64:
586:
296:
76:
520:
126:
97:
141:
284:", obliging family members never to discuss disagreeable issues concerning the family with outsiders or sometimes even within the family. Many "family secrets" are maintained by using a mutually agreed-upon construct (an official family story) when speaking with outside members. Agreement to maintain the secret is often coerced through "shaming" and reference to family
430:
Secrecy in elections is a growing issue, particularly secrecy of vote counts on computerized vote counting machines. While voting, citizens are acting in a unique sovereign or "owner" capacity (instead of being a subject of the laws, as is true outside of elections) in selecting their government
458:
Research on corporate secrecy has studied the factors supporting secret organizations. In particular, scholars in economics and management have paid attention to the way firms participating in cartels work together to maintain secrecy and conceal their activities from antitrust authorities. The
431:
servants. It is argued that secrecy is impermissible as against the public in the area of elections where the government gets all of its power and taxing authority. In any event, permissible secrecy varies significantly with the context involved.
216:"True" secrecy systems where the meaning of the message is concealed by the cypher, code, etc. Although, its existence is not hidden. The enemy is assumed to have any special equipment necessary to intercept and record the transmitted signal.
609:
Military secrecy is the concealing of information about martial affairs that is purposely not made available to the general public and hence to any enemy, in order to gain an advantage or to not reveal a weakness, to avoid
666:
repercussions. The alternative, declining to answer when asked something, may suggest the answer and may therefore not always be suitable for keeping a secret. Also, the other may insist that one answer the question.
451:, to meet legal requirements, or, in some cases, to conceal nefarious behavior. New products under development, unique manufacturing techniques, or simply lists of customers are types of information protected by
205:
Concealment systems, including such methods as invisible ink, concealing a message in a harmless text in a fake covering cryptogram, or other methods in which the existence of the message is concealed from the
89:
is the practice of hiding information from certain individuals or groups who do not have the "need to know", perhaps while sharing it with other individuals. That which is kept hidden is known as the secret.
984:"Chapter 5: Handling and safeguarding of classified and protected information and assets – Industrial Security Manual – Security requirements for contracting with the Government of Canada – Canada.ca"
577:. It is considered easier to verify software reliability if one can be sure that different parts of the program can only access (and therefore depend on) a known limited amount of information.
407:
secret, but many believe government secrecy to be excessive and too often employed for political purposes. Many countries have laws that attempt to limit government secrecy, such as the U.S.
1074:
Faulkner, Robert R.; Cheney, Eric R.; Fisher, Gene A.; Baker, Wayne E. (2003). "Crime by
Committee: Conspirators and Company Men in the Illegal Electrical Industry Cartel, 1954–1959".
939:
Manderson, Lenore; Davis, Mark; Colwell, Chip; Ahlin, Tanja (December 2015). "On
Secrecy, Disclosure, the Public, and the Private in Anthropology: An Introduction to Supplement 12".
110:
Secrecy by government entities is often decried as excessive or in promotion of poor operation; excessive revelation of information on individuals can conflict with virtues of
178:(where mathematical and technical strategies are used to hide messages), true secrecy (where restrictions are put upon those who take part of the message, such as through
626:, training methods, plans, and the number and location of specific weapons. Some secrets involve information in broader areas, such as secure communications,
346:
secret sharing is one way for people to establish traditional relations with other people. A commonly used narrative that describes this kind of behavior is
93:
Secrecy is often controversial, depending on the content or nature of the secret, the group or people keeping the secret, and the motivation for secrecy.
496:
1031:
Baker, Wayne E.; Faulkner, Robert R. (1993). "The Social
Organization of Conspiracy: Illegal Networks in the Heavy Electrical Equipment Industry".
303:
925:
393:
408:
404:
1109:
459:
diversity of the participants (in terms of age and size of the firms) influences their ability to coordinate to avoid being detected.
633:
1191:
1397:
The federal information manual: how the government collects, manages, and discloses information under FOIA and other statutes
1175:
377:
538:
164:
1591:
1261:
765:
647:
53:
1616:
1530:
1492:
1470:
1444:
1408:
1372:
570:
1229:
Lightfoot, Geoffrey; Wisniewski, Tomasz Piotr (2014). "Information asymmetry and power in a surveillance society".
1007:
1636:
226:
1133:
157:
1607:
1383:
365:
often attempt to conceal information from other governments and the public. These state secrets can include
1334:
1303:
888:
480:
may be used to launder money from criminal activity, to finance terrorism, or to evade taxes. Registers of
57:
1454:
755:
79:
1418:
Maret, Susan, ed. (2014). "Government secrecy, Research in Social
Problems and Public Policy, vol. 19".
1462:
805:
564:
546:
642:
310:
Secrets are sometimes kept to provide the pleasure of surprise. This includes keeping secret about a
17:
873:
1549:
1545:
1514:
1400:
542:
46:
31:
448:
27:
Practice of hiding information to certain individual or group for personal or interpersonal reason
815:
715:
42:
38:
388:
in the U.S.) and classify material according to the level of protection needed (hence the term "
1008:"- THE FREEDOM OF INFORMATION ACT: ENSURING TRANSPARENCY AND ACCOUNTABILITY IN THE DIGITAL AGE"
983:
720:
618:
efforts. Most military secrets are tactical in nature, such as the strengths and weaknesses of
567:. Many believe that security technology can be more effective if it itself is not kept secret.
389:
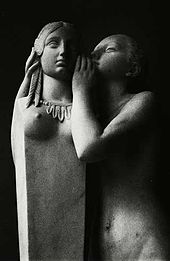
179:
149:
63:
918:
1584:
Everybody Lies: Big Data, New Data, and What the
Internet Can Tell Us About Who We Really Are
860:
600:
593:
585:
119:
574:
552:
481:
381:
849:
104:
8:
785:
1351:
1320:
1087:
1056:
964:
770:
725:
675:
674:
wrote: 'Do nothing secretly; for Time sees and hears all things, and discloses all.'.
1587:
1557:
1526:
1519:
1488:
1466:
1440:
1423:
1404:
1368:
1355:
1324:
1289:
1257:
1216:
1171:
1091:
1048:
968:
956:
906:
735:
658:
Excessive secrecy is often cited as a source of much human conflict. One may have to
556:
477:
351:
269:
295:
246:. Squirrels bury nuts, hiding them, and they try to remember their locations later.
1631:
1343:
1312:
1285:
1163:
1083:
1040:
948:
800:
740:
623:
500:
319:
133:
1332:
Birchall, Clare (December 2011). "Transparency interrupted: secrets of the left".
1252:
Secrecy in the
Sunshine Era: The Promise and Failures of U.S. Open Government Laws
466:
system encourages inventors to publish information in exchange for a limited time
1566:
1250:
730:
705:
504:
315:
210:
186:, where secrets are hidden in plain sight behind complex idiosyncratic language (
153:
115:
1502:
96:
1480:
795:
790:
531:
492:
471:
416:
198:
1556:, London: Longman, Rees, Orme, Brown, Green, & Longman, pp. 128–131,
75:
1625:
1427:
1347:
1316:
1095:
1052:
960:
710:
637:
619:
611:
385:
347:
281:
273:
191:
1110:"How Anonymous Shell Companies Finance Insurgents, Criminals, and Dictators"
519:
311:
201:
in 1948 reads that there are three systems of secrecy within communication:
1561:
1517:(1991), "Sir Henry Taylor (1800-86): On secrecy", in Gross, John J. (ed.),
982:
Government of Canada, Public
Services and Procurement Canada (2017-12-12).
775:
627:
560:
474:
use secrecy as a way to attract members by creating a sense of importance.
452:
422:
412:
343:
160:
68:
1159:
Read "Computers at Risk: Safe
Computing in the Information Age" at NAP.edu
1157:
887:
November 2018, Emma Bryce-Live
Science Contributor 17 (17 November 2018).
780:
604:
440:
373:
336:
183:
396:
for access and other protection methods, such as keeping documents in a
252:
attempt to consciously conceal aspects of themselves from others due to
125:
1192:"Digital Open Source Intelligence and International Security: A Primer"
1060:
663:
615:
362:
272:
which they are not capable of incorporating psychologically into their
265:
261:
175:
1276:": The false choice between secrecy and transparency in US politics".
140:
827:
810:
760:
750:
700:
671:
444:
370:
243:
167:
1437:
Death by mustard gas: how military secrecy and lost weapons can kill
1044:
952:
821:
745:
508:
467:
326:
145:
1167:
111:
1612:
1506:
630:, intelligence operations, and cooperation with third parties.
463:
366:
289:
277:
235:
231:
187:
687:
470:
on its use, though patent applications are initially secret.
285:
253:
249:
174:
Secrecy can exist in a number of different ways: encoding or
683:
397:
257:
239:
938:
491:
organizations to keep certain information secret, such as
268:. Humans may also attempt to conceal aspects of their own
1073:
889:"How Do Squirrels Remember Where They Buried Their Nuts?"
679:
659:
288:. The information may even be something as trivial as a
213:, is a special equipment required to recover the message.
1581:
636:
rights in regard to military secrecy were uphold in the
52:"Clandestinity" redirects here. Not to be confused with
1485:
Secrets and lies: digital security in a networked world
1459:
Blacked out: government secrecy in the information age
439:
Organizations, ranging from multi-national for profit
376:
tactics, and secrets obtained illicitly from others ("
1525:, Oxford England New York: Oxford University Press,
1365:
Secrets: on the ethics of concealment and revelation
981:
1228:
1518:
1297:Birchall, Clare (December 2011). "Introduction to
1249:
678:said: "Three things cannot long stay hidden: the
484:aim at fighting corporate secrecy in that sense.
37:Several terms redirect here. For other uses, see
1623:
1608:An Open Source Collection of Readings on Secrecy
1439:. Newport, New South Wales: Big Sky Publishing.
662:in order to hold a secret, which might lead to
551:Preservation of secrets is one of the goals of
419:information they are supposed to keep secret. (
403:Few people dispute the desirability of keeping
1420:Research in Social Problems and Public Policy
1219:, decided 8 March 1953, accessed 5 April 2023
1030:
886:
507:). Europe has particularly strict laws about
1217:United States v. Reynolds, 345 U.S. 1 (1953)
847:
260:of violence, rejection, harassment, loss of
1394:
1274:There's been too much secrecy in this City
405:Critical Nuclear Weapon Design Information
1301:: the politics of opacity and openness".
1138:European Commission - European Commission
850:"Communication Theory of Secrecy Systems"
1479:
1434:
1331:
1296:
1271:
924:CS1 maint: numeric names: authors list (
584:
518:
294:
139:
130:A Secret from on High (Secret d'en haut)
124:
95:
74:
62:
1453:
563:. The latter depends on the secrecy of
14:
1624:
1544:
1513:
1382:Canal, Vicente Aceituno (April 2006).
1247:
1417:
1381:
503:that are under preparation (to limit
1362:
539:Full disclosure (computer security)
380:"). Most nations have some form of
197:Another classification proposed by
24:
1575:
1088:10.1111/j.1745-9125.2003.tb00996.x
766:Freedom of information legislation
335:– is important in many aspects of
180:government security classification
54:Clandestinity (Catholic canon law)
25:
1648:
1617:Federation of American Scientists
1601:
1582:Seth Stephens-Davidowitz (2018).
1503:"Secrecy Legal News and Research"
421:For a recent (2005) example, see
415:. Government officials sometimes
1487:. Indianapolis, Indiana: Wiley.
1395:Gidiere III, P. Stephen (2006).
1290:10.2752/175174311X12861940861905
1272:Birchall, Clare (March 2011). ""
101:First secret confidence to Venus
1222:
1209:
1184:
1150:
434:
227:Sociological aspects of secrecy
1256:. University Press of Kansas.
1126:
1102:
1067:
1024:
1000:
975:
932:
880:
841:
573:is a design principle in much
234:conceal the location of their
209:Privacy systems, for example,
118:. It is often contrasted with
13:
1:
1335:Theory, Culture & Society
1304:Theory, Culture & Society
834:
357:
1231:Information and Organization
1114:Council on Foreign Relations
1033:American Sociological Review
514:
220:
67:U.S. soldier at camp during
7:
1367:. New York: Vintage Books.
1248:Arnold, Jason Ross (2014).
1134:"Data protection in the EU"
848:Shannon, C.E. (1946–1948).
693:
580:
80:Loose lips might sink ships
10:
1653:
1463:Cambridge University Press
598:
555:. Techniques used include
547:security through obscurity
536:
409:Freedom of Information Act
392:"). An individual needs a
224:
51:
36:
29:
1548:(1836), "On secrecy", in
1521:The Oxford book of essays
1384:"How secret is a secret?"
643:United States v. Reynolds
369:designs, military plans,
318:of a story, and avoiding
1435:Plunkett, Geoff (2014).
1422:. Bingley, UK: Emerald.
1401:American Bar Association
1348:10.1177/0263276411423040
1317:10.1177/0263276411427744
1299:secrecy and transparency
653:
47:Secrets (disambiguation)
32:Secrecy (disambiguation)
816:State Secrets Privilege
806:Somebody Else's Problem
716:Clandestine cell system
670:Nearly 2500 years ago,
150:security classification
136:(Hypolite Moulin), 1879
43:Secret (disambiguation)
39:Covert (disambiguation)
1637:Classified information
1461:. Cambridge New York:
868:Cite journal requires
721:Classified information
596:
534:
390:classified information
307:
171:
137:
107:
83:
72:
56:. For other uses, see
1363:Bok, Sissela (1989).
988:www.tpsgc-pwgsc.gc.ca
756:Don't ask, don't tell
601:Military intelligence
594:Edmund Blair Leighton
588:
543:Kerckhoffs' principle
522:
449:competitive advantage
302:, (Das Geheimnis) by
298:
143:
128:
99:
82:, World War II slogan
78:
66:
1586:. Dey Street Books.
941:Current Anthropology
575:software engineering
553:information security
482:beneficial ownership
382:Official Secrets Act
280:sometimes maintain "
30:For other uses, see
1543:Also available as:
786:Secrecy (sociology)
638:landmark legal case
447:, keep secrets for
120:social transparency
1215:US Supreme Court,
947:(S12): S183–S190.
917:has generic name (
771:Media transparency
726:Concealment device
676:Gautama Siddhartha
597:
590:A Stolen Interview
571:Information hiding
565:cryptographic keys
535:
400:, are stipulated.
394:security clearance
322:of a magic trick.
308:
172:
138:
108:
84:
73:
1455:Roberts, Alasdair
1278:Cultural Politics
1177:978-0-309-04388-5
736:Conspiracy theory
646:, decided by the
557:physical security
501:financial reports
499:in the U.S.), or
352:The Secret Sharer
105:François Jouffroy
16:(Redirected from
1644:
1597:
1565:
1536:
1524:
1510:
1498:
1476:
1450:
1431:
1414:
1391:
1378:
1359:
1328:
1293:
1267:
1255:
1239:
1238:
1226:
1220:
1213:
1207:
1206:
1204:
1203:
1188:
1182:
1181:
1154:
1148:
1147:
1145:
1144:
1130:
1124:
1123:
1121:
1120:
1106:
1100:
1099:
1071:
1065:
1064:
1028:
1022:
1021:
1019:
1018:
1004:
998:
997:
995:
994:
979:
973:
972:
936:
930:
929:
922:
916:
912:
910:
902:
900:
899:
884:
878:
877:
871:
866:
864:
856:
854:
845:
801:Self-concealment
741:Covert operation
614:, or to help in
472:Secret societies
350:'s short story "
334:
134:Hippolyte Moulin
21:
1652:
1651:
1647:
1646:
1645:
1643:
1642:
1641:
1622:
1621:
1604:
1594:
1578:
1576:Further reading
1573:
1533:
1501:
1495:
1481:Schneier, Bruce
1473:
1447:
1411:
1375:
1264:
1243:
1242:
1227:
1223:
1214:
1210:
1201:
1199:
1190:
1189:
1185:
1178:
1156:
1155:
1151:
1142:
1140:
1132:
1131:
1127:
1118:
1116:
1108:
1107:
1103:
1072:
1068:
1045:10.2307/2095954
1029:
1025:
1016:
1014:
1012:www.govinfo.gov
1006:
1005:
1001:
992:
990:
980:
976:
937:
933:
923:
914:
913:
904:
903:
897:
895:
893:livescience.com
885:
881:
869:
867:
858:
857:
852:
846:
842:
837:
832:
731:Confidentiality
706:Banking secrecy
696:
656:
607:
583:
549:
517:
505:insider trading
493:medical records
478:Shell companies
437:
360:
332:
229:
223:
211:voice inversion
116:confidentiality
61:
50:
35:
28:
23:
22:
15:
12:
11:
5:
1650:
1640:
1639:
1634:
1620:
1619:
1610:
1603:
1602:External links
1600:
1599:
1598:
1593:978-0062390868
1592:
1577:
1574:
1572:
1571:
1570:
1569:
1538:
1537:
1531:
1511:
1499:
1493:
1477:
1471:
1451:
1445:
1432:
1415:
1409:
1392:
1379:
1373:
1360:
1342:(7–8): 60–84.
1329:
1294:
1284:(1): 133–156.
1269:
1263:978-0700619924
1262:
1244:
1241:
1240:
1221:
1208:
1198:. 17 July 2018
1183:
1176:
1149:
1125:
1101:
1082:(2): 511–554.
1066:
1039:(6): 837–860.
1023:
999:
974:
953:10.1086/683302
931:
879:
870:|journal=
839:
838:
836:
833:
831:
830:
825:
818:
813:
808:
803:
798:
796:Secret sharing
793:
791:Secret passage
788:
783:
778:
773:
768:
763:
758:
753:
748:
743:
738:
733:
728:
723:
718:
713:
708:
703:
697:
695:
692:
655:
652:
620:weapon systems
582:
579:
532:Felix Nussbaum
516:
513:
436:
433:
359:
356:
325:Keeping one’s
314:, not telling
312:surprise party
304:Moritz Stifter
282:family secrets
225:Main article:
222:
219:
218:
217:
214:
207:
199:Claude Shannon
165:Vice President
152:stickers on a
26:
9:
6:
4:
3:
2:
1649:
1638:
1635:
1633:
1630:
1629:
1627:
1618:
1614:
1611:
1609:
1606:
1605:
1595:
1589:
1585:
1580:
1579:
1568:
1563:
1559:
1555:
1554:The statesman
1551:
1550:Taylor, Henry
1547:
1546:Taylor, Henry
1542:
1541:
1540:
1539:
1534:
1532:9780192141859
1528:
1523:
1522:
1516:
1515:Taylor, Henry
1512:
1508:
1504:
1500:
1496:
1494:9780471453802
1490:
1486:
1482:
1478:
1474:
1472:9780521858700
1468:
1464:
1460:
1456:
1452:
1448:
1446:9781922132918
1442:
1438:
1433:
1429:
1425:
1421:
1416:
1412:
1410:9781590315798
1406:
1402:
1398:
1393:
1389:
1385:
1380:
1376:
1374:9780679724735
1370:
1366:
1361:
1357:
1353:
1349:
1345:
1341:
1337:
1336:
1330:
1326:
1322:
1318:
1314:
1311:(7–8): 7–25.
1310:
1306:
1305:
1300:
1295:
1291:
1287:
1283:
1279:
1275:
1270:
1265:
1259:
1254:
1253:
1246:
1245:
1237:(4): 214–235.
1236:
1232:
1225:
1218:
1212:
1197:
1193:
1187:
1179:
1173:
1169:
1168:10.17226/1581
1165:
1161:
1160:
1153:
1139:
1135:
1129:
1115:
1111:
1105:
1097:
1093:
1089:
1085:
1081:
1077:
1070:
1062:
1058:
1054:
1050:
1046:
1042:
1038:
1034:
1027:
1013:
1009:
1003:
989:
985:
978:
970:
966:
962:
958:
954:
950:
946:
942:
935:
927:
920:
908:
894:
890:
883:
875:
862:
851:
844:
840:
829:
826:
824:
823:
819:
817:
814:
812:
809:
807:
804:
802:
799:
797:
794:
792:
789:
787:
784:
782:
779:
777:
774:
772:
769:
767:
764:
762:
759:
757:
754:
752:
749:
747:
744:
742:
739:
737:
734:
732:
729:
727:
724:
722:
719:
717:
714:
712:
711:Black project
709:
707:
704:
702:
699:
698:
691:
689:
685:
681:
677:
673:
668:
665:
664:psychological
661:
651:
649:
648:Supreme Court
645:
644:
639:
635:
634:US Government
631:
629:
625:
621:
617:
613:
612:embarrassment
606:
602:
595:
591:
587:
578:
576:
572:
568:
566:
562:
558:
554:
548:
544:
540:
533:
529:
528:) (Le secret)
525:
524:Das Geheimnis
521:
512:
510:
506:
502:
498:
494:
490:
485:
483:
479:
475:
473:
469:
465:
460:
456:
454:
450:
446:
443:to nonprofit
442:
432:
428:
426:
424:
418:
414:
413:sunshine laws
410:
406:
401:
399:
395:
391:
387:
386:Espionage Act
383:
379:
375:
372:
368:
364:
355:
353:
349:
348:Joseph Conrad
345:
340:
338:
331:
328:
323:
321:
317:
313:
305:
301:
297:
293:
291:
287:
283:
279:
275:
271:
267:
264:, or loss of
263:
259:
255:
251:
247:
245:
241:
237:
233:
228:
215:
212:
208:
204:
203:
202:
200:
195:
193:
192:steganography
189:
185:
181:
177:
170:, May 1, 2011
169:
166:
162:
159:
158:U.S.President
155:
151:
147:
142:
135:
131:
127:
123:
121:
117:
113:
106:
102:
98:
94:
91:
88:
81:
77:
70:
65:
59:
55:
48:
44:
40:
33:
19:
1613:Secrecy News
1583:
1553:
1520:
1484:
1458:
1436:
1419:
1396:
1388:ISSA Journal
1387:
1364:
1339:
1333:
1308:
1302:
1298:
1281:
1277:
1273:
1251:
1234:
1230:
1224:
1211:
1200:. Retrieved
1195:
1186:
1158:
1152:
1141:. Retrieved
1137:
1128:
1117:. Retrieved
1113:
1104:
1079:
1075:
1069:
1036:
1032:
1026:
1015:. Retrieved
1011:
1002:
991:. Retrieved
987:
977:
944:
940:
934:
915:|first=
896:. Retrieved
892:
882:
861:cite journal
843:
820:
776:Need to know
669:
657:
641:
632:
628:cryptography
608:
589:
569:
561:cryptography
550:
527:
523:
488:
486:
476:
461:
457:
453:trade secret
441:corporations
438:
435:Corporations
429:
423:Plame affair
420:
402:
378:intelligence
361:
344:anthropology
341:
329:
324:
309:
299:
248:
230:
196:
173:
161:Barack Obama
129:
109:
100:
92:
86:
85:
69:World War II
1399:. Chicago:
1196:edam.org.tr
1076:Criminology
781:Open secret
605:Born secret
526:(The Secret
487:Other laws
374:negotiation
363:Governments
337:game theory
184:obfuscation
58:Clandestine
1626:Categories
1202:2020-06-03
1143:2020-06-03
1119:2020-06-03
1017:2020-06-03
993:2020-06-03
898:2020-06-03
835:References
616:propaganda
599:See also:
537:See also:
371:diplomatic
358:Government
300:The Secret
266:employment
262:acceptance
256:, or from
176:encryption
156:, between
1615:from the
1428:0196-1152
1356:144862855
1325:145098295
1096:1745-9125
1053:0003-1224
969:147148098
961:0011-3204
828:WikiLeaks
811:Smuggling
761:Espionage
751:Deception
701:Ambiguity
672:Sophocles
650:in 1953.
515:Computing
511:privacy.
445:charities
274:conscious
244:predators
221:Sociology
168:Joe Biden
18:Secretive
1567:Preview.
1483:(2004).
1457:(2006).
1162:. 1991.
907:cite web
822:Sub rosa
746:Cover-up
694:See also
686:and the
581:Military
509:database
468:monopoly
327:strategy
320:exposure
316:spoilers
278:Families
276:being.
146:burn bag
1632:Secrecy
1562:4790233
1552:(ed.),
1061:2095954
624:tactics
489:require
232:Animals
112:privacy
87:Secrecy
1590:
1560:
1529:
1507:JURIST
1491:
1469:
1443:
1426:
1407:
1371:
1354:
1323:
1260:
1174:
1094:
1059:
1051:
967:
959:
682:, the
545:, and
464:patent
455:laws.
367:weapon
333:
330:secret
306:, 1885
290:recipe
250:Humans
206:enemy.
188:jargon
182:) and
154:laptop
45:, and
1352:S2CID
1321:S2CID
1057:JSTOR
965:S2CID
853:(PDF)
688:truth
654:Views
497:HIPAA
384:(the
286:honor
254:shame
242:from
190:) or
1588:ISBN
1558:OCLC
1527:ISBN
1489:ISBN
1467:ISBN
1441:ISBN
1424:ISSN
1405:ISBN
1369:ISBN
1258:ISBN
1172:ISBN
1092:ISSN
1049:ISSN
957:ISSN
926:link
919:help
874:help
855:: 1.
690:.".
684:moon
603:and
559:and
462:The
417:leak
411:and
398:safe
270:self
258:fear
240:nest
163:and
148:and
114:and
1344:doi
1313:doi
1286:doi
1164:doi
1084:doi
1041:doi
949:doi
680:sun
660:lie
640:of
354:".
342:In
238:or
236:den
1628::
1505:.
1465:.
1403:.
1386:.
1350:.
1340:28
1338:.
1319:.
1309:28
1307:.
1280:.
1235:24
1233:.
1194:.
1170:.
1136:.
1112:.
1090:.
1080:41
1078:.
1055:.
1047:.
1037:58
1035:.
1010:.
986:.
963:.
955:.
945:56
943:.
911::
909:}}
905:{{
891:.
865::
863:}}
859:{{
622:,
592:,
541:,
530:,
427:)
339:.
292:.
194:.
144:A
132:,
122:.
103:,
41:,
1596:.
1564:.
1535:.
1509:.
1497:.
1475:.
1449:.
1430:.
1413:.
1390:.
1377:.
1358:.
1346::
1327:.
1315::
1292:.
1288::
1282:7
1268:*
1266:.
1205:.
1180:.
1166::
1146:.
1122:.
1098:.
1086::
1063:.
1043::
1020:.
996:.
971:.
951::
928:)
921:)
901:.
876:)
872:(
495:(
425:.
71:.
60:.
49:.
34:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.