C in NIST SP 800-38D provides guidance for these constraints (for example, if
1956:
denotes the total number of blocks in the encoding (the input to the GHASH function), then there is a method of constructing a targeted ciphertext forgery that is expected to succeed with a probability of approximately
1998:
bits long. However, this work does not show a more effective attack than was previously known; the success probability in observation 1 of this paper matches that of lemma 2 from the INDOCRYPT 2004 analysis (setting
1842:
When both authentication and encryption need to be performed on a message, a software implementation can achieve speed gains by overlapping the execution of those operations. Performance is increased by exploiting
1116:
62:
knowledge of K, upon reception of AD, C and T, can decrypt the ciphertext to recover the plaintext P and can check the tag T to ensure that neither ciphertext nor associated data were tampered with.
351:
98:
Different block cipher modes of operation can have significantly different performance and efficiency characteristics, even when used with the same block cipher. GCM can take full advantage of
189:
Authentication: The
Additional Data and these ciphertext blocks are combined using multiplication with a key-dependent constant H in the Galois field GF(2) to produce the authentication tag.
1965:
is shorter than 128, then each successful forgery in this attack increases the probability that subsequent targeted forgeries will succeed, and leaks information about the hash subkey,
1952:
Ferguson and
Saarinen independently described how an attacker can perform optimal attacks against GCM authentication, which meet the lower bound on its security. Ferguson showed that, if
1929:-bit tag at random, it is expected to be correct for given data with probability measure 2. With GCM, however, an adversary can increase their likelihood of success by choosing tags with
1053:{\displaystyle X_{i}=\sum _{j=1}^{i}S_{j}\cdot H^{i-j+1}={\begin{cases}0&{\text{for }}i=0\\\left(X_{i-1}\oplus S_{i}\right)\cdot H&{\text{for }}i=1,\ldots ,m+n+1\end{cases}}}
276:
54:
which is widely adopted for its performance. GCM throughput rates for state-of-the-art, high-speed communication channels can be achieved with inexpensive hardware resources.
833:
4694:
4524:
184:
GCM operation. For simplicity, a case with only a single block of additional authenticated data (labeled Auth Data 1) and two blocks of plaintext is shown.
1876:. It is secure when it is used with a block cipher that is indistinguishable from a random permutation; however, security depends on choosing a unique
281:
The authentication tag is constructed by feeding blocks of data into the GHASH function and encrypting the result. This GHASH function is defined by
2642:
2437:
1828:
4362:
1824:
207:
4282:
3609:
2690:
1776:
3670:
428:
First, the authenticated text and the cipher text are separately zero-padded to multiples of 128 bits and combined into a single message
3699:
2306:
4757:
1933:
words – the total length of the ciphertext plus any additional authenticated data (AAD) – with probability measure 2 by a factor of
1848:
generator that takes an annotated C version of a cryptographic algorithm and generates code that runs well on the target processor.
4742:
1811:
instruction, highlighting its use for GCM. In 2011, SPARC added the XMULX and XMULXHI instructions, which also perform 64 × 64 bit
177:
that can be used to verify the integrity of the data. The encrypted text then contains the IV, ciphertext, and authentication tag.
3436:
2792:
2277:
199:
4752:
4298:
3426:
2920:
2544:
2421:
2346:
2162:
2092:
287:
123:
2404:
Manley, Raymond; Gregg, David (2010). "A Program
Generator for Intel AES-NI Instructions". In Gong, G.; Gupta, K.C. (eds.).
1891:
bits of plain text (64 GiB). NIST Special
Publication 800-38D includes guidelines for initialization vector selection.
3589:
3563:
3431:
3327:
2500:
1915:
and the maximal packet size is 2 bytes, the authentication decryption function should be invoked no more than 2 times; if
1818:
Impressive performance results are published for GCM on a number of platforms. Käsper and
Schwabe described a "Faster and
17:
1922:
and the maximal packet size is 2 bytes, the authentication decryption function should be invoked no more than 2 times).
4059:
3404:
4226:
2560:
2113:
4355:
202:
of encryption with the new Galois mode of authentication. The key feature is the ease of parallel computation of the
2517:
McGrew, David A.; Viega, John (2004). "The
Security and Performance of the Galois/counter mode (GCM) of Operation".
3573:
2683:
1937:. Although, one must bear in mind that these optimal tags are still dominated by the algorithm's survival measure
3663:
3452:
1757:
99:
1831:
achieved 2.47 cycles per byte on the 3rd generation Intel processors. Appropriate patches were prepared for the
206:
multiplication used for authentication. This feature permits higher throughput than encryption algorithms, like
4573:
4504:
4267:
3752:
3704:
3630:
2039:
43:
2329:
Käsper, E.; Schwabe, P. (2009). "Faster and Timing-Attack
Resistant AES-GCM". In Clavier, C.; Gaj, K. (eds.).
57:
The GCM algorithm provides both data authenticity (integrity) and confidentiality and belongs to the class of
4054:
2655:
1844:
216:
4348:
4272:
2720:
1977:
GCM should monitor and, if necessary, limit the number of unsuccessful verification attempts for each key.
137:
4689:
4644:
4447:
4041:
3683:
3679:
3516:
2676:
2075:
Lemsitzer, S.; Wolkerstorfer, J.; Felber, N.; Braendli, M. (2007). Paillier, P.; Verbauwhede, I. (eds.).
2018:
88:
2390:
Gopal, V., Feghali, W., Guilford, J., Ozturk, E., Wolrich, G., Dixon, M., Locktyukhin, M., Perminov, M.
4568:
3656:
3533:
3443:
3421:
2734:
2307:"Intel Carry-Less Multiplication Instruction and its Usage for Computing the GCM Mode (Revision 2.02)"
4684:
3937:
3538:
3394:
3347:
2822:
2149:. Lecture Notes in Computer Science. Vol. 3017. Berlin, Heidelberg: Springer. pp. 408–426.
1836:
3742:
2485:
2182:
1491:
1150:
932:
463:
4674:
4664:
4519:
4277:
4113:
3812:
3807:
3604:
3486:
3361:
2730:
2077:
Cryptographic
Hardware and Embedded Systems - CHES 2007 . GCM-AES Architecture Optimized for FPGAs
2034:
1949:. Moreover, GCM is neither well-suited for use with very short tag-lengths nor very long messages.
1772:
1768:
58:
2527:
1903:
may be any one of the following five values: 128, 120, 112, 104, or 96. For certain applications,
4669:
4659:
4452:
4412:
4405:
4390:
4385:
4200:
4020:
3543:
3332:
2703:
2142:
170:
47:
2363:
818:
4747:
4457:
4400:
4308:
3694:
3635:
3511:
3506:
3458:
2522:
1733:
4717:
4563:
4509:
4323:
3973:
3927:
3817:
3775:
3760:
3625:
3448:
3307:
2885:
2472:
2391:
1877:
1808:
127:
107:
92:
2648:
4679:
4603:
3993:
3897:
3847:
3822:
3528:
3411:
3337:
3020:
3000:
2207:
RFC 4106 The Use of Galois/Counter Mode (GCM) in IPsec Encapsulating Security Payload (ESP)
2022:
1884:
103:
8:
4432:
4318:
4195:
4083:
3983:
3902:
3862:
3842:
3491:
3468:
2787:
1101:
If it is necessary to parallelize the hash computation, this can be done by interleaving
156:, and so it is essential that a different IV is used for each stream that is encrypted.
4548:
4532:
4474:
4252:
4236:
4185:
3770:
3476:
3384:
3096:
3025:
2995:
2940:
1812:
1801:
1081:
174:
2464:
2184:
Recommendation for Block Cipher Modes of Operation: Galois/Counter Mode (GCM) and GMAC
1718:
Recommendation for Block Cipher Modes of Operation: Galois/Counter Mode (GCM) and GMAC
4608:
4598:
4464:
4129:
3196:
2895:
2855:
2850:
2817:
2777:
2725:
2540:
2417:
2342:
2278:"Algorithm Registration - Computer Security Objects Register | CSRC | CSRC"
2158:
2088:
1873:
1853:
2603:: The Use of Galois/Counter Mode (GCM) in IPsec Encapsulating Security Payload (ESP)
4543:
4395:
4216:
4170:
3932:
3568:
3463:
3342:
3201:
3081:
3050:
2744:
2532:
2460:
2409:
2334:
2150:
2080:
126:, blocks are numbered sequentially, and then this block number is combined with an
2364:"AES-GCM for Efficient Authenticated Encryption – Ending the Reign of HMAC-SHA-1?"
180:
4231:
4180:
4175:
3963:
3678:
3415:
3399:
3388:
3322:
3281:
3246:
3176:
3156:
3030:
2910:
2905:
2860:
2536:
2413:
2408:. Lecture Notes in Computer Science. Vol. 6498. Springer. pp. 311–327.
2154:
2084:
2079:. Lecture Notes in Computer Science. Vol. 4727. Springer. pp. 227–238.
1973:
may be compromised entirely and the authentication assurance is completely lost.
2621:
2614:
2607:
2600:
2338:
4618:
4538:
4494:
4437:
4422:
4221:
3949:
3553:
3501:
3312:
3297:
3236:
3231:
3116:
2865:
111:
2627:
2333:. Lecture Notes in Computer Science. Vol. 5747. Springer. pp. 1–17.
1795:
GCM requires one block cipher operation and one 128-bit multiplication in the
210:, which use chaining modes. The GF(2) field used is defined by the polynomial
4736:
4699:
4654:
4613:
4593:
4484:
4442:
4417:
4313:
4190:
3548:
3496:
3375:
3357:
3146:
3121:
3111:
2935:
2925:
2772:
2594:
2392:"Fast Cryptographic Computation on Intel Architecture via Function Stitching"
1819:
1780:
1749:
153:
87:) is an authentication-only variant of the GCM which can form an incremental
3892:
2501:"The Galois/Counter Mode of Operation (GCM) Intellectual Property Statement"
4649:
4489:
4479:
4469:
4427:
4371:
3481:
3302:
3266:
3131:
3010:
2965:
2797:
2749:
2699:
1796:
1764:
1729:
1443:
If the length of the IV is not 96, the GHASH function is used to calculate
372:
203:
74:
70:
51:
31:
2624:: Addition of the Camellia Cipher Suites to Transport Layer Security (TLS)
2610:: The Use of Galois Message Authentication Code (GMAC) in IPsec ESP and AH
4628:
4303:
4149:
4078:
4074:
3091:
3086:
2970:
2044:
141:
2254:
Addition of the Camellia Cipher Suites to Transport Layer Security (TLS)
2218:
The Use of Galois Message Authentication Code (GMAC) in IPsec ESP and AH
4588:
4558:
4553:
4514:
3523:
3241:
3181:
3065:
3060:
3005:
2875:
2738:
2291:
2109:
1753:
1702:
384:
160:
149:
1925:
Like with any message authentication code, if the adversary chooses a
4578:
3978:
3857:
3256:
3251:
3141:
3055:
2950:
2930:
2230:
AES Galois Counter Mode for the Secure Shell Transport Layer Protocol
1864:
According to the authors' statement, GCM is unencumbered by patents.
145:
3765:
2575:"Cycling Attacks on GCM, GHASH and Other Polynomial MACs and Hashes"
2143:"CWC: A High-Performance Conventional Authenticated Encryption Mode"
2074:
4623:
4583:
4257:
4154:
4139:
4134:
4124:
4088:
4008:
3922:
3802:
3594:
3558:
3352:
3015:
2890:
2870:
2782:
1981:
1737:
1706:
2574:
4093:
4049:
3827:
3261:
3211:
3171:
3161:
3106:
3101:
2945:
2754:
2649:
AES-GCM and AES-CCM Authenticated Encryption in Secure RTP (SRTP)
1832:
1784:
66:
4499:
4262:
4003:
3998:
3968:
3958:
3917:
3912:
3907:
3887:
3882:
3852:
3837:
3797:
3599:
3221:
3216:
3151:
3136:
3126:
3071:
3045:
3040:
3035:
2915:
2900:
2638:
2521:. Lecture Notes in Computer Science. Vol. 3348. Springer.
1745:
3988:
3877:
3832:
3780:
3737:
3732:
3726:
3317:
3276:
3226:
3206:
3191:
2980:
2960:
2880:
2845:
1760:
1741:
811:) mod 128 is the bit length of the final block of
799:) mod 128 is the bit length of the final block of
4103:
4098:
4069:
4064:
4028:
3166:
3075:
2990:
2985:
2975:
2955:
2827:
2812:
1713:
1684:
1286:
1046:
758:
65:
GCM uses a block cipher with block size 128 bits (commonly
1716:
announced the release of NIST Special Publication 800-38D
1063:
The second form is an efficient iterative algorithm (each
3872:
3867:
3720:
3271:
3186:
2807:
2802:
2572:
2130:
Note that there is a typo in the formulas in the article.
77:
GF(2) to compute the authentication tag; hence the name.
2595:
NIST Special Publication SP800-38D defining GCM and GMAC
2457:
2331:
Cryptographic Hardware and Embedded Systems - CHES 2009
783:) are the 64-bit representations of the bit lengths of
346:{\displaystyle \operatorname {GHASH} (H,A,C)=X_{m+n+1}}
159:
The ciphertext blocks are considered coefficients of a
4525:
Cryptographically secure pseudorandom number generator
2617:: AES Galois Counter Mode (GCM) Cipher Suites for TLS
2141:
Kohno, Tadayoshi; Viega, John; Whiting, Doug (2004).
1456:
1114:
854:
821:
444:
379:
is data which is only authenticated (not encrypted),
290:
219:
2698:
2660:
2632:
59:
authenticated encryption with associated data (AEAD)
2566:
2242:
AES Galois Counter Mode (GCM) Cipher Suites for TLS
2064:
AES Galois Counter Mode (GCM) Cipher Suites for TLS
1887:). For any given key, GCM is limited to encrypting
2628:IEEE 802.1AE – Media Access Control (MAC) Security
1880:for every encryption performed with the same key (
1690:
1432:
1052:
827:
764:
345:
270:
102:and implementing GCM can make efficient use of an
2266:The Transport Layer Security protocol version 1.3
2176:
2174:
2140:
163:which is then evaluated at a key-dependent point
4734:
371:, a string of 128 zero bits encrypted using the
152:. Like all counter modes, this is essentially a
1856:are less complex compared to AES accelerators.
27:Authenticated encryption mode for block ciphers
2305:Gueron, Shay; Kounavis, Michael (April 2014).
2304:
2171:
4356:
3664:
2684:
2328:
1777:Commercial National Security Algorithm (CNSA)
173:. The result is then encrypted, producing an
2180:
2114:"The Galois/Counter Mode of Operation (GCM)"
1804:per the original NIST submission, or both).
1771:1.2 and TLS 1.3. AES-GCM is included in the
1705:and David A. McGrew to be an improvement to
114:that hamper its efficiency and performance.
2516:
2403:
2292:"Why SoftEther VPN – SoftEther VPN Project"
2107:
73:for encryption, and uses arithmetic in the
4363:
4349:
3671:
3657:
2691:
2677:
2656:The Galois/Counter Mode of Operation (GCM)
2506:. Computer Security Resource Center, NIST.
2438:"IoT Security Part 6: Galois Counter Mode"
2526:
2017:). Saarinen also described a GCM variant
1670:
1669:
106:or a hardware pipeline. By contrast, the
2573:Markku-Juhani O. Saarinen (2011-04-20).
1720:making GCM and GMAC official standards.
179:
140:. The result of this encryption is then
2498:
2406:Progress in Cryptology - INDOCRYPT 2010
1899:, is a security parameter. In general,
271:{\displaystyle x^{128}+x^{7}+x^{2}+x+1}
130:(IV) and encrypted with a block cipher
14:
4735:
2633:IEEE Security in Storage Working Group
2145:. In Roy, Bimal; Meier, Willi (eds.).
835:denotes concatenation of bit strings.
4344:
3652:
2672:
193:
2371:Workshop on Real-World Cryptography
1775:and its latest replacement in 2018
1665:
399:is the number of 128-bit blocks in
391:is the number of 128-bit blocks in
24:
2643:Fibre Channel – Security Protocols
2361:
1476:
1473:
1470:
1467:
1464:
1461:
1458:
117:
81:Galois Message Authentication Code
25:
4769:
2588:
2465:10.1109/SOCC46988.2019.1570548289
2190:(Technical report). NIST. 800-38D
4758:Authenticated-encryption schemes
4713:
4712:
4370:
2561:Authentication Weaknesses in GCM
4743:Block cipher modes of operation
2553:
2510:
2499:McGrew, David A.; Viega, John.
2492:
2451:
2430:
2397:
2384:
2355:
2322:
2298:
2284:
2270:
2258:
2246:
1779:suite. GCM mode is used in the
403:(rounded up), and the variable
110:(CBC) mode of operation incurs
91:. Both GCM and GMAC can accept
4574:Information-theoretic security
4268:NIST hash function competition
2639:INCITS T11 Technical Committee
2635:developed the P1619.1 standard
2234:
2222:
2210:
2201:
2134:
2101:
2068:
2056:
2040:Block cipher mode of operation
1790:
1783:server and client, as well as
1662:
1653:
1622:
1613:
1541:
1532:
724:
718:
706:
700:
315:
297:
13:
1:
2519:Proceedings of INDOCRYPT 2004
2181:Dworkin, Morris (2007–2011).
2050:
1845:instruction-level parallelism
1084:to the first. Only the final
4753:Message authentication codes
4273:Password Hashing Competition
3684:message authentication codes
3680:Cryptographic hash functions
2537:10.1007/978-3-540-30556-9_27
2414:10.1007/978-3-642-17401-8_22
2155:10.1007/978-3-540-25937-4_26
2085:10.1007/978-3-540-74735-2_16
1872:GCM is proven secure in the
1752:Security Protocols (FC-SP),
1732:(MACsec) Ethernet security,
198:GCM combines the well-known
7:
4690:Message authentication code
4645:Cryptographic hash function
4448:Cryptographic hash function
4227:Merkle–Damgård construction
2339:10.1007/978-3-642-04138-9_1
2028:
2019:Sophie Germain Counter Mode
1867:
89:message authentication code
10:
4774:
4569:Harvest now, decrypt later
1859:
1852:hardware accelerators for
1707:Carter–Wegman counter mode
828:{\displaystyle \parallel }
4708:
4685:Post-quantum cryptography
4637:
4378:
4340:
4291:
4245:
4209:
4163:
4112:
4040:
4017:
3946:
3790:
3751:
3713:
3690:
3648:
3618:
3582:
3574:Time/memory/data tradeoff
3371:
3290:
2836:
2763:
2711:
2668:
2664:
2579:Cryptology ePrint Archive
1813:carry-less multiplication
4675:Quantum key distribution
4665:Authenticated encryption
4520:Random number generation
4021:key derivation functions
3362:Whitening transformation
2147:Fast Software Encryption
2035:Authenticated encryption
1773:NSA Suite B Cryptography
1736:Wifi security protocol,
1728:GCM mode is used in the
4670:Public-key cryptography
4660:Symmetric-key algorithm
4453:Key derivation function
4413:Cryptographic primitive
4406:Authentication protocol
4391:Outline of cryptography
4386:History of cryptography
4299:Hash-based cryptography
4201:Length extension attack
3333:Confusion and diffusion
1980:Saarinen described GCM
1874:concrete security model
1080:) produced by applying
171:finite field arithmetic
4458:Secure Hash Algorithms
4401:Cryptographic protocol
4309:Message authentication
2480:Cite journal requires
1991:for messages that are
1961:⋅2. If the tag length
1945:for arbitrarily large
1723:
1692:
1434:
1331:
1054:
888:
829:
766:
347:
272:
190:
93:initialization vectors
4564:End-to-end encryption
4510:Cryptojacking malware
3626:Initialization vector
2023:Sophie Germain primes
1878:initialization vector
1693:
1435:
1311:
1055:
868:
830:
767:
348:
273:
183:
128:initialization vector
108:cipher block chaining
95:of arbitrary length.
4680:Quantum cryptography
4604:Trusted timestamping
3405:3-subset MITM attack
3021:Intel Cascade Cipher
3001:Hasty Pudding cipher
1885:stream cipher attack
1807:Intel has added the
1701:GCM was designed by
1454:
1112:
852:
819:
442:
288:
217:
104:instruction pipeline
4433:Cryptographic nonce
4196:Side-channel attack
3444:Differential-linear
1787:since version 2.4.
1370:
1205:
1137:
1098:remains an output.
648:
528:
100:parallel processing
36:Galois/Counter Mode
18:Galois/Counter mode
4549:Subliminal channel
4533:Pseudorandom noise
4475:Key (cryptography)
4253:CAESAR Competition
4237:HAIFA construction
4186:Brute-force attack
3517:Differential-fault
2735:internal mechanics
2394:Intel Corp. (2010)
2108:McGrew, David A.;
1712:In November 2007,
1688:
1683:
1430:
1428:
1337:
1285:
1181:
1119:
1050:
1045:
825:
762:
757:
634:
514:
425:is defined below.
343:
268:
194:Mathematical basis
191:
175:authentication tag
4730:
4729:
4726:
4725:
4609:Key-based routing
4599:Trapdoor function
4465:Digital signature
4336:
4335:
4332:
4331:
4130:ChaCha20-Poly1305
3947:Password hashing/
3644:
3643:
3631:Mode of operation
3308:Lai–Massey scheme
2546:978-3-540-30556-9
2423:978-3-642-17400-1
2348:978-3-642-04138-9
2164:978-3-540-25937-4
2094:978-3-540-74734-5
1854:ChaCha20-Poly1305
1756:.1 tape storage,
1679:
1633:
1524:
1242:
1161:
1008:
943:
807: = len(
795: = len(
732:
673:
589:
553:
481:
44:mode of operation
16:(Redirected from
4765:
4716:
4715:
4544:Insecure channel
4396:Classical cipher
4365:
4358:
4351:
4342:
4341:
4217:Avalanche effect
4171:Collision attack
3714:Common functions
3673:
3666:
3659:
3650:
3649:
3502:Power-monitoring
3343:Avalanche effect
3051:Khufu and Khafre
2704:security summary
2693:
2686:
2679:
2670:
2669:
2666:
2665:
2662:
2661:
2583:
2582:
2570:
2564:
2559:Niels Ferguson,
2557:
2551:
2550:
2530:
2514:
2508:
2507:
2505:
2496:
2490:
2489:
2483:
2478:
2476:
2468:
2455:
2449:
2448:
2446:
2445:
2434:
2428:
2427:
2401:
2395:
2388:
2382:
2381:
2379:
2377:
2368:
2359:
2353:
2352:
2326:
2320:
2319:
2317:
2316:
2311:
2302:
2296:
2295:
2288:
2282:
2281:
2274:
2268:
2262:
2256:
2250:
2244:
2238:
2232:
2226:
2220:
2214:
2208:
2205:
2199:
2198:
2196:
2195:
2189:
2178:
2169:
2168:
2138:
2132:
2128:
2126:
2124:
2118:
2105:
2099:
2098:
2072:
2066:
2060:
2021:(SGCM) based on
2016:
2005:
1997:
1990:
1944:
1921:
1914:
1890:
1697:
1695:
1694:
1689:
1687:
1686:
1680:
1677:
1634:
1632: with
1631:
1629:
1625:
1609:
1608:
1596:
1595:
1583:
1582:
1525:
1522:
1512:
1511:
1482:
1439:
1437:
1436:
1431:
1429:
1425:
1424:
1400:
1396:
1395:
1394:
1369:
1368:
1360:
1330:
1325:
1303:
1302:
1289:
1288:
1243:
1240:
1236:
1235:
1223:
1219:
1218:
1217:
1204:
1203:
1195:
1162:
1159:
1136:
1135:
1127:
1059:
1057:
1056:
1051:
1049:
1048:
1009:
1006:
996:
992:
991:
990:
978:
977:
944:
941:
923:
922:
898:
897:
887:
882:
864:
863:
834:
832:
831:
826:
791:, respectively,
771:
769:
768:
763:
761:
760:
733:
730:
674:
671:
667:
666:
647:
642:
590:
587:
583:
582:
554:
551:
547:
546:
527:
522:
482:
479:
475:
474:
454:
453:
424:
352:
350:
349:
344:
342:
341:
277:
275:
274:
269:
255:
254:
242:
241:
229:
228:
168:
135:
21:
4773:
4772:
4768:
4767:
4766:
4764:
4763:
4762:
4733:
4732:
4731:
4722:
4704:
4633:
4374:
4369:
4328:
4287:
4246:Standardization
4241:
4232:Sponge function
4205:
4181:Birthday attack
4176:Preimage attack
4159:
4115:
4108:
4036:
4019:
4018:General purpose
4013:
3948:
3942:
3791:Other functions
3786:
3753:SHA-3 finalists
3747:
3709:
3686:
3677:
3640:
3614:
3583:Standardization
3578:
3507:Electromagnetic
3459:Integral/Square
3416:Piling-up lemma
3400:Biclique attack
3389:EFF DES cracker
3373:
3367:
3298:Feistel network
3286:
2911:CIPHERUNICORN-E
2906:CIPHERUNICORN-A
2838:
2832:
2765:
2759:
2713:
2707:
2697:
2591:
2586:
2571:
2567:
2558:
2554:
2547:
2515:
2511:
2503:
2497:
2493:
2481:
2479:
2470:
2469:
2456:
2452:
2443:
2441:
2436:
2435:
2431:
2424:
2402:
2398:
2389:
2385:
2375:
2373:
2366:
2360:
2356:
2349:
2327:
2323:
2314:
2312:
2309:
2303:
2299:
2290:
2289:
2285:
2276:
2275:
2271:
2263:
2259:
2251:
2247:
2239:
2235:
2227:
2223:
2215:
2211:
2206:
2202:
2193:
2191:
2187:
2179:
2172:
2165:
2139:
2135:
2122:
2120:
2116:
2106:
2102:
2095:
2073:
2069:
2061:
2057:
2053:
2031:
2007:
2000:
1992:
1985:
1938:
1916:
1909:
1888:
1870:
1862:
1802:Horner's method
1793:
1734:WPA3-Enterprise
1726:
1682:
1681:
1676:
1674:
1630:
1604:
1600:
1591:
1587:
1578:
1574:
1564:
1560:
1551:
1550:
1521:
1519:
1507:
1503:
1487:
1486:
1457:
1455:
1452:
1451:
1427:
1426:
1408:
1404:
1378:
1374:
1362:
1361:
1341:
1336:
1332:
1326:
1315:
1304:
1298:
1294:
1291:
1290:
1284:
1283:
1239:
1237:
1231:
1227:
1213:
1209:
1197:
1196:
1185:
1180:
1176:
1173:
1172:
1158:
1156:
1146:
1145:
1138:
1129:
1128:
1123:
1115:
1113:
1110:
1109:
1097:
1082:Horner's method
1079:
1068:
1044:
1043:
1005:
1003:
986:
982:
967:
963:
962:
958:
955:
954:
940:
938:
928:
927:
906:
902:
893:
889:
883:
872:
859:
855:
853:
850:
849:
845:is defined as:
843:
820:
817:
816:
756:
755:
729:
727:
691:
690:
670:
668:
656:
652:
643:
638:
631:
630:
586:
584:
572:
568:
565:
564:
550:
548:
536:
532:
523:
518:
511:
510:
478:
476:
470:
466:
459:
458:
449:
445:
443:
440:
439:
433:
411:
408:
365:
325:
321:
289:
286:
285:
250:
246:
237:
233:
224:
220:
218:
215:
214:
196:
188:
185:
164:
148:to produce the
131:
122:Like in normal
120:
118:Basic operation
112:pipeline stalls
28:
23:
22:
15:
12:
11:
5:
4771:
4761:
4760:
4755:
4750:
4745:
4728:
4727:
4724:
4723:
4721:
4720:
4709:
4706:
4705:
4703:
4702:
4697:
4695:Random numbers
4692:
4687:
4682:
4677:
4672:
4667:
4662:
4657:
4652:
4647:
4641:
4639:
4635:
4634:
4632:
4631:
4626:
4621:
4619:Garlic routing
4616:
4611:
4606:
4601:
4596:
4591:
4586:
4581:
4576:
4571:
4566:
4561:
4556:
4551:
4546:
4541:
4539:Secure channel
4536:
4530:
4529:
4528:
4517:
4512:
4507:
4502:
4497:
4495:Key stretching
4492:
4487:
4482:
4477:
4472:
4467:
4462:
4461:
4460:
4455:
4450:
4440:
4438:Cryptovirology
4435:
4430:
4425:
4423:Cryptocurrency
4420:
4415:
4410:
4409:
4408:
4398:
4393:
4388:
4382:
4380:
4376:
4375:
4368:
4367:
4360:
4353:
4345:
4338:
4337:
4334:
4333:
4330:
4329:
4327:
4326:
4321:
4316:
4311:
4306:
4301:
4295:
4293:
4289:
4288:
4286:
4285:
4280:
4275:
4270:
4265:
4260:
4255:
4249:
4247:
4243:
4242:
4240:
4239:
4234:
4229:
4224:
4222:Hash collision
4219:
4213:
4211:
4207:
4206:
4204:
4203:
4198:
4193:
4188:
4183:
4178:
4173:
4167:
4165:
4161:
4160:
4158:
4157:
4152:
4147:
4142:
4137:
4132:
4127:
4121:
4119:
4110:
4109:
4107:
4106:
4101:
4096:
4091:
4086:
4081:
4072:
4067:
4062:
4057:
4052:
4046:
4044:
4038:
4037:
4035:
4034:
4031:
4025:
4023:
4015:
4014:
4012:
4011:
4006:
4001:
3996:
3991:
3986:
3981:
3976:
3971:
3966:
3961:
3955:
3953:
3950:key stretching
3944:
3943:
3941:
3940:
3935:
3930:
3925:
3920:
3915:
3910:
3905:
3900:
3895:
3890:
3885:
3880:
3875:
3870:
3865:
3860:
3855:
3850:
3845:
3840:
3835:
3830:
3825:
3820:
3815:
3810:
3805:
3800:
3794:
3792:
3788:
3787:
3785:
3784:
3778:
3773:
3768:
3763:
3757:
3755:
3749:
3748:
3746:
3745:
3740:
3735:
3730:
3724:
3717:
3715:
3711:
3710:
3708:
3707:
3702:
3697:
3691:
3688:
3687:
3676:
3675:
3668:
3661:
3653:
3646:
3645:
3642:
3641:
3639:
3638:
3633:
3628:
3622:
3620:
3616:
3615:
3613:
3612:
3607:
3602:
3597:
3592:
3586:
3584:
3580:
3579:
3577:
3576:
3571:
3566:
3561:
3556:
3551:
3546:
3541:
3536:
3531:
3526:
3521:
3520:
3519:
3514:
3509:
3504:
3499:
3489:
3484:
3479:
3474:
3466:
3461:
3456:
3449:Distinguishing
3446:
3441:
3440:
3439:
3434:
3429:
3419:
3409:
3408:
3407:
3402:
3392:
3381:
3379:
3369:
3368:
3366:
3365:
3355:
3350:
3345:
3340:
3335:
3330:
3325:
3320:
3315:
3313:Product cipher
3310:
3305:
3300:
3294:
3292:
3288:
3287:
3285:
3284:
3279:
3274:
3269:
3264:
3259:
3254:
3249:
3244:
3239:
3234:
3229:
3224:
3219:
3214:
3209:
3204:
3199:
3194:
3189:
3184:
3179:
3174:
3169:
3164:
3159:
3154:
3149:
3144:
3139:
3134:
3129:
3124:
3119:
3114:
3109:
3104:
3099:
3094:
3089:
3084:
3079:
3068:
3063:
3058:
3053:
3048:
3043:
3038:
3033:
3028:
3023:
3018:
3013:
3008:
3003:
2998:
2993:
2988:
2983:
2978:
2973:
2968:
2963:
2958:
2953:
2948:
2943:
2941:Cryptomeria/C2
2938:
2933:
2928:
2923:
2918:
2913:
2908:
2903:
2898:
2893:
2888:
2883:
2878:
2873:
2868:
2863:
2858:
2853:
2848:
2842:
2840:
2834:
2833:
2831:
2830:
2825:
2820:
2815:
2810:
2805:
2800:
2795:
2790:
2785:
2780:
2775:
2769:
2767:
2761:
2760:
2758:
2757:
2752:
2747:
2742:
2728:
2723:
2717:
2715:
2709:
2708:
2696:
2695:
2688:
2681:
2673:
2659:
2658:
2652:
2651:
2646:
2636:
2630:
2625:
2618:
2611:
2604:
2597:
2590:
2589:External links
2587:
2585:
2584:
2565:
2552:
2545:
2509:
2491:
2482:|journal=
2450:
2429:
2422:
2396:
2383:
2362:Gueron, Shay.
2354:
2347:
2321:
2297:
2283:
2280:. 24 May 2016.
2269:
2257:
2245:
2233:
2221:
2209:
2200:
2170:
2163:
2133:
2100:
2093:
2067:
2054:
2052:
2049:
2048:
2047:
2042:
2037:
2030:
2027:
1969:. Eventually,
1869:
1866:
1861:
1858:
1792:
1789:
1725:
1722:
1699:
1698:
1685:
1675:
1673:
1668:
1664:
1661:
1658:
1655:
1652:
1649:
1646:
1643:
1640:
1637:
1628:
1624:
1621:
1618:
1615:
1612:
1607:
1603:
1599:
1594:
1590:
1586:
1581:
1577:
1573:
1570:
1567:
1563:
1559:
1556:
1553:
1552:
1549:
1546:
1543:
1540:
1537:
1534:
1531:
1528:
1520:
1518:
1515:
1510:
1506:
1502:
1499:
1496:
1493:
1492:
1490:
1485:
1481:
1478:
1475:
1472:
1469:
1466:
1463:
1460:
1441:
1440:
1423:
1420:
1417:
1414:
1411:
1407:
1403:
1399:
1393:
1390:
1387:
1384:
1381:
1377:
1373:
1367:
1364:
1359:
1356:
1353:
1350:
1347:
1344:
1340:
1335:
1329:
1324:
1321:
1318:
1314:
1310:
1307:
1305:
1301:
1297:
1293:
1292:
1287:
1282:
1279:
1276:
1273:
1270:
1267:
1264:
1261:
1258:
1255:
1252:
1249:
1246:
1238:
1234:
1230:
1226:
1222:
1216:
1212:
1208:
1202:
1199:
1194:
1191:
1188:
1184:
1179:
1175:
1174:
1171:
1168:
1165:
1157:
1155:
1152:
1151:
1149:
1144:
1141:
1139:
1134:
1131:
1126:
1122:
1118:
1117:
1088:
1074:
1066:
1061:
1060:
1047:
1042:
1039:
1036:
1033:
1030:
1027:
1024:
1021:
1018:
1015:
1012:
1004:
1002:
999:
995:
989:
985:
981:
976:
973:
970:
966:
961:
957:
956:
953:
950:
947:
939:
937:
934:
933:
931:
926:
921:
918:
915:
912:
909:
905:
901:
896:
892:
886:
881:
878:
875:
871:
867:
862:
858:
841:
824:
773:
772:
759:
754:
751:
748:
745:
742:
739:
736:
728:
726:
723:
720:
717:
714:
711:
708:
705:
702:
699:
696:
693:
692:
689:
686:
683:
680:
677:
669:
665:
662:
659:
655:
651:
646:
641:
637:
633:
632:
629:
626:
623:
620:
617:
614:
611:
608:
605:
602:
599:
596:
593:
585:
581:
578:
575:
571:
567:
566:
563:
560:
557:
549:
545:
542:
539:
535:
531:
526:
521:
517:
513:
512:
509:
506:
503:
500:
497:
494:
491:
488:
485:
477:
473:
469:
465:
464:
462:
457:
452:
448:
431:
406:
395:(rounded up),
363:
354:
353:
340:
337:
334:
331:
328:
324:
320:
317:
314:
311:
308:
305:
302:
299:
296:
293:
279:
278:
267:
264:
261:
258:
253:
249:
245:
240:
236:
232:
227:
223:
195:
192:
119:
116:
69:) operated in
50:cryptographic
26:
9:
6:
4:
3:
2:
4770:
4759:
4756:
4754:
4751:
4749:
4748:Finite fields
4746:
4744:
4741:
4740:
4738:
4719:
4711:
4710:
4707:
4701:
4700:Steganography
4698:
4696:
4693:
4691:
4688:
4686:
4683:
4681:
4678:
4676:
4673:
4671:
4668:
4666:
4663:
4661:
4658:
4656:
4655:Stream cipher
4653:
4651:
4648:
4646:
4643:
4642:
4640:
4636:
4630:
4627:
4625:
4622:
4620:
4617:
4615:
4614:Onion routing
4612:
4610:
4607:
4605:
4602:
4600:
4597:
4595:
4594:Shared secret
4592:
4590:
4587:
4585:
4582:
4580:
4577:
4575:
4572:
4570:
4567:
4565:
4562:
4560:
4557:
4555:
4552:
4550:
4547:
4545:
4542:
4540:
4537:
4534:
4531:
4526:
4523:
4522:
4521:
4518:
4516:
4513:
4511:
4508:
4506:
4503:
4501:
4498:
4496:
4493:
4491:
4488:
4486:
4485:Key generator
4483:
4481:
4478:
4476:
4473:
4471:
4468:
4466:
4463:
4459:
4456:
4454:
4451:
4449:
4446:
4445:
4444:
4443:Hash function
4441:
4439:
4436:
4434:
4431:
4429:
4426:
4424:
4421:
4419:
4418:Cryptanalysis
4416:
4414:
4411:
4407:
4404:
4403:
4402:
4399:
4397:
4394:
4392:
4389:
4387:
4384:
4383:
4381:
4377:
4373:
4366:
4361:
4359:
4354:
4352:
4347:
4346:
4343:
4339:
4325:
4322:
4320:
4317:
4315:
4314:Proof of work
4312:
4310:
4307:
4305:
4302:
4300:
4297:
4296:
4294:
4290:
4284:
4281:
4279:
4276:
4274:
4271:
4269:
4266:
4264:
4261:
4259:
4256:
4254:
4251:
4250:
4248:
4244:
4238:
4235:
4233:
4230:
4228:
4225:
4223:
4220:
4218:
4215:
4214:
4212:
4208:
4202:
4199:
4197:
4194:
4192:
4191:Rainbow table
4189:
4187:
4184:
4182:
4179:
4177:
4174:
4172:
4169:
4168:
4166:
4162:
4156:
4153:
4151:
4148:
4146:
4143:
4141:
4138:
4136:
4133:
4131:
4128:
4126:
4123:
4122:
4120:
4117:
4114:Authenticated
4111:
4105:
4102:
4100:
4097:
4095:
4092:
4090:
4087:
4085:
4082:
4080:
4076:
4073:
4071:
4068:
4066:
4063:
4061:
4058:
4056:
4053:
4051:
4048:
4047:
4045:
4043:
4042:MAC functions
4039:
4032:
4030:
4027:
4026:
4024:
4022:
4016:
4010:
4007:
4005:
4002:
4000:
3997:
3995:
3992:
3990:
3987:
3985:
3982:
3980:
3977:
3975:
3972:
3970:
3967:
3965:
3962:
3960:
3957:
3956:
3954:
3951:
3945:
3939:
3936:
3934:
3931:
3929:
3926:
3924:
3921:
3919:
3916:
3914:
3911:
3909:
3906:
3904:
3901:
3899:
3896:
3894:
3891:
3889:
3886:
3884:
3881:
3879:
3876:
3874:
3871:
3869:
3866:
3864:
3861:
3859:
3856:
3854:
3851:
3849:
3846:
3844:
3841:
3839:
3836:
3834:
3831:
3829:
3826:
3824:
3821:
3819:
3816:
3814:
3811:
3809:
3806:
3804:
3801:
3799:
3796:
3795:
3793:
3789:
3782:
3779:
3777:
3774:
3772:
3769:
3767:
3764:
3762:
3759:
3758:
3756:
3754:
3750:
3744:
3741:
3739:
3736:
3734:
3731:
3729:(compromised)
3728:
3725:
3723:(compromised)
3722:
3719:
3718:
3716:
3712:
3706:
3705:Known attacks
3703:
3701:
3698:
3696:
3693:
3692:
3689:
3685:
3681:
3674:
3669:
3667:
3662:
3660:
3655:
3654:
3651:
3647:
3637:
3634:
3632:
3629:
3627:
3624:
3623:
3621:
3617:
3611:
3608:
3606:
3603:
3601:
3598:
3596:
3593:
3591:
3588:
3587:
3585:
3581:
3575:
3572:
3570:
3567:
3565:
3562:
3560:
3557:
3555:
3552:
3550:
3547:
3545:
3542:
3540:
3537:
3535:
3532:
3530:
3529:Interpolation
3527:
3525:
3522:
3518:
3515:
3513:
3510:
3508:
3505:
3503:
3500:
3498:
3495:
3494:
3493:
3490:
3488:
3485:
3483:
3480:
3478:
3475:
3473:
3472:
3467:
3465:
3462:
3460:
3457:
3454:
3450:
3447:
3445:
3442:
3438:
3435:
3433:
3430:
3428:
3425:
3424:
3423:
3420:
3417:
3413:
3410:
3406:
3403:
3401:
3398:
3397:
3396:
3393:
3390:
3386:
3383:
3382:
3380:
3377:
3376:cryptanalysis
3370:
3363:
3359:
3358:Key whitening
3356:
3354:
3351:
3349:
3346:
3344:
3341:
3339:
3336:
3334:
3331:
3329:
3326:
3324:
3321:
3319:
3316:
3314:
3311:
3309:
3306:
3304:
3301:
3299:
3296:
3295:
3293:
3289:
3283:
3280:
3278:
3275:
3273:
3270:
3268:
3265:
3263:
3260:
3258:
3255:
3253:
3250:
3248:
3245:
3243:
3240:
3238:
3235:
3233:
3230:
3228:
3225:
3223:
3220:
3218:
3215:
3213:
3210:
3208:
3205:
3203:
3200:
3198:
3195:
3193:
3190:
3188:
3185:
3183:
3180:
3178:
3175:
3173:
3170:
3168:
3165:
3163:
3160:
3158:
3155:
3153:
3150:
3148:
3147:New Data Seal
3145:
3143:
3140:
3138:
3135:
3133:
3130:
3128:
3125:
3123:
3120:
3118:
3115:
3113:
3110:
3108:
3105:
3103:
3100:
3098:
3095:
3093:
3090:
3088:
3085:
3083:
3080:
3077:
3073:
3069:
3067:
3064:
3062:
3059:
3057:
3054:
3052:
3049:
3047:
3044:
3042:
3039:
3037:
3034:
3032:
3029:
3027:
3024:
3022:
3019:
3017:
3014:
3012:
3009:
3007:
3004:
3002:
2999:
2997:
2994:
2992:
2989:
2987:
2984:
2982:
2979:
2977:
2974:
2972:
2969:
2967:
2964:
2962:
2959:
2957:
2954:
2952:
2949:
2947:
2944:
2942:
2939:
2937:
2934:
2932:
2929:
2927:
2924:
2922:
2919:
2917:
2914:
2912:
2909:
2907:
2904:
2902:
2899:
2897:
2894:
2892:
2889:
2887:
2886:BEAR and LION
2884:
2882:
2879:
2877:
2874:
2872:
2869:
2867:
2864:
2862:
2859:
2857:
2854:
2852:
2849:
2847:
2844:
2843:
2841:
2835:
2829:
2826:
2824:
2821:
2819:
2816:
2814:
2811:
2809:
2806:
2804:
2801:
2799:
2796:
2794:
2791:
2789:
2786:
2784:
2781:
2779:
2776:
2774:
2771:
2770:
2768:
2762:
2756:
2753:
2751:
2748:
2746:
2743:
2740:
2736:
2732:
2729:
2727:
2724:
2722:
2719:
2718:
2716:
2710:
2705:
2701:
2700:Block ciphers
2694:
2689:
2687:
2682:
2680:
2675:
2674:
2671:
2667:
2663:
2657:
2654:
2653:
2650:
2647:
2644:
2640:
2637:
2634:
2631:
2629:
2626:
2623:
2619:
2616:
2612:
2609:
2605:
2602:
2598:
2596:
2593:
2592:
2580:
2576:
2569:
2562:
2556:
2548:
2542:
2538:
2534:
2529:
2528:10.1.1.1.4591
2524:
2520:
2513:
2502:
2495:
2487:
2474:
2466:
2462:
2454:
2439:
2433:
2425:
2419:
2415:
2411:
2407:
2400:
2393:
2387:
2372:
2365:
2358:
2350:
2344:
2340:
2336:
2332:
2325:
2308:
2301:
2293:
2287:
2279:
2273:
2267:
2261:
2255:
2249:
2243:
2237:
2231:
2225:
2219:
2213:
2204:
2186:
2185:
2177:
2175:
2166:
2160:
2156:
2152:
2148:
2144:
2137:
2131:
2115:
2111:
2104:
2096:
2090:
2086:
2082:
2078:
2071:
2065:
2059:
2055:
2046:
2043:
2041:
2038:
2036:
2033:
2032:
2026:
2024:
2020:
2014:
2010:
2003:
1995:
1988:
1983:
1978:
1974:
1972:
1968:
1964:
1960:
1955:
1950:
1948:
1942:
1936:
1932:
1928:
1923:
1919:
1912:
1906:
1902:
1898:
1892:
1886:
1883:
1879:
1875:
1865:
1857:
1855:
1849:
1846:
1840:
1838:
1834:
1830:
1826:
1821:
1820:Timing-Attack
1816:
1814:
1810:
1805:
1803:
1798:
1788:
1786:
1782:
1781:SoftEther VPN
1778:
1774:
1770:
1766:
1762:
1759:
1755:
1751:
1750:Fibre Channel
1747:
1743:
1740:(also dubbed
1739:
1738:IEEE 802.11ad
1735:
1731:
1721:
1719:
1715:
1710:
1708:
1704:
1671:
1666:
1659:
1656:
1650:
1647:
1644:
1641:
1638:
1635:
1626:
1619:
1616:
1610:
1605:
1601:
1597:
1592:
1588:
1584:
1579:
1575:
1571:
1568:
1565:
1561:
1557:
1554:
1547:
1544:
1538:
1535:
1529:
1526:
1516:
1513:
1508:
1504:
1500:
1497:
1494:
1488:
1483:
1479:
1450:
1449:
1448:
1446:
1421:
1418:
1415:
1412:
1409:
1405:
1401:
1397:
1391:
1388:
1385:
1382:
1379:
1375:
1371:
1365:
1363:
1357:
1354:
1351:
1348:
1345:
1342:
1338:
1333:
1327:
1322:
1319:
1316:
1312:
1308:
1306:
1299:
1295:
1280:
1277:
1274:
1271:
1268:
1265:
1262:
1259:
1256:
1253:
1250:
1247:
1244:
1232:
1228:
1224:
1220:
1214:
1210:
1206:
1200:
1198:
1192:
1189:
1186:
1182:
1177:
1169:
1166:
1163:
1153:
1147:
1142:
1140:
1132:
1130:
1124:
1120:
1108:
1107:
1106:
1104:
1099:
1095:
1091:
1087:
1083:
1077:
1073:
1069:
1040:
1037:
1034:
1031:
1028:
1025:
1022:
1019:
1016:
1013:
1010:
1000:
997:
993:
987:
983:
979:
974:
971:
968:
964:
959:
951:
948:
945:
935:
929:
924:
919:
916:
913:
910:
907:
903:
899:
894:
890:
884:
879:
876:
873:
869:
865:
860:
856:
848:
847:
846:
844:
836:
822:
814:
810:
806:
802:
798:
794:
790:
786:
782:
778:
752:
749:
746:
743:
740:
737:
734:
721:
715:
712:
709:
703:
697:
694:
687:
684:
681:
678:
675:
663:
660:
657:
653:
649:
644:
639:
635:
627:
624:
621:
618:
615:
612:
609:
606:
603:
600:
597:
594:
591:
579:
576:
573:
569:
561:
558:
555:
543:
540:
537:
533:
529:
524:
519:
515:
507:
504:
501:
498:
495:
492:
489:
486:
483:
471:
467:
460:
455:
450:
446:
438:
437:
436:
434:
426:
422:
418:
414:
409:
402:
398:
394:
390:
386:
382:
378:
374:
370:
366:
359:
338:
335:
332:
329:
326:
322:
318:
312:
309:
306:
303:
300:
294:
291:
284:
283:
282:
265:
262:
259:
256:
251:
247:
243:
238:
234:
230:
225:
221:
213:
212:
211:
209:
205:
201:
182:
178:
176:
172:
167:
162:
157:
155:
154:stream cipher
151:
147:
143:
139:
134:
129:
125:
115:
113:
109:
105:
101:
96:
94:
90:
86:
82:
78:
76:
72:
68:
63:
60:
55:
53:
52:block ciphers
49:
48:symmetric-key
45:
41:
37:
33:
19:
4650:Block cipher
4490:Key schedule
4480:Key exchange
4470:Kleptography
4428:Cryptosystem
4372:Cryptography
4144:
3534:Partitioning
3492:Side-channel
3470:
3437:Higher-order
3422:Differential
3303:Key schedule
2578:
2568:
2563:, 2005-05-20
2555:
2518:
2512:
2494:
2473:cite journal
2453:
2442:. Retrieved
2440:. 2016-05-06
2432:
2405:
2399:
2386:
2374:. Retrieved
2370:
2357:
2330:
2324:
2313:. Retrieved
2300:
2286:
2272:
2265:
2260:
2253:
2248:
2241:
2236:
2229:
2224:
2217:
2212:
2203:
2192:. Retrieved
2183:
2146:
2136:
2129:
2121:. Retrieved
2103:
2076:
2070:
2063:
2058:
2012:
2008:
2001:
1993:
1986:
1979:
1975:
1970:
1966:
1962:
1958:
1953:
1951:
1946:
1940:
1934:
1930:
1926:
1924:
1917:
1910:
1904:
1900:
1896:
1893:
1881:
1871:
1863:
1850:
1841:
1829:Vlad Krasnov
1817:
1806:
1797:Galois field
1794:
1730:IEEE 802.1AE
1727:
1717:
1711:
1709:(CWC mode).
1700:
1444:
1442:
1102:
1100:
1093:
1089:
1085:
1075:
1071:
1064:
1062:
839:
837:
812:
808:
804:
800:
796:
792:
788:
784:
780:
776:
774:
429:
427:
420:
416:
412:
404:
400:
396:
392:
388:
380:
376:
373:block cipher
368:
361:
357:
355:
280:
204:Galois field
200:counter mode
197:
165:
158:
132:
124:counter mode
121:
97:
84:
80:
79:
75:Galois field
71:counter mode
64:
56:
39:
35:
32:cryptography
29:
4638:Mathematics
4629:Mix network
4304:Merkle tree
4292:Utilization
4278:NSA Suite B
3619:Utilization
3605:NSA Suite B
3590:AES process
3539:Rubber-hose
3477:Related-key
3385:Brute-force
2764:Less common
2581:. FSE 2012.
2119:. p. 5
2110:Viega, John
2045:AES-GCM-SIV
1839:libraries.
1825:Shay Gueron
1791:Performance
1763:standards,
1070:depends on
367:(0) is the
4737:Categories
4589:Ciphertext
4559:Decryption
4554:Encryption
4515:Ransomware
4116:encryption
3893:RadioGatún
3700:Comparison
3569:Chi-square
3487:Rotational
3427:Impossible
3348:Block size
3242:Spectr-H64
3066:Ladder-DES
3061:Kuznyechik
3006:Hierocrypt
2876:BassOmatic
2839:algorithms
2766:algorithms
2739:Triple DES
2714:algorithms
2444:2023-10-17
2376:8 February
2315:2023-09-01
2194:2015-08-18
2051:References
1754:IEEE P1619
1703:John Viega
779:) and len(
775:where len(
415:= 0, ...,
385:ciphertext
161:polynomial
150:ciphertext
136:, usually
4579:Plaintext
4033:KDF1/KDF2
3952:functions
3938:Whirlpool
3544:Black-bag
3464:Boomerang
3453:Known-key
3432:Truncated
3257:Threefish
3252:SXAL/MBAL
3142:MultiSwap
3097:MacGuffin
3056:KN-Cipher
2996:Grand Cru
2951:CS-Cipher
2931:COCONUT98
2641:works on
2620:RFC
2613:RFC
2606:RFC
2599:RFC
2523:CiteSeerX
2264:RFC 8446
2252:RFC 6367
2240:RFC 5288
2228:RFC 5647
2216:RFC 4543
2062:RFC 5288
1982:weak keys
1809:PCLMULQDQ
1744:), ANSI (
1678:otherwise
1651:
1645:−
1611:
1598:∥
1585:∥
1572:∥
1558:
1530:
1523:for
1514:∥
1501:∥
1445:Counter 0
1413:−
1402:⋅
1389:−
1372:⊕
1352:−
1313:∑
1278:−
1257:…
1241:for
1225:⋅
1207:⊕
1190:−
1167:≤
1160:for
1023:…
1007:for
998:⋅
980:⊕
972:−
942:for
911:−
900:⋅
870:∑
823:∥
731:for
716:
710:∥
698:
672:for
661:−
650:∥
645:∗
625:−
610:…
588:for
577:−
552:for
541:−
530:∥
525:∗
505:−
496:…
480:for
295:
146:plaintext
144:with the
4718:Category
4624:Kademlia
4584:Codetext
4527:(CSPRNG)
4505:Machines
4258:CRYPTREC
4089:Poly1305
4009:yescrypt
3923:Streebog
3803:CubeHash
3783:(winner)
3595:CRYPTREC
3559:Weak key
3512:Acoustic
3353:Key size
3197:Red Pike
3016:IDEA NXT
2896:Chiasmus
2891:CAST-256
2871:BaseKing
2856:Akelarre
2851:Adiantum
2818:Skipjack
2783:CAST-128
2778:Camellia
2726:Blowfish
2645:project.
2112:(2005).
2029:See also
1868:Security
1366:′
1201:′
1133:′
369:hash key
169:, using
4379:General
4164:Attacks
4094:SipHash
4050:CBC-MAC
3984:LM hash
3964:Balloon
3828:HAS-160
3636:Padding
3554:Rebound
3262:Treyfer
3212:SAVILLE
3172:PRESENT
3162:NOEKEON
3107:MAGENTA
3102:Madryga
3082:Lucifer
2946:CRYPTON
2755:Twofish
2745:Serpent
2123:20 July
1889:2 − 256
1860:Patents
1833:OpenSSL
1785:OpenVPN
1105:times:
383:is the
187:blocks.
67:AES-128
42:) is a
4500:Keygen
4324:Pepper
4263:NESSIE
4210:Design
4004:scrypt
3999:PBKDF2
3974:Catena
3969:bcrypt
3959:Argon2
3918:Snefru
3913:Shabal
3908:SWIFFT
3888:RIPEMD
3883:N-hash
3858:MASH-2
3853:MASH-1
3838:Kupyna
3798:BLAKE3
3781:Keccak
3766:Grøstl
3743:BLAKE2
3600:NESSIE
3549:Davies
3497:Timing
3412:Linear
3372:Attack
3291:Design
3282:Zodiac
3247:Square
3222:SHACAL
3217:SC2000
3177:Prince
3157:Nimbus
3152:NewDES
3137:MULTI2
3127:MISTY1
3070:LOKI (
3046:KHAZAD
3041:KeeLoq
3036:KASUMI
3031:Kalyna
2916:CLEFIA
2901:CIKS-1
2861:Anubis
2712:Common
2543:
2525:
2420:
2345:
2161:
2091:
1746:INCITS
815:, and
356:where
4535:(PRN)
4118:modes
3994:Makwa
3989:Lyra2
3979:crypt
3928:Tiger
3878:MDC-2
3833:HAVAL
3818:Fugue
3776:Skein
3761:BLAKE
3738:SHA-3
3733:SHA-2
3727:SHA-1
3482:Slide
3338:Round
3323:P-box
3318:S-box
3277:XXTEA
3237:Speck
3232:Simon
3227:SHARK
3207:SAFER
3192:REDOC
3117:Mercy
3076:89/91
3026:Iraqi
2991:G-DES
2981:FEA-M
2961:DES-X
2926:Cobra
2881:BATON
2866:Ascon
2846:3-Way
2837:Other
2504:(PDF)
2367:(PDF)
2310:(PDF)
2188:(PDF)
2117:(PDF)
2015:× 128
2004:= 128
1996:× 128
1761:IPsec
1742:WiGig
1555:GHASH
838:Then
292:GHASH
142:XORed
4319:Salt
4283:CNSA
4150:IAPM
4104:VMAC
4099:UMAC
4084:PMAC
4079:CMAC
4075:OMAC
4070:NMAC
4065:HMAC
4060:GMAC
4029:HKDF
3898:SIMD
3848:Lane
3823:GOST
3808:ECOH
3695:List
3682:and
3610:CNSA
3469:Mod
3395:MITM
3167:NUSH
3122:MESH
3112:MARS
2986:FROG
2976:FEAL
2956:DEAL
2936:Crab
2921:CMEA
2828:XTEA
2813:SEED
2793:IDEA
2788:GOST
2773:ARIA
2622:6367
2615:5288
2608:4543
2601:4106
2541:ISBN
2486:help
2418:ISBN
2378:2013
2343:ISBN
2159:ISBN
2125:2013
2089:ISBN
2006:and
1939:1 −
1920:= 64
1913:= 32
1835:and
1827:and
1758:IETF
1714:NIST
787:and
410:for
85:GMAC
46:for
4155:OCB
4145:GCM
4140:EAX
4135:CWC
4125:CCM
4055:DAA
3933:VSH
3903:SM3
3873:MD6
3868:MD4
3863:MD2
3843:LSH
3813:FSB
3721:MD5
3564:Tau
3524:XSL
3328:SPN
3272:xmx
3267:UES
3202:S-1
3187:RC2
3132:MMB
3011:ICE
2966:DFC
2823:TEA
2808:RC6
2803:RC5
2798:LEA
2750:SM4
2731:DES
2721:AES
2533:doi
2461:doi
2410:doi
2335:doi
2151:doi
2081:doi
1882:see
1837:NSS
1769:TLS
1765:SSH
1724:Use
1672:128
1667:mod
1648:len
1642:128
1602:len
1527:len
713:len
695:len
658:128
538:128
423:+ 1
226:128
208:CBC
138:AES
40:GCM
30:In
4739::
3771:JH
3092:M8
3087:M6
3074:,
3072:97
2971:E2
2737:,
2577:.
2539:.
2531:.
2477::
2475:}}
2471:{{
2416:.
2369:.
2341:.
2173:^
2157:.
2087:.
2025:.
2011:=
1989:⋅2
1943:⋅2
1767:,
1748:)
1606:64
1593:64
1548:96
1509:31
1447::
1096:+1
1078:−1
803:,
435::
419:+
387:,
375:,
360:=
34:,
4364:e
4357:t
4350:v
4077:/
3672:e
3665:t
3658:v
3471:n
3455:)
3451:(
3418:)
3414:(
3391:)
3387:(
3378:)
3374:(
3364:)
3360:(
3182:Q
3078:)
2741:)
2733:(
2706:)
2702:(
2692:e
2685:t
2678:v
2549:.
2535::
2488:)
2484:(
2467:.
2463::
2447:.
2426:.
2412::
2380:.
2351:.
2337::
2318:.
2294:.
2197:.
2167:.
2153::
2127:.
2097:.
2083::
2013:n
2009:l
2002:w
1994:n
1987:n
1971:H
1967:H
1963:t
1959:n
1954:n
1947:t
1941:n
1935:n
1931:n
1927:t
1918:t
1911:t
1905:t
1901:t
1897:t
1663:)
1660:V
1657:I
1654:(
1639:=
1636:s
1627:)
1623:)
1620:V
1617:I
1614:(
1589:0
1580:s
1576:0
1569:V
1566:I
1562:(
1545:=
1542:)
1539:V
1536:I
1533:(
1517:1
1505:0
1498:V
1495:I
1489:{
1484:=
1480:0
1477:r
1474:e
1471:t
1468:n
1465:u
1462:o
1459:C
1422:1
1419:+
1416:j
1410:k
1406:H
1398:)
1392:k
1386:j
1383:+
1380:i
1376:S
1358:k
1355:2
1349:j
1346:+
1343:i
1339:X
1334:(
1328:k
1323:1
1320:=
1317:j
1309:=
1300:i
1296:X
1281:k
1275:1
1272:+
1269:n
1266:+
1263:m
1260:,
1254:,
1251:1
1248:=
1245:i
1233:k
1229:H
1221:)
1215:i
1211:S
1193:k
1187:i
1183:X
1178:(
1170:0
1164:i
1154:0
1148:{
1143:=
1125:i
1121:X
1103:k
1094:n
1092:+
1090:m
1086:X
1076:i
1072:X
1067:i
1065:X
1041:1
1038:+
1035:n
1032:+
1029:m
1026:,
1020:,
1017:1
1014:=
1011:i
1001:H
994:)
988:i
984:S
975:1
969:i
965:X
960:(
952:0
949:=
946:i
936:0
930:{
925:=
920:1
917:+
914:j
908:i
904:H
895:j
891:S
885:i
880:1
877:=
874:j
866:=
861:i
857:X
842:i
840:X
813:C
809:C
805:u
801:A
797:A
793:v
789:C
785:A
781:C
777:A
753:1
750:+
747:n
744:+
741:m
738:=
735:i
725:)
722:C
719:(
707:)
704:A
701:(
688:n
685:+
682:m
679:=
676:i
664:u
654:0
640:n
636:C
628:1
622:n
619:+
616:m
613:,
607:,
604:1
601:+
598:m
595:=
592:i
580:m
574:i
570:C
562:m
559:=
556:i
544:v
534:0
520:m
516:A
508:1
502:m
499:,
493:,
490:1
487:=
484:i
472:i
468:A
461:{
456:=
451:i
447:S
432:i
430:S
421:n
417:m
413:i
407:i
405:X
401:C
397:n
393:A
389:m
381:C
377:A
364:k
362:E
358:H
339:1
336:+
333:n
330:+
327:m
323:X
319:=
316:)
313:C
310:,
307:A
304:,
301:H
298:(
266:1
263:+
260:x
257:+
252:2
248:x
244:+
239:7
235:x
231:+
222:x
166:H
133:E
83:(
38:(
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.