162:
43:
292:. The protocol enables users to securely exchange secret keys even if an opponent is monitoring that communication channel. The D–H key exchange protocol, however, does not by itself address authentication (i.e. the problem of being sure of the actual identity of the person or 'entity' at the other end of the communication channel). Authentication is crucial when an opponent can both monitor
259:
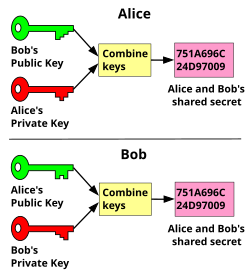
Known as the Diffie-Hellman key exchange, the encryption key can be openly communicated as it poses no risk to the confidentiality of encrypted messages. One party exchanges the keys to another party where they can then encrypt messages using the key and send back the cipher text. Only the decryption
247:
Public-key cryptography uses a two-key system, consisting of the public and the private keys, where messages are encrypted with one key and decrypted with another. It depends on the selected cryptographic algorithm which key—public or private—is used for encrypting messages, and which for decrypting.
357:
endorsements that “this public key belongs to this user”. As with notary endorsements, there can be mistakes or misunderstandings in such vouchings. Additionally, the notary itself can be untrusted. There have been several high-profile public failures by assorted certificate authorities.
319:
which serves for other users as a non-tamperable authentication of identity. The infrastructure is safe, unless the CA itself is compromised. In case it is, though, many PKIs provide a way to revoke certificates so other users will not trust them. Revoked certificates are usually put in
228:
utilized a single key to encrypt and decrypt messages. For two parties to communicate confidentially, they must first exchange the secret key so that each party is able to encrypt messages before sending, and decrypt received ones. This process is known as the key exchange.
169:
scheme, each party generates a public/private key pair and distributes the public key. After obtaining an authentic copy of each other's public keys, Alice and Bob can compute a shared secret offline. The shared secret can be used, for instance, as the key for a
349:
governments proposed establishing so-called “national CAs” whose certificates would be mandatory to install on citizens’ devices and, once installed and trusted, could be used for monitoring, intercepting, modifying, or blocking the encrypted internet traffic.
244:. If two parties cannot establish a secure initial key exchange, they won't be able to communicate securely without the risk of messages being intercepted and decrypted by a third party who acquired the key during the initial key exchange.
722:
219:
The key exchange problem describes ways to exchange whatever keys or other information are needed for establishing a secure communication channel so that no one else can obtain a copy. Historically, before the invention of
260:
key—in this case, it's the private key—can decrypt that message. At no time during the Diffie-Hellman key exchange is any sensitive information at risk of compromise, as opposed to symmetrical key exchange.
178:
If the sender and receiver wish to exchange encrypted messages, each must be equipped to encrypt messages to be sent and decrypt messages received. The nature of the equipping they require depends on the
570:
370:
system, which avoids central
Certificate Authorities entirely. Each user is responsible for getting a certificate from another user before using that certificate to communicate with the user.
272:' another's identity in any of several ways, this is not a trivial or easily solved problem, particularly when the two users involved have never met and know nothing about each other.
698:
342:
fallacy. For actual trustworthiness, personal verification that the certificate belongs to the CA and establishment of trust in the CA are required. This is usually not possible.
256:(DSA), the private key is used for authenticating them. The public key can be sent over non-secure channels or shared in public; the private key is only available to its owner.
418:) of a quantum state introduces perturbations in that state. Over many systems, these perturbations are detectable as noise by the receiver, making it possible to detect
268:
In principle, the only remaining problem was to be sure (or at least confident) that a public key actually belonged to its supposed owner. Because it is possible to '
594:
338:
This does nothing to solve the problem though, as the trustworthiness of the CA itself is still not guaranteed for any particular individual. It is a form of
545:
232:
The overarching problem with symmetrical cryptography, or single-key cryptography, is that it requires a secret key to be communicated through trusted
488:
311:(PKIs) have been proposed as a workaround for the problem of identity authentication. In their most usual implementation, each user applies to a “
634:
647:
653:
571:"Security Certificate Of The Republic Of Kazakhstan: The State Will Be Able To Control The Encrypted Internet Traffic Of Users"
390:
107:
79:
749:
731:
707:
498:
458:
126:
86:
759:
754:
415:
414:
exploits certain properties of quantum physics to ensure its security. It relies on the fact that observations (or
335:). Many commercial firms, as well as a few government departments, have established such certificate authorities.
453:
285:
166:
331:
or issued regulations encouraging PKIs by giving (more or less) legal effect to these digital certificates (see
668:
W. Diffie and M. E. Hellman, IEEE Transactions on
Information Theory, vol. IT-22, Nov. 1976, pp: 644–654.
423:
64:
93:
60:
321:
253:
75:
682:
Whitfield Diffie, Proceedings of the IEEE, vol. 76, no. 5, May 1988, pp: 560–577 (1.9MB PDF file)
308:
419:
411:
406:
297:
665:
339:
225:
221:
171:
53:
676:
Martin E. Hellman, Bailey W. Diffie, and Ralph C. Merkle, U.S. Patent #4,200,770, 29 April 1980
431:
281:
595:"The Kremlin reportedly wants to create a state-operated center for issuing SSL certificates"
312:
31:
427:
27:
100:
8:
515:
371:
316:
184:
723:
The Code Book: the evolution of secrecy from Mary Queen of Scots to quantum cryptography
443:
249:
151:
659:
727:
703:
689:
494:
375:
332:
393:
algorithms can perform a cryptographic key exchange utilizing knowledge of a user's
526:
353:
For those new to such things, these arrangements are best thought of as electronic
346:
463:
269:
693:
685:
448:
241:
237:
672:
619:
743:
636:
Symantec caught once again improperly issuing illegitimate HTTPS certificates
530:
484:
354:
203:
with the public/private key property, both will need the other's public key.
196:
367:
289:
161:
147:
20:
717:
711:
328:
300:
or MITM attacks) and was addressed in the fourth section of the paper.
200:
180:
679:
155:
42:
734:
513:
394:
188:
154:
are exchanged between two parties, allowing use of a cryptographic
430:
of quantum mechanics, the protocol assumes the availability of an
379:
233:
252:, the private key is used for decrypting messages, while in the
192:
382:
Internet
Standard) employ just such a web of trust mechanism.
482:
288:(D–H) based on concepts developed by Hellman's PhD student
280:
In 1976, Whitfield Diffie and Martin
Hellman published a
514:
Diffie, Whitfield; Hellman, Martin E. (November 1976).
385:
327:
Several countries and other jurisdictions have passed
195:, they will need appropriate keys. If the cipher is a
199:, both will need a copy of the same key. If it is an
211:
Key exchange is done either in-band or out-of-band.
67:. Unsourced material may be challenged and removed.
741:
648:The possibility of Non-Secret digital encryption
546:"Kazakhstan's Unsettling New Cybersecurity Plan"
366:At the other end of the conceptual range is the
296:messages within the communication channel (AKA
680:The First Ten Years of Public-Key Cryptography
324:which any certificate can be matched against.
275:
303:
568:
490:CompTIA Security+ Study Guide: Exam SY0-501
214:
654:Non-Secret Encryption Using a Finite Field
26:"Kex" redirects here. For other uses, see
660:Thoughts on Cheaper Non-Secret Encryption
127:Learn how and when to remove this message
183:technique they might use. If they use a
160:
523:IEEE Transactions on Information Theory
400:
187:, both will require a copy of the same
742:
315:” (CA), trusted by all parties, for a
206:
543:
391:Password-authenticated key agreement
386:Password-authenticated key agreement
65:adding citations to reliable sources
36:
569:Shapovalova, Natalia (2016-01-05).
13:
673:Cryptographic apparatus and method
14:
771:
263:
702:Boca Raton, Florida: CRC Press.
699:Handbook of Applied Cryptography
656:MJ Williamson, January 21, 1974.
516:"New Directions in Cryptography"
41:
662:MJ Williamson, August 10, 1976.
544:Wolff, Josephine (2015-12-14).
361:
52:needs additional citations for
666:New Directions in Cryptography
627:
612:
587:
562:
537:
507:
476:
1:
469:
459:Elliptic-curve Diffie–Hellman
224:(asymmetrical cryptography),
345:There are known cases where
322:certificate revocation lists
242:secure communication channel
7:
454:Diffie–Hellman key exchange
437:
286:Diffie–Hellman key exchange
276:Diffie–Hellman key exchange
254:Digital Signature Algorithm
167:Diffie–Hellman key exchange
10:
776:
650:J. H. Ellis, January 1970.
404:
378:(an implementation of the
309:Public key infrastructures
226:symmetric-key cryptography
25:
18:
493:. John Wiley & Sons.
420:man-in-the-middle attacks
304:Public key infrastructure
750:Cryptographic primitives
531:10.1109/TIT.1976.1055638
412:Quantum key distribution
407:quantum key distribution
215:The key exchange problem
760:Public-key cryptography
755:Cryptographic protocols
434:between Alice and Bob.
340:argument from authority
222:public-key cryptography
525:. IT-22 (6): 644–654.
282:cryptographic protocol
175:
432:authenticated channel
313:certificate authority
201:asymmetric key cipher
164:
32:KEXS (disambiguation)
726:New York: Doubleday
401:Quantum key exchange
197:symmetric key cipher
61:improve this article
28:KEX (disambiguation)
16:Cryptographic method
487:(October 5, 2017).
317:digital certificate
207:Channel of exchange
690:van Oorschot, Paul
621:CA/Symantec Issues
444:Key (cryptography)
176:
152:cryptographic keys
19:For the film, see
333:digital signature
298:man-in-the-middle
146:) is a method in
144:key establishment
137:
136:
129:
111:
767:
712:Available online
675:
640:
639:
631:
625:
624:
616:
610:
609:
607:
606:
591:
585:
584:
582:
581:
566:
560:
559:
557:
556:
541:
535:
534:
520:
511:
505:
504:
483:Emmett Dulaney,
480:
248:For example, in
191:. If they use a
172:symmetric cipher
132:
125:
121:
118:
112:
110:
69:
45:
37:
775:
774:
770:
769:
768:
766:
765:
764:
740:
739:
694:Vanstone, Scott
686:Menezes, Alfred
671:
644:
643:
633:
632:
628:
618:
617:
613:
604:
602:
593:
592:
588:
579:
577:
567:
563:
554:
552:
542:
538:
518:
512:
508:
501:
481:
477:
472:
464:Forward secrecy
440:
409:
403:
388:
364:
306:
278:
266:
240:, or any other
238:diplomatic bags
217:
209:
133:
122:
116:
113:
70:
68:
58:
46:
35:
24:
17:
12:
11:
5:
773:
763:
762:
757:
752:
738:
737:
715:
683:
677:
669:
663:
657:
651:
642:
641:
626:
611:
586:
561:
536:
506:
499:
474:
473:
471:
468:
467:
466:
461:
456:
451:
449:Key management
446:
439:
436:
405:Main article:
402:
399:
387:
384:
363:
360:
305:
302:
277:
274:
265:
264:Identification
262:
216:
213:
208:
205:
135:
134:
76:"Key exchange"
49:
47:
40:
15:
9:
6:
4:
3:
2:
772:
761:
758:
756:
753:
751:
748:
747:
745:
736:
733:
732:0-385-49531-5
729:
725:
724:
719:
716:
713:
709:
708:0-8493-8523-7
705:
701:
700:
695:
691:
687:
684:
681:
678:
674:
670:
667:
664:
661:
658:
655:
652:
649:
646:
645:
638:
637:
630:
623:
622:
615:
600:
596:
590:
576:
572:
565:
551:
547:
540:
532:
528:
524:
517:
510:
502:
500:9781119416906
496:
492:
491:
486:
485:Chuck Easttom
479:
475:
465:
462:
460:
457:
455:
452:
450:
447:
445:
442:
441:
435:
433:
429:
425:
422:. Beside the
421:
417:
413:
408:
398:
396:
392:
383:
381:
377:
373:
369:
359:
356:
351:
348:
347:authoritarian
343:
341:
336:
334:
330:
325:
323:
318:
314:
310:
301:
299:
295:
291:
287:
283:
273:
271:
261:
257:
255:
251:
245:
243:
239:
235:
230:
227:
223:
212:
204:
202:
198:
194:
190:
186:
182:
173:
168:
163:
159:
157:
153:
149:
145:
141:
131:
128:
120:
117:November 2014
109:
106:
102:
99:
95:
92:
88:
85:
81:
78: –
77:
73:
72:Find sources:
66:
62:
56:
55:
50:This article
48:
44:
39:
38:
33:
29:
22:
721:
718:Singh, Simon
697:
635:
629:
620:
614:
603:. Retrieved
601:. 2016-02-15
598:
589:
578:. Retrieved
574:
564:
553:. Retrieved
549:
539:
522:
509:
489:
478:
428:completeness
416:measurements
410:
389:
368:web of trust
365:
362:Web of trust
352:
344:
337:
326:
307:
293:
290:Ralph Merkle
279:
267:
258:
246:
231:
218:
210:
177:
148:cryptography
143:
140:Key exchange
139:
138:
123:
114:
104:
97:
90:
83:
71:
59:Please help
54:verification
51:
21:Key Exchange
424:correctness
329:legislation
284:called the
744:Categories
605:2019-01-09
580:2019-01-09
555:2019-01-09
470:References
181:encryption
87:newspapers
696:(1997).
294:and alter
156:algorithm
150:by which
735:Cambodia
438:See also
395:password
234:couriers
189:codebook
720:(1999)
380:OpenPGP
165:In the
101:scholar
730:
706:
599:Meduza
575:Mondaq
497:
355:notary
193:cipher
142:(also
103:
96:
89:
82:
74:
550:Slate
519:(PDF)
270:spoof
108:JSTOR
94:books
728:ISBN
704:ISBN
495:ISBN
426:and
374:and
185:code
80:news
30:and
710:. (
527:doi
376:GPG
372:PGP
250:RSA
63:by
746::
692:;
688:;
597:.
573:.
548:.
521:.
397:.
236:,
158:.
714:)
608:.
583:.
558:.
533:.
529::
503:.
174:.
130:)
124:(
119:)
115:(
105:·
98:·
91:·
84:·
57:.
34:.
23:.
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.