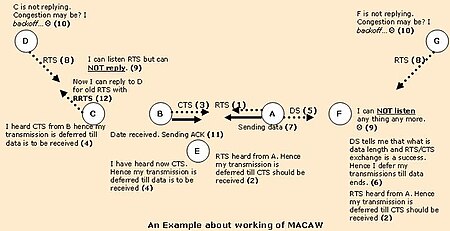
235:. Node G assumes that its RTS was not successful because of collision and hence backs off before it tries again. In this case, the solution provided by the RRTS mechanism will not improve the situation much since the DATA frames sent from B are rather long compared to the other frames. The probability that F is exposed to transmission from A is rather high. Node F has no idea about any node interested in initiating data transfer to it, until G happens to transmit an RTS in between transmissions from A.
82:
231:. Assume that node G has data to send to node F in our example. Node G has no information about the ongoing data transfer from A to B. It initiates the process by sending an RTS signal to node F. Node F is in the transmission range of node A and cannot hear the RTS from node G, since it is exposed to
97:
frame (CTS). After receiving CTS, node A sends data. After successful reception, node B replies with an acknowledgement frame (ACK). If node A has to send more than one data fragment, it has to wait a random time after each successful data transfer and compete with adjacent nodes for the medium using
183:
Now, when node C, which cannot reply earlier due to ongoing transmission between node A and node B, sends an RRTS message to node D during next contention period, the recipient of the RRTS (node D) immediately responds with an RTS and the normal message exchange is commenced. Other nodes overhearing
112:
Before sending a long DATA frame, node A sends a short Data-Sending frame (DS), which provides information about the length of the DATA frame. Every station that overhears this frame knows that the RTS/CTS exchange was successful. An overhearing station (node F), which might have received RTS and DS
218:
Additional back-off algorithms have been developed and researched to improve performance. The basic principle is based on the use of sequencing techniques where each node in the wireless network maintains a counter which limits the number attempts to less than or equal to the sequence number or use
179:
If A has multiple data fragments to send, the only instant when node D successfully can initiate a data transfer is during small gaps in between that node A has completed data transfer and completion of node B next CTS (for node A next data transfer request). However, due to the node D backoff time
163:
Node D is unaware of the ongoing data transfer between node A and node B. Node D has data to send to node C, which is in the transmission range of node B. D initiates the process by sending an RTS frame to node C. Node C has already deferred its transmission until the completion of the current data
143:
protocol, meaning that after the medium has been busy, for example after a CTS message, the station waits a random time after the start of a time slot before sending an RTS. This results in fair access to the medium. If for example nodes A, B and C have data fragments to send after a busy period,
101:
Any node overhearing an RTS frame (for example node F or node E in the illustration) refrains from sending anything until a CTS is received, or after waiting a certain time. If the captured RTS is not followed by a CTS, the maximum waiting time is the RTS propagation time and the destination node
545:
P.Venkata
Krishna & N.Ch.S.N.Iyengar, 'Sequencing Technique – An Enhancement to 802.11 Medium Access Control to improve the performance of Wireless Networks', Int. J. Communication Networks and Distributed Systems, Vol.1, No.1, pp 52-70,
535:
P. Venkata
Krishna & N.Ch.S.N. Iyengar “Design of Sequencing Medium Access Control to improve the performance of Wireless Networks” Journal of Computing and Information Technology (CIT Journal), Vol. 16, No. 2, pp. 81-89, June
180:
period the probability to capture the medium during this small time interval is not high. To increase the per-node fairness, MACAW introduces a new control message called "Request for
Request to Send" (RRTS).
525:
Sudip Misra, P. Venkata
Krishna and Kiran Issac Abraham, “Learning Automata Solution for Medium Access with Channel Reservation in Wireless Networks” accepted in Wireless Personal Communications (WPS),
109:), plus a random time. Both the RTS and CTS frames contain information about the length of the DATA frame. Hence a node uses that information to estimate the time for the data transmission completion.
516:
and V. Saritha, “Virtual
Backoff Algorithm: An Enhancement to 802.11 Medium Access Control to Improve the Performance of Wireless Networks” in IEEE Trans. on Vehicular Technology (VTS), 2010
219:
wireless channel states to control the access probabilities so that a node with a good channel state has a higher probability of contention success. This reduces the number of collisions.
168:
at node B). Hence, even though it receives RTS from node D, it does not reply back with CTS. Node D assumes that its RTS was not successful because of collision and hence proceeds to
105:
Any node (node C and node E) overhearing a CTS frame refrains from sending anything for the time until the data frame and ACK should have been received (solving the
834:
801:
574:
137:
654:
617:
442:
659:
702:
940:
140:
819:
251:
935:
85:
An example to illustrate the principle of MACAW. It is assumed that only adjacent nodes are in transmission range of each other.
730:
337:
567:
634:
390:
604:
497:
839:
697:
462:
849:
961:
629:
811:
773:
692:
612:
560:
712:
113:
but not CTS, defers its transmissions until after the ACK frame should have been received plus a random time.
966:
829:
745:
669:
646:
187:
To summarize, a transfer may in this case consist of the following sequence of frames between node D and C:
927:
844:
144:
they will have the same chance to access the medium since they are in transmission range of each other.
489:
908:
428:
375:
319:
903:
228:
46:
552:
232:
165:
106:
913:
454:
184:
an RRTS defer for two time slots, long enough to hear if a successful RTS–CTS exchange occurs.
116:
To sum up, a successful data transfer (A to B) consists of the following sequence of frames:
898:
587:
583:
415:
396:. IEEE/ACM Transactions on Networking, Vol. 12, No. 3, pp. 493-506, June 2004. Archived from
362:
306:
89:
Assume that node A has data to transfer to node B. Node A initiates the process by sending a
38:
17:
446:
288:
882:
8:
622:
513:
173:
62:
50:
391:"Medium Access Control With Coordinated Adaptive Sleeping for Wireless Sensor Networks"
781:
877:
791:
595:
493:
458:
447:
864:
764:
344:
73:
in addition to the RTS/CTS mechanism, MACAW does not make use of carrier sense.
294:. In the Proc. ACM SIGCOMM Conference (SIGCOMM '94), August 1994, pages 212-225
42:
955:
397:
70:
194:“Request for Request to send” frame (RRTS) from C to D (after a short delay)
481:
45:. Furthermore, it is the foundation of many other MAC protocols used in
872:
854:
239:
27:
Slotted medium access control protocol widely used in ad hoc networks
93:
frame (RTS) to node B. The destination node (node B) replies with a
786:
687:
582:
682:
81:
720:
677:
338:"An Energy-Efficient MAC Protocol for Wireless Sensor Networks"
57:
frame sequence for transferring data, sometimes preceded by an
796:
66:
480:
449:
486:
Energy and spectrum efficient wireless network design
31:
Multiple Access with
Collision Avoidance for Wireless
289:"MACAW: A Medium Access Protocol for Wireless LAN's"
61:frame sequence, in view to provide solution to the
286:
53:mechanism is adopted from this protocol. It uses
953:
238:Furthermore, MACAW might not behave normally in
287:Vaduvur Bharghavan; et al. (1994-08-01).
568:
164:transfer between node A and node B (to avoid
65:. Although protocols based on MACAW, such as
575:
561:
76:
197:“Request To Send” frame (RTS) from D to C
191:“Request To Send” frame (RTS) from D to C
120:“Request To Send” frame (RTS) from A to B
331:
329:
252:Multiple Access with Collision Avoidance
132:Acknowledgement frame (ACK) from B to A.
80:
282:
280:
278:
276:
274:
272:
270:
268:
209:Acknowledgement frame (ACK) from C to D
200:“Clear To Send” frame (CTS) from C to D
123:“Clear To Send” frame (CTS) from B to A
14:
954:
476:
474:
388:
335:
556:
435:
382:
326:
203:“Data Sending” frame (DS) from D to C
126:“Data Sending” frame (DS) from A to B
441:
265:
222:
129:DATA fragment frame from A to B, and
471:
227:MACAW does not generally solve the
213:
24:
389:Wei Ye; et al. (2004-06-01).
336:Wei Ye; et al. (2002-06-01).
25:
978:
512:P. Venkata Krishna, Sudip Misra,
206:DATA fragment frame from D to C,
539:
529:
519:
506:
343:. INFOCOM 2002. Archived from
41:(MAC) protocol widely used in
13:
1:
892:Delay and disruption tolerant
258:
7:
245:
10:
983:
490:Cambridge University Press
926:
891:
863:
810:
772:
763:
744:
729:
711:
668:
645:
603:
594:
229:exposed terminal problem
147:
47:wireless sensor networks
962:Wireless sensor network
484:; Guocong Song (2014).
233:co-channel interference
166:co-channel interference
107:hidden terminal problem
98:the RTS/CTS mechanism.
77:Principles of operation
914:Dynamic Source Routing
584:Channel access methods
423:Cite journal requires
370:Cite journal requires
314:Cite journal requires
86:
84:
39:medium access control
967:Media access control
588:media access control
812:Collision avoidance
514:Mohhamed S. Obaidat
174:exponential backoff
63:hidden node problem
55:RTS-CTS-DS-DATA-ACK
51:IEEE 802.11 RTS/CTS
774:Collision recovery
87:
949:
948:
928:Duplexing methods
922:
921:
759:
758:
453:. Wiley. p.
223:Unsolved problems
102:turnaround time.
16:(Redirected from
974:
770:
769:
601:
600:
577:
570:
563:
554:
553:
547:
543:
537:
533:
527:
523:
517:
510:
504:
503:
478:
469:
468:
452:
439:
433:
432:
426:
421:
419:
411:
409:
408:
402:
395:
386:
380:
379:
373:
368:
366:
358:
356:
355:
349:
342:
333:
324:
323:
317:
312:
310:
302:
300:
299:
293:
284:
214:Ongoing research
160:
159:
155:
21:
982:
981:
977:
976:
975:
973:
972:
971:
952:
951:
950:
945:
918:
887:
859:
806:
755:
740:
725:
707:
664:
641:
590:
581:
551:
550:
544:
540:
534:
530:
524:
520:
511:
507:
500:
479:
472:
465:
440:
436:
424:
422:
413:
412:
406:
404:
400:
393:
387:
383:
371:
369:
360:
359:
353:
351:
347:
340:
334:
327:
315:
313:
304:
303:
297:
295:
291:
285:
266:
261:
248:
225:
216:
161:
157:
153:
151:
150:
91:Request to Send
79:
43:ad hoc networks
37:) is a slotted
28:
23:
22:
15:
12:
11:
5:
980:
970:
969:
964:
947:
946:
944:
943:
938:
932:
930:
924:
923:
920:
919:
917:
916:
911:
906:
901:
895:
893:
889:
888:
886:
885:
880:
875:
869:
867:
865:Collision-free
861:
860:
858:
857:
852:
847:
842:
837:
832:
827:
822:
816:
814:
808:
807:
805:
804:
799:
794:
789:
784:
778:
776:
767:
761:
760:
757:
756:
754:
753:
750:
748:
742:
741:
739:
738:
735:
733:
727:
726:
724:
723:
717:
715:
709:
708:
706:
705:
700:
695:
690:
685:
680:
674:
672:
666:
665:
663:
662:
657:
651:
649:
643:
642:
640:
639:
638:
637:
627:
626:
625:
620:
609:
607:
598:
592:
591:
580:
579:
572:
565:
557:
549:
548:
538:
528:
518:
505:
499:978-1107039889
498:
470:
463:
434:
425:|journal=
381:
372:|journal=
325:
316:|journal=
263:
262:
260:
257:
256:
255:
247:
244:
224:
221:
215:
212:
211:
210:
207:
204:
201:
198:
195:
192:
149:
146:
138:non-persistent
134:
133:
130:
127:
124:
121:
78:
75:
26:
9:
6:
4:
3:
2:
979:
968:
965:
963:
960:
959:
957:
942:
939:
937:
934:
933:
931:
929:
925:
915:
912:
910:
907:
905:
902:
900:
897:
896:
894:
890:
884:
881:
879:
876:
874:
871:
870:
868:
866:
862:
856:
853:
851:
848:
846:
843:
841:
838:
836:
833:
831:
828:
826:
823:
821:
818:
817:
815:
813:
809:
803:
800:
798:
795:
793:
790:
788:
787:Slotted ALOHA
785:
783:
780:
779:
777:
775:
771:
768:
766:
762:
752:
751:
749:
747:
743:
737:
736:
734:
732:
728:
722:
719:
718:
716:
714:
710:
704:
701:
699:
696:
694:
691:
689:
686:
684:
681:
679:
676:
675:
673:
671:
667:
661:
658:
656:
653:
652:
650:
648:
644:
636:
633:
632:
631:
628:
624:
621:
619:
616:
615:
614:
611:
610:
608:
606:
602:
599:
597:
596:Channel-based
593:
589:
585:
578:
573:
571:
566:
564:
559:
558:
555:
542:
532:
522:
515:
509:
501:
495:
491:
487:
483:
477:
475:
466:
464:0-470-09510-5
460:
456:
451:
450:
444:
438:
430:
417:
403:on 2006-12-09
399:
392:
385:
377:
364:
350:on 2006-11-04
346:
339:
332:
330:
321:
308:
290:
283:
281:
279:
277:
275:
273:
271:
269:
264:
253:
250:
249:
243:
241:
236:
234:
230:
220:
208:
205:
202:
199:
196:
193:
190:
189:
188:
185:
181:
177:
175:
171:
167:
156:
145:
142:
139:
131:
128:
125:
122:
119:
118:
117:
114:
110:
108:
103:
99:
96:
95:Clear To Send
92:
83:
74:
72:
71:carrier sense
68:
64:
60:
56:
52:
48:
44:
40:
36:
32:
19:
824:
765:Packet-based
541:
531:
521:
508:
485:
482:Guowang Miao
448:
443:Karl, Holger
437:
416:cite journal
405:. Retrieved
398:the original
384:
363:cite journal
352:. Retrieved
345:the original
307:cite journal
296:. Retrieved
240:multicasting
237:
226:
217:
186:
182:
178:
176:algorithm).
169:
162:
135:
115:
111:
104:
100:
94:
90:
88:
58:
54:
34:
30:
29:
136:MACAW is a
49:(WSN). The
956:Categories
873:Token Ring
407:2006-12-27
354:2006-11-26
298:2007-01-18
259:References
172:(using an
878:Token bus
855:CSMA/CARP
883:MS-ALOHA
688:TD-SCDMA
526:Springer
445:(2005).
246:See also
170:back off
59:RTS-RRTS
835:CSMA/CA
802:CSMA/CD
792:R-ALOHA
721:HC-SDMA
703:MC-CDMA
698:FH-CDMA
693:DS-CDMA
683:TD-CDMA
655:MF-TDMA
623:SC-FDMA
141:slotted
678:W-CDMA
496:
461:
254:(MACA)
152:": -->
69:, use
904:VANET
899:MANET
825:MACAW
797:AX.25
782:ALOHA
660:STDMA
618:OFDMA
536:2008.
401:(PDF)
394:(PDF)
348:(PDF)
341:(PDF)
292:(PDF)
148:RRTS
67:S-MAC
35:MACAW
18:MACAW
830:CSMA
820:MACA
746:PAMA
731:PDMA
713:SDMA
670:CDMA
647:TDMA
635:WDMA
605:FDMA
586:and
546:2008
494:ISBN
459:ISBN
429:help
376:help
320:help
154:edit
941:FDD
936:TDD
909:DTN
850:HCF
845:PCF
840:DCF
630:WDM
613:FDM
455:117
958::
492:.
488:.
473:^
457:.
420::
418:}}
414:{{
367::
365:}}
361:{{
328:^
311::
309:}}
305:{{
267:^
242:.
576:e
569:t
562:v
502:.
467:.
431:)
427:(
410:.
378:)
374:(
357:.
322:)
318:(
301:.
158:]
33:(
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.