20:
177:. This can make it more difficult to determine the actual location of the origin server / website and, for instance, more challenging to initiate legal action such as takedowns or block access to the website, as the IP address of the website may not be immediately apparent. Additionally, the reverse proxy may be located in a different jurisdiction with different legal requirements, further complicating the takedown process.
260:
Reverse proxies can operate wherever multiple web-servers must be accessible via a single public IP address. The web servers listen on different ports in the same machine, with the same local IP address or, possibly, on different machines with different local IP addresses. The reverse proxy analyzes
256:
In a technique named "spoon-feeding", a dynamically generated page can be produced all at once and served to the reverse proxy, which can then return it to the client a little bit at a time. The program that generates the page need not remain open, thus releasing server resources during the possibly
314:
Applications that were developed for the internal use of a company are not typically hardened to public standards and are not necessarily designed to withstand all hacking attempts. When an organisation allows external access to such internal applications via a reverse proxy, they might
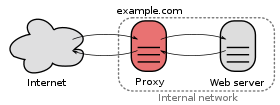
39:). The internal server delivers the requested resource back to the proxy, which in turn delivers it to the client. The client on the Internet is unaware of the internal network, and cannot tell whether it is communicating with a proxy or directly with a web server.
63:, but in reality merely acts as an intermediary that forwards the client's requests to one or more ordinary web servers. Reverse proxies help increase scalability, performance, resilience, and security, but they also carry a number of risks.
310:
an existing
Internet-facing server into a reverse proxy server. Compromised or converted systems allow external attackers to specify where they want their attacks proxied to, enabling their access to internal networks and systems.
295:
and the reverse proxy needs to filter/cache/compress or otherwise modify or improve the traffic, the proxy first must decrypt and re-encrypt communications. This requires the proxy to possess the
35:). The proxy inspects the request, determines that it is valid and that it does not have the requested resource in its own cache. It then forwards the request to some internal web server (
489:
151:
of static content, which further reduces the load on these internal servers and the internal network. It is also common for reverse proxies to add features such as
299:
and its corresponding private key, extending the number of systems that can have access to non-encrypted data and making it a more valuable target for attackers.
544:
433:
82:
on a company-internal network, and only the reverse proxy needs to be directly exposed to the
Internet. Reverse proxy servers are implemented in popular
306:
happen either when hackers succeed in abusing an existing reverse proxy that was intentionally deployed by an organisation, or when hackers succeed in
131:, which are used when the client is restricted to a private, internal network and asks a forward proxy to retrieve resources from the public Internet.
318:
If a reverse proxy is not configured to filter attacks or it does not receive daily updates to keep its attack signature database up to date, a
246:. Proxy caches of this sort can often satisfy a considerable number of website requests, greatly reducing the load on the origin server(s).
322:
vulnerability can pass through unfiltered, enabling attackers to gain control of the system(s) that are behind the reverse proxy server.
481:
384:
220:
from incoming requests to several servers, with each server supporting its own application area. In the case of reverse proxying
455:
536:
273:
425:
584:
170:
to the
Internet while relaying requests to different internal servers based on the URL of the HTTP request.
511:
360:
187:
or distributed denial-of-service attacks (DDoS). Without a reverse proxy, removing malware or initiating
579:
217:
144:
116:
making requests through it and it can also read and modify any non-encrypted traffic and risks logging
228:
in each incoming request in order to match the relevant internal location of the requested resource.
199:
184:
156:
140:
348:
191:(while simultaneously dealing with the attack) on one's own site, for example, can be difficult.
56:
344:, its outage (e.g., by a misconfiguration or DDoS attack) could bring down all fronted domains.
574:
276:
without requiring application code to handle the logic of which version is served to a client.
303:
210:
380:
319:
188:
180:
83:
79:
407:
8:
70:
often set up reverse proxies to facilitate the communication between an
Internet user's
262:
98:
90:
148:
78:. An important advantage of doing so is that the web servers can be hidden behind a
250:
239:
206:
152:
106:
44:
205:
itself, but instead offload the task to a reverse proxy that may be equipped with
296:
243:
235:
280:
195:
568:
174:
128:
459:
52:
537:"Cloudflare outage knocks out major sites and services, including Discord"
341:
269:
163:
71:
19:
326:
292:
221:
202:
167:
159:
to the communication channel between the client and the reverse proxy.
113:
86:
75:
67:
60:
315:
unintentionally increase their own attack surface and invite hackers.
334:
307:
261:
each incoming request and delivers it to the right server within the
232:
101:. Dedicated reverse proxy servers, such as the open source software
117:
330:
121:
102:
482:"Possible to add basic HTTP access authentication via HAProxy?"
183:
features can protect against common web-based attacks, like a
173:
Reverse proxies can hide the existence and characteristics of
94:
257:
extended time the client requires to complete the transfer.
109:, are used by some of the biggest websites on the Internet.
512:"forward_auth (Caddyfile directive) - Caddy Documentation"
408:"Nginx: the high-performance web server and reverse proxy"
231:
A reverse proxy can reduce load on its origin servers by
225:
351:
if there is no other way to access the back end server.
337:
in the hands of the third party who operates the proxy.
143:
use reverse proxies, together with other techniques, to
283:
to a web server that does not have any authentication.
166:, which, for example, allows them to present a single
373:
147:
between internal servers. Reverse proxies can keep a
335:
triad of confidentiality, integrity and availability
566:
325:Using the reverse proxy of a third party (e.g.,
340:If a reverse proxy is fronting many different
448:
224:, the reverse proxy may have to rewrite the
23:Example scenario: A client on the Internet (
456:"squid-cache wiki entry on "SpoonFeeding""
249:A reverse proxy can optimize content by
18:
253:it in order to speed up loading times.
567:
124:if compromised by a malicious party.
436:from the original on 26 November 2020
405:
458:. Francesco Chemolli. Archived from
492:from the original on 4 October 2018
387:from the original on 28 August 2018
13:
383:. The Apache Software Foundation.
347:Reverse proxies can also become a
14:
596:
547:from the original on 22 June 2020
279:A reverse proxy can add access
198:, a web server may not perform
529:
504:
474:
418:
406:Reese, Will (September 2008).
399:
302:The vast majority of external
185:denial-of-service attack (DoS)
112:A reverse proxy can track all
1:
426:"Proxy servers and tunneling"
381:"Forward and reverse proxies"
366:
291:When the transit traffic is
268:Reverse proxies can perform
162:Reverse proxies can inspect
127:Reverse proxies differ from
7:
361:Network address translation
354:
10:
601:
141:content delivery networks
51:or surrogate server is a
286:
349:single point of failure
134:
27:) makes a request to a
40:
33:red oval in the middle
585:Internet architecture
211:TLS termination proxy
22:
333:) places the entire
274:multivariate testing
216:A reverse proxy can
181:Application firewall
55:that appears to any
16:Type of proxy server
218:distribute the load
139:Large websites and
66:Companies that run
462:on 25 January 2019
263:local area network
59:to be an ordinary
41:
580:Computer networks
541:finance.yahoo.com
45:computer networks
37:oval on the right
25:cloud on the left
592:
557:
556:
554:
552:
533:
527:
526:
524:
522:
508:
502:
501:
499:
497:
478:
472:
471:
469:
467:
452:
446:
445:
443:
441:
422:
416:
415:
403:
397:
396:
394:
392:
377:
244:web acceleration
207:TLS acceleration
145:balance the load
600:
599:
595:
594:
593:
591:
590:
589:
565:
564:
561:
560:
550:
548:
535:
534:
530:
520:
518:
516:caddyserver.com
510:
509:
505:
495:
493:
486:serverfault.com
480:
479:
475:
465:
463:
454:
453:
449:
439:
437:
424:
423:
419:
404:
400:
390:
388:
379:
378:
374:
369:
357:
297:TLS certificate
289:
240:dynamic content
209:hardware. (See
196:secure websites
194:In the case of
137:
129:forward proxies
17:
12:
11:
5:
598:
588:
587:
582:
577:
559:
558:
528:
503:
473:
447:
417:
398:
371:
370:
368:
365:
364:
363:
356:
353:
288:
285:
281:authentication
236:static content
175:origin servers
157:TLS encryption
136:
133:
15:
9:
6:
4:
3:
2:
597:
586:
583:
581:
578:
576:
575:Reverse proxy
573:
572:
570:
563:
546:
542:
538:
532:
517:
513:
507:
491:
487:
483:
477:
461:
457:
451:
435:
431:
427:
421:
413:
412:Linux Journal
409:
402:
386:
382:
376:
372:
362:
359:
358:
352:
350:
345:
343:
338:
336:
332:
328:
323:
321:
316:
312:
309:
305:
304:data breaches
300:
298:
294:
284:
282:
277:
275:
271:
266:
264:
258:
254:
252:
247:
245:
241:
237:
234:
229:
227:
223:
219:
214:
212:
208:
204:
201:
197:
192:
190:
186:
182:
178:
176:
171:
169:
165:
160:
158:
154:
150:
146:
142:
132:
130:
125:
123:
120:or injecting
119:
115:
110:
108:
104:
100:
96:
92:
88:
85:
81:
77:
73:
69:
64:
62:
58:
54:
50:
49:reverse proxy
46:
38:
34:
30:
29:reverse proxy
26:
21:
562:
549:. Retrieved
540:
531:
519:. Retrieved
515:
506:
494:. Retrieved
485:
476:
464:. Retrieved
460:the original
450:
438:. Retrieved
430:MDN Web Docs
429:
420:
411:
401:
389:. Retrieved
375:
346:
339:
324:
317:
313:
301:
290:
278:
267:
259:
255:
248:
230:
215:
193:
179:
172:
164:HTTP headers
161:
138:
126:
114:IP addresses
111:
65:
53:proxy server
48:
42:
36:
32:
28:
24:
551:14 December
270:A/B testing
251:compressing
242:, known as
222:web servers
153:compression
87:web servers
84:open-source
76:web servers
68:web servers
569:Categories
466:9 February
440:6 December
367:References
327:Cloudflare
308:converting
203:encryption
168:IP address
89:, such as
61:web server
391:26 August
293:encrypted
189:takedowns
118:passwords
545:Archived
496:27 April
490:Archived
434:Archived
385:Archived
355:See also
320:zero-day
80:firewall
74:and the
31:server (
342:domains
331:Imperva
233:caching
122:malware
103:HAProxy
72:browser
521:22 May
414:(173).
97:, and
91:Apache
57:client
287:Risks
149:cache
107:Squid
99:Caddy
95:Nginx
553:2020
523:2022
498:2016
468:2011
442:2020
393:2018
272:and
238:and
135:Uses
105:and
47:, a
226:URL
213:.)
200:TLS
155:or
43:In
571::
543:.
539:.
514:.
488:.
484:.
432:.
428:.
410:.
329:,
265:.
93:,
555:.
525:.
500:.
470:.
444:.
395:.
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.