1079:. Although microkernels are very small by themselves, in combination with all their required auxiliary code they are, in fact, often larger than monolithic kernels. Advocates of monolithic kernels also point out that the two-tiered structure of microkernel systems, in which most of the operating system does not interact directly with the hardware, creates a not-insignificant cost in terms of system efficiency. These types of kernels normally provide only the minimal services such as defining memory address spaces, inter-process communication (IPC) and the process management. The other functions such as running the hardware processes are not handled directly by microkernels. Proponents of microkernels point out those monolithic kernels have the disadvantage that an error in the kernel can cause the entire system to crash. However, with a microkernel, if a kernel process crashes, it is still possible to prevent a crash of the system as a whole by merely restarting the service that caused the error.
558:
may be able to perform many different operations, including read, write, delete or execute, but a user-level application may only be permitted to perform some of these operations (e.g., it may only be allowed to read the file). A common implementation of this is for the kernel to provide an object to the application (typically so called a "file handle") which the application may then invoke operations on, the validity of which the kernel checks at the time the operation is requested. Such a system may be extended to cover all objects that the kernel manages, and indeed to objects provided by other user applications.
573:
needs to access an object protected by a capability, it performs a system call and the kernel then checks whether the application's capability grants it permission to perform the requested action, and if it is permitted performs the access for it (either directly, or by delegating the request to another user-level process). The performance cost of address space switching limits the practicality of this approach in systems with complex interactions between objects, but it is used in current operating systems for objects that are not accessed frequently or which are not expected to perform quickly.
330:) on behalf of the OS. It provides the operating system with an API, procedures and information about how to control and communicate with a certain piece of hardware. Device drivers are an important and vital dependency for all OS and their applications. The design goal of a driver is abstraction; the function of the driver is to translate the OS-mandated abstract function calls (programming calls) into device-specific calls. In theory, a device should work correctly with a suitable driver. Device drivers are used for e.g. video cards, sound cards, printers, scanners, modems, and Network cards.
1278:. Hybrid kernels are similar to microkernels, except they include some additional code in kernel-space to increase performance. These kernels represent a compromise that was implemented by some developers to accommodate the major advantages of both monolithic and microkernels. These types of kernels are extensions of microkernels with some properties of monolithic kernels. Unlike monolithic kernels, these types of kernels are unable to load modules at runtime on their own. This implies running some services (such as the
1025:
systems, and network stacks. Microkernels were invented as a reaction to traditional "monolithic" kernel design, whereby all system functionality was put in a one static program running in a special "system" mode of the processor. In the microkernel, only the most fundamental of tasks are performed such as being able to access some (not necessarily all) of the hardware, manage memory and coordinate message passing between the processes. Some systems that use microkernels are QNX and the HURD. In the case of
885:
be accessed by most programs which cannot be put in a library is in the kernel space: Device drivers, scheduler, memory handling, file systems, and network stacks. Many system calls are provided to applications, to allow them to access all those services. A monolithic kernel, while initially loaded with subsystems that may not be needed, can be tuned to a point where it is as fast as or faster than the one that was specifically designed for the hardware, although more relevant in a general sense.
1361:), providing application developers with the functionalities of a conventional operating system. This comes down to every user writing their own rest-of-the kernel from near scratch, which is a very-risky, complex and quite a daunting assignment - particularly in a time-constrained production-oriented environment, which is why exokernels have never caught on. A major advantage of exokernel-based systems is that they can incorporate multiple library operating systems, each exporting a different
279:. Virtual addressing allows the kernel to make a given physical address appear to be another address, the virtual address. Virtual address spaces may be different for different processes; the memory that one process accesses at a particular (virtual) address may be different memory from what another process accesses at the same address. This allows every program to behave as if it is the only one (apart from the kernel) running and thus prevents applications from crashing each other.
291:). As a result, operating systems can allow programs to use more memory than the system has physically available. When a program needs data which is not currently in RAM, the CPU signals to the kernel that this has happened, and the kernel responds by writing the contents of an inactive memory block to disk (if necessary) and replacing it with the data requested by the program. The program can then be resumed from the point where it was stopped. This scheme is generally known as
1552:
966:
810:), which is common in conventional commercial systems; in fact, every module needing protection is therefore preferably included into the kernel. This link between monolithic design and "privileged mode" can be reconducted to the key issue of mechanism-policy separation; in fact the "privileged mode" architectural approach melds together the protection mechanism with the security policies, while the major alternative architectural approach,
916:
Hence, not far to travel at all. The monolithic Linux kernel can be made extremely small not only because of its ability to dynamically load modules but also because of its ease of customization. In fact, there are some versions that are small enough to fit together with a large number of utilities and other programs on a single floppy disk and still provide a fully functional operating system (one of the most popular of which is
1224:
865:
38:
253:(IPC). These implementations may be located within the kernel itself or the kernel can also rely on other processes it is running. Although the kernel must provide IPC in order to provide access to the facilities provided by each other, kernels must also provide running programs with a method to make requests to access these facilities. The kernel is also responsible for context switching between processes or threads.
1290:
code tainted module has the potential to destabilize a running kernel. It is possible to write a driver for a microkernel in a completely separate memory space and test it before "going" live. When a kernel module is loaded, it accesses the monolithic portion's memory space by adding to it what it needs, therefore, opening the doorway to possible pollution. A few advantages to the modular (or) Hybrid kernel are:
1086:. Servers allow the operating system to be modified by simply starting and stopping programs. For a machine without networking support, for instance, the networking server is not started. The task of moving in and out of the kernel to move data between the various applications and servers creates overhead which is detrimental to the efficiency of microkernels in comparison with monolithic kernels.
213:(RAM) is used to store both program instructions and data. Typically, both need to be present in memory in order for a program to execute. Often multiple programs will want access to memory, frequently demanding more memory than the computer has available. The kernel is responsible for deciding which memory each process can use, and determining what to do when not enough memory is available.
1177:), which some developers argue is necessary to increase the performance of the system. Some developers also maintain that monolithic systems are extremely efficient if well written. The monolithic model tends to be more efficient through the use of shared kernel memory, rather than the slower IPC system of microkernel designs, which is typically based on
1607:, which allowed users to complete operations in stages, feeding a file through a chain of single-purpose tools. Although the end result was the same, using smaller programs in this way dramatically increased flexibility as well as ease of development and use, allowing the user to modify their workflow by adding or removing a program from the chain.
306:). The applications are not permitted by the processor to address kernel memory, thus preventing an application from damaging the running kernel. This fundamental partition of memory space has contributed much to the current designs of actual general-purpose kernels and is almost universal in such systems, although some research kernels (e.g.,
932:
servers to provide more functionality. This particular approach defines a high-level virtual interface over the hardware, with a set of system calls to implement operating system services such as process management, concurrency and memory management in several modules that run in supervisor mode. This design has several flaws and limitations:
487:. A call gate is a special address stored by the kernel in a list in kernel memory at a location known to the processor. When the processor detects a call to that address, it instead redirects to the target location without causing an access violation. This requires hardware support, but the hardware for it is quite common.
1426:, provided that the authors of those programs are willing to work without any hardware abstraction or operating system support. Most early computers operated this way during the 1950s and early 1960s, which were reset and reloaded between the execution of different programs. Eventually, small ancillary programs such as
129:. This separation prevents user data and kernel data from interfering with each other and causing instability and slowness, as well as preventing malfunctioning applications from affecting other applications or crashing the entire operating system. Even in systems where the kernel is included in application
2830:
Levy 84, p.1 quote: "Conventional architectures support a single privileged mode of operation. This structure leads to monolithic design; any module needing protection must be part of the single operating system kernel. If, instead, any module could execute within a protected domain, systems could be
992:
Microkernel (also abbreviated μK or uK) is the term describing an approach to operating system design by which the functionality of the system is moved out of the traditional "kernel", into a set of "servers" that communicate through a "minimal" kernel, leaving as little as possible in "system space"
931:
These types of kernels consist of the core functions of the operating system and the device drivers with the ability to load modules at runtime. They provide rich and powerful abstractions of the underlying hardware. They provide a small set of simple hardware abstractions and use applications called
915:
Most work in the monolithic kernel is done via system calls. These are interfaces, usually kept in a tabular structure, that access some subsystem within the kernel such as disk operations. Essentially calls are made within programs and a checked copy of the request is passed through the system call.
884:
Monolithic kernels, which have traditionally been used by Unix-like operating systems, contain all the operating system core functions and the device drivers. A monolithic kernel is one single program that contains all of the code necessary to perform every kernel-related task. Every part which is to
798:
In minimal microkernel just some very basic policies are included, and its mechanisms allows what is running on top of the kernel (the remaining part of the operating system and the other applications) to decide which policies to adopt (as memory management, high level process scheduling, file system
748:
or hardware abstraction layer. Frequently, applications will require access to these devices. The kernel must maintain the list of these devices by querying the system for them in some way. This can be done through the BIOS, or through one of the various system buses (such as PCI/PCIE, or USB). Using
572:
An alternative approach is to simulate capabilities using commonly supported hierarchical domains. In this approach, each protected object must reside in an address space that the application does not have access to; the kernel also maintains a list of capabilities in such memory. When an application
2950:
The tightly coupled nature of a monolithic kernel allows it to make very efficient use of the underlying hardware
Microkernels, on the other hand, run a lot more of the core processes in userland. Unfortunately, these benefits come at the cost of the microkernel having to pass a lot of information
1289:
Many traditionally monolithic kernels are now at least adding (or else using) the module capability. The most well known of these kernels is the Linux kernel. The modular kernel essentially can have parts of it that are built into the core kernel binary or binaries that load into memory on demand. A
1215:
architecture that leads to the design of a monolithic kernel has a significant performance drawback each time there's an interaction between different levels of protection (i.e., when a process has to manipulate a data structure both in "user mode" and "supervisor mode"), since this requires message
1184:
The performance of microkernels was poor in both the 1980s and early 1990s. However, studies that empirically measured the performance of these microkernels did not analyze the reasons of such inefficiency. The explanations of this data were left to "folklore", with the assumption that they were due
1614:
consists of two parts: first, the huge collection of utility programs that drive most operations; second, the kernel that runs the programs. Under Unix, from a programming standpoint, the distinction between the two is fairly thin; the kernel is a program, running in supervisor mode, that acts as a
1058:
basis with the microkernel. As an example, if a request for more memory is sent, a port is opened with the microkernel and the request sent through. Once within the microkernel, the steps are similar to system calls. The rationale was that it would bring modularity in the system architecture, which
1024:
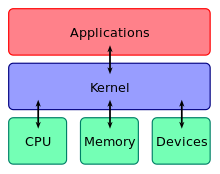
Only parts which really require being in a privileged mode are in kernel space: IPC (Inter-Process
Communication), basic scheduler, or scheduling primitives, basic memory handling, basic I/O primitives. Many critical parts are now running in user space: The complete scheduler, memory handling, file
557:
Many kernels provide implementation of "capabilities", i.e., objects that are provided to user code which allow limited access to an underlying object managed by the kernel. A common example is file handling: a file is a representation of information stored on a permanent storage device. The kernel
880:
stated that "it is in opinion easier to implement a monolithic kernel". The main disadvantages of monolithic kernels are the dependencies between system components – a bug in a device driver might crash the entire system – and the fact that large kernels can become
623:
Typical computer systems today use hardware-enforced rules about what programs are allowed to access what data. The processor monitors the execution and stops a program that violates a rule, such as a user process that tries to write to kernel memory. In systems that lack support for capabilities,
1304:
Modules, generally, communicate with the kernel using a module interface of some sort. The interface is generalized (although particular to a given operating system) so it is not always possible to use modules. Often the device drivers may need more flexibility than the module interface affords.
1498:
project in 1965. Another ongoing issue was properly handling computing resources: users spent most of their time staring at the terminal and thinking about what to input instead of actually using the resources of the computer, and a time-sharing system should give the CPU time to an active user
1353:
Exokernels are a still-experimental approach to operating system design. They differ from other types of kernels in limiting their functionality to the protection and multiplexing of the raw hardware, providing no hardware abstractions on top of which to develop applications. This separation of
805:
presented arguments in favour of separation of mechanism and policy. The failure to properly fulfill this separation is one of the major causes of the lack of substantial innovation in existing operating systems, a problem common in computer architecture. The monolithic design is induced by the
1646:
posed another problem. Even if network communication can be compared to file access, the low-level packet-oriented architecture dealt with discrete chunks of data and not with whole files. As the capability of computers grew, Unix became increasingly cluttered with code. It is also because the
436:
In computing, a system call is how a process requests a service from an operating system's kernel that it does not normally have permission to run. System calls provide the interface between a process and the operating system. Most operations interacting with the system require permissions not
642:
No need for separate address spaces. Switching between address spaces is a slow operation that causes a great deal of overhead, and a lot of optimization work is currently performed in order to prevent unnecessary switches in current operating systems. Switching is completely unnecessary in a
743:
Similar to physical memory, allowing applications direct access to controller ports and registers can cause the controller to malfunction, or system to crash. With this, depending on the complexity of the device, some devices can get surprisingly complex to program, and use several different
993:
and as much as possible in "user space". A microkernel that is designed for a specific platform or device is only ever going to have what it needs to operate. The microkernel approach consists of defining a simple abstraction over the hardware, with a set of primitives or
749:
an example of a video driver, when an application requests an operation on a device, such as displaying a character, the kernel needs to send this request to the current active video driver. The video driver, in turn, needs to carry out this request. This is an example of
1537:, that have direct access to the hardware. There is no memory protection, and the kernel is almost always running in user mode. Only special actions are executed in kernel mode, and user-mode applications can ask the operating system to execute their code in kernel mode.
471:
The method of invoking the kernel function varies from kernel to kernel. If memory isolation is in use, it is impossible for a user process to call the kernel directly, because that would be a violation of the processor's access control rules. A few possibilities are:
1141:
have virtual memory support. To reduce the kernel's footprint, extensive editing has to be performed to carefully remove unneeded code, which can be very difficult with non-obvious interdependencies between parts of a kernel with millions of lines of code.
1109:
The disadvantages for microkernels are extremely context-based. As an example, they work well for small single-purpose (and critical) systems because if not many processes need to run, then the complications of process management are effectively mitigated.
1586:
were represented as a "file" at a known location – when data was copied to the file, it printed out. Other systems, to provide a similar functionality, tended to virtualize devices at a lower level – that is, both devices
646:
Flexibility. Any protection scheme that can be designed to be expressed via a programming language can be implemented using this method. Changes to the protection scheme (e.g. from a hierarchical system to a capability-based one) do not require new
833:
try to run most of their services in user space, aiming to improve maintainability and modularity of the codebase. Most kernels do not fit exactly into one of these categories, but are rather found in between these two designs. These are called
65:
and generally has complete control over everything in the system. The kernel is also responsible for preventing and mitigating conflicts between different processes. It is the portion of the operating system code that is always resident in
386:
where the kernel will be rewritten if the available hardware changes), configured by the user (typical on older PCs and on systems that are not designed for personal use) or detected by the operating system at run time (normally called
947:
Bugs in one part of the kernel have strong side effects; since every function in the kernel has all the privileges, a bug in one function can corrupt data structure of another, totally unrelated part of the kernel, or of any running
1471:, computers had grown enormously in power – to the point where computer operators were looking for new ways to get people to use their spare time on their machines. One of the major developments during this era was
583:
An important kernel design decision is the choice of the abstraction levels where the security mechanisms and policies should be implemented. Kernel security mechanisms play a critical role in supporting security at higher levels.
378:
For example, to show the user something on the screen, an application would make a request to the kernel, which would forward the request to its display driver, which is then responsible for actually plotting the character/pixel.
201:
This central component of a computer system is responsible for executing programs. The kernel takes responsibility for deciding at any time which of the many running programs should be allocated to the processor or processors.
501:
Using a memory-based queue. An application that makes large numbers of requests but does not need to wait for the result of each may add details of requests to an area of memory that the kernel periodically scans to find
944:. Rebooting the computer is often required. This is not just a problem of convenience to the developers. When debugging is harder, and as difficulties become stronger, it becomes more likely that code will be "buggier".
1528:
was released in 1985, and was among the first – and certainly most successful – home computers to feature an advanced kernel architecture. The AmigaOS kernel's executive component,
282:
On many systems, a program's virtual address may refer to data which is not currently in memory. The layer of indirection provided by virtual addressing allows the operating system to use other data stores, like a
2196:. . . nearly all system calls invoked from C programs by calling a library procedure . . . The library procedure . . . executes a TRAP instruction to switch from user mode to kernel mode and start execution . . .
1145:
By the early 1990s, due to the various shortcomings of monolithic kernels versus microkernels, monolithic kernels were considered obsolete by virtually all operating system researchers. As a result, the design of
1825:'s kernel is considered a hybrid kernel because the kernel itself contains tasks such as the Window Manager and the IPC Managers, with a client/server layered subsystem model. It was designed as a modified
444:
instruction that causes the processor to change mode. An example would be from supervisor mode to protected mode. This is where the operating system performs actions like accessing hardware devices or the
624:
processes are isolated from each other by using separate address spaces. Calls from user processes into the kernel are regulated by requiring them to use one of the above-described system call methods.
2888:
655:
Longer application startup time. Applications must be verified when they are started to ensure they have been compiled by the correct compiler, or may need recompiling either from source code or from
1305:
Essentially, it is two system calls and often the safety checks that only have to be done once in the monolithic kernel now may be done twice. Some of the disadvantages of the modular approach are:
912:, allowing modules to be loaded into the kernel at runtime, permitting easy extension of the kernel's capabilities as required, while helping to minimize the amount of code running in kernel space.
1603:
utilities and concepts, dramatically simplifying operation. As an extension of the same paradigm, Unix allows programmers to manipulate files using a series of small programs, using the concept of
1453:
introduced the system design philosophy of a small nucleus "upon which operating systems for different purposes could be built in an orderly manner", what would be called the microkernel approach.
1117:, and the use of different operating systems on top of the same unchanged kernel. It is also possible to dynamically switch among operating systems and to have more than one active simultaneously.
229:. The kernel provides convenient methods for applications to use these devices which are typically abstracted by the kernel so that applications do not need to know their implementation details.
4220:
457:
or
Windows API. The library handles the low-level details of passing information to the kernel and switching to supervisor mode. System calls include close, open, read, wait and write.
1208:
of those concepts. Therefore it remained to be studied if the solution to build an efficient microkernel was, unlike previous attempts, to apply the correct construction techniques.
872:
In a monolithic kernel, all OS services run along with the main kernel thread, thus also residing in the same memory area. This approach provides rich and powerful hardware access.
1706:, populated by self-written hobby kernels which mostly end up sharing many features with Linux, FreeBSD, DragonflyBSD, OpenBSD or NetBSD kernels and/or being compatible with them.
2816:
Levy 84, p.1 quote: "Although the complexity of computer applications increases yearly, the underlying hardware architecture for applications has remained unchanged for decades."
708:
are sufficient primitives to express any functionality of process cooperation. However this approach is generally held to be lacking in terms of safety and efficiency, whereas a
1354:
hardware protection from hardware management enables application developers to determine how to make the most efficient use of the available hardware for each specific program.
587:
One approach is to use firmware and kernel support for fault tolerance (see above), and build the security policy for malicious behavior on top of that (adding features such as
1478:
The development of time-sharing systems led to a number of problems. One was that users, particularly at universities where the systems were being developed, seemed to want to
437:
available to a user-level process, e.g., I/O performed with a device present on the system, or any form of communication with other processes requires the use of system calls.
1033:
user sessions can be entire snapshots of the system itself or views as it is referred to. The very essence of the microkernel architecture illustrates some of its advantages:
712:
approach is more flexible. A number of other approaches (either lower- or higher-level) are available as well, with many modern kernels providing support for systems such as
670:. Such operations cannot be permitted in a language-based protection system, which means that applications may need to be rewritten and may, in some cases, lose performance.
2951:
in and out of the kernel space through a process known as a context switch. Context switches introduce considerable overhead and therefore result in a performance penalty.
460:
To actually perform useful work, a process must be able to access the services provided by the kernel. This is implemented differently by each kernel, but most provide a
576:
If the firmware does not support protection mechanisms, it is possible to simulate protection at a higher level, for example by simulating capabilities by manipulating
1059:
would entail a cleaner system, easier to debug or dynamically modify, customizable to users' needs, and more performing. They are part of the operating systems like
498:) may lack. System call instructions have been added to recent models of x86 processors, however, and some operating systems for PCs make use of them when available.
3069:
Baumann, Andrew; Barham, Paul; Dagand, Pierre-Evariste; Harris, Tim; Isaacs, Rebecca; Peter, Simon; Roscoe, Timothy; Schüpbach, Adrian; Singhania, Akhilesh (2009).
1286:) in kernel space to reduce the performance overhead of a traditional microkernel, but still running kernel code (such as device drivers) as servers in user space.
4009:
3945:
604:
The lack of many critical security mechanisms in current mainstream operating systems impedes the implementation of adequate security policies at the application
267:
The kernel has full access to the system's memory and must allow processes to safely access this memory as they require it. Often the first step in doing this is
1196:
In fact, as guessed in 1995, the reasons for the poor performance of microkernels might as well have been: (1) an actual inefficiency of the whole microkernel
2885:
3453:
728:
The idea of a kernel where I/O devices are handled uniformly with other processes, as parallel co-operating processes, was first proposed and implemented by
1475:, whereby a number of users would get small slices of computer time, at a rate at which it appeared they were each connected to their own, slower, machine.
635:. The language may then be designed such that it is impossible for the programmer to instruct it to do something that will violate a security requirement.
580:, but there are performance implications. Lack of hardware support may not be an issue, however, for systems that choose to use language-based protection.
70:
and facilitates interactions between hardware and software components. A full kernel controls all hardware resources (e.g. I/O, memory, cryptography) via
1899:, i.e. the capacity to run multiple operating systems on the same machine totally independently from each other. Hence the first such system was called
1438:. As these were developed, they formed the basis of what became early operating system kernels. The "bare metal" approach is still used today on some
608:. In fact, a common misconception in computer security is that any security policy can be implemented in an application regardless of kernel support.
117:
or other less critical parts of the operating system. The kernel performs its tasks, such as running processes, managing hardware devices such as the
2038:
The highest privilege level has various names throughout different architectures, such as supervisor mode, kernel mode, CPL0, DPL0, ring 0, etc. See
2930:
4519:
1294:
Faster development time for drivers that can operate from within modules. No reboot required for testing (provided the kernel is not destabilized).
611:
According to Mars
Research Group developers, a lack of isolation is one of the main factors undermining kernel security. They propose their driver
3283:
4236:
3185:
799:
management, etc.). A monolithic kernel instead tends to include many policies, therefore restricting the rest of the system to rely on them.
418:
or memory location. Important decisions have to be made when designing the device management system, as in some designs accesses may involve
744:
controllers. Because of this, providing a more abstract interface to manage the device is important. This interface is normally done by a
4466:
3926:
3482:
3051:
2852:
1802:, an operating system with a very similar interface, but intended for high-end and business users. This line started with the release of
3810:
2971:
954:
Even if the modules servicing these operations are separate from the whole, the code integration is tight and difficult to do correctly.
3427:
1933:(mainly the L3 and the L4 kernel) was created to demonstrate that microkernels are not necessarily slow. Newer implementations such as
774:
is the support that allows the implementation of many different policies, while a policy is a particular "mode of operation". Example:
547:); whether they are hardware supported or language based; whether they are more an open mechanism or a binding policy; and many more.
410:-specific topic, these drivers are handled differently by each kind of kernel design, but in every case, the kernel has to provide the
17:
2489:
449:. Generally the operating system provides a library that sits between the operating system and normal user programs. Usually it is a
2337:
298:
Virtual addressing also allows creation of virtual partitions of memory in two disjointed areas, one being reserved for the kernel (
2899:
1113:
A microkernel allows the implementation of the remaining part of the operating system as a normal application program written in a
2433:
535:
The mechanisms or policies provided by the kernel can be classified according to several criteria, including: static (enforced at
2877:
2777:
Lecture Notes In
Computer Science; Vol. 563. Proceedings of the International Workshop on Operating Systems of the 90s and Beyond
2382:
Lepreau, Jay; Ford, Bryan; Hibler, Mike (1996). "The persistent relevance of the local operating system to global applications".
881:
very difficult to maintain; Thompson also stated that "It is also easier for to turn into a mess in a hurry as it is modified."
2799:
The past 25 years have shown that research on operating system architecture had a minor effect on existing main stream [
440:
A system call is a mechanism that is used by the application program to request a service from the operating system. They use a
125:. In contrast, application programs such as browsers, word processors, or audio or video players use a separate area of memory,
1980:
1779:. Because of its dependence on another operating system, initial releases of Windows, prior to Windows 95, were considered an
1231:
approach combines the speed and simpler design of a monolithic kernel with the modularity and execution safety of a microkernel
3367:
4795:
4766:
4426:
4409:
4230:
4162:
4148:
4122:
4045:
3920:
3796:
3761:
3712:
3540:
3515:
3496:
3214:
3129:
2711:
2401:
2260:
2189:
2103:
815:
525:
262:
1102:
Messaging bugs can be harder to fix due to the longer trip they have to take versus the one off copy in a monolithic kernel.
1046:
More persistence in general, if one instance goes haywire, it is often possible to substitute it with an operational mirror.
4388:
4261:
761:
The above listed tasks and features can be provided in many ways that differ from each other in design and implementation.
74:, arbitrates conflicts between processes concerning such resources, and optimizes the utilization of common resources e.g.
3338:
245:) and the protection mechanism used to mediate access to the resources within a domain. Kernels also provide methods for
595:. Approaches that delegate enforcement of security policy to the compiler and/or the application level are often called
3953:
3733:
766:
246:
2564:
Huang, Yongzhe; Narayanan, Vikram; Detweiler, David; Huang, Kaiming; Tan, Gang; Jaeger, Trent; Burtsev, Anton (2022).
1638:
could be treated as a file or a byte stream, which is printed to or read from, the same did not seem to be true for a
4981:
2792:
1929:, is the best-known general-purpose microkernel, other microkernels have been developed with more specific aims. The
1767:
1328:
540:
396:
732:(although similar ideas were suggested in 1967). In Hansen's description of this, the "common" processes are called
113:
The critical code of the kernel is usually loaded into a separate area of memory, which is protected from access by
4570:
4514:
2910:
1357:
Exokernels in themselves are extremely small. However, they are accompanied by library operating systems (see also
1309:
With more interfaces to pass through, the possibility of increased bugs exists (which implies more security holes).
3460:
3160:
2536:
2359:
Loscocco, P. A.; Smalley, S. D.; Muckelbauer, P. A.; Taylor, R. C.; Turner, S. J.; Farrell, J. F. (October 1998).
4489:
4459:
2384:
Proceedings of the 7th workshop on ACM SIGOPS European workshop
Systems support for worldwide applications - EW 7
1968:
1576:
1450:
1114:
238:
1312:
Maintaining modules can be confusing for some administrators when dealing with problems like symbol differences.
4682:
4580:
4309:
1679:
1297:
On demand capability versus spending time recompiling a whole kernel for things like new drivers or subsystems.
1082:
Other services provided by the kernel such as networking are implemented in user-space programs referred to as
683:
307:
3961:
Linden, Theodore A. (December 1976). "Operating System
Structures to Support Security and Reliable Software".
2072:
1615:
program loader and supervisor for the small utility programs making up the rest of the system, and to provide
791:
Because the mechanism and policy are separated, the policy can be easily changed to e.g. require the use of a
4960:
4509:
4494:
2541:
1938:
1159:
326:. A device driver is a computer program encapsulating, monitoring and controlling a hardware device (via its
82:
usage, file systems, and network sockets. On most systems, the kernel is one of the first programs loaded on
2216:
Swift 2005, p.29 quote: "isolation, resource control, decision verification (checking), and error recovery."
1814:
with a completely different, much more sophisticated operating system. This is the line that continues with
1300:
Faster integration of third party technology (related to development but pertinent unto itself nonetheless).
516:
An important consideration in the design of a kernel is the support it provides for protection from faults (
4555:
4540:
4499:
4140:
3070:
1662:
Modern Unix-derivatives are generally based on module-loading monolithic kernels. Examples of this are the
1413:
936:
Coding in kernel can be challenging, in part because one cannot use common libraries (like a full-featured
31:
3265:
4721:
4668:
1985:
1624:
1186:
1174:
1054:
system to handle requests from one server to another. The message passing system generally operates on a
1006:
826:
811:
750:
612:
566:
303:
299:
250:
221:
I/O devices include, but are not limited to, peripherals such as keyboards, mice, disk drives, printers,
126:
122:
2360:
1327:
A nanokernel delegates virtually all services – including even the most basic ones like
1185:
to the increased frequency of switches from "kernel-mode" to "user-mode", to the increased frequency of
1017:. Microkernels are easier to maintain than monolithic kernels, but the large number of system calls and
182:
run most but not all of their services in user space, like user processes do, mainly for resilience and
4986:
4736:
4575:
4452:
4439:
1934:
1926:
1822:
1479:
1055:
415:
3302:"Windows - Official Site for Microsoft Windows 10 Home & Pro OS, laptops, PCs, tablets & more"
4771:
4550:
4545:
4504:
4060:
3643:
3309:
3254:
2938:
1743:
1703:
1040:
Patches can be tested in a separate instance, and then swapped in to take over a production instance.
3657:
2468:
1021:
might slow down the system because they typically generate more overhead than plain function calls.
494:
instruction. This technique requires special hardware support, which common architectures (notably,
4814:
4701:
4565:
4074:
3177:
1888:
1639:
1076:
450:
382:
A kernel must maintain a list of available devices. This list may be known in advance (e.g., on an
3532:
3526:
3397:
2361:"The Inevitability of Failure: The Flawed Assumption of Security in Modern Computing Environments"
977:, separate programs that assume former kernel functions, such as device drivers, GUI servers, etc.
327:
4560:
3031:
1616:
1522:
1483:
787:
Authorization server requires a password which is verified against stored passwords in a database
705:
701:
597:
422:, making the operation very CPU-intensive and easily causing a significant performance overhead.
107:
75:
4037:
4027:
3704:
3694:
2772:
1599:
the system at the file level allowed users to manipulate the entire system using their existing
4948:
4887:
4776:
4756:
4705:
4663:
4069:
4058:; Jerome H. Saltzer (March 1972). "A hardware architecture for implementing protection rings".
3652:
2463:
2026:
1854:
1592:
1126:
909:
565:(MMU) the responsibility of checking access-rights for every memory access, a mechanism called
562:
446:
195:
4279:
Gettys, James; Karlton, Philip L.; McGregor, Scott (1990). "The X window system, version 11".
4114:
4108:
3910:
3150:
3055:
2844:
561:
An efficient and simple way to provide hardware support of capabilities is to delegate to the
4731:
4697:
4599:
4535:
4033:
3963:
3776:
3555:
3488:
3018:
interactions between different levels of protection require transmission of messages by value
2773:"The Immortality of Operating Systems, or: Is Research in Operating Systems still Justified?"
2510:
2014:
1930:
1905:
1780:
1392:
1138:
1002:
770:
is the substantial difference between the philosophy of micro and monolithic kernels. Here a
717:
675:
628:
543:); pre-emptive or post-detection; according to the protection principles they satisfy (e.g.,
268:
242:
3861:
3419:
2896:
1791:
series adding 32-bit addressing and pre-emptive multitasking; but ended with the release of
1647:
modularity of the Unix kernel is extensively scalable. While kernels might have had 100,000
4928:
4902:
3478:
1957:
1648:
1631:
1503:
several layers deep, and partitioning this expensive resource led to major developments in
1388:
973:
approach, the kernel itself only provides basic functionality that allows the execution of
643:
language-based protection system, as all code can safely operate in the same address space.
288:
210:
114:
42:
3817:
Härtig, Hermann; Hohmuth, Michael; Liedtke, Jochen; Schönberg, Sebastian (December 1997).
2565:
2451:
2330:
1150:
as a monolithic kernel rather than a microkernel was the topic of a famous debate between
1043:
Rapid development time and new software can be tested without having to reboot the kernel.
631:, the kernel will only allow code to execute that has been produced by a trusted language
8:
4897:
4849:
4726:
4364:
4132:
2177:
1896:
1583:
1533:, uses a microkernel message-passing design, but there are other kernel components, like
1395:. It does not assume shared memory but rather implements inter-process communications as
1370:
1155:
276:
183:
152:
145:
2248:
814:, clearly distinguishes between the two, leading naturally to a microkernel design (see
4834:
4741:
4345:
4329:
4296:
4193:
4095:
3998:
3802:
3678:
3626:
3580:
2717:
2670:
2481:
2426:
2407:
2308:
2119:
1877:
1862:
1667:
1439:
1427:
974:
937:
920:). This ability to miniaturize its kernel has also led to a rapid growth in the use of
461:
454:
3849:
2874:
2432:(Report). Vol. II. Air Force Electronic Systems Division. ESD-TR-73-51, Vol. II.
4943:
4892:
4824:
4781:
4622:
4422:
4405:
4349:
4337:
4226:
4185:
4144:
4118:
4087:
4055:
4041:
3990:
3916:
3870:
3792:
3781:
Proceedings of the sixteenth ACM symposium on
Operating systems principles - SOSP '97
3757:
3722:
3708:
3690:
3670:
3638:
3618:
3584:
3572:
3536:
3511:
3492:
3237:
2934:
2788:
2707:
2397:
2256:
2185:
2099:
1964:
1772:
1735:
1635:
1487:
1275:
1247:
1170:
1099:
More software for interfacing is required, there is a potential for performance loss.
998:
859:
822:
802:
605:
521:
484:
167:
148:
134:
79:
4300:
4099:
4002:
3783:. 16th ACM Symposium on Operating Systems Principles (SOSP'97). Saint-Malo, France.
3630:
3287:
2721:
2674:
2411:
2312:
1634:
or byte stream no longer was as universally applicable as it was before. Although a
908:
kernel, all of which fall into the category of Unix-like operating systems, support
4923:
4475:
4392:
4321:
4288:
4197:
4177:
4079:
3985:
3980:
3972:
3895:
3830:
3806:
3784:
3700:
3682:
3662:
3608:
3592:
3564:
3359:
2780:
2697:
2660:
2598:
2588:
2473:
2387:
2298:
1990:
1846:
1842:
1784:
1643:
1500:
1435:
1339:
to make the kernel memory requirement even smaller than a traditional microkernel.
1130:
1094:
1010:
806:"kernel mode"/"user mode" architectural approach to protection (technically called
544:
407:
160:
62:
54:
4201:
3206:
3121:
2485:
666:. On traditional systems, applications frequently perform operations that are not
4867:
4829:
4800:
4400:
3269:
3258:
2914:
2903:
2892:
2881:
2039:
1953:
1866:
1604:
1443:
1396:
1212:
1178:
1051:
925:
807:
709:
698:
694:
569:. Most commercial computer architectures lack such MMU support for capabilities.
529:
517:
391:). In plug-and-play systems, a device manager first performs a scan on different
383:
284:
175:
118:
103:
67:
4252:
3863:
The IA-32 Architecture
Software Developer's Manual, Volume 1: Basic Architecture
1787:). This product line continued to evolve through the 1980s and 1990s, with the
1623:
services for these programs; beyond that, the kernel didn't intervene at all in
4953:
4877:
4839:
4711:
4161:; E. Cohen; W. Corwin; A. Jones; R. Levin; C. Pierson; F. Pollack (June 1974).
3941:
3772:
3330:
3181:
2689:
2275:
Silberschatz & Galvin, Operating System
Concepts, 4th ed, pp. 445 & 446
1995:
1963:, while originally created for educational purposes, is now focused on being a
1922:
1803:
1728:
1715:
1596:
1504:
1491:
1366:
1190:
1151:
1134:
1018:
905:
792:
419:
403:(USB), to detect installed devices, then searches for the appropriate drivers.
392:
226:
3037:
2963:
2537:"Automatic device driver isolation protects against bugs in operating systems"
1399:. Barrelfish was the first operating system to be described as a multikernel.
4975:
4862:
4819:
4658:
4612:
4341:
4333:
4312:(February 2005). "Improving the reliability of commodity operating systems".
4307:
4189:
4091:
3994:
3751:
3674:
3622:
3576:
3550:
1918:
1884:. In other operating systems, the supervisor is generally called the kernel.
1830:
1755:
1738:. Apple moved to a nanokernel design in Mac OS 8.6. Against this, the modern
1687:
1336:
1279:
1267:
1241:
1228:
1217:
958:
835:
745:
729:
713:
388:
323:
292:
272:
171:
130:
71:
4325:
3726:
3477:
1446:, but in general, newer computers use modern operating systems and kernels.
4746:
4292:
4158:
3900:
3883:
3879:
3854:
Proceedings of the 8th ACM International Symposium on Computer Architecture
3845:
2477:
1858:
1663:
1652:
1620:
1600:
1472:
1462:
1423:
1147:
1009:. Other services, including those normally provided by the kernel, such as
941:
889:
877:
588:
550:
Support for hierarchical protection domains is typically implemented using
536:
441:
411:
191:
95:
4181:
4083:
3976:
3835:
3818:
3788:
3666:
3613:
3596:
3568:
2702:
2694:
Proceedings of the ACM symposium on Operating System Principles - SOSP '67
2665:
2648:
2602:
2392:
2303:
2286:
480:. This method is available on most hardware, and is therefore very common.
4872:
4854:
4637:
4627:
4617:
1826:
1572:
1568:
1382:
1125:
As the computer kernel grows, so grows the size and vulnerability of its
994:
987:
970:
830:
667:
663:
491:
431:
179:
156:
4419:
Computer Organisation and Architecture: An Introduction (Second edition)
2907:
2873:
Recordings of the debate between Torvalds and Tanenbaum can be found at
2589:
Jonathan S. Shapiro; Jonathan M. Smith; David J. Farber (1999). "EROS".
2365:
Proceedings of the 21st National Information Systems Security Conference
1129:; and, besides reducing security, there is the problem of enlarging the
137:
is used to prevent unauthorized applications from modifying the kernel.
4010:"Operating System Structures to Support Security and Reliable Software"
3753:
Classic operating systems: from batch processing to distributed systems
3750:
Per Brinch Hansen, ed. (2001). "1 The evolution of operating systems".
3154:
2784:
2093:
1892:
1850:
1815:
1811:
1807:
1799:
1792:
1788:
1724:
1702:. Apart from these alternatives, amateur developers maintain an active
1422:
to run a computer. Programs can be directly loaded and executed on the
1322:
1283:
1251:
839:
577:
371:
350:
Simulating work with hardware, while doing something entirely different
319:
91:
87:
1551:
333:
At the hardware level, common abstractions of device drivers include:
322:
connected to the computer, which are controlled by the kernel through
4809:
4716:
4642:
4607:
3072:
The Multikernel: a new OS architecture for scalable multicore systems
2831:
built as a collection of independent modules extensible by any user."
1732:
1556:
1358:
1348:
1246:
Hybrid kernels are used in most commercial operating systems such as
965:
843:
679:
551:
477:
4444:
1630:
Over the years the computing model changed, and Unix's treatment of
1250:
NT 3.1, NT 3.5, NT 3.51, NT 4.0, 2000, XP, Vista, 7, 8, 8.1 and 10.
524:). These two aspects are usually not clearly distinguished, and the
4938:
2064:
1431:
1418:
Strictly speaking, an operating system (and thus, a kernel) is not
1060:
1030:
656:
632:
592:
591:
mechanisms where necessary), delegating some responsibility to the
347:
Using a lower-level device driver (file drivers using disk drivers)
99:
58:
3262:
1173:
are designed to have all of their code in the same address space (
627:
An alternative approach is to use language-based protection. In a
4933:
4632:
4440:
Detailed comparison between most popular operating system kernels
2449:
2368:
1806:
in 1993, and was introduced to general users with the release of
1691:
1683:
1675:
1516:
1495:
1271:
1068:
917:
897:
893:
414:
to allow drivers to physically access their devices through some
358:
Allowing the operating system direct access to hardware resources
187:
83:
2358:
2025:
Virtual addressing is most commonly achieved through a built-in
1223:
1158:. There is merit on both sides of the argument presented in the
864:
37:
30:"Kernel (computer science)" redirects here. For other uses, see
1881:
1776:
1695:
1555:
A diagram of the predecessor/successor family relationship for
1499:
during these periods. Finally, the systems typically offered a
846:
are available, but are seldom used for production systems. The
354:
And at the software level, device driver abstractions include:
287:, to store what would otherwise have to remain in main memory (
194:
is both monolithic and modular, since it can insert and remove
4250:
3950:
Proc. 15th ACM Symposium on Operating System Principles (SOSP)
1751:
4882:
4157:
3816:
3770:
2233:
2231:
1960:
1942:
1833:
but does not meet all of the criteria of a pure microkernel.
1739:
1719:
1699:
1525:
1332:
1263:
1255:
1064:
940:), and because one needs to use a source-level debugger like
921:
901:
370:
Implementing a language (often a high-level language such as
365:
4369:
Operating Systems: Design and Implementation (Third edition)
4218:
2563:
1865:, and similar functions and regulates the flow of work in a
1564:
1546:
1468:
1391:
machine as a network of independent cores, as if it were a
873:
674:
Examples of systems with language-based protection include
341:
4054:
3775:; Schönberg, Sebastian; Wolter, Jean (October 5–8, 1997).
3641:(April 1970). "The nucleus of a Multiprogramming System".
2228:
1204:
implemented in those microkernels, and (3) the particular
1089:
Disadvantages in the microkernel exist however. Some are:
951:
Kernels often become very large and difficult to maintain.
364:
Implementing an interface for non-driver software such as
318:
To perform useful functions, processes need access to the
4918:
3251:
3089:
3068:
2801:
1949:
1873:
1747:
1671:
1656:
1362:
1259:
1072:
1026:
1013:, are implemented in user-space programs, referred to as
847:
781:
User login attempts are routed to an authorization server
618:
615:
framework for protection, primarily in the Linux kernel.
495:
465:
400:
222:
141:
4254:
Improving the reliability of commodity operating systems
4163:"HYDRA: the kernel of a multiprocessor operating system"
2839:
2837:
1872:
Historically, this term was essentially associated with
3877:
3850:"IBM System/38 support for capability-based addressing"
3389:
2826:
2824:
2822:
1945:
next to other L4 processes in separate address spaces.
3301:
3010:
2845:"Open Sources: Voices from the Open Source Revolution"
2619:. Math. Dep., Technological U., Eindhoven, Sept. 1965.
2450:
Jerry H. Saltzer; Mike D. Schroeder (September 1975).
2329:
Schneider, Fred B.; Morrissett, Greg; Harper, Robert.
1120:
1105:
Process management in general can be very complicated.
468:, which in turn invokes the related kernel functions.
4278:
3553:(December 1976). "Fault tolerant operating systems".
2834:
2690:"Dynamic Supervisors - their design and construction"
2328:
1133:. This is mitigated to some degree by perfecting the
825:
execute all of their code in the same address space (
155:
requests a service from the kernel, it must invoke a
90:). It handles the rest of startup as well as memory,
4251:
Swift, Michael M.; Brian N. Bershad; Henry M. Levy.
3531:(revisited first ed.). Addison-Wesley. p.
2819:
2287:"An implementation of capabilities on the PDP-11/45"
1887:
In the 1970s, IBM further abstracted the supervisor
3843:
3508:
Embedded Microprocessor Systems: Real World Designs
2452:"The protection of information in computer systems"
4320:(1). Association for Computing Machinery: 77–110.
4222:Architettura dei Sistemi di Elaborazione, volume 1
3721:
3749:
3549:
3078:. 22nd Symposium on Operating Systems Principles.
2924:
2922:
2867:
2381:
1829:, as the Windows NT kernel was influenced by the
1456:
1434:were left in memory between runs, or loaded from
1407:
528:in the kernel design leads to the rejection of a
166:There are different kernel architecture designs.
4973:
4397:Computer Organization and Design (Sixth edition)
3387:
3272:and other operating system enthusiast web sites.
2649:"SHARER, a time sharing system for the CDC 6600"
2646:
2284:
2246:
2240:
2210:
1567:, programmers decided to model every high-level
1402:
756:
190:is a notable example of microkernel design. The
3878:Levin, R.; Cohen, E.; Corwin, W.; Pollack, F.;
3597:"Why not innovations in computer architecture?"
3156:Introduction and Overview of the Multics System
2964:"Operating Systems/Kernel Models - Wikiversity"
2687:
2184:(3rd ed.). Prentice Hall. pp. 50–51.
41:An oversimplification of how a kernel connects
4383:Understanding the Linux Kernel (Third edition)
3908:
3105:
2919:
2094:Randal E. Bryant; David R. O'Hallaron (2016).
1952:is a microkernel which is principally used in
1912:
1235:
4460:
4219:Baiardi, F.; A. Tomasi; M. Vanneschi (1988).
3481:; James L. Peterson; Peter B. Galvin (1991).
3102:Ball: Embedded Microprocessor Designs, p. 129
2931:"What Is Darwin (and How It Powers Mac OS X)"
2354:
2352:
2350:
2253:IA-64 Linux Kernel: Design and Implementation
2163:
2161:
121:, and handling interrupts, in this protected
3756:. New York: Springer-Verlag. pp. 1–36.
3149:
2994:
2992:
2990:
2988:
2566:"KSplit: Automating Device Driver Isolation"
2324:
2322:
2247:Eranian, Stephane; Mosberger, David (2002).
2129:
2127:
2096:Computer Systems: A Programmer's Perspective
1651:in the seventies and eighties, kernels like
3819:"The performance of μ-kernel-based systems"
3777:"The performance of μ-kernel-based systems"
3388:Zoller (inaktiv), Heinz (7 December 2013).
2928:
2688:Huxtable, D. H. R.; Warwick, M. T. (1967).
2633:
2631:
2629:
2627:
2625:
2427:Computer Security Technology Planning Study
2219:
1775:was first released in 1985 as an add-on to
1709:
4467:
4453:
2748:
2746:
2609:
2347:
2278:
2249:"Virtual Memory in the IA-64 Linux Kernel"
2158:
850:hypervisor, for example, is an exokernel.
704:and unlock operations operating on binary
697:proved that from a logical point of view,
506:
4376:Modern Operating Systems (Fourth edition)
4131:
4073:
3984:
3899:
3834:
3656:
3612:
2985:
2755:
2701:
2664:
2647:Harrison, M. C.; Schwartz, J. T. (1967).
2467:
2391:
2319:
2302:
2285:Hoch, Charles; J. C. Browne (July 1980).
2176:
2124:
997:to implement minimal OS services such as
961:, a bug can bring down the entire system.
3096:
3033:WWDC 2000 Session 106 – Mac OS X: Kernel
3001:
2764:
2622:
2424:
2201:
2151:
2149:
2147:
2145:
2143:
2141:
2139:
1742:(originally named Mac OS X) is based on
1550:
1387:A multikernel operating system treats a
1222:
964:
863:
723:
36:
32:Kernel (disambiguation) § Computing
4110:The logical design of Operating systems
3940:
3591:
3235:
3172:
3170:
3159:. 1965 Fall Joint Computer Conference.
2743:
2331:"A Language-Based Approach to Security"
2098:(Third ed.). Pearson. p. 17.
2059:
2057:
1849:, that controls the execution of other
1841:Supervisory program or supervisor is a
1571:, because they believed the purpose of
888:Modern monolithic kernels, such as the
216:
205:
14:
4974:
3960:
3884:"Policy/Mechanism separation in Hydra"
3689:
3637:
3601:ACM SIGARCH Computer Architecture News
3524:
3331:"The L4 microkernel family - Overview"
3236:Wheeler, David A. (October 12, 2004).
2770:
1981:Comparison of operating system kernels
1704:operating system development community
689:
619:Hardware- or language-based protection
302:) and the other for the applications (
232:
4474:
4448:
4025:
3281:
2136:
1750:, which was created by combining the
853:
816:Separation of protection and security
638:Advantages of this approach include:
530:hierarchical structure for protection
263:Memory management (operating systems)
4417:B.S. Chalk, A.T. Carter, R.W. Hind,
4314:ACM Transactions on Computer Systems
4308:Michael M. Swift; Brian N. Bershad;
4106:
3727:"The evolution of operating systems"
3528:An introduction to operating systems
3510:(first ed.). Elsevier Science.
3505:
3451:
3238:"Linux Kernel 2.6: It's Worth More!"
3217:from the original on 9 November 2010
3167:
2855:from the original on 1 February 2020
2075:from the original on 8 December 2006
2054:
1761:
1746:, which uses a hybrid kernel called
340:Using a high-level interface (Video
313:
256:
3888:ACM Sigops Operating Systems Review
3823:ACM SIGOPS Operating Systems Review
3771:Härtig, Hermann; Hohmuth, Michael;
3454:"Monolithic kernel vs. Microkernel"
3360:"The Fiasco microkernel - Overview"
2591:ACM Sigops Operating Systems Review
2291:ACM SIGOPS Operating Systems Review
1659:, have more than 13 million lines.
1121:Monolithic kernels vs. microkernels
736:, while the I/O devices are called
241:are defining the execution domain (
27:Core of a computer operating system
24:
4374:Andrew S. Tanenbaum, Herbert Bos,
4358:
3400:from the original on 19 April 2001
3323:
3122:"BSTJ version of C.ACM Unix paper"
2534:
2367:. pp. 303–314. Archived from
1891:from the hardware, resulting in a
1189:and to the increased frequency of
957:Since the modules run in the same
767:separation of mechanism and policy
25:
4998:
4433:
4281:Software: Practice and Experience
3912:Capability-based computer systems
3250:This community mostly gathers at
3090:"The Barrelfish operating system"
3029:
1836:
1768:Microsoft Windows version history
1655:, of modern Unix successors like
1591:files would be instances of some
1365:, for example one for high level
520:) and from malicious behaviours (
397:Peripheral Component Interconnect
328:Hardware/Software Interface (HSI)
4571:Object-oriented operating system
4137:Structured Computer Organization
3915:. Maynard, Mass: Digital Press.
3813:from the original on 2020-02-17.
3163:from the original on 2011-07-09.
3052:"KeyKOS Nanokernel Architecture"
3036:. 14 minutes in. Archived from
2617:Cooperating Sequential Processes
2439:from the original on 2011-07-21.
2343:from the original on 2018-12-22.
1880:operating systems starting with
1262:, which is based upon code from
629:language-based protection system
4381:Daniel P. Bovet, Marco Cesati,
4267:from the original on 2007-07-19
3929:from the original on 2007-07-13
3739:from the original on 2011-07-25
3491:: Addison-Wesley. p. 696.
3430:from the original on 2019-03-24
3412:
3381:
3370:from the original on 2006-06-16
3352:
3341:from the original on 2006-08-21
3312:from the original on 2011-08-20
3294:
3275:
3244:
3229:
3199:
3188:from the original on 2016-10-04
3178:"The Single Unix Specification"
3143:
3132:from the original on 2005-12-30
3114:
3082:
3062:
3044:
3023:
2974:from the original on 2014-12-18
2956:
2810:
2734:
2681:
2640:
2582:
2557:
2528:
2511:"Fine-grained kernel isolation"
2503:
2492:from the original on 2021-03-08
2443:
2418:
2375:
2269:
2032:
2019:
1451:RC 4000 Multiprogramming System
1376:
1213:hierarchical protection domains
981:
808:hierarchical protection domains
425:
406:As device management is a very
225:devices, network adapters, and
4581:Supercomputer operating system
3016:Hansen 73, section 7.3 p.233 "
2170:
2112:
2087:
2071:. Bellevue Linux Users Group.
2007:
1680:Berkeley Software Distribution
1457:Time-sharing operating systems
1408:Early operating system kernels
1316:
1165:
868:Diagram of a monolithic kernel
838:. More exotic designs such as
13:
1:
4225:(in Italian). Franco Angeli.
3856:. ACM/IEEE. pp. 341–348.
3282:Singh, Amit (December 2003).
2542:Pennsylvania State University
2425:Anderson, J. (October 1972).
2048:
1403:History of kernel development
1342:
757:Kernel-wide design approaches
511:
45:to the hardware of a computer
4556:Just enough operating system
4541:Distributed operating system
4141:Englewood Cliffs, New Jersey
3263:The Mega-Tokyo Message Board
1783:(not to be confused with an
1494:became a major focus of the
1414:History of operating systems
1258:uses a hybrid kernel called
526:adoption of this distinction
361:Only implementing primitives
7:
4669:User space and kernel space
4036:: Addison-Wesley. pp.
3696:Operating System Principles
3525:Deitel, Harvey M. (1984) .
2637:Brinch Hansen 70 pp.238–241
1986:Inter-process communication
1974:
1913:Development of microkernels
1563:During the design phase of
1236:Hybrid (or modular) kernels
1187:inter-process communication
1007:inter-process communication
812:capability-based addressing
751:inter-process communication
567:capability-based addressing
476:Using a software-simulated
251:inter-process communication
10:
5003:
4576:Real-time operating system
3946:"On µ-Kernel Construction"
3444:
3111:Hansen 2001 (os), pp.17–18
2908:Andrew Tanenbaum's website
1927:Carnegie Mellon University
1823:architecture of Windows NT
1810:in October 2001—replacing
1765:
1731:in 1984, bundled with its
1713:
1544:
1514:
1460:
1411:
1380:
1346:
1320:
1239:
985:
857:
539:) or dynamic (enforced at
429:
260:
174:with the CPU executing in
29:
18:Nucleus (operating system)
4911:
4848:
4794:
4772:Multilevel feedback queue
4767:Fixed-priority preemptive
4755:
4690:
4681:
4651:
4598:
4589:
4551:Hobbyist operating system
4546:Embedded operating system
4528:
4482:
4170:Communications of the ACM
4113:. Prentice-Hall. p.
4061:Communications of the ACM
3848:; Hoffman, R. L. (1981).
3703:: Prentice Hall. p.
3644:Communications of the ACM
3506:Ball, Stuart R. (2002) .
3484:Operating system concepts
2653:Communications of the ACM
1798:Microsoft also developed
1160:Tanenbaum–Torvalds debate
310:) take other approaches.
237:Key aspects necessary in
170:run entirely in a single
4982:Operating system kernels
4815:General protection fault
4566:Network operating system
4520:User features comparison
3252:Bona Fide OS Development
2182:Modern Operating Systems
2001:
1710:Classic Mac OS and macOS
1682:variant kernels such as
1640:graphical user interface
1510:
1467:In the decade preceding
1369:development and one for
1050:Most microkernels use a
102:, translating them into
4561:Mobile operating system
4326:10.1145/1047915.1047919
3986:2027/mdp.39015086560037
3909:Levy, Henry M. (1984).
3452:Roch, Benjamin (2004).
3420:"QNX Operating Systems"
2771:Nehmer, Jürgen (1991).
2696:. pp. 11.1–11.17.
2515:mars-research.github.io
2456:Proceedings of the IEEE
1610:In the Unix model, the
1540:
1486:time. For this reason,
1482:the system to get more
910:loadable kernel modules
651:Disadvantages include:
598:language-based security
507:Kernel design decisions
196:loadable kernel modules
108:central processing unit
4664:Loadable kernel module
4421:, Palgrave Macmillan (
4367:, Albert S. Woodhull,
4293:10.1002/spe.4380201404
4107:Shaw, Alan C. (1974).
4026:Lorin, Harold (1981).
3901:10.1145/1067629.806531
2478:10.1109/PROC.1975.9939
2027:memory management unit
1560:
1335: – to
1232:
1211:On the other end, the
1139:computer architectures
1127:trusted computing base
978:
869:
718:remote procedure calls
563:memory management unit
447:memory management unit
271:, usually achieved by
46:
4732:Process control block
4698:Computer multitasking
4536:Disk operating system
4182:10.1145/355616.364017
4084:10.1145/361268.361275
4056:Schroeder, Michael D.
4034:Boston, Massachusetts
3977:10.1145/356678.356682
3964:ACM Computing Surveys
3836:10.1145/269005.266660
3789:10.1145/268998.266660
3667:10.1145/362258.362278
3614:10.1145/859504.859506
3569:10.1145/356678.356680
3556:ACM Computing Surveys
3489:Boston, Massachusetts
3479:Silberschatz, Abraham
3390:"L4Ka - L4Ka Project"
3213:. 29 September 2010.
2703:10.1145/800001.811675
2666:10.1145/363717.363778
2603:10.1145/319344.319163
2393:10.1145/504450.504477
2304:10.1145/850697.850701
2255:. Prentice Hall PTR.
2042:for more information.
2015:Computer architecture
2013:It may depend on the
1931:L4 microkernel family
1845:, usually part of an
1781:operating environment
1554:
1329:interrupt controllers
1226:
1200:, (2) the particular
968:
867:
724:I/O device management
261:Further information:
106:instructions for the
40:
4903:Virtual tape library
4495:Forensic engineering
4133:Tanenbaum, Andrew S.
3364:os.inf.tu-dresden.de
3335:os.inf.tu-dresden.de
2386:. pp. 133–140.
2178:Tanenbaum, Andrew S.
2155:Wulf 1974 pp.337–345
1958:open-source software
1632:everything as a file
1424:"bare metal" machine
1137:system, but not all
401:Universal Serial Bus
337:Interfacing directly
217:Input/output devices
211:Random-access memory
206:Random-access memory
178:, mainly for speed.
159:, usually through a
115:application software
98:(I/O) requests from
43:application software
4912:Supporting concepts
4898:Virtual file system
4365:Andrew S. Tanenbaum
3153:; Vissotsky, V. A.
1897:full virtualization
1727:first launched its
1577:data transformation
1440:video game consoles
1115:high-level language
690:Process cooperation
239:resource management
233:Resource management
4835:Segmentation fault
4683:Process management
4389:David A. Patterson
3748:included in book:
3723:Hansen, Per Brinch
3691:Hansen, Per Brinch
3639:Hansen, Per Brinch
3424:blackberry.qnx.com
3268:2022-01-25 at the
3257:2022-01-17 at the
2968:en.wikiversity.org
2913:2015-08-05 at the
2902:2014-09-21 at the
2891:2013-05-26 at the
2880:2012-10-03 at the
2785:10.1007/BFb0024528
2779:. pp. 77–83.
2544:via techxplore.com
2120:Daemon (computing)
1561:
1393:distributed system
1233:
1171:Monolithic kernels
1037:Easier to maintain
979:
870:
854:Monolithic kernels
823:monolithic kernels
738:external processes
734:internal processes
269:virtual addressing
168:Monolithic kernels
47:
4987:Operating systems
4969:
4968:
4825:Memory protection
4796:Memory management
4790:
4789:
4782:Shortest job next
4677:
4676:
4476:Operating systems
4427:978-1-4039-0164-4
4413:
4410:978-0-12-820109-1
4232:978-88-204-2746-7
4150:978-0-13-148521-1
4143:: Prentice-Hall.
4124:978-0-13-540112-5
4047:978-0-201-14464-2
4029:Operating systems
3944:(December 1995).
3922:978-0-932376-22-0
3871:Intel Corporation
3798:978-0-89791-916-6
3763:978-0-387-95113-3
3714:978-0-13-637843-3
3593:Denning, Peter J.
3551:Denning, Peter J.
3542:978-0-201-14502-1
3517:978-0-7506-7534-5
3498:978-0-201-51379-0
3284:"XNU: The Kernel"
2929:Matthew Russell.
2886:groups.google.com
2851:. 29 March 1999.
2713:978-1-4503-7370-8
2403:978-1-4503-7339-5
2262:978-0-13-061014-0
2191:978-0-13-600663-3
2167:Silberschatz 1991
2105:978-0-13-409266-9
1773:Microsoft Windows
1762:Microsoft Windows
1736:personal computer
1678:, as well as the
1276:monolithic kernel
1248:Microsoft Windows
999:memory management
860:Monolithic kernel
803:Per Brinch Hansen
764:The principle of
606:abstraction level
314:Device management
257:Memory management
149:abstraction layer
135:memory protection
57:at the core of a
16:(Redirected from
4994:
4924:Computer network
4688:
4687:
4596:
4595:
4469:
4462:
4455:
4446:
4445:
4403:
4393:John L. Hennessy
4353:
4304:
4275:
4273:
4272:
4266:
4259:
4247:
4245:
4244:
4235:. Archived from
4215:
4213:
4212:
4206:
4200:. Archived from
4167:
4154:
4128:
4103:
4077:
4051:
4022:
4020:
4019:
4014:
4006:
3988:
3957:
3952:. Archived from
3937:
3935:
3934:
3905:
3903:
3874:
3868:
3857:
3840:
3838:
3814:
3767:
3747:
3745:
3744:
3738:
3731:
3718:
3701:Englewood Cliffs
3686:
3660:
3634:
3616:
3588:
3546:
3521:
3502:
3474:
3472:
3471:
3465:
3459:. Archived from
3458:
3439:
3438:
3436:
3435:
3416:
3410:
3409:
3407:
3405:
3385:
3379:
3378:
3376:
3375:
3356:
3350:
3349:
3347:
3346:
3327:
3321:
3320:
3318:
3317:
3298:
3292:
3291:
3286:. Archived from
3279:
3273:
3248:
3242:
3241:
3233:
3227:
3226:
3224:
3222:
3207:"Unix's Revenge"
3203:
3197:
3196:
3194:
3193:
3174:
3165:
3164:
3147:
3141:
3140:
3138:
3137:
3118:
3112:
3109:
3103:
3100:
3094:
3093:
3086:
3080:
3079:
3077:
3066:
3060:
3059:
3054:. Archived from
3048:
3042:
3041:
3027:
3021:
3014:
3008:
3005:
2999:
2996:
2983:
2982:
2980:
2979:
2960:
2954:
2953:
2947:
2946:
2937:. Archived from
2926:
2917:
2871:
2865:
2864:
2862:
2860:
2841:
2832:
2828:
2817:
2814:
2808:
2807:
2768:
2762:
2759:
2753:
2750:
2741:
2738:
2732:
2731:
2729:
2728:
2705:
2685:
2679:
2678:
2668:
2644:
2638:
2635:
2620:
2615:Dijkstra, E. W.
2613:
2607:
2606:
2586:
2580:
2579:
2577:
2575:
2570:
2561:
2555:
2554:
2552:
2550:
2532:
2526:
2525:
2523:
2521:
2507:
2501:
2500:
2498:
2497:
2471:
2462:(9): 1278–1308.
2447:
2441:
2440:
2438:
2431:
2422:
2416:
2415:
2395:
2379:
2373:
2372:
2356:
2345:
2344:
2342:
2335:
2326:
2317:
2316:
2306:
2282:
2276:
2273:
2267:
2266:
2244:
2238:
2235:
2226:
2223:
2217:
2214:
2208:
2205:
2199:
2198:
2174:
2168:
2165:
2156:
2153:
2134:
2131:
2122:
2116:
2110:
2109:
2091:
2085:
2084:
2082:
2080:
2061:
2043:
2036:
2030:
2023:
2017:
2011:
1991:Operating system
1971:microkernel OS.
1954:embedded systems
1941:are able to run
1847:operating system
1843:computer program
1831:Mach microkernel
1785:operating system
1612:operating system
1569:device as a file
1535:graphics.library
1501:memory hierarchy
1444:embedded systems
1270:(OSFMK 7.3) and
1191:context switches
1156:Andrew Tanenbaum
1131:memory footprint
1095:memory footprint
1019:context switches
926:embedded systems
904:kernel, and the
490:Using a special
420:context switches
393:peripheral buses
161:wrapper function
63:operating system
55:computer program
21:
5002:
5001:
4997:
4996:
4995:
4993:
4992:
4991:
4972:
4971:
4970:
4965:
4907:
4868:Defragmentation
4853:
4844:
4830:Protection ring
4799:
4786:
4758:
4751:
4673:
4647:
4585:
4524:
4478:
4473:
4436:
4401:Morgan Kaufmann
4361:
4359:Further reading
4356:
4270:
4268:
4264:
4257:
4242:
4240:
4233:
4210:
4208:
4204:
4165:
4151:
4125:
4048:
4017:
4015:
4012:
4008:
3942:Liedtke, Jochen
3932:
3930:
3923:
3866:
3860:
3844:Houdek, M. E.;
3799:
3773:Liedtke, Jochen
3764:
3742:
3740:
3736:
3729:
3715:
3658:10.1.1.105.4204
3543:
3518:
3499:
3469:
3467:
3463:
3456:
3447:
3442:
3433:
3431:
3418:
3417:
3413:
3403:
3401:
3386:
3382:
3373:
3371:
3358:
3357:
3353:
3344:
3342:
3329:
3328:
3324:
3315:
3313:
3300:
3299:
3295:
3280:
3276:
3270:Wayback Machine
3259:Wayback Machine
3249:
3245:
3234:
3230:
3220:
3218:
3205:
3204:
3200:
3191:
3189:
3176:
3175:
3168:
3148:
3144:
3135:
3133:
3120:
3119:
3115:
3110:
3106:
3101:
3097:
3088:
3087:
3083:
3075:
3067:
3063:
3050:
3049:
3045:
3028:
3024:
3015:
3011:
3006:
3002:
2997:
2986:
2977:
2975:
2962:
2961:
2957:
2944:
2942:
2927:
2920:
2915:Wayback Machine
2904:Wayback Machine
2893:Wayback Machine
2882:Wayback Machine
2872:
2868:
2858:
2856:
2843:
2842:
2835:
2829:
2820:
2815:
2811:
2795:
2769:
2765:
2760:
2756:
2751:
2744:
2739:
2735:
2726:
2724:
2714:
2686:
2682:
2659:(10): 659–665.
2645:
2641:
2636:
2623:
2614:
2610:
2587:
2583:
2573:
2571:
2568:
2562:
2558:
2548:
2546:
2533:
2529:
2519:
2517:
2509:
2508:
2504:
2495:
2493:
2469:10.1.1.126.9257
2448:
2444:
2436:
2429:
2423:
2419:
2404:
2380:
2376:
2357:
2348:
2340:
2333:
2327:
2320:
2283:
2279:
2274:
2270:
2263:
2245:
2241:
2236:
2229:
2224:
2220:
2215:
2211:
2206:
2202:
2192:
2175:
2171:
2166:
2159:
2154:
2137:
2132:
2125:
2117:
2113:
2106:
2092:
2088:
2078:
2076:
2063:
2062:
2055:
2051:
2046:
2040:Protection ring
2037:
2033:
2024:
2020:
2012:
2008:
2004:
1977:
1965:highly reliable
1921:, developed by
1915:
1901:Virtual Machine
1867:data processing
1855:work scheduling
1839:
1770:
1764:
1754:kernel and the
1722:
1714:Main articles:
1712:
1601:file management
1549:
1543:
1519:
1513:
1465:
1459:
1428:program loaders
1416:
1410:
1405:
1397:message passing
1385:
1379:
1351:
1345:
1325:
1319:
1244:
1238:
1179:message passing
1168:
1123:
1093:Larger running
1052:message passing
990:
984:
862:
856:
759:
726:
710:message passing
695:Edsger Dijkstra
692:
621:
518:fault tolerance
514:
509:
434:
428:
384:embedded system
316:
265:
259:
247:synchronization
235:
227:display devices
219:
208:
176:supervisor mode
104:data-processing
35:
28:
23:
22:
15:
12:
11:
5:
5000:
4990:
4989:
4984:
4967:
4966:
4964:
4963:
4958:
4957:
4956:
4954:User interface
4951:
4941:
4936:
4931:
4926:
4921:
4915:
4913:
4909:
4908:
4906:
4905:
4900:
4895:
4890:
4885:
4880:
4878:File attribute
4875:
4870:
4865:
4859:
4857:
4846:
4845:
4843:
4842:
4840:Virtual memory
4837:
4832:
4827:
4822:
4817:
4812:
4806:
4804:
4792:
4791:
4788:
4787:
4785:
4784:
4779:
4774:
4769:
4763:
4761:
4753:
4752:
4750:
4749:
4744:
4739:
4734:
4729:
4724:
4719:
4714:
4712:Context switch
4709:
4694:
4692:
4685:
4679:
4678:
4675:
4674:
4672:
4671:
4666:
4661:
4655:
4653:
4649:
4648:
4646:
4645:
4640:
4635:
4630:
4625:
4620:
4615:
4610:
4604:
4602:
4593:
4587:
4586:
4584:
4583:
4578:
4573:
4568:
4563:
4558:
4553:
4548:
4543:
4538:
4532:
4530:
4526:
4525:
4523:
4522:
4517:
4512:
4507:
4502:
4497:
4492:
4486:
4484:
4480:
4479:
4472:
4471:
4464:
4457:
4449:
4443:
4442:
4435:
4434:External links
4432:
4431:
4430:
4415:
4386:
4379:
4372:
4360:
4357:
4355:
4354:
4305:
4276:
4248:
4231:
4216:
4176:(6): 337–345.
4155:
4149:
4129:
4123:
4104:
4075:10.1.1.83.8304
4068:(3): 157–170.
4052:
4046:
4023:
3971:(4): 409–445.
3958:
3956:on 2007-03-13.
3938:
3921:
3906:
3894:(5): 132–140.
3875:
3858:
3841:
3797:
3768:
3762:
3719:
3713:
3687:
3651:(4): 238–241.
3635:
3595:(April 1980).
3589:
3563:(4): 359–389.
3547:
3541:
3522:
3516:
3503:
3497:
3475:
3448:
3446:
3443:
3441:
3440:
3411:
3380:
3351:
3322:
3293:
3290:on 2011-08-12.
3274:
3243:
3228:
3198:
3182:The Open Group
3166:
3151:Corbató, F. J.
3142:
3113:
3104:
3095:
3081:
3061:
3058:on 2011-06-21.
3043:
3040:on 2021-10-30.
3022:
3009:
3000:
2984:
2955:
2935:O'Reilly Media
2918:
2866:
2833:
2818:
2809:
2805:] systems.
2793:
2763:
2754:
2742:
2733:
2712:
2680:
2639:
2621:
2608:
2597:(5): 170–185.
2581:
2556:
2535:Fetzer, Mary.
2527:
2502:
2442:
2417:
2402:
2374:
2371:on 2007-06-21.
2346:
2318:
2277:
2268:
2261:
2239:
2227:
2218:
2209:
2200:
2190:
2169:
2157:
2135:
2123:
2111:
2104:
2086:
2052:
2050:
2047:
2045:
2044:
2031:
2018:
2005:
2003:
2000:
1999:
1998:
1996:Virtual memory
1993:
1988:
1983:
1976:
1973:
1948:Additionally,
1923:Richard Rashid
1914:
1911:
1853:and regulates
1838:
1837:IBM Supervisor
1835:
1804:Windows NT 3.1
1766:Main article:
1763:
1760:
1729:classic Mac OS
1716:Classic Mac OS
1711:
1708:
1582:For instance,
1545:Main article:
1542:
1539:
1515:Main article:
1512:
1509:
1505:virtual memory
1492:access control
1461:Main article:
1458:
1455:
1412:Main article:
1409:
1406:
1404:
1401:
1381:Main article:
1378:
1375:
1347:Main article:
1344:
1341:
1337:device drivers
1321:Main article:
1318:
1315:
1314:
1313:
1310:
1302:
1301:
1298:
1295:
1240:Main article:
1237:
1234:
1206:implementation
1167:
1164:
1152:Linus Torvalds
1135:virtual memory
1122:
1119:
1107:
1106:
1103:
1100:
1097:
1048:
1047:
1044:
1041:
1038:
986:Main article:
983:
980:
963:
962:
955:
952:
949:
945:
858:Main article:
855:
852:
836:hybrid kernels
793:security token
789:
788:
782:
758:
755:
725:
722:
691:
688:
672:
671:
660:
649:
648:
644:
620:
617:
513:
510:
508:
505:
504:
503:
499:
488:
481:
430:Main article:
427:
424:
376:
375:
368:
362:
359:
352:
351:
348:
345:
338:
324:device drivers
315:
312:
258:
255:
234:
231:
218:
215:
207:
204:
131:address spaces
72:device drivers
26:
9:
6:
4:
3:
2:
4999:
4988:
4985:
4983:
4980:
4979:
4977:
4962:
4959:
4955:
4952:
4950:
4947:
4946:
4945:
4942:
4940:
4937:
4935:
4932:
4930:
4927:
4925:
4922:
4920:
4917:
4916:
4914:
4910:
4904:
4901:
4899:
4896:
4894:
4891:
4889:
4886:
4884:
4881:
4879:
4876:
4874:
4871:
4869:
4866:
4864:
4861:
4860:
4858:
4856:
4851:
4847:
4841:
4838:
4836:
4833:
4831:
4828:
4826:
4823:
4821:
4820:Memory paging
4818:
4816:
4813:
4811:
4808:
4807:
4805:
4802:
4797:
4793:
4783:
4780:
4778:
4775:
4773:
4770:
4768:
4765:
4764:
4762:
4760:
4754:
4748:
4745:
4743:
4740:
4738:
4735:
4733:
4730:
4728:
4725:
4723:
4720:
4718:
4715:
4713:
4710:
4707:
4703:
4699:
4696:
4695:
4693:
4689:
4686:
4684:
4680:
4670:
4667:
4665:
4662:
4660:
4659:Device driver
4657:
4656:
4654:
4650:
4644:
4641:
4639:
4636:
4634:
4631:
4629:
4626:
4624:
4621:
4619:
4616:
4614:
4611:
4609:
4606:
4605:
4603:
4601:
4600:Architectures
4597:
4594:
4592:
4588:
4582:
4579:
4577:
4574:
4572:
4569:
4567:
4564:
4562:
4559:
4557:
4554:
4552:
4549:
4547:
4544:
4542:
4539:
4537:
4534:
4533:
4531:
4527:
4521:
4518:
4516:
4513:
4511:
4508:
4506:
4503:
4501:
4498:
4496:
4493:
4491:
4488:
4487:
4485:
4481:
4477:
4470:
4465:
4463:
4458:
4456:
4451:
4450:
4447:
4441:
4438:
4437:
4428:
4424:
4420:
4416:
4411:
4407:
4402:
4398:
4394:
4390:
4387:
4384:
4380:
4377:
4373:
4370:
4366:
4363:
4362:
4351:
4347:
4343:
4339:
4335:
4331:
4327:
4323:
4319:
4315:
4311:
4310:Henry M. Levy
4306:
4302:
4298:
4294:
4290:
4286:
4282:
4277:
4263:
4256:
4255:
4249:
4239:on 2012-06-27
4238:
4234:
4228:
4224:
4223:
4217:
4207:on 2007-09-26
4203:
4199:
4195:
4191:
4187:
4183:
4179:
4175:
4171:
4164:
4160:
4156:
4152:
4146:
4142:
4138:
4134:
4130:
4126:
4120:
4116:
4112:
4111:
4105:
4101:
4097:
4093:
4089:
4085:
4081:
4076:
4071:
4067:
4063:
4062:
4057:
4053:
4049:
4043:
4039:
4035:
4031:
4030:
4024:
4011:
4004:
4000:
3996:
3992:
3987:
3982:
3978:
3974:
3970:
3966:
3965:
3959:
3955:
3951:
3947:
3943:
3939:
3928:
3924:
3918:
3914:
3913:
3907:
3902:
3897:
3893:
3889:
3885:
3881:
3880:Wulf, William
3876:
3872:
3865:
3864:
3859:
3855:
3851:
3847:
3846:Soltis, F. G.
3842:
3837:
3832:
3828:
3824:
3820:
3812:
3808:
3804:
3800:
3794:
3790:
3786:
3782:
3778:
3774:
3769:
3765:
3759:
3755:
3754:
3735:
3728:
3724:
3720:
3716:
3710:
3706:
3702:
3698:
3697:
3692:
3688:
3684:
3680:
3676:
3672:
3668:
3664:
3659:
3654:
3650:
3646:
3645:
3640:
3636:
3632:
3628:
3624:
3620:
3615:
3610:
3606:
3602:
3598:
3594:
3590:
3586:
3582:
3578:
3574:
3570:
3566:
3562:
3558:
3557:
3552:
3548:
3544:
3538:
3534:
3530:
3529:
3523:
3519:
3513:
3509:
3504:
3500:
3494:
3490:
3486:
3485:
3480:
3476:
3466:on 2006-11-01
3462:
3455:
3450:
3449:
3429:
3425:
3421:
3415:
3399:
3395:
3391:
3384:
3369:
3365:
3361:
3355:
3340:
3336:
3332:
3326:
3311:
3307:
3303:
3297:
3289:
3285:
3278:
3271:
3267:
3264:
3260:
3256:
3253:
3247:
3239:
3232:
3216:
3212:
3208:
3202:
3187:
3183:
3179:
3173:
3171:
3162:
3158:
3157:
3152:
3146:
3131:
3127:
3126:bell-labs.com
3123:
3117:
3108:
3099:
3091:
3085:
3074:
3073:
3065:
3057:
3053:
3047:
3039:
3035:
3034:
3026:
3019:
3013:
3004:
2995:
2993:
2991:
2989:
2973:
2969:
2965:
2959:
2952:
2941:on 2007-12-08
2940:
2936:
2932:
2925:
2923:
2916:
2912:
2909:
2905:
2901:
2898:
2894:
2890:
2887:
2883:
2879:
2876:
2870:
2854:
2850:
2849:1-56592-582-3
2846:
2840:
2838:
2827:
2825:
2823:
2813:
2806:
2804:
2803:
2796:
2794:3-540-54987-0
2790:
2786:
2782:
2778:
2774:
2767:
2758:
2749:
2747:
2737:
2723:
2719:
2715:
2709:
2704:
2699:
2695:
2691:
2684:
2676:
2672:
2667:
2662:
2658:
2654:
2650:
2643:
2634:
2632:
2630:
2628:
2626:
2618:
2612:
2604:
2600:
2596:
2592:
2585:
2567:
2560:
2545:
2543:
2538:
2531:
2516:
2512:
2506:
2491:
2487:
2483:
2479:
2475:
2470:
2465:
2461:
2457:
2453:
2446:
2435:
2428:
2421:
2413:
2409:
2405:
2399:
2394:
2389:
2385:
2378:
2370:
2366:
2362:
2355:
2353:
2351:
2339:
2332:
2325:
2323:
2314:
2310:
2305:
2300:
2296:
2292:
2288:
2281:
2272:
2264:
2258:
2254:
2250:
2243:
2234:
2232:
2222:
2213:
2204:
2197:
2193:
2187:
2183:
2179:
2173:
2164:
2162:
2152:
2150:
2148:
2146:
2144:
2142:
2140:
2130:
2128:
2121:
2115:
2107:
2101:
2097:
2090:
2074:
2070:
2066:
2060:
2058:
2053:
2041:
2035:
2028:
2022:
2016:
2010:
2006:
1997:
1994:
1992:
1989:
1987:
1984:
1982:
1979:
1978:
1972:
1970:
1966:
1962:
1959:
1955:
1951:
1946:
1944:
1940:
1936:
1932:
1928:
1924:
1920:
1910:
1908:
1907:
1902:
1898:
1895:that enabled
1894:
1890:
1885:
1883:
1879:
1875:
1870:
1868:
1864:
1863:error actions
1860:
1856:
1852:
1848:
1844:
1834:
1832:
1828:
1824:
1819:
1817:
1813:
1809:
1805:
1801:
1796:
1794:
1790:
1786:
1782:
1778:
1774:
1769:
1759:
1757:
1753:
1749:
1745:
1741:
1737:
1734:
1730:
1726:
1721:
1717:
1707:
1705:
1701:
1697:
1693:
1689:
1688:DragonFly BSD
1685:
1681:
1677:
1673:
1669:
1668:distributions
1665:
1660:
1658:
1654:
1650:
1649:lines of code
1645:
1641:
1637:
1633:
1628:
1626:
1622:
1618:
1613:
1608:
1606:
1602:
1598:
1594:
1590:
1585:
1580:
1578:
1574:
1570:
1566:
1558:
1553:
1548:
1538:
1536:
1532:
1527:
1524:
1518:
1508:
1506:
1502:
1497:
1493:
1489:
1485:
1481:
1476:
1474:
1470:
1464:
1454:
1452:
1449:In 1969, the
1447:
1445:
1441:
1437:
1433:
1429:
1425:
1421:
1415:
1400:
1398:
1394:
1390:
1384:
1374:
1372:
1368:
1364:
1360:
1355:
1350:
1340:
1338:
1334:
1330:
1324:
1311:
1308:
1307:
1306:
1299:
1296:
1293:
1292:
1291:
1287:
1285:
1281:
1280:network stack
1277:
1273:
1269:
1265:
1261:
1257:
1253:
1249:
1243:
1242:Hybrid kernel
1230:
1229:hybrid kernel
1225:
1221:
1219:
1214:
1209:
1207:
1203:
1199:
1194:
1192:
1188:
1182:
1180:
1176:
1172:
1163:
1161:
1157:
1153:
1149:
1143:
1140:
1136:
1132:
1128:
1118:
1116:
1111:
1104:
1101:
1098:
1096:
1092:
1091:
1090:
1087:
1085:
1080:
1078:
1074:
1070:
1066:
1062:
1057:
1053:
1045:
1042:
1039:
1036:
1035:
1034:
1032:
1028:
1022:
1020:
1016:
1012:
1008:
1004:
1000:
996:
989:
976:
972:
967:
960:
959:address space
956:
953:
950:
946:
943:
939:
935:
934:
933:
929:
927:
923:
919:
913:
911:
907:
903:
899:
895:
891:
886:
882:
879:
875:
866:
861:
851:
849:
845:
841:
837:
832:
828:
824:
819:
817:
813:
809:
804:
800:
796:
794:
786:
783:
780:
777:
776:
775:
773:
769:
768:
762:
754:
752:
747:
746:device driver
741:
739:
735:
731:
730:Brinch Hansen
721:
719:
715:
714:shared memory
711:
707:
703:
700:
696:
687:
685:
681:
677:
669:
665:
661:
658:
654:
653:
652:
645:
641:
640:
639:
636:
634:
630:
625:
616:
614:
609:
607:
602:
600:
599:
594:
590:
585:
581:
579:
574:
570:
568:
564:
559:
555:
553:
548:
546:
542:
538:
533:
531:
527:
523:
519:
500:
497:
493:
489:
486:
482:
479:
475:
474:
473:
469:
467:
463:
458:
456:
452:
448:
443:
438:
433:
423:
421:
417:
413:
409:
404:
402:
398:
394:
390:
389:plug and play
385:
380:
373:
369:
367:
363:
360:
357:
356:
355:
349:
346:
343:
339:
336:
335:
334:
331:
329:
325:
321:
311:
309:
305:
301:
296:
294:
293:demand paging
290:
286:
280:
278:
274:
270:
264:
254:
252:
248:
244:
243:address space
240:
230:
228:
224:
214:
212:
203:
199:
197:
193:
189:
185:
181:
177:
173:
172:address space
169:
164:
162:
158:
154:
150:
147:
143:
140:The kernel's
138:
136:
132:
128:
124:
120:
116:
111:
109:
105:
101:
97:
93:
89:
85:
81:
77:
73:
69:
64:
60:
56:
52:
44:
39:
33:
19:
4855:file systems
4747:Time-sharing
4590:
4418:
4396:
4382:
4375:
4368:
4317:
4313:
4284:
4280:
4269:. Retrieved
4253:
4241:. Retrieved
4237:the original
4221:
4209:. Retrieved
4202:the original
4173:
4169:
4136:
4109:
4065:
4059:
4028:
4016:. Retrieved
3968:
3962:
3954:the original
3949:
3931:. Retrieved
3911:
3891:
3887:
3862:
3853:
3829:(5): 66–77.
3826:
3822:
3780:
3752:
3741:. Retrieved
3695:
3648:
3642:
3604:
3600:
3560:
3554:
3527:
3507:
3483:
3468:. Retrieved
3461:the original
3432:. Retrieved
3423:
3414:
3402:. Retrieved
3394:www.l4ka.org
3393:
3383:
3372:. Retrieved
3363:
3354:
3343:. Retrieved
3334:
3325:
3314:. Retrieved
3305:
3296:
3288:the original
3277:
3246:
3231:
3219:. Retrieved
3210:
3201:
3190:. Retrieved
3155:
3145:
3134:. Retrieved
3125:
3116:
3107:
3098:
3084:
3071:
3064:
3056:the original
3046:
3038:the original
3032:
3030:Magee, Jim.
3025:
3017:
3012:
3003:
2976:. Retrieved
2967:
2958:
2949:
2943:. Retrieved
2939:the original
2869:
2857:. Retrieved
2848:
2812:
2800:
2798:
2776:
2766:
2761:Denning 1980
2757:
2740:Baiardi 1988
2736:
2725:. Retrieved
2693:
2683:
2656:
2652:
2642:
2616:
2611:
2594:
2590:
2584:
2572:. Retrieved
2559:
2549:15 September
2547:. Retrieved
2540:
2530:
2520:15 September
2518:. Retrieved
2514:
2505:
2494:. Retrieved
2459:
2455:
2445:
2420:
2383:
2377:
2369:the original
2364:
2297:(3): 22–32.
2294:
2290:
2280:
2271:
2252:
2242:
2225:Schroeder 72
2221:
2212:
2207:Denning 1976
2203:
2195:
2181:
2172:
2114:
2095:
2089:
2079:15 September
2077:. Retrieved
2068:
2034:
2021:
2009:
1969:self-healing
1947:
1916:
1904:
1900:
1886:
1871:
1861:operations,
1859:input/output
1840:
1820:
1797:
1771:
1723:
1666:in the many
1664:Linux kernel
1661:
1629:
1611:
1609:
1597:Virtualizing
1588:
1581:
1562:
1534:
1531:exec.library
1530:
1520:
1477:
1473:time-sharing
1466:
1463:Time-sharing
1448:
1419:
1417:
1386:
1377:Multikernels
1356:
1352:
1326:
1303:
1288:
1245:
1210:
1205:
1201:
1197:
1195:
1183:
1175:kernel space
1169:
1144:
1124:
1112:
1108:
1088:
1083:
1081:
1049:
1023:
1014:
1003:multitasking
995:system calls
991:
982:Microkernels
930:
914:
900:kernel, the
896:kernel, the
890:Linux kernel
887:
883:
878:Ken Thompson
871:
831:microkernels
827:kernel space
820:
801:
797:
790:
784:
778:
771:
765:
763:
760:
742:
737:
733:
727:
693:
673:
664:type systems
650:
637:
626:
622:
610:
603:
596:
589:cryptography
586:
582:
575:
571:
560:
556:
549:
537:compile time
534:
515:
470:
459:
442:machine-code
439:
435:
426:System calls
405:
381:
377:
353:
332:
317:
300:kernel space
297:
281:
277:segmentation
266:
236:
220:
209:
200:
198:at runtime.
192:Linux kernel
180:Microkernels
165:
139:
123:kernel space
112:
96:input/output
50:
48:
4873:Device file
4863:Boot loader
4777:Round-robin
4702:Cooperative
4638:Rump kernel
4628:Multikernel
4618:Microkernel
4515:Usage share
4287:: S35–S67.
3306:windows.com
2897:oreilly.com
2574:20 December
1876:'s line of
1827:microkernel
1756:Mach kernel
1593:lower level
1573:computation
1383:Multikernel
1317:Nanokernels
1268:Mach kernel
1166:Performance
988:Microkernel
971:microkernel
840:nanokernels
684:Singularity
662:Inflexible
578:page tables
492:system call
432:System call
320:peripherals
308:Singularity
157:system call
92:peripherals
86:(after the
4976:Categories
4803:protection
4759:algorithms
4757:Scheduling
4706:Preemptive
4652:Components
4623:Monolithic
4490:Comparison
4271:2007-07-16
4243:2006-10-10
4211:2007-07-18
4018:2023-12-20
3933:2007-07-18
3743:2006-10-24
3607:(2): 4–7.
3470:2006-10-12
3434:2019-03-24
3374:2006-07-10
3345:2006-08-11
3316:2019-03-24
3211:asymco.com
3192:2016-09-29
3136:2006-08-17
2998:Liedtke 95
2978:2014-12-18
2945:2008-12-09
2727:2023-12-20
2496:2007-07-15
2049:References
1956:, and the
1893:hypervisor
1816:Windows 11
1812:Windows 9x
1808:Windows XP
1800:Windows NT
1793:Windows Me
1789:Windows 9x
1644:Networking
1625:user space
1389:multi-core
1343:Exokernels
1323:Nanokernel
1284:filesystem
1011:networking
876:developer
844:exokernels
779:Mechanism:
706:semaphores
512:Protection
395:, such as
372:PostScript
304:user space
285:hard drive
184:modularity
127:user space
88:bootloader
4893:Partition
4810:Bus error
4737:Real-time
4717:Interrupt
4643:Unikernel
4608:Exokernel
4350:208013080
4342:0734-2071
4334:1557-7333
4190:0001-0782
4092:0001-0782
4070:CiteSeerX
3995:0360-0300
3675:0001-0782
3653:CiteSeerX
3623:0163-5964
3585:207736773
3577:0360-0300
3221:2 October
3007:Härtig 97
2464:CiteSeerX
2237:Linden 76
2133:Roch 2004
1939:Pistachio
1917:Although
1878:mainframe
1795:in 2000.
1733:Macintosh
1595:concept.
1557:Unix-like
1523:Commodore
1507:systems.
1432:debuggers
1373:control.
1371:real-time
1359:unikernel
1349:Exokernel
772:mechanism
680:Microsoft
668:type safe
647:hardware.
613:isolation
552:CPU modes
502:requests.
485:call gate
478:interrupt
462:C library
451:C library
399:(PCI) or
151:. When a
146:low-level
142:interface
119:hard disk
4939:Live USB
4801:resource
4691:Concepts
4529:Variants
4510:Timeline
4301:26329062
4262:Archived
4159:Wulf, W.
4135:(1979).
4100:14422402
4003:16720589
3927:Archived
3882:(1975).
3811:Archived
3734:Archived
3725:(2001).
3693:(1973).
3631:14065743
3428:Archived
3404:24 March
3398:Archived
3368:Archived
3339:Archived
3310:Archived
3266:Archived
3255:Archived
3215:Archived
3186:Archived
3161:Archived
3130:Archived
2972:Archived
2911:Archived
2900:Archived
2889:Archived
2878:Archived
2859:24 March
2853:Archived
2752:Levin 75
2722:17709902
2675:14550794
2490:Archived
2434:Archived
2412:10027108
2338:Archived
2313:17487360
2180:(2008).
2073:Archived
2065:"Kernel"
1975:See also
1869:system.
1851:routines
1636:terminal
1584:printers
1488:security
1420:required
1218:by value
1216:copying
1202:concepts
1198:approach
1077:Redox OS
1061:GNU Hurd
948:program.
657:bytecode
633:compiler
593:compiler
541:run time
522:security
483:Using a
453:such as
100:software
59:computer
4934:Live CD
4888:Journal
4852:access,
4850:Storage
4727:Process
4633:vkernel
4500:History
4483:General
4198:8011765
4038:161–186
3873:. 2002.
3807:1706253
3683:9414037
3445:Sources
2875:dina.dk
1692:OpenBSD
1684:FreeBSD
1676:IBM AIX
1617:locking
1559:systems
1517:AmigaOS
1496:Multics
1331:or the
1282:or the
1272:FreeBSD
1254:'s own
1084:servers
1069:MkLinux
1015:servers
975:servers
969:In the
918:muLinux
906:Solaris
894:FreeBSD
785:Policy:
753:(IPC).
545:Denning
275:and/or
188:MINIX 3
153:process
84:startup
4742:Thread
4613:Hybrid
4591:Kernel
4425:
4408:
4348:
4340:
4332:
4299:
4229:
4196:
4188:
4147:
4121:
4098:
4090:
4072:
4044:
4001:
3993:
3919:
3805:
3795:
3760:
3711:
3681:
3673:
3655:
3629:
3621:
3583:
3575:
3539:
3514:
3495:
2791:
2720:
2710:
2673:
2486:269166
2484:
2466:
2410:
2400:
2311:
2259:
2188:
2102:
1935:Fiasco
1882:OS/360
1777:MS-DOS
1752:4.3BSD
1744:Darwin
1698:, and
1696:NetBSD
1005:, and
892:, the
821:While
699:atomic
464:or an
273:paging
94:, and
78:&
68:memory
51:kernel
4944:Shell
4883:Inode
4346:S2CID
4330:eISSN
4297:S2CID
4265:(PDF)
4258:(PDF)
4205:(PDF)
4194:S2CID
4166:(PDF)
4096:S2CID
4013:(PDF)
3999:S2CID
3867:(PDF)
3803:S2CID
3737:(PDF)
3730:(PDF)
3679:S2CID
3627:S2CID
3581:S2CID
3464:(PDF)
3457:(PDF)
3076:(PDF)
2718:S2CID
2671:S2CID
2569:(PDF)
2482:S2CID
2437:(PDF)
2430:(PDF)
2408:S2CID
2341:(PDF)
2334:(PDF)
2309:S2CID
2069:Linfo
2002:Notes
1961:MINIX
1943:Linux
1889:state
1740:macOS
1725:Apple
1720:macOS
1700:macOS
1653:Linux
1605:pipes
1526:Amiga
1511:Amiga
1333:timer
1264:OSF/1
1256:macOS
1252:Apple
1148:Linux
1065:MINIX
922:Linux
902:HP-UX
455:Glibc
366:TWAIN
144:is a
80:cache
53:is a
4505:List
4423:ISBN
4406:ISBN
4338:ISSN
4227:ISBN
4186:ISSN
4145:ISBN
4119:ISBN
4088:ISSN
4042:ISBN
3991:ISSN
3917:ISBN
3793:ISBN
3758:ISBN
3709:ISBN
3671:ISSN
3619:ISSN
3573:ISSN
3537:ISBN
3512:ISBN
3493:ISBN
3406:2019
3223:2010
2906:and
2861:2019
2789:ISBN
2708:ISBN
2576:2023
2551:2022
2522:2022
2398:ISBN
2257:ISBN
2186:ISBN
2118:cf.
2100:ISBN
2081:2016
1967:and
1937:and
1919:Mach
1821:The
1718:and
1619:and
1575:was
1565:Unix
1547:Unix
1541:Unix
1521:The
1490:and
1480:hack
1469:Unix
1442:and
1430:and
1227:The
1154:and
1075:and
1056:port
1031:Hurd
1029:and
938:libc
874:UNIX
842:and
716:and
702:lock
678:and
416:port
342:BIOS
249:and
49:The
4961:PXE
4949:CLI
4929:HAL
4919:API
4722:IPC
4322:doi
4289:doi
4178:doi
4115:304
4080:doi
3981:hdl
3973:doi
3896:doi
3831:doi
3785:doi
3705:496
3663:doi
3609:doi
3565:doi
3533:673
3261:,
2802:sic
2781:doi
2698:doi
2661:doi
2599:doi
2474:doi
2388:doi
2299:doi
1950:QNX
1925:at
1903:or
1874:IBM
1748:XNU
1672:GNU
1670:of
1657:GNU
1621:I/O
1589:and
1484:CPU
1436:ROM
1363:API
1274:'s
1266:'s
1260:XNU
1193:.
1073:QNX
1027:QNX
942:gdb
924:in
898:AIX
848:Xen
829:),
818:).
682:'s
496:x86
466:API
412:I/O
289:RAM
223:USB
76:CPU
61:'s
4978::
4704:,
4429:).
4399:,
4395:,
4391:,
4344:.
4336:.
4328:.
4318:23
4316:.
4295:.
4285:20
4283:.
4260:.
4192:.
4184:.
4174:17
4172:.
4168:.
4139:.
4117:.
4094:.
4086:.
4078:.
4066:15
4064:.
4040:.
4032:.
4007:,
3997:.
3989:.
3979:.
3967:.
3948:.
3925:.
3890:.
3886:.
3869:.
3852:.
3827:31
3825:.
3821:.
3815:,
3809:.
3801:.
3791:.
3779:.
3732:.
3707:.
3699:.
3677:.
3669:.
3661:.
3649:13
3647:.
3625:.
3617:.
3603:.
3599:.
3579:.
3571:.
3559:.
3535:.
3487:.
3426:.
3422:.
3396:.
3392:.
3366:.
3362:.
3337:.
3333:.
3308:.
3304:.
3209:.
3184:.
3180:.
3169:^
3128:.
3124:.
2987:^
2970:.
2966:.
2948:.
2933:.
2921:^
2895:,
2884:,
2847:.
2836:^
2821:^
2797:.
2787:.
2775:.
2745:^
2716:.
2706:.
2692:.
2669:.
2657:10
2655:.
2651:.
2624:^
2595:33
2593:.
2539:.
2513:.
2488:.
2480:.
2472:.
2460:63
2458:.
2454:.
2406:.
2396:.
2363:.
2349:^
2336:.
2321:^
2307:.
2295:14
2293:.
2289:.
2251:.
2230:^
2194:.
2160:^
2138:^
2126:^
2067:.
2056:^
1909:.
1906:VM
1857:,
1818:.
1758:.
1694:,
1690:,
1686:,
1674:,
1642:.
1627:.
1579:.
1367:UI
1220:.
1181:.
1162:.
1071:,
1067:,
1063:,
1001:,
928:.
795:.
740:.
720:.
686:.
676:JX
601:.
554:.
532:.
408:OS
295:.
186:.
163:.
133:,
110:.
4798:,
4708:)
4700:(
4468:e
4461:t
4454:v
4414:;
4412:)
4404:(
4385:;
4378:;
4371:;
4352:.
4324::
4303:.
4291::
4274:.
4246:.
4214:.
4180::
4153:.
4127:.
4102:.
4082::
4050:.
4021:.
4005:.
3983::
3975::
3969:8
3936:.
3904:.
3898::
3892:9
3839:.
3833::
3787::
3766:.
3746:.
3717:.
3685:.
3665::
3633:.
3611::
3605:8
3587:.
3567::
3561:8
3545:.
3520:.
3501:.
3473:.
3437:.
3408:.
3377:.
3348:.
3319:.
3240:.
3225:.
3195:.
3139:.
3092:.
3020:"
2981:.
2863:.
2783::
2730:.
2700::
2677:.
2663::
2605:.
2601::
2578:.
2553:.
2524:.
2499:.
2476::
2414:.
2390::
2315:.
2301::
2265:.
2108:.
2083:.
2029:.
659:.
374:)
344:)
34:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.