36:
200:
1061:
550:
The original language content in the response is replaced by the translated content as it passes back through the proxy. The translations used in a translation proxy can be either machine translation, human translation, or a combination of machine and human translation. Different translation proxy implementations have different capabilities. Some allow further customization of the source site for the local audiences such as excluding the source content or substituting the source content with the original local content.
140:
221:(SSL) encryption is often not done by the web server itself, but by a reverse proxy that is equipped with SSL acceleration hardware. Furthermore, a host can provide a single "SSL proxy" to provide SSL encryption for an arbitrary number of hosts, removing the need for a separate SSL server certificate for each host, with the downside that all hosts behind the SSL proxy have to share a common DNS name or IP address for SSL connections. This problem can partly be overcome by using the
1195:, residential proxy users connect to the target through residential IP addresses. The target then identifies them as organic internet users. It does not let any tracking tool identify the reallocation of the user. Any residential proxy can send any number of concurrent requests, and IP addresses are directly related to a specific region. Unlike regular residential proxies, which hide the user's real IP address behind another IP address, rotating residential proxies, also known as
286:
1114:, which is an enhancement of Tor's onion routing. I2P is fully distributed and works by encrypting all communications in various layers and relaying them through a network of routers run by volunteers in various locations. By keeping the source of the information hidden, I2P offers censorship resistance. The goals of I2P are to protect users' personal freedom, privacy, and ability to conduct confidential business.
466:
868:"A 'transparent proxy' is a proxy that does not modify the request or response beyond what is required for proxy authentication and identification". "A 'non-transparent proxy' is a proxy that modifies the request or response in order to provide some added service to the user agent, such as group annotation services, media type transformation, protocol reduction, or anonymity filtering".
1094:" refers to the layered nature of the encryption service: The original data are encrypted and re-encrypted multiple times, then sent through successive Tor relays, each one of which decrypts a "layer" of encryption before passing the data on to the next relay and ultimately the destination. This reduces the possibility of the original data being unscrambled or understood in transit.
492:
and administrators of these other proxies are unknown, the user may fall victim to a false sense of security just because those details are out of sight and mind. In what is more of an inconvenience than a risk, proxy users may find themselves being blocked from certain Web sites, as numerous forums and Web sites
982:
By attempting to make a connection to an IP address at which there is known to be no server. The proxy will accept the connection and then attempt to proxy it on. When the proxy finds no server to accept the connection, it may return an error message or simply close the connection to the client. This
549:
A translation proxy is a proxy server that is used to localize a website experience for different markets. Traffic from the global audience is routed through the translation proxy to the source website. As visitors browse the proxied site, requests go back to the source site where pages are rendered.
491:
By chaining the proxies which do not reveal data about the original requester, it is possible to obfuscate activities from the eyes of the user's destination. However, more traces will be left on the intermediate hops, which could be used or offered up to trace the user's activities. If the policies
379:
Many workplaces, schools, and colleges restrict web sites and online services that are accessible and available in their buildings. Governments also censor undesirable content. This is done either with a specialized proxy, called a content filter (both commercial and free products are available), or
1007:
in the user's browser window, processes the request, and returns the results to the user's browser. Consequently, it can be used on a device or network that does not allow "true" proxy settings to be changed. The first recorded CGI proxy, named "rover" at the time but renamed in 1998 to "CGIProxy",
568:
may be differentiated into several varieties. The destination server (the server that ultimately satisfies the web request) receives requests from the anonymizing proxy server and thus does not receive information about the end user's address. The requests are not anonymous to the anonymizing proxy
1141:
In the client configuration of layer-3 NAT, configuring the gateway is sufficient. However, for the client configuration of a layer 7 proxy, the destination of the packets that the client generates must always be the proxy server (layer 7), then the proxy server reads each packet and finds out the
971:
By comparing the results of online IP checkers when accessed using HTTPS vs. HTTP, as most intercepting proxies do not intercept SSL. If there is suspicion of SSL being intercepted, one can examine the certificate associated with any secure web site, the root certificate should indicate whether it
909:
that depend on certain behaviors of intercepting proxies that do not check or have access to information about the original (intercepted) destination. This problem may be resolved by using an integrated packet-level and application level appliance or software which is then able to communicate this
432:
In a workplace setting where the client is managed by the organization, devices may be configured to trust a root certificate whose private key is known to the proxy. In such situations, proxy analysis of the contents of an SSL/TLS transaction becomes possible. The proxy is effectively operating a
1039:
as a means to bypass local filtering. Since many of these users do not care about the collateral damage they are causing, it became necessary for organizations to hide their proxies, disclosing the URLs only to those who take the trouble to contact the organization and demonstrate a genuine need.
967:
By comparing the client's external IP address to the address seen by an external web server, or sometimes by examining the HTTP headers received by a server. A number of sites have been created to address this issue, by reporting the user's IP address as seen by the site back to the user on a web
635:
prohibit the web site from linking directly to the outside domains. Proxies also allow the browser to make web requests to externally hosted content on behalf of a website when cross-domain restrictions (in place to protect websites from the likes of data theft) prohibit the browser from directly
583:
with header lines such as HTTP_VIA, HTTP_X_FORWARDED_FOR, or HTTP_FORWARDED, which may reveal the IP address of the client. Other anonymizing proxy servers, known as elite or high-anonymity proxies, make it appear that the proxy server is the client. A website could still suspect a proxy is being
469:
Many organizations block access to popular websites such as
Facebook. Users can use proxy servers to circumvent this security. However, by connecting to proxy servers, they might be opening themselves up to danger by passing sensitive information such as personal photos and passwords through the
207:
A reverse proxy (or surrogate) is a proxy server that appears to clients to be an ordinary server. Reverse proxies forward requests to one or more ordinary servers that handle the request. The response from the original server is returned as if it came directly from the proxy server, leaving the
954:
Once traffic reaches the proxy machine itself, interception is commonly performed with NAT (Network
Address Translation). Such setups are invisible to the client browser, but leave the proxy visible to the web server and other devices on the internet side of the proxy. Recent Linux and some BSD
516:
server accelerates service requests by retrieving the content saved from a previous request made by the same client or even other clients. Caching proxies keep local copies of frequently requested resources, allowing large organizations to significantly reduce their upstream bandwidth usage and
212:
and with a destination of one of the neighborhood's web servers goes through the proxy server. The use of "reverse" originates in its counterpart "forward proxy" since the reverse proxy sits closer to the web server and serves only a restricted set of websites. There are several reasons for
1150:
means that the proxy uses the layer-7 proxy advantages without the knowledge of the client. The client presumes that the gateway is a NAT in layer 3, and it does not have any idea about the inside of the packet, but through this method, the layer-3 packets are sent to the layer-7 proxy for
532:
performance in the presence of high round-trip times or high packet loss (such as wireless or mobile phone networks); or highly asymmetric links featuring very different upload and download rates. PEPs can make more efficient use of the network, for example, by merging TCP
947:(Web Cache Control Protocol). This proprietary protocol resides on the router and is configured from the cache, allowing the cache to determine what ports and traffic is sent to it via transparent redirection from the router. This redirection can occur in one of two ways:
904:
The diversion or interception of a TCP connection creates several issues. First, the original destination IP and port must somehow be communicated to the proxy. This is not always possible (e.g., where the gateway and proxy reside on different hosts). There is a class of
887:
Intercepting proxies are commonly used in businesses to enforce acceptable use policies and to ease administrative overheads since no client browser configuration is required. This second reason, however is mitigated by features such as Active
Directory group policy, or
263:
Security: the proxy server is an additional layer of defense and can protect against some OS and web-server-specific attacks. However, it does not provide any protection from attacks against the web application or service itself, which is generally considered the larger
983:
difference in behavior is simple to detect. For example, most web browsers will generate a browser created error page in the case where they cannot connect to an HTTP server but will return a different error in the case where the connection is accepted and then closed.
1019:
language), or PHProxy (written in the PHP language). As of April 2016, CGIProxy has received about two million downloads, Glype has received almost a million downloads, whilst PHProxy still receives hundreds of downloads per week. Despite waning in popularity due to
344:
web proxy server provides administrative control over the content that may be relayed in one or both directions through the proxy. It is commonly used in both commercial and non-commercial organizations (especially schools) to ensure that
Internet usage conforms to
271:
access to some functions while keeping the servers behind the firewalls. If used in this way, security measures should be considered to protect the rest of your infrastructure in case this server is compromised, as its web application is exposed to attack from the
895:
Intercepting proxies are also commonly used by ISPs in some countries to save upstream bandwidth and improve customer response times by caching. This is more common in countries where bandwidth is more limited (e.g. island nations) or must be paid for.
846:
communication without requiring any special client configuration. Clients need not be aware of the existence of the proxy. A transparent proxy is normally located between the client and the
Internet, with the proxy performing some of the functions of a
409:
Most web filtering companies use an internet-wide crawling robot that assesses the likelihood that content is a certain type. Manual labor is used to correct the resultant database based on complaints or known flaws in the content-matching algorithms.
75:, the client directs the request to the proxy server, which evaluates the request and performs the required network transactions. This serves as a method to simplify or control the complexity of the request, or provide additional benefits such as
1052:"). Suffix proxy servers are easier to use than regular proxy servers, but they do not offer high levels of anonymity, and their primary use is for bypassing web filters. However, this is rarely used due to more advanced web filters.
878:
In 2009 a security flaw in the way that transparent proxies operate was published by Robert Auger, and the
Computer Emergency Response Team issued an advisory listing dozens of affected transparent and intercepting proxy servers.
921:, as the client browser believes it is talking to a server rather than a proxy. This can cause problems where an intercepting proxy requires authentication, and then the user connects to a site that also requires authentication.
487:
used – can be captured and analyzed by the proxy operator. For this reason, passwords to online services (such as webmail and banking) should always be exchanged over a cryptographically secured connection, such as SSL.
1145:
Because NAT operates at layer-3, it is less resource-intensive than the layer-7 proxy, but also less flexible. As we compare these two technologies, we might encounter a terminology known as 'transparent firewall'.
259:
Spoon feeding: reduces resource usage caused by slow clients on the web servers by caching the content the web server sent and slowly "spoon feeding" it to the client. This especially benefits dynamically generated
1906:
1117:
Each user of I2P runs an I2P router on their computer (node). The I2P router takes care of finding other peers and building anonymizing tunnels through them. I2P provides proxies for all protocols (HTTP,
398:
filtering, or content keyword filtering. Blacklists are often provided and maintained by web-filtering companies, often grouped into categories (pornography, gambling, shopping, social networks, etc..).
39:
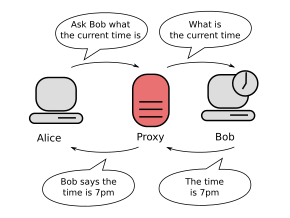
Communication between two computers connected through a third computer acting as a proxy server. This can protect Alice's privacy, as Bob only knows about the proxy and cannot identify or contact Alice
406:
files could be blocked based on fleshtone matches, or language filters could dynamically detect unwanted language. If the content is rejected then an HTTP fetch error may be returned to the requester.
955:
releases provide TPROXY (transparent proxy) which performs IP-level (OSI Layer 3) transparent interception and spoofing of outbound traffic, hiding the proxy IP address from other network devices.
584:
used if the client sends packets that include a cookie from a previous visit that did not use the high-anonymity proxy server. Clearing cookies, and possibly the cache, would solve this problem.
203:
A reverse proxy taking requests from the
Internet and forwarding them to servers in an internal network. Those making requests connect to the proxy and may not be aware of the internal network.
383:
Websites commonly used by students to circumvent filters and access blocked content often include a proxy, from which the user can then access the websites that the filter is trying to block.
517:
costs, while significantly increasing performance. Most ISPs and large businesses have a caching proxy. Caching proxies were the first kind of proxy server. Web proxies are commonly used to
600:
to determine the geographic source of requests. Using a proxy server that is physically located inside a specific country or a city gives advertisers the ability to test geotargeted ads.
932:
In integrated firewall/proxy servers where the router/firewall is on the same host as the proxy, communicating original destination information can be done by any method, for example
1509:
1171:
Some client programs "SOCKS-ify" requests, which allows adaptation of any networked software to connect to external networks via certain types of proxy servers (mostly SOCKS).
115:
is usually an internal-facing proxy used as a front-end to control and protect access to a server on a private network. A reverse proxy commonly also performs tasks such as
1210:
and exposed a range of unauthorized activities conducted by RESIP hosts. These activities encompassed illegal promotion, fast fluxing, phishing, hosting malware, and more.
569:
server, however, and so a degree of trust is present between the proxy server and the user. Many proxy servers are funded through a continued advertising link to the user.
1079:. Tor client software routes Internet traffic through a worldwide volunteer network of servers for concealing a user's computer location or usage from someone conducting
1902:
1748:
1542:
243:: the reverse proxy can distribute the load to several web servers, each serving its own application area. In such a case, the reverse proxy may need to rewrite the
2368:
1202:
Despite the providers assertion that the proxy hosts are voluntarily participating, numerous proxies are operated on potentially compromised hosts, including
402:
The proxy then fetches the content, assuming the requested URL is acceptable. At this point, a dynamic filter may be applied on the return path. For example,
667:
184:, the originating IP address can be retrieved as well. The main benefit of using this type of server is its ability to cache a website for faster retrieval.
87:. A proxy server thus functions on behalf of the client when requesting service, potentially masking the true origin of the request to the resource server.
2243:
1367:
462:
In some cases, users can circumvent proxies that filter using blacklists by using services designed to proxy information from a non-blacklisted location.
1048:
A suffix proxy allows a user to access web content by appending the name of the proxy server to the URL of the requested content (e.g. "en.wikipedia.org.
445:
If the destination server filters content based on the origin of the request, the use of a proxy can circumvent this filter. For example, a server using
649:
Secondary market brokers use web proxy servers to circumvent restrictions on online purchases of limited products such as limited sneakers or tickets.
267:
Extranet publishing: a reverse proxy server facing the
Internet can be used to communicate to a firewall server internal to an organization, providing
250:
Serve/cache static content: A reverse proxy can offload the web servers by caching static content like pictures and other static graphical content.
2421:
Mi, Xianghang; Feng, Xuan; Liao, Xiaojing; Liu, Baojun; Wang, XiaoFeng; Qian, Feng; Li, Zhou; Alrwais, Sumayah; Sun, Limin; Liu, Ying (May 2019).
1199:, conceal the user's real IP address behind a pool of proxies. These proxies switch between themselves at every session or at regular intervals.
1163:
proxy server takes DNS queries from a (usually local) network and forwards them to an
Internet Domain Name Server. It may also cache DNS records.
456:
Web proxies are the most common means of bypassing government censorship, although no more than 3% of
Internet users use any circumvention tools.
1932:
170:
of the client. Although this type of server can be discovered easily, it can be beneficial for some users as it hides the originating IP address.
1428:
2399:
1313:
111:. A forward proxy is an Internet-facing proxy used to retrieve data from a wide range of sources (in most cases, anywhere on the Internet). A
933:
924:
Finally, intercepting connections can cause problems for HTTP caches, as some requests and responses become uncacheable by a shared cache.
1502:
1087:. Using Tor makes tracing Internet activity more difficult, and is intended to protect users' personal freedom and their online privacy.
1206:
devices. Through the process of cross-referencing the hosts, researchers have identified and analyzed logs that have been classified as
616:
of the internal network. This makes requests from machines and users on the local network anonymous. Proxies can also be combined with
2487:
459:
Some proxy service providers allow businesses access to their proxy network for rerouting traffic for business intelligence purposes.
521:
web pages from a web server. Poorly implemented caching proxies can cause problems, such as an inability to use user authentication.
2478:
1799:
1962:
575:: Some proxy servers implement a logon requirement. In large organizations, authorized users must log on to gain access to the
208:
client with no knowledge of the original server. Reverse proxies are installed in the vicinity of one or more web servers. All
1744:
1534:
483:
upon the data-flow between client machines and the web. All content sent or accessed – including passwords submitted and
2442:
2362:
2309:
2044:
2001:
1876:
1632:
1404:
421:
Web filtering proxies are not able to peer inside secure sockets HTTP transactions, assuming the chain-of-trust of SSL/TLS (
2469:
745:
method to set up forwarding of arbitrary data through the connection; a common policy is to only forward port 443 to allow
369:
1774:
1337:
453:
to restrict its service to a certain country can be accessed using a proxy located in that country to access the service.
2526:
1008:
was developed by American computer scientist James Marshall in early 1996 for an article in "Unix Review" by Rich Morin.
889:
2022:
1336:. 6th International Conference on Distributed Computing Systems. Cambridge, MA, USA. pp. 198–204. inria-00444651.
1235:
2352:
2108:
1936:
944:
1080:
631:
Proxies allow web sites to make web requests to externally hosted resources (e.g. images, music files, etc.) when
380:
by using a cache-extension protocol such as ICAP, that allows plug-in extensions to an open caching architecture.
2235:
2178:
Estrada-Jiménez, José (March 2017). "Online advertising: Analysis of privacy threats and protection approaches".
1835:
1706:
1658:
534:
68:
and the server providing that resource. It improves privacy, security, and possibly performance in the process.
1452:"Identifying legitimate Web users and bots with different traffic profiles — an Information Bottleneck approach"
1359:
990:
specially programmed Adobe Flash SWF applications or Sun Java applets that send HTTP calls back to their server.
2516:
2156:
848:
769:
529:
104:
2270:
413:
Some proxies scan outbound content, e.g., for data loss prevention; or scan content for malicious software.
2511:
2506:
1207:
1028:
979:
for a proxied protocol such as HTTP (port 80) with that for a non-proxied protocol such as SMTP (port 25).
710:
This request is sent to the proxy server, the proxy makes the request specified and returns the response.
1564:
1135:
663:
609:
525:
2325:
1594:
1084:
71:
Instead of connecting directly to a server that can fulfill a request for a resource, such as a file or
1250:
875:
attacks, which are a type of denial-of-service attack. TCP Intercept is available for IP traffic only.
365:
240:
177:
116:
80:
76:
1420:
822:
also forwards arbitrary data after a connection phase, and is similar to HTTP CONNECT in web proxies.
623:
An incorrectly configured proxy can provide access to a network otherwise isolated from the Internet.
579:. The organization can thereby track usage to individuals. Some anonymizing proxy servers may forward
564:
An anonymous proxy server (sometimes called a web proxy) generally attempts to anonymize web surfing.
2521:
1180:
2391:
2130:
1993:
1306:
1000:
434:
422:
335:
297:
234:
2354:
Go Web Scraping Quick Start Guide: Implement the power of Go to scrape and crawl data from the web
1024:
and other privacy methods, as of September 2021 there are still a few hundred CGI proxies online.
1270:
120:
843:
2531:
230:
27:
20:
2301:
2294:
1825:
360:, either to give detailed information about the URLs accessed by specific users or to monitor
2070:
742:
470:
proxy server. This image illustrates a common example: schools blocking websites to students.
426:
387:
361:
346:
84:
1985:
1696:
1849:
1720:
1672:
1220:
968:
page. Google also returns the IP address as seen by the page if the user searches for "IP".
906:
803:
For clients, the problem of complex or multiple proxy-servers is solved by a client-server
617:
597:
218:
166:: This server reveals its identity as a proxy server but does not disclose the originating
1032:
8:
1986:
1803:
871:
TCP Intercept is a traffic filtering security feature that protects TCP servers from TCP
493:
45:
2448:
2213:
1481:
1203:
1192:
1160:
1107:
1076:
852:
785:
753:
632:
316:
A reverse proxy mainly protects the server, while a forward proxy protects the client.
155:
proxy server that is accessible by any Internet user. In 2008, network security expert
61:
53:
524:
A proxy that is designed to mitigate specific link related issues or degradation is a
2452:
2438:
2358:
2305:
2205:
1997:
1628:
1621:
1508:. The Berkman Center for Internet & Society at Harvard University. October 2010.
1485:
1473:
1400:
1188:
804:
613:
538:
497:
446:
341:
159:
estimated that "hundreds of thousands" of open proxies are operated on the Internet.
152:
128:
2217:
1958:
963:
Several methods may be used to detect the presence of an intercepting proxy server:
247:
in each web page (translation from externally known URLs to the internal locations).
2428:
2195:
2187:
1839:
1710:
1662:
1463:
1245:
858:
781:
501:
256:: the proxy server can optimize and compress the content to speed up the load time.
253:
209:
103:. A proxy server that passes unmodified requests and responses is usually called a
2048:
1880:
1639:
A proxy server helps speed up Internet access by storing frequently accessed pages
1179:
A residential proxy is an intermediary that uses a real IP address provided by an
176:
This server not only identifies itself as a proxy server, but with the support of
2191:
1468:
1451:
1275:
1065:
1036:
163:
1852:
1829:
1723:
1700:
1675:
1652:
862:
592:
Advertisers use proxy servers for validating, checking and quality assurance of
425:) has not been tampered with. The SSL/TLS chain-of-trust relies on trusted root
2422:
1770:
1331:
1225:
1111:
761:
580:
576:
353:
2500:
2209:
1477:
1260:
1091:
1072:
948:
608:
A proxy can keep the internal network structure of a company secret by using
480:
194:
112:
99:, or at any point between the user's computer and destination servers on the
2018:
1702:
Performance Enhancing Proxies Intended to Mitigate Link-Related Degradations
1302:
1184:
1011:
The majority of CGI proxies are powered by one of CGIProxy (written in the
596:. A geotargeting ad server checks the request source IP address and uses a
593:
65:
57:
2433:
2100:
1392:
484:
450:
156:
2427:. 2019 IEEE Symposium on Security and Privacy (SP). pp. 1185–1201.
1928:
1864:
a client MUST send the target URI in absolute-form as the request-target
376:
by scanning incoming content in real-time before it enters the network.
372:-based antivirus software to provide security against viruses and other
285:
199:
1333:
Structure and Encapsulation in Distributed Systems: the Proxy Principle
1265:
1255:
976:
565:
559:
357:
167:
148:
124:
2200:
917:
authentication, especially connection-oriented authentication such as
437:, allowed by the client's trust of a root certificate the proxy owns.
143:
An open proxy forwarding requests from and to anywhere on the Internet
1844:
1715:
1667:
1281:
1240:
1131:
1060:
975:
By comparing the sequence of network hops reported by a tool such as
872:
757:
518:
139:
1959:"Subversion Dev: Transparent Proxy detection (was Re: Introduction_"
865:(Hypertext Transfer Protocol—HTTP/1.1) offers standard definitions:
16:
Computer server that makes and receives requests on behalf of a user
2424:
Resident Evil: Understanding Residential IP Proxy as a Dark Service
2148:
1004:
987:
268:
217:
Encryption/SSL acceleration: when secure websites are created, the
100:
72:
35:
1903:"Socket Capable Browser Plugins Result in Transparent Proxy Abuse"
79:, privacy, or security. Proxies were devised to add structure and
1230:
937:
793:
789:
777:
765:
373:
2491:
2482:
2473:
2292:
Zwicky, Elizabeth D.; Cooper, Simon; Chapman, D. Brent (2000).
1572:
797:
2266:
772:
configured as proxy (e.g., with Application Request Routing),
819:
773:
746:
391:
226:
1125:
465:
1012:
918:
914:
403:
395:
1557:
504:
the site. Proxy bouncing can be used to maintain privacy.
2078:
1130:
The proxy concept refers to a layer 7 application in the
1119:
1103:
1031:
to disabled people, but have since been shut down due to
1021:
1016:
670:
except the full URL is passed, instead of just the path.
244:
19:
For Knowledge's policy on editing from open proxies, see
1745:"Hot Tactics For Geo-Targeted Ads on Google & Bing"
666:
requests. The request from the client is the same as a
386:
Requests may be filtered by several methods, such as a
1535:"How to Check if Website is Down or Working Worldwide"
910:
information between the packet handler and the proxy.
1413:
1138:(NAT) is similar to a proxy but operates in layer 3.
1879:. ukproxyserver.org. 1 February 2011. Archived from
1565:"Using a Ninjaproxy to get through a filtered proxy"
2291:
1623:
Beginning Ubuntu Linux: From Novice to Professional
537:(acknowledgements) or compressing data sent at the
440:
352:Content filtering proxy servers will often support
2293:
1787:The proxy server is, above all, a security device.
1650:
1620:
1027:Some CGI proxies were set up for purposes such as
276:
1450:Suchacka, Grażyna; Iwański, Jacek (7 June 2020).
943:Interception can also be performed using Cisco's
553:
2498:
2236:"Privacy for People Who Don't Show Their Navels"
356:to control web access. It also usually produces
2177:
2063:
1838:. June 2014. p. 41. sec. 5.3.2.
1449:
2326:"What Is a Proxy Server and How Does It Work?"
416:
2420:
1818:
1301:
951:(OSI Layer 3) or MAC rewrites (OSI Layer 2).
652:
587:
364:usage statistics. It may also communicate to
1709:. June 2001. p. 4. sec. 2.1.
1278:which discusses host-based HTTP acceleration
1174:
528:(PEPs). These are typically used to improve
474:
2264:
1689:
1055:
972:was issued for the purpose of intercepting.
644:
329:
324:
2258:
2432:
2229:
2227:
2199:
1843:
1714:
1666:
1497:
1495:
1467:
1126:Comparison to network address translators
927:
626:
1059:
842:, a transparent proxy intercepts normal
507:
464:
198:
138:
95:A proxy server may reside on the user's
34:
1983:
1905:. The Security Practice. 9 March 2009.
1644:
1329:
913:Intercepting also creates problems for
2499:
2233:
2224:
1618:
1503:"2010 Circumvention Tool Usage Report"
1492:
1387:
1385:
1191:. Instead of connecting directly to a
1097:
1003:web proxy accepts target URLs using a
752:Examples of web proxy servers include
2402:from the original on 26 December 2021
2350:
2159:from the original on 1 September 2021
2025:from the original on 16 November 2018
1751:from the original on 14 February 2014
1545:from the original on 14 December 2019
1431:from the original on 10 February 2011
1370:from the original on 26 November 2020
1340:from the original on 26 December 2018
1106:('I2P') is a proxy network aiming at
678:https://en.wikipedia.org/Proxy_server
479:Proxies can be installed in order to
2371:from the original on 17 January 2023
2234:Glater, Jonathan (25 January 2006).
2016:
1965:from the original on 16 October 2015
1909:from the original on 2 February 2010
1515:from the original on 18 January 2012
1391:
1319:from the original on 9 October 2016.
825:
657:
280:
1831:HTTP/1.1 Message Syntax and Routing
1777:from the original on 23 August 2011
1382:
1037:third party advertising the service
639:
13:
2389:
2300:(2nd ed.). O'Reilly. p.
2246:from the original on 29 April 2011
2149:"Proxy Stats :: Get Proxi.es"
2111:from the original on 14 March 2016
1651:I. Cooper; J. Dilley (June 2001).
1236:Distributed Checksum Clearinghouse
213:installing reverse proxy servers:
188:
14:
2543:
2463:
2273:from the original on 9 April 2010
1939:from the original on 10 July 2010
1771:"Firewall and Proxy Server HOWTO"
1654:Known HTTP Proxy/Caching Problems
1015:language), Glype (written in the
1075:is a system intended to provide
441:Bypassing filters and censorship
284:
210:traffic coming from the Internet
2414:
2392:"What are Residential Proxies?"
2383:
2344:
2318:
2285:
2171:
2141:
2123:
2093:
2037:
2010:
1977:
1951:
1921:
1895:
1869:
1792:
1763:
1737:
1612:
1587:
1181:Internet Service Provider (ISP)
1043:
1029:making websites more accessible
892:and automatic proxy detection.
636:accessing the outside domains.
277:Forward proxy vs. reverse proxy
134:
1929:"Vulnerability Note VU#435052"
1877:"Transparent Proxy Definition"
1527:
1443:
1352:
1323:
1295:
1183:with physical devices such as
814:
554:Accessing services anonymously
544:
1:
2479:Free web-based proxy services
1421:"Forward and Reverse Proxies"
1399:. US: Insecure. p. 270.
1360:"Proxy servers and tunneling"
1305:; Altis, Kevin (April 1994).
1288:
1166:
2192:10.1016/j.comcom.2016.12.016
1961:. Tracetop.sourceforge.net.
1569:advanced filtering mechanics
1469:10.1016/j.knosys.2020.105875
1208:potentially unwanted program
1154:
994:
958:
7:
2296:Building Internet Firewalls
2047:. June 1996. Archived from
1800:"Sneaker Bot Supreme Proxy"
1213:
1136:Network address translation
741:Some web proxies allow the
610:network address translation
603:
526:Performance Enhancing Proxy
496:from proxies known to have
417:Filtering of encrypted data
10:
2548:
2527:Computer security software
2470:Proxy software and scripts
1988:Squid The Definitive Guide
1330:Shapiro, Marc (May 1986).
1251:InterPlanetary File System
882:
653:Implementations of proxies
588:QA geotargeted advertising
557:
333:
192:
25:
18:
1802:. GeoSurf. Archived from
1175:Residential proxy (RESIP)
899:
696:Basic encoded-credentials
633:cross-domain restrictions
475:Logging and eavesdropping
2357:. Packt Publishing Ltd.
1307:"World-Wide Web Proxies"
1056:Tor onion proxy software
796:, Tinyproxy, RabbIT and
736:text/html; charset UTF-8
712:
672:
645:Secondary market brokers
435:man-in-the-middle attack
423:Transport Layer Security
336:Content-control software
330:Content-control software
325:Monitoring and filtering
90:
2488:Free http proxy servers
2351:Smith, Vincent (2019).
2267:"Tor: anonymity online"
2180:Computer Communications
2045:"The Limits of Control"
1984:Wessels, Duane (2004).
1456:Knowledge-Based Systems
1271:Virtual private network
427:certificate authorities
394:, URL regex filtering,
319:
1571:. TSNP. Archived from
1189:computers of end-users
1069:
1035:, usually caused by a
928:Implementation methods
788:(reverse proxy only),
627:Cross-domain resources
471:
204:
144:
41:
28:Proxy (disambiguation)
21:Knowledge:Open proxies
2517:Internet architecture
2434:10.1109/SP.2019.00011
2071:"Glype® Proxy Script"
1992:. O'Reilly. pp.
1619:Thomas, Keir (2006).
1397:Nmap network scanning
1104:I2P anonymous network
1063:
612:, which can help the
508:Improving performance
468:
347:acceptable use policy
334:Further information:
202:
142:
38:
1935:. 23 February 2009.
1806:on 24 September 2017
1541:. 19 November 2019.
1221:Application firewall
1148:Transparent firewall
1081:network surveillance
668:regular HTTP request
662:Web proxies forward
229:certificates or the
219:Secure Sockets Layer
26:For other uses, see
2512:Network performance
2507:Computer networking
1197:backconnect proxies
1132:OSI reference model
1098:I2P anonymous proxy
690:Proxy-Authorization
354:user authentication
85:distributed systems
46:computer networking
2240:The New York Times
1204:Internet of things
1142:true destination.
1070:
907:cross-site attacks
832:intercepting proxy
494:block IP addresses
472:
296:. You can help by
205:
178:HTTP header fields
174:Transparent proxy:
145:
54:server application
42:
2444:978-1-5386-6660-9
2364:978-1-78961-294-3
2311:978-1-56592-871-8
2265:The Tor Project.
2081:on 3 January 2013
2017:Marshall, James.
2003:978-0-596-00162-9
1634:978-1-59059-627-2
1406:978-0-9799587-1-7
1033:excessive traffic
844:application layer
830:Also known as an
826:Transparent proxy
805:Proxy auto-config
658:Web proxy servers
539:application layer
342:content-filtering
314:
313:
2539:
2522:Internet privacy
2457:
2456:
2436:
2418:
2412:
2411:
2409:
2407:
2387:
2381:
2380:
2378:
2376:
2348:
2342:
2341:
2339:
2337:
2322:
2316:
2315:
2299:
2289:
2283:
2282:
2280:
2278:
2262:
2256:
2255:
2253:
2251:
2231:
2222:
2221:
2203:
2175:
2169:
2168:
2166:
2164:
2145:
2139:
2138:
2127:
2121:
2120:
2118:
2116:
2097:
2091:
2090:
2088:
2086:
2077:. Archived from
2067:
2061:
2060:
2058:
2056:
2051:on 6 August 2020
2041:
2035:
2034:
2032:
2030:
2014:
2008:
2007:
1991:
1981:
1975:
1974:
1972:
1970:
1955:
1949:
1948:
1946:
1944:
1925:
1919:
1918:
1916:
1914:
1899:
1893:
1892:
1890:
1888:
1873:
1867:
1866:
1861:
1859:
1847:
1845:10.17487/RFC7230
1822:
1816:
1815:
1813:
1811:
1796:
1790:
1789:
1784:
1782:
1767:
1761:
1760:
1758:
1756:
1747:. October 2013.
1741:
1735:
1734:
1732:
1730:
1718:
1716:10.17487/RFC3135
1693:
1687:
1686:
1684:
1682:
1670:
1668:10.17487/RFC3143
1648:
1642:
1641:
1626:
1616:
1610:
1609:
1607:
1605:
1591:
1585:
1584:
1582:
1580:
1561:
1555:
1554:
1552:
1550:
1531:
1525:
1524:
1522:
1520:
1514:
1507:
1499:
1490:
1489:
1471:
1447:
1441:
1440:
1438:
1436:
1417:
1411:
1410:
1389:
1380:
1379:
1377:
1375:
1356:
1350:
1349:
1347:
1345:
1327:
1321:
1320:
1318:
1311:
1299:
1246:Internet privacy
1110:. It implements
1108:online anonymity
1085:traffic analysis
1077:online anonymity
737:
734:
731:
728:
725:
722:
719:
716:
706:
703:
700:
697:
694:
691:
688:
685:
682:
679:
676:
640:Malicious usages
309:
306:
288:
281:
183:
56:that acts as an
2547:
2546:
2542:
2541:
2540:
2538:
2537:
2536:
2497:
2496:
2466:
2461:
2460:
2445:
2419:
2415:
2405:
2403:
2390:Keenan, James.
2388:
2384:
2374:
2372:
2365:
2349:
2345:
2335:
2333:
2332:. 17 April 2023
2324:
2323:
2319:
2312:
2290:
2286:
2276:
2274:
2263:
2259:
2249:
2247:
2232:
2225:
2176:
2172:
2162:
2160:
2147:
2146:
2142:
2131:"Google Trends"
2129:
2128:
2124:
2114:
2112:
2099:
2098:
2094:
2084:
2082:
2069:
2068:
2064:
2054:
2052:
2043:
2042:
2038:
2028:
2026:
2015:
2011:
2004:
1982:
1978:
1968:
1966:
1957:
1956:
1952:
1942:
1940:
1927:
1926:
1922:
1912:
1910:
1901:
1900:
1896:
1886:
1884:
1883:on 1 March 2013
1875:
1874:
1870:
1857:
1855:
1826:"absolute-form"
1824:
1823:
1819:
1809:
1807:
1798:
1797:
1793:
1780:
1778:
1769:
1768:
1764:
1754:
1752:
1743:
1742:
1738:
1728:
1726:
1695:
1694:
1690:
1680:
1678:
1649:
1645:
1635:
1617:
1613:
1603:
1601:
1595:"Caching Proxy"
1593:
1592:
1588:
1578:
1576:
1575:on 9 March 2016
1563:
1562:
1558:
1548:
1546:
1533:
1532:
1528:
1518:
1516:
1512:
1505:
1501:
1500:
1493:
1448:
1444:
1434:
1432:
1425:httpd mod_proxy
1419:
1418:
1414:
1407:
1390:
1383:
1373:
1371:
1358:
1357:
1353:
1343:
1341:
1328:
1324:
1316:
1309:
1300:
1296:
1291:
1286:
1276:Web accelerator
1216:
1177:
1169:
1157:
1151:investigation.
1128:
1122:, SOCKS, ...).
1100:
1068:Tor-network map
1058:
1050:SuffixProxy.com
1046:
997:
986:By serving the
961:
930:
902:
885:
828:
817:
739:
738:
735:
732:
729:
726:
723:
720:
717:
714:
708:
707:
704:
701:
698:
695:
692:
689:
686:
683:
680:
677:
674:
660:
655:
647:
642:
629:
606:
598:geo-IP database
594:geotargeted ads
590:
562:
556:
547:
510:
477:
443:
419:
338:
332:
327:
322:
310:
304:
301:
294:needs expansion
279:
197:
191:
189:Reverse proxies
182:X-Forwarded-For
181:
164:Anonymous proxy
137:
109:tunneling proxy
107:or sometimes a
93:
31:
24:
17:
12:
11:
5:
2545:
2535:
2534:
2529:
2524:
2519:
2514:
2509:
2495:
2494:
2485:
2476:
2465:
2464:External links
2462:
2459:
2458:
2443:
2413:
2396:Smartproxy.com
2382:
2363:
2343:
2317:
2310:
2284:
2257:
2223:
2170:
2140:
2122:
2092:
2062:
2036:
2009:
2002:
1976:
1950:
1920:
1894:
1868:
1817:
1791:
1762:
1736:
1688:
1643:
1633:
1611:
1586:
1556:
1526:
1491:
1442:
1412:
1405:
1381:
1351:
1322:
1293:
1292:
1290:
1287:
1285:
1284:
1279:
1273:
1268:
1263:
1258:
1253:
1248:
1243:
1238:
1233:
1228:
1226:Captive portal
1223:
1217:
1215:
1212:
1176:
1173:
1168:
1165:
1156:
1153:
1127:
1124:
1112:garlic routing
1099:
1096:
1057:
1054:
1045:
1042:
996:
993:
992:
991:
984:
980:
973:
969:
960:
957:
929:
926:
901:
898:
884:
881:
827:
824:
816:
813:
762:Traffic Server
713:
673:
659:
656:
654:
651:
646:
643:
641:
638:
628:
625:
605:
602:
589:
586:
573:Access control
558:Main article:
555:
552:
546:
543:
509:
506:
476:
473:
442:
439:
418:
415:
392:DNS blacklists
368:-based and/or
331:
328:
326:
323:
321:
318:
312:
311:
305:September 2024
291:
289:
278:
275:
274:
273:
265:
261:
257:
251:
248:
241:Load balancing
238:
223:SubjectAltName
193:Main article:
190:
187:
186:
185:
171:
136:
133:
121:authentication
117:load-balancing
97:local computer
92:
89:
77:load balancing
15:
9:
6:
4:
3:
2:
2544:
2533:
2532:Proxy servers
2530:
2528:
2525:
2523:
2520:
2518:
2515:
2513:
2510:
2508:
2505:
2504:
2502:
2493:
2489:
2486:
2484:
2480:
2477:
2475:
2471:
2468:
2467:
2454:
2450:
2446:
2440:
2435:
2430:
2426:
2425:
2417:
2401:
2397:
2393:
2386:
2370:
2366:
2360:
2356:
2355:
2347:
2331:
2327:
2321:
2313:
2307:
2303:
2298:
2297:
2288:
2272:
2268:
2261:
2245:
2241:
2237:
2230:
2228:
2219:
2215:
2211:
2207:
2202:
2197:
2193:
2189:
2185:
2181:
2174:
2158:
2154:
2150:
2144:
2136:
2135:Google Trends
2132:
2126:
2110:
2106:
2102:
2096:
2080:
2076:
2072:
2066:
2050:
2046:
2040:
2024:
2020:
2013:
2005:
1999:
1995:
1990:
1989:
1980:
1964:
1960:
1954:
1938:
1934:
1930:
1924:
1908:
1904:
1898:
1882:
1878:
1872:
1865:
1854:
1851:
1846:
1841:
1837:
1833:
1832:
1827:
1821:
1805:
1801:
1795:
1788:
1776:
1772:
1766:
1750:
1746:
1740:
1725:
1722:
1717:
1712:
1708:
1704:
1703:
1698:
1692:
1677:
1674:
1669:
1664:
1660:
1656:
1655:
1647:
1640:
1636:
1630:
1625:
1624:
1615:
1600:
1596:
1590:
1574:
1570:
1566:
1560:
1544:
1540:
1536:
1530:
1511:
1504:
1498:
1496:
1487:
1483:
1479:
1475:
1470:
1465:
1461:
1457:
1453:
1446:
1430:
1426:
1422:
1416:
1408:
1402:
1398:
1394:
1388:
1386:
1369:
1365:
1361:
1355:
1339:
1335:
1334:
1326:
1315:
1308:
1304:
1303:Luotonen, Ari
1298:
1294:
1283:
1280:
1277:
1274:
1272:
1269:
1267:
1264:
1262:
1261:Proxy pattern
1259:
1257:
1254:
1252:
1249:
1247:
1244:
1242:
1239:
1237:
1234:
1232:
1229:
1227:
1224:
1222:
1219:
1218:
1211:
1209:
1205:
1200:
1198:
1194:
1190:
1186:
1182:
1172:
1164:
1162:
1152:
1149:
1143:
1139:
1137:
1133:
1123:
1121:
1115:
1113:
1109:
1105:
1095:
1093:
1092:Onion routing
1088:
1086:
1082:
1078:
1074:
1067:
1062:
1053:
1051:
1041:
1038:
1034:
1030:
1025:
1023:
1018:
1014:
1009:
1006:
1002:
989:
985:
981:
978:
974:
970:
966:
965:
964:
956:
952:
950:
949:GRE tunneling
946:
941:
939:
935:
934:Microsoft TMG
925:
922:
920:
916:
911:
908:
897:
893:
891:
880:
876:
874:
869:
866:
864:
860:
856:
854:
850:
845:
841:
837:
833:
823:
821:
812:
810:
806:
801:
799:
795:
791:
787:
783:
779:
775:
771:
767:
763:
759:
755:
750:
748:
744:
711:
671:
669:
665:
650:
637:
634:
624:
621:
619:
615:
611:
601:
599:
595:
585:
582:
578:
574:
570:
567:
561:
551:
542:
540:
536:
531:
527:
522:
520:
515:
514:caching proxy
505:
503:
499:
495:
489:
486:
482:
467:
463:
460:
457:
454:
452:
448:
438:
436:
430:
428:
424:
414:
411:
407:
405:
400:
397:
393:
389:
384:
381:
377:
375:
371:
367:
363:
359:
355:
350:
348:
343:
337:
317:
308:
299:
295:
292:This section
290:
287:
283:
282:
270:
266:
262:
258:
255:
252:
249:
246:
242:
239:
236:
232:
231:SNI extension
228:
224:
220:
216:
215:
214:
211:
201:
196:
195:Reverse proxy
179:
175:
172:
169:
165:
162:
161:
160:
158:
154:
150:
141:
132:
130:
126:
122:
118:
114:
113:reverse proxy
110:
106:
102:
98:
88:
86:
82:
81:encapsulation
78:
74:
69:
67:
64:requesting a
63:
59:
55:
51:
47:
37:
33:
29:
22:
2423:
2416:
2404:. Retrieved
2395:
2385:
2373:. Retrieved
2353:
2346:
2334:. Retrieved
2329:
2320:
2295:
2287:
2275:. Retrieved
2260:
2248:. Retrieved
2239:
2183:
2179:
2173:
2161:. Retrieved
2152:
2143:
2134:
2125:
2113:. Retrieved
2104:
2095:
2083:. Retrieved
2079:the original
2074:
2065:
2053:. Retrieved
2049:the original
2039:
2027:. Retrieved
2012:
1987:
1979:
1967:. Retrieved
1953:
1941:. Retrieved
1923:
1911:. Retrieved
1897:
1885:. Retrieved
1881:the original
1871:
1863:
1856:. Retrieved
1830:
1820:
1810:24 September
1808:. Retrieved
1804:the original
1794:
1786:
1779:. Retrieved
1773:. tldp.org.
1765:
1753:. Retrieved
1739:
1727:. Retrieved
1701:
1691:
1679:. Retrieved
1653:
1646:
1638:
1622:
1614:
1602:. Retrieved
1598:
1589:
1579:17 September
1577:. Retrieved
1573:the original
1568:
1559:
1547:. Retrieved
1538:
1529:
1519:15 September
1517:. Retrieved
1459:
1455:
1445:
1433:. Retrieved
1424:
1415:
1396:
1393:Lyon, Gordon
1372:. Retrieved
1364:MDN Web Docs
1363:
1354:
1342:. Retrieved
1332:
1325:
1297:
1201:
1196:
1178:
1170:
1158:
1147:
1144:
1140:
1129:
1116:
1101:
1089:
1071:
1049:
1047:
1044:Suffix proxy
1026:
1010:
998:
962:
953:
942:
931:
923:
912:
903:
894:
886:
877:
870:
867:
857:
840:forced proxy
839:
836:inline proxy
835:
831:
829:
818:
808:
802:
751:
743:HTTP CONNECT
740:
730:Content-Type
709:
661:
648:
630:
622:
607:
591:
581:data packets
572:
571:
563:
548:
523:
513:
511:
490:
478:
461:
458:
455:
444:
431:
420:
412:
408:
401:
385:
382:
378:
351:
339:
315:
302:
298:adding to it
293:
222:
206:
173:
146:
135:Open proxies
108:
96:
94:
70:
58:intermediary
50:proxy server
49:
43:
32:
2406:26 December
2375:19 November
2330:IPRoyal.com
2163:5 September
2153:getproxi.es
2105:SourceForge
2055:12 November
2029:12 November
1969:16 November
1887:14 February
1781:4 September
1729:21 February
1599:www.ibm.com
1549:14 December
1435:20 December
1344:26 December
815:SOCKS proxy
566:Anonymizers
545:Translation
451:geolocation
254:Compression
225:feature of
157:Gordon Lyon
2501:Categories
2201:2117/99742
2019:"CGIProxy"
1858:4 November
1755:7 February
1697:"Layering"
1627:. Apress.
1462:: 105875.
1427:. Apache.
1374:6 December
1289:References
1266:SMTP proxy
1256:Proxy list
1167:Proxifiers
977:traceroute
807:protocol (
560:Anonymizer
168:IP address
153:forwarding
149:open proxy
125:decryption
60:between a
2453:132479013
2277:9 January
2210:0140-3664
2186:: 32–51.
2101:"PHProxy"
2075:glype.com
1943:14 August
1913:14 August
1539:Hostinger
1486:216514793
1478:0950-7051
1282:Web cache
1241:FreeProxy
1155:DNS proxy
995:CGI proxy
959:Detection
873:SYN flood
758:mod_proxy
749:traffic.
705:text/html
618:firewalls
481:eavesdrop
362:bandwidth
272:Internet.
40:directly.
2400:Archived
2369:Archived
2271:Archived
2250:4 August
2244:Archived
2218:34656772
2157:Archived
2109:Archived
2023:Archived
1963:Archived
1937:Archived
1907:Archived
1775:Archived
1749:Archived
1543:Archived
1510:Archived
1429:Archived
1395:(2008).
1368:Archived
1338:Archived
1314:Archived
1214:See also
1005:Web form
988:end-user
809:PAC file
614:security
604:Security
269:extranet
180:such as
101:Internet
73:web page
66:resource
2115:7 April
1933:US CERT
1231:Darknet
1185:mobiles
1066:Vidalia
938:WinGate
883:Purpose
849:gateway
794:Ziproxy
790:WinGate
786:Varnish
778:Privoxy
766:HAProxy
502:trolled
498:spammed
485:cookies
449:-based
374:malware
264:threat.
129:caching
105:gateway
2492:Curlie
2483:Curlie
2474:Curlie
2451:
2441:
2361:
2336:2 July
2308:
2216:
2208:
2085:17 May
2000:
1681:17 May
1631:
1604:2 July
1484:
1476:
1403:
1193:server
900:Issues
861:
853:router
798:Polipo
756:(with
754:Apache
699:Accept
366:daemon
260:pages.
62:client
2449:S2CID
2214:S2CID
1513:(PDF)
1506:(PDF)
1482:S2CID
1317:(PDF)
1310:(PDF)
838:, or
820:SOCKS
782:Squid
774:Nginx
747:HTTPS
519:cache
227:X.509
151:is a
91:Types
52:is a
2439:ISBN
2408:2021
2377:2020
2359:ISBN
2338:2023
2306:ISBN
2279:2011
2252:2011
2206:ISSN
2165:2021
2117:2016
2087:2019
2057:2018
2031:2018
1998:ISBN
1971:2014
1945:2010
1915:2010
1889:2013
1860:2017
1853:7230
1836:IETF
1812:2017
1783:2011
1757:2014
1731:2014
1724:3135
1707:IETF
1683:2019
1676:3143
1659:IETF
1629:ISBN
1606:2023
1581:2011
1551:2019
1521:2011
1474:ISSN
1437:2010
1401:ISBN
1376:2020
1346:2018
1187:and
1102:The
1064:The
1022:VPNs
1013:Perl
945:WCCP
919:NTLM
915:HTTP
890:DHCP
863:2616
715:HTTP
681:HTTP
664:HTTP
535:ACKs
404:JPEG
396:MIME
370:ICAP
358:logs
320:Uses
245:URLs
127:and
48:, a
2490:at
2481:at
2472:at
2429:doi
2302:235
2196:hdl
2188:doi
2184:100
1994:130
1850:RFC
1840:doi
1721:RFC
1711:doi
1673:RFC
1663:doi
1464:doi
1460:197
1161:DNS
1120:IRC
1083:or
1073:Tor
1017:PHP
1001:CGI
936:or
859:RFC
851:or
811:).
770:IIS
764:),
760:or
724:200
721:1.1
687:1.1
675:GET
577:web
530:TCP
500:or
390:or
388:URL
300:.
235:TLS
233:of
147:An
83:to
44:In
2503::
2447:.
2437:.
2398:.
2394:.
2367:.
2328:.
2304:.
2269:.
2242:.
2238:.
2226:^
2212:.
2204:.
2194:.
2182:.
2155:.
2151:.
2133:.
2107:.
2103:.
2073:.
2021:.
1996:.
1931:.
1862:.
1848:.
1834:.
1828:.
1785:.
1719:.
1705:.
1699:.
1671:.
1661:.
1657:.
1637:.
1597:.
1567:.
1537:.
1494:^
1480:.
1472:.
1458:.
1454:.
1423:.
1384:^
1366:.
1362:.
1312:.
1159:A
1134:.
999:A
940:.
855:.
834:,
800:.
792:,
784:,
780:,
776:,
768:,
727:OK
620:.
541:.
512:A
447:IP
429:.
349:.
340:A
131:.
123:,
119:,
2455:.
2431::
2410:.
2379:.
2340:.
2314:.
2281:.
2254:.
2220:.
2198::
2190::
2167:.
2137:.
2119:.
2089:.
2059:.
2033:.
2006:.
1973:.
1947:.
1917:.
1891:.
1842::
1814:.
1759:.
1733:.
1713::
1685:.
1665::
1608:.
1583:.
1553:.
1523:.
1488:.
1466::
1439:.
1409:.
1378:.
1348:.
1090:"
733::
718:/
702::
693::
684:/
307:)
303:(
237:.
30:.
23:.
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.