3273:
1129:
57:
336:
209:
3285:
3259:
1143:
861:, which initially start out the same. NAT in Netfilter is implemented by simply changing the reply address, and where desired, port. When packets are received, their connection tuple will also be compared against the reply address pair (and ports). Being fragment-free is also a requirement for NAT. (If need be, IPv4 packets may be refragmented by the normal, non-Netfilter, IPv4 stack.)
617:(inbound interface, for example), and manage connection tracking data. Arithmetic, bitwise and comparison operators can be used for making decisions based on that data. The virtual machine is also capable of manipulating sets of data (typically IP addresses), allowing multiple comparison operations to be replaced with a single set lookup.
723:
Each
Netfilter connection is uniquely identified by a (layer-3 protocol, source address, destination address, layer-4 protocol, layer-4 key) tuple. The layer-4 key depends on the transport protocol; for TCP/UDP it is the port numbers, for tunnels it can be their tunnel ID, but otherwise is just zero,
616:
into the Linux kernel, which is able to execute bytecode to inspect a network packet and make decisions on how that packet should be handled. The operations implemented by this virtual machine are intentionally made basic: it can get data from the packet itself, have a look at the associated metadata
620:
This is in contrast to the legacy
Xtables (iptables, etc.) code, which has protocol awareness so deeply built into the code that it has had to be replicated four times—for IPv4, IPv6, ARP, and Ethernet bridging—as the firewall engines are too protocol-specific to be used in a generic
561:
targets. (These so-called "targets" refer to
Security-Enhanced Linux markers.) Mandatory Access Control is implemented by Linux Security Modules such as SELinux. The security table is called following the call of the filter table, allowing any Discretionary Access Control (DAC) rules in the filter
446:
Each table is actually its own hook, and each table was introduced to serve a specific purpose. As far as
Netfilter is concerned, it runs a particular table in a specific order with respect to other tables. Any table can call itself and it also can execute its own rules, which enables possibilities
316:), Netfilter separates packet operations into multiple parts, described below. Each connects to the Netfilter hooks at different points to access packets. The connection tracking and NAT subsystems are more general and more powerful than the rudimentary versions within ipchains and ipfwadm.
699:
The connection state however is completely independent of any upper-level state, such as TCP's or SCTP's state. Part of the reason for this is that when merely forwarding packets, i.e. no local delivery, the TCP engine may not necessarily be invoked at all. Even
426:
comprise the legacy packet filtering portion of the
Netfilter hook system. They provide a table-based system for defining firewall rules that can filter or transform packets. The tables can be administered through the user-space tools
199:
functions with the kernel's networking stack. Those functions, usually applied to the traffic in the form of filtering and modification rules, are called for every packet that traverses the respective hook within the networking stack.
522:
Registers two hooks: Destination
Network Address Translation-based transformations ("DNAT") are applied before the filter hook, Source Network Address Translation-based transformations ("SNAT") are applied afterwards. The
512:
table to run after
Connection Tracking (see below) (but still before any other table), so that modifications can be made to the packet. This enables additional modifications by rules that follow, such as NAT or further
830:
or TCP segmentation, the helper will not necessarily recognize patterns and therefore not perform its operation. IP fragmentation is dealt with the connection tracking subsystem requiring defragmentation, though
814:
Through the use of plugin modules, connection tracking can be given knowledge of application-layer protocols and thus understand that two or more distinct connections are "related". For example, consider the
1116:
The
Netfilter project organizes an annual meeting for developers, which is used to discuss ongoing research and development efforts. The 2018 Netfilter workshop took place in Berlin, Germany, in June 2018.
720:
have, at least, a pseudo connection state. The heuristic for such protocols is often based upon a preset timeout value for inactivity, after whose expiration a
Netfilter connection is dropped.
1027:
as a prefix of their names, that can be used to perform different tasks from the userspace. These libraries are released under the GNU GPL version 2. Specifically, they are the following:
688:
One of the important features built on top of the
Netfilter framework is connection tracking. Connection tracking allows the kernel to keep track of all logical network connections or
737:
can make use of checking the connection's information such as states, statuses and more to make packet filtering rules more powerful and easier to manage. The most common states are:
297:. Both ipchains and ipfwadm alter the networking code so they can manipulate packets, as Linux kernel lacked a general packets control framework until the introduction of Netfilter.
762:
assigned to a packet that is initiating a new connection and which has been "expected"; the aforementioned mini-ALGs set up these expectations, for example, when the
823:
module is loaded, the first packet of an FTP data connection will be classified as "related" instead of "new", as it is logically part of an existing connection.
692:, and thereby relate all of the packets which may make up that connection. NAT relies on this information to translate all related packets in the same way, and
1559:
888:
is a set of user-space tools for Linux that allow system administrators to interact with the Connection Tracking entries and tables. The package includes the
443:. Notice that although both the kernel modules and userspace utilities have similar names, each of them is a different entity with different functionality.
802:
A normal example would be that the first packet the conntrack subsystem sees will be classified "new", the reply would be classified "established" and an
2835:
900:
can be used to enable high availability cluster-based stateful firewalls and collect statistics of the stateful firewall use. The command line interface
954:
Any entry in one set can be bound to another set, allowing for sophisticated matching operations. A set can only be removed (destroyed) if there are no
1451:
1430:
869:
Similar to connection tracking helpers, NAT helpers will do a packet inspection and substitute original addresses by reply addresses in the payload.
947:
rules, but of course may come with a greater memory footprint. Different storage algorithms (for the data structures in memory) are provided in
2124:
1237:
819:
protocol. A control connection is established, but whenever data is transferred, a separate connection is established to transfer it. When the
1900:
1162:
1553:
826:
The helpers only inspect one packet at a time, so if vital information for connection tracking is split across two packets, either due to
2924:
1586:
2919:
798:
a special state that can be assigned by the administrator to bypass connection tracking for a particular packet (see raw table, above).
877:
Though not being kernel modules that make use of Netfilter code directly, the Netfilter project hosts a few more noteworthy software.
286:
271:
2016:
943:, but can also contain sets of other network numbers, depending on its "type". These sets are much more lookup-efficient than bare
254:
became chairman of the coreteam. In April 2004, following a crack-down by the project on those distributing the project's software
485:
Netfilter modules not organized into tables (see below) are capable of checking for the origin to select their mode of operation.
724:
as if it were not part of the tuple. To be able to inspect the TCP port in all cases, packets will be mandatorily defragmented.
450:
Rules are organized into chains, or in other words, "chains of rules". These chains are named with predefined titles, including
168:-related operations to be implemented in the form of customized handlers. Netfilter offers various functions and operations for
3316:
2049:
3277:
1134:
973:
possible without the large performance penalties imposed by the connection tracking in such cases. By redirecting initial
327:
flow offload infrastructure was added, allowing a speedup of software flow table forwarding and hardware offload support.
985:
state, freeing up connection tracking from accounting large numbers of potentially invalid connections. This way, huge
278:). In September 2007 Patrick McHardy, who led development for past years, was elected as new chairman of the coreteam.
2656:
2424:
939:
is used to set up, maintain and inspect so called "IP sets" in the Linux kernel. An IP set usually contains a set of
803:
2371:
275:
701:
663:
module). This is necessary for the in-kernel connection tracking and NAT helper modules (which are a form of "mini-
102:
996:
proxy functionality was merged into the Netfilter, with the release of version 3.12 of the Linux kernel mainline.
499:
that can be used to filter packets before they reach more memory-demanding operations such as Connection Tracking.
3321:
2154:
2114:
1579:
196:
2416:
462:. These chain titles help describe the origin in the Netfilter stack. Packet reception, for example, falls into
3326:
2766:
290:
495:
When loaded, registers a hook that will be called before any other Netfilter hook. It provides a table called
3200:
2094:
1930:
1895:
713:
806:
error would be "related". An ICMP error packet which did not match any known connection would be "invalid".
3081:
2129:
1925:
1611:
638:
626:
1011:
can deliver packets via the userspace queueing mechanism to it, and connection tracking can interact with
2483:
1890:
1007:
is a user-space daemon to receive and log packets and event notifications from the Netfilter subsystems.
981:
target, connections are not registered within the connection tracking until they reach a validated final
848:
528:
301:
173:
48:
1285:
3311:
3182:
2996:
2042:
1572:
689:
683:
240:
3187:
2829:
2818:
2321:
2165:
664:
300:
Whereas ipchains and ipfwadm combine packet filtering and NAT (particularly three specific kinds of
2750:
2735:
2651:
2439:
2244:
1968:
1915:
1910:
83:
1015:
to exchange further information about packets or events (such as connection teardown, NAT setup).
3093:
2892:
2528:
2305:
2282:
2011:
56:
1472:
3238:
3215:
3210:
3045:
3011:
3001:
2873:
2695:
2234:
2104:
1703:
1656:
1216:
1157:
816:
767:
705:
562:
table to take effect before any MAC rules. This table provides the following built-in chains:
3289:
3192:
2035:
1885:
527:
table (or "nat") that is made available to iptables is merely a "configuration database" for
244:
3222:
2824:
2386:
2084:
1940:
1920:
1606:
1595:
1188:
835:
is not handled. In case of FTP, segmentation is deemed not to happen "near" a command like
181:
8:
3018:
2497:
2356:
2290:
1081:
allows changes to be performed to the iptables firewall rulesets; it is not based on any
110:
3172:
3006:
2592:
2492:
2429:
2351:
2346:
2134:
1713:
904:
provides a more flexible interface to the connection tracking system than the obsolete
717:
659:
module will defragment IPv4 packets before they reach Netfilter's connection tracking (
553:
Used for Mandatory Access Control (MAC) networking rules, such as those enabled by the
281:
Prior to iptables, the predominant software packages for creating Linux firewalls were
259:
180:, which provide the functionality required for directing packets through a network and
157:
16:
Packet alteration framework for Linux and the umbrella project for software of the same
3143:
2791:
2761:
2756:
2607:
2262:
2224:
1870:
1621:
1616:
1200:
1168:
1367:
1229:
2897:
2459:
2180:
2170:
2079:
1935:
1698:
1626:
1036:
allows to perform userspace packet queueing in conjunction with iptables; based on
827:
670:
The IPv6 defragmenter is not a module in its own right, but is integrated into the
650:
177:
165:
126:
90:
1546:
1525:
3133:
2801:
2582:
1721:
613:
255:
1047:
allows manipulation of connection tracking entries from the userspace; based on
3163:
3068:
2979:
2856:
2851:
2846:
2841:
2624:
2449:
2444:
2089:
1790:
1206:
787:
783:
630:
339:
Flow of network packets through Netfilter with legacy iptables packet filtering
243:(GPL) license, and on 26 August 1999 it was merged into version 2.3.15 of the
3305:
3098:
2914:
2720:
2710:
2469:
2341:
2219:
1850:
1845:
1795:
1211:
634:
216:
192:
169:
115:
1860:
928:
does not make use of Netfilter hooks for instance, but actually provides an
667:") that only work reliably on entire packets, not necessarily on fragments.
3263:
2984:
2902:
2796:
2740:
2099:
2058:
1994:
1855:
1281:
1148:
251:
161:
2989:
2882:
2464:
2361:
832:
1535:
470:
represents locally delivered data, and forwarded traffic falls into the
335:
3076:
3038:
2943:
2931:
2861:
2771:
2257:
2160:
2119:
1905:
1785:
1741:
1493:
1183:
1069:
allows operations on queues, connection tracking and logs; part of the
940:
839:
with standard segment sizes, so is not dealt with in Netfilter either.
294:
267:
208:
3051:
2938:
2907:
2612:
2401:
2272:
2229:
1989:
1973:
1751:
1693:
1661:
970:
932:
module to match and do minimal modifications (set/clear) to IP sets.
1564:
373:
355:
3056:
2877:
2866:
2786:
2730:
2725:
2671:
2619:
2508:
2434:
1960:
1950:
1818:
1780:
1676:
1671:
1406:
1342:
1318:
1298:
1178:
1174:
584:
405:
391:
364:
346:
282:
224:
1540:
1058:
allows collection of log messages generated by iptables; based on
727:
Netfilter connections can be manipulated with the user-space tool
3138:
3123:
3033:
3023:
2963:
2887:
2781:
2705:
2646:
2560:
2523:
2454:
2396:
2391:
2295:
2252:
1945:
1823:
1736:
1688:
1683:
1651:
1410:
1346:
1323:
1303:
1259:"netfilter/iptables project homepage - The netfilter.org project"
1194:
1083:
263:
188:
131:
382:
3128:
3113:
3103:
2958:
2953:
2715:
2666:
2639:
2602:
2572:
2539:
2518:
2267:
2214:
2109:
2027:
1800:
1726:
1530:
1384:
2948:
2811:
2745:
2700:
2661:
2629:
2597:
2555:
2550:
2513:
2381:
2376:
2336:
2331:
1837:
1636:
1554:
Netfilter and Iptables — Stateful Firewalling for Linux
1258:
709:
570:(for altering locally-generated packets before routing), and
95:
1311:
1291:
184:
packets from reaching sensitive locations within a network.
3028:
2806:
2634:
2565:
2209:
1746:
1731:
589:
nftables is the new packet-filtering portion of Netfilter.
324:
320:
637:, and more efficient execution, storage, and incremental,
531:
mappings only, and not intended for filtering of any kind.
3258:
3108:
3086:
1765:
1518:
1142:
1088:
574:(for altering packets being routed through the computer).
223:
in 1998; he had also authored the project's predecessor,
696:
can use this information to act as a stateful firewall.
544:
table, used for general-purpose filtering (firewalling).
212:
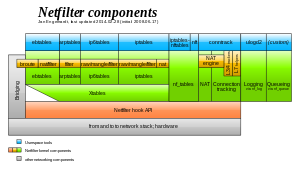
Relation of (some of) the different Netfilter components
142:
274:
Germany, which refused to follow the GPL's terms (see
916:
Unlike other extensions such as Connection Tracking,
1124:
474:chain. Locally generated output passes through the
1203:, another low-level component of the network stack
1023:Netfilter also provides a set of libraries having
289:in Linux kernel 2.0.x, which in turn was based on
3303:
1404:
1340:
566:(for packets coming into the computer itself),
1336:
1334:
1286:netfilter archeology: 18 years from 2.3 to 4.x
1235:
842:
809:
235:) in 1999. The software they produced (called
3067:
2043:
1901:Microsoft Forefront Threat Management Gateway
1580:
872:
330:
951:for the user to select an optimum solution.
1365:
1331:
989:floods can be handled in an effective way.
593:is the new userspace utility that replaces
191:inside the Linux kernel, allowing specific
3171:
2050:
2036:
1587:
1573:
1407:"netfilter: implement netfilter SYN proxy"
422:(the underscore is part of the name), and
247:and thus was in the 2.4.0 stable version.
55:
644:
478:chain, and packets to be sent out are in
447:for additional processing and iteration.
3278:Free and open-source software portal
2836:Earliest eligible virtual deadline first
2017:List of router or firewall distributions
1368:"Netfilter's Connection Tracking System"
334:
207:
1541:Home of the Netfilter Workshop websites
1103:allows operations on IP sets; based on
924:than it is to the core Netfilter code.
625:are simplification of the Linux kernel
3304:
1111:
1018:
892:daemon and the command line interface
754:part of an already-existing connection
677:
227:. As the project grew, he founded the
2072:
2031:
1594:
1568:
1452:"netfilter: add IPv6 SYNPROXY target"
1431:"netfilter: add SYNPROXY core/target"
1197:, an API used by Netfilter extensions
958:rules or other sets referring to it.
612:nftables kernel engine adds a simple
1496:. workshop.netfilter.org. 2018-09-26
1277:
1275:
1236:Linus Torvalds (15 September 2024).
1135:Free and open-source software portal
1366:Neira Ayuso, Pablo (14 June 2006).
13:
880:
786:, e.g. it would not adhere to the
262:without complying with the GPL, a
14:
3338:
1510:
1272:
746:trying to create a new connection
702:connectionless-mode transmissions
621:manner. The main advantages over
3284:
3283:
3271:
3257:
2125:Supported computer architectures
2057:
1141:
1127:
266:court granted Welte an historic
2155:The Linux Programming Interface
1486:
1465:
1444:
1423:
969:target makes handling of large
1560:Network overview by Rami Rosen
1473:"Netfilter Library (libnl-nf)"
1405:Patrick McHardy (2013-08-07).
1398:
1377:
1359:
1341:Jonathan Corbet (2013-08-20).
1251:
864:
187:Netfilter represents a set of
1:
3317:Free network-related software
1931:Trend Micro Internet Security
1896:McAfee Personal Firewall Plus
1319:"Flow offload infrastructure"
1299:"Flow offload infrastructure"
1223:
853:Each connection has a set of
1926:Symantec Endpoint Protection
1612:Context-based access control
961:
641:changes of filtering rules.
7:
1891:Kaspersky Internet Security
1475:. infradead.org. 2013-04-02
1163:Geniatech v. McHardy (2018)
1120:
935:The user-space tool called
849:Network address translation
843:Network address translation
810:Connection tracking helpers
782:the packet was found to be
578:
525:network address translation
399:
174:network address translation
10:
3343:
2997:High-performance computing
2819:Process and I/O schedulers
1091:is internally used by the
873:Further Netfilter projects
846:
684:Stateful packet inspection
681:
648:
582:
403:
331:Userspace utility programs
285:in Linux kernel 2.2.x and
241:GNU General Public License
221:netfilter/iptables project
203:
3251:
3231:
3162:
2972:
2830:Completely Fair Scheduler
2688:
2581:
2491:
2482:
2415:
2320:
2313:
2304:
2281:
2243:
2202:
2195:
2143:
2095:Tanenbaum–Torvalds debate
2065:
2007:
1982:
1959:
1878:
1869:
1836:
1811:
1773:
1764:
1712:
1644:
1635:
1602:
1547:Writing Netfilter Modules
1494:"14th Netfilter Workshop"
410:The kernel modules named
137:
125:
101:
89:
79:
75:
47:
43:
24:
2751:Kernel same-page merging
1969:Comodo Internet Security
1916:Norton Personal Firewall
1911:Norton Internet Security
1526:conntrack-tools homepage
1454:. kernel.org. 2013-08-27
1433:. kernel.org. 2013-08-27
1343:"The return of nftables"
999:
911:
3094:OS-level virtualization
2012:Comparison of firewalls
896:. The userspace daemon
3322:Free security software
3239:List of Linux adopters
2181:Linux User Group (LUG)
1704:Uncomplicated Firewall
1217:Uncomplicated Firewall
1158:Berkeley Packet Filter
1043:libnetfilter_conntrack
906:/proc/net/nf_conntrack
645:Packet defragmentation
340:
213:
30:; 25 years ago
3327:Linux kernel features
1886:Check Point Integrity
1387:. ipset.netfilter.org
1177:, the predecessor to
508:Registers a hook and
338:
245:Linux kernel mainline
211:
62:; 14 days ago
2825:Brain Fuck Scheduler
2085:Linux Mark Institute
1941:Windows Live OneCare
1921:Outpost Firewall Pro
1607:Application firewall
1189:Linux Virtual Server
992:On 3 November 2013,
276:GPL-related disputes
239:hereafter) uses the
164:that allows various
3019:Real-time computing
2291:Linux Standard Base
1556:" (11 October 2001)
1171:(IPVS, part of LVS)
1112:Netfilter workshops
1019:Userspace libraries
920:is more related to
718:tunneling protocols
678:Connection tracking
229:Netfilter Core Team
111:Linux kernel module
60:/ 15 September 2024
28:26 August 1999
21:
3007:Compute Node Linux
2593:C standard library
1032:libnetfilter_queue
855:original addresses
341:
214:
19:
3312:Firewall software
3299:
3298:
3247:
3246:
3158:
3157:
3154:
3153:
2792:Network scheduler
2684:
2683:
2680:
2679:
2478:
2477:
2225:Linux kernel oops
2191:
2190:
2171:Linux conferences
2025:
2024:
2003:
2002:
1832:
1831:
1760:
1759:
1622:Stateful firewall
1617:Personal firewall
1596:Firewall software
1288:, 5 December 2017
1201:Network scheduler
1169:IP Virtual Server
1087:library, and its
1065:libnl-3-netfilter
672:nf_conntrack_ipv6
661:nf_conntrack_ipv4
151:
150:
67:15 September 2024
3334:
3287:
3286:
3276:
3275:
3274:
3264:Linux portal
3262:
3261:
3169:
3168:
3065:
3064:
2874:Security Modules
2489:
2488:
2318:
2317:
2311:
2310:
2200:
2199:
2080:Linux Foundation
2070:
2069:
2052:
2045:
2038:
2029:
2028:
1936:Windows Firewall
1876:
1875:
1771:
1770:
1642:
1641:
1627:Virtual firewall
1589:
1582:
1575:
1566:
1565:
1549:" (e-book; 2009)
1522:
1521:
1519:Official website
1505:
1504:
1502:
1501:
1490:
1484:
1483:
1481:
1480:
1469:
1463:
1462:
1460:
1459:
1448:
1442:
1441:
1439:
1438:
1427:
1421:
1420:
1418:
1417:
1402:
1396:
1395:
1393:
1392:
1381:
1375:
1374:
1372:
1363:
1357:
1356:
1354:
1353:
1338:
1329:
1328:
1315:
1309:
1308:
1295:
1289:
1279:
1270:
1269:
1267:
1266:
1255:
1249:
1248:
1246:
1244:
1233:
1151:
1146:
1145:
1137:
1132:
1131:
1130:
1106:
1100:
1094:
1086:
1078:
1072:
1066:
1061:
1055:
1054:libnetfilter_log
1050:
1044:
1039:
1033:
1026:
1014:
1010:
1006:
995:
988:
984:
980:
977:requests to the
976:
968:
957:
950:
946:
938:
931:
927:
923:
919:
907:
903:
899:
895:
891:
887:
838:
833:TCP segmentation
828:IP fragmentation
822:
821:nf_conntrack_ftp
795:
779:
773:
765:
764:nf_conntrack_ftp
759:
751:
743:
736:
730:
695:
673:
662:
658:
651:IP fragmentation
631:code duplication
624:
608:
604:
600:
596:
592:
573:
569:
565:
560:
556:
549:
536:
518:
504:
491:
481:
477:
473:
469:
465:
461:
457:
453:
442:
438:
434:
430:
425:
421:
417:
413:
395:
394:
386:
385:
377:
376:
368:
367:
359:
358:
350:
349:
178:port translation
170:packet filtering
160:provided by the
147:
144:
91:Operating system
70:
68:
63:
59:
38:
36:
31:
22:
18:
3342:
3341:
3337:
3336:
3335:
3333:
3332:
3331:
3302:
3301:
3300:
3295:
3272:
3270:
3256:
3243:
3227:
3174:
3150:
3134:User-mode Linux
3063:
2968:
2676:
2584:
2577:
2496:
2474:
2411:
2323:
2300:
2277:
2239:
2187:
2139:
2130:Version history
2061:
2056:
2026:
2021:
1999:
1978:
1955:
1865:
1861:VirusBarrier X6
1828:
1807:
1756:
1722:Endian Firewall
1708:
1631:
1598:
1593:
1517:
1516:
1513:
1508:
1499:
1497:
1492:
1491:
1487:
1478:
1476:
1471:
1470:
1466:
1457:
1455:
1450:
1449:
1445:
1436:
1434:
1429:
1428:
1424:
1415:
1413:
1403:
1399:
1390:
1388:
1383:
1382:
1378:
1370:
1364:
1360:
1351:
1349:
1339:
1332:
1317:
1316:
1312:
1297:
1296:
1292:
1280:
1273:
1264:
1262:
1261:. netfilter.org
1257:
1256:
1252:
1242:
1240:
1234:
1230:
1226:
1221:
1147:
1140:
1133:
1128:
1126:
1123:
1114:
1104:
1098:
1092:
1082:
1076:
1070:
1064:
1059:
1053:
1048:
1042:
1037:
1031:
1024:
1021:
1012:
1008:
1004:
1002:
993:
986:
982:
978:
974:
966:
964:
955:
948:
944:
936:
929:
925:
921:
917:
914:
905:
901:
897:
893:
889:
886:conntrack-tools
885:
883:
881:conntrack-tools
875:
867:
859:reply addresses
851:
845:
836:
820:
812:
793:
777:
771:
766:module sees an
763:
757:
749:
741:
734:
728:
693:
686:
680:
671:
660:
656:
653:
647:
635:error reporting
629:, reduction of
622:
614:virtual machine
606:
602:
598:
594:
590:
587:
581:
571:
567:
563:
558:
554:
548:security_filter
547:
534:
516:
502:
489:
479:
475:
471:
467:
463:
459:
455:
451:
440:
436:
432:
428:
423:
419:
415:
411:
408:
402:
390:
389:
381:
380:
372:
371:
363:
362:
354:
353:
345:
344:
333:
310:port forwarding
250:In August 2003
206:
141:
121:
71:
66:
64:
61:
34:
32:
29:
25:Initial release
17:
12:
11:
5:
3340:
3330:
3329:
3324:
3319:
3314:
3297:
3296:
3294:
3293:
3281:
3267:
3252:
3249:
3248:
3245:
3244:
3242:
3241:
3235:
3233:
3229:
3228:
3226:
3225:
3220:
3219:
3218:
3213:
3205:
3204:
3203:
3195:
3190:
3185:
3179:
3177:
3166:
3160:
3159:
3156:
3155:
3152:
3151:
3149:
3148:
3147:
3146:
3141:
3136:
3131:
3126:
3118:
3117:
3116:
3111:
3106:
3101:
3091:
3090:
3089:
3084:
3073:
3071:
3069:Virtualization
3062:
3061:
3060:
3059:
3054:
3043:
3042:
3041:
3036:
3031:
3026:
3016:
3015:
3014:
3009:
3004:
2994:
2993:
2992:
2987:
2976:
2974:
2970:
2969:
2967:
2966:
2961:
2956:
2951:
2946:
2941:
2935:
2934:
2929:
2928:
2927:
2922:
2915:Device drivers
2911:
2910:
2905:
2900:
2895:
2890:
2885:
2880:
2870:
2869:
2864:
2859:
2857:SCHED_DEADLINE
2854:
2852:O(1) scheduler
2849:
2847:O(n) scheduler
2844:
2842:Noop scheduler
2839:
2833:
2827:
2822:
2815:
2814:
2809:
2804:
2799:
2794:
2789:
2784:
2779:
2774:
2769:
2764:
2759:
2754:
2748:
2743:
2738:
2733:
2728:
2723:
2718:
2713:
2708:
2703:
2698:
2696:Kernel modules
2692:
2690:
2686:
2685:
2682:
2681:
2678:
2677:
2675:
2674:
2669:
2664:
2659:
2654:
2649:
2644:
2643:
2642:
2637:
2632:
2627:
2622:
2617:
2616:
2615:
2605:
2600:
2589:
2587:
2579:
2578:
2576:
2575:
2570:
2569:
2568:
2558:
2553:
2548:
2545:
2542:
2537:
2534:
2531:
2526:
2521:
2516:
2511:
2506:
2502:
2500:
2486:
2480:
2479:
2476:
2475:
2473:
2472:
2467:
2462:
2457:
2452:
2450:Memory barrier
2447:
2442:
2437:
2432:
2427:
2421:
2419:
2413:
2412:
2410:
2409:
2408:
2407:
2404:
2399:
2394:
2389:
2384:
2379:
2369:
2368:
2367:
2364:
2359:
2354:
2349:
2344:
2339:
2328:
2326:
2315:
2308:
2302:
2301:
2299:
2298:
2293:
2287:
2285:
2279:
2278:
2276:
2275:
2270:
2265:
2260:
2255:
2249:
2247:
2241:
2240:
2238:
2237:
2232:
2227:
2222:
2217:
2212:
2206:
2204:
2197:
2193:
2192:
2189:
2188:
2186:
2185:
2184:
2183:
2175:
2174:
2173:
2168:
2163:
2158:
2147:
2145:
2141:
2140:
2138:
2137:
2132:
2127:
2122:
2117:
2112:
2107:
2102:
2097:
2092:
2087:
2082:
2076:
2074:
2067:
2063:
2062:
2055:
2054:
2047:
2040:
2032:
2023:
2022:
2020:
2019:
2014:
2008:
2005:
2004:
2001:
2000:
1998:
1997:
1992:
1986:
1984:
1980:
1979:
1977:
1976:
1971:
1965:
1963:
1957:
1956:
1954:
1953:
1948:
1943:
1938:
1933:
1928:
1923:
1918:
1913:
1908:
1903:
1898:
1893:
1888:
1882:
1880:
1873:
1867:
1866:
1864:
1863:
1858:
1853:
1848:
1842:
1840:
1834:
1833:
1830:
1829:
1827:
1826:
1821:
1815:
1813:
1809:
1808:
1806:
1805:
1804:
1803:
1793:
1788:
1783:
1777:
1775:
1768:
1762:
1761:
1758:
1757:
1755:
1754:
1749:
1744:
1739:
1734:
1729:
1724:
1718:
1716:
1710:
1709:
1707:
1706:
1701:
1696:
1691:
1686:
1681:
1680:
1679:
1674:
1664:
1659:
1654:
1648:
1646:
1639:
1633:
1632:
1630:
1629:
1624:
1619:
1614:
1609:
1603:
1600:
1599:
1592:
1591:
1584:
1577:
1569:
1563:
1562:
1557:
1550:
1543:
1538:
1536:ulogd homepage
1533:
1531:ipset homepage
1528:
1523:
1512:
1511:External links
1509:
1507:
1506:
1485:
1464:
1443:
1422:
1397:
1376:
1358:
1330:
1310:
1290:
1271:
1250:
1227:
1225:
1222:
1220:
1219:
1214:
1209:
1207:NPF (firewall)
1204:
1198:
1192:
1186:
1181:
1172:
1166:
1160:
1154:
1153:
1152:
1138:
1122:
1119:
1113:
1110:
1109:
1108:
1101:
1096:
1079:
1074:
1067:
1062:
1056:
1051:
1045:
1040:
1034:
1020:
1017:
1001:
998:
963:
960:
913:
910:
882:
879:
874:
871:
866:
863:
847:Main article:
844:
841:
811:
808:
800:
799:
796:
791:
780:
775:
760:
755:
752:
747:
744:
679:
676:
657:nf_defrag_ipv4
646:
643:
583:Main article:
580:
577:
576:
575:
551:
545:
540:Registers the
538:
535:iptable_filter
532:
520:
514:
506:
503:iptable_mangle
500:
493:
404:Main article:
401:
398:
397:
396:
387:
378:
369:
360:
351:
332:
329:
205:
202:
193:kernel modules
149:
148:
139:
135:
134:
129:
123:
122:
120:
119:
113:
107:
105:
99:
98:
93:
87:
86:
81:
77:
76:
73:
72:
53:
51:
49:Stable release
45:
44:
41:
40:
39:(Linux 2.3.15)
26:
15:
9:
6:
4:
3:
2:
3339:
3328:
3325:
3323:
3320:
3318:
3315:
3313:
3310:
3309:
3307:
3292:
3291:
3282:
3280:
3279:
3268:
3266:
3265:
3260:
3254:
3253:
3250:
3240:
3237:
3236:
3234:
3230:
3224:
3221:
3217:
3214:
3212:
3209:
3208:
3206:
3202:
3199:
3198:
3197:Thin client:
3196:
3194:
3191:
3189:
3186:
3184:
3181:
3180:
3178:
3176:
3170:
3167:
3165:
3161:
3145:
3142:
3140:
3137:
3135:
3132:
3130:
3127:
3125:
3122:
3121:
3119:
3115:
3112:
3110:
3107:
3105:
3102:
3100:
3099:Linux-VServer
3097:
3096:
3095:
3092:
3088:
3085:
3083:
3080:
3079:
3078:
3075:
3074:
3072:
3070:
3066:
3058:
3055:
3053:
3050:
3049:
3047:
3044:
3040:
3037:
3035:
3032:
3030:
3027:
3025:
3022:
3021:
3020:
3017:
3013:
3010:
3008:
3005:
3003:
3000:
2999:
2998:
2995:
2991:
2988:
2986:
2983:
2982:
2981:
2978:
2977:
2975:
2971:
2965:
2962:
2960:
2957:
2955:
2952:
2950:
2947:
2945:
2942:
2940:
2937:
2936:
2933:
2930:
2926:
2923:
2921:
2918:
2917:
2916:
2913:
2912:
2909:
2906:
2904:
2901:
2899:
2896:
2894:
2891:
2889:
2886:
2884:
2881:
2879:
2875:
2872:
2871:
2868:
2865:
2863:
2860:
2858:
2855:
2853:
2850:
2848:
2845:
2843:
2840:
2837:
2834:
2831:
2828:
2826:
2823:
2820:
2817:
2816:
2813:
2810:
2808:
2805:
2803:
2800:
2798:
2795:
2793:
2790:
2788:
2785:
2783:
2780:
2778:
2775:
2773:
2770:
2768:
2765:
2763:
2760:
2758:
2755:
2752:
2749:
2747:
2744:
2742:
2739:
2737:
2734:
2732:
2729:
2727:
2724:
2722:
2721:Device mapper
2719:
2717:
2714:
2712:
2709:
2707:
2704:
2702:
2699:
2697:
2694:
2693:
2691:
2687:
2673:
2670:
2668:
2665:
2663:
2660:
2658:
2655:
2653:
2650:
2648:
2645:
2641:
2638:
2636:
2633:
2631:
2628:
2626:
2623:
2621:
2618:
2614:
2611:
2610:
2609:
2606:
2604:
2601:
2599:
2596:
2595:
2594:
2591:
2590:
2588:
2586:
2580:
2574:
2571:
2567:
2564:
2563:
2562:
2559:
2557:
2554:
2552:
2549:
2546:
2543:
2541:
2538:
2535:
2532:
2530:
2527:
2525:
2522:
2520:
2517:
2515:
2512:
2510:
2507:
2504:
2503:
2501:
2499:
2494:
2490:
2487:
2485:
2481:
2471:
2468:
2466:
2463:
2461:
2458:
2456:
2453:
2451:
2448:
2446:
2443:
2441:
2438:
2436:
2433:
2431:
2428:
2426:
2423:
2422:
2420:
2418:
2414:
2405:
2403:
2400:
2398:
2395:
2393:
2390:
2388:
2385:
2383:
2380:
2378:
2375:
2374:
2373:
2370:
2365:
2363:
2360:
2358:
2355:
2353:
2350:
2348:
2345:
2343:
2340:
2338:
2335:
2334:
2333:
2330:
2329:
2327:
2325:
2319:
2316:
2312:
2309:
2307:
2303:
2297:
2294:
2292:
2289:
2288:
2286:
2284:
2280:
2274:
2271:
2269:
2266:
2264:
2261:
2259:
2256:
2254:
2251:
2250:
2248:
2246:
2242:
2236:
2233:
2231:
2228:
2226:
2223:
2221:
2218:
2216:
2213:
2211:
2208:
2207:
2205:
2201:
2198:
2194:
2182:
2179:
2178:
2176:
2172:
2169:
2167:
2164:
2162:
2159:
2157:
2156:
2152:
2151:
2149:
2148:
2146:
2142:
2136:
2133:
2131:
2128:
2126:
2123:
2121:
2118:
2116:
2113:
2111:
2108:
2106:
2103:
2101:
2098:
2096:
2093:
2091:
2088:
2086:
2083:
2081:
2078:
2077:
2075:
2071:
2068:
2064:
2060:
2053:
2048:
2046:
2041:
2039:
2034:
2033:
2030:
2018:
2015:
2013:
2010:
2009:
2006:
1996:
1993:
1991:
1988:
1987:
1985:
1981:
1975:
1972:
1970:
1967:
1966:
1964:
1962:
1958:
1952:
1949:
1947:
1944:
1942:
1939:
1937:
1934:
1932:
1929:
1927:
1924:
1922:
1919:
1917:
1914:
1912:
1909:
1907:
1904:
1902:
1899:
1897:
1894:
1892:
1889:
1887:
1884:
1883:
1881:
1877:
1874:
1872:
1868:
1862:
1859:
1857:
1854:
1852:
1851:NetBarrier X4
1849:
1847:
1846:Little Snitch
1844:
1843:
1841:
1839:
1835:
1825:
1822:
1820:
1817:
1816:
1814:
1810:
1802:
1799:
1798:
1797:
1794:
1792:
1789:
1787:
1784:
1782:
1779:
1778:
1776:
1772:
1769:
1767:
1763:
1753:
1750:
1748:
1745:
1743:
1740:
1738:
1735:
1733:
1730:
1728:
1725:
1723:
1720:
1719:
1717:
1715:
1711:
1705:
1702:
1700:
1697:
1695:
1692:
1690:
1687:
1685:
1682:
1678:
1675:
1673:
1670:
1669:
1668:
1665:
1663:
1660:
1658:
1655:
1653:
1650:
1649:
1647:
1643:
1640:
1638:
1634:
1628:
1625:
1623:
1620:
1618:
1615:
1613:
1610:
1608:
1605:
1604:
1601:
1597:
1590:
1585:
1583:
1578:
1576:
1571:
1570:
1567:
1561:
1558:
1555:
1551:
1548:
1544:
1542:
1539:
1537:
1534:
1532:
1529:
1527:
1524:
1520:
1515:
1514:
1495:
1489:
1474:
1468:
1453:
1447:
1432:
1426:
1412:
1408:
1401:
1386:
1380:
1369:
1362:
1348:
1344:
1337:
1335:
1326:
1325:
1320:
1314:
1306:
1305:
1300:
1294:
1287:
1283:
1278:
1276:
1260:
1254:
1239:
1232:
1228:
1218:
1215:
1213:
1212:PF (firewall)
1210:
1208:
1205:
1202:
1199:
1196:
1193:
1190:
1187:
1185:
1182:
1180:
1176:
1173:
1170:
1167:
1164:
1161:
1159:
1156:
1155:
1150:
1144:
1139:
1136:
1125:
1118:
1102:
1097:
1090:
1085:
1080:
1075:
1068:
1063:
1057:
1052:
1046:
1041:
1035:
1030:
1029:
1028:
1016:
997:
990:
972:
959:
952:
942:
933:
909:
878:
870:
862:
860:
856:
850:
840:
834:
829:
824:
818:
807:
805:
797:
792:
789:
785:
781:
776:
769:
761:
756:
753:
748:
745:
740:
739:
738:
732:
725:
721:
719:
715:
711:
707:
703:
697:
691:
685:
675:
668:
666:
652:
642:
640:
636:
632:
628:
618:
615:
610:
586:
552:
546:
543:
539:
533:
530:
526:
521:
515:
511:
507:
501:
498:
494:
488:
487:
486:
483:
448:
444:
407:
393:
388:
384:
379:
375:
370:
366:
361:
357:
352:
348:
343:
342:
337:
328:
326:
322:
317:
315:
311:
307:
303:
298:
296:
292:
288:
284:
279:
277:
273:
269:
265:
261:
257:
253:
248:
246:
242:
238:
234:
230:
226:
222:
218:
217:Rusty Russell
210:
201:
198:
194:
190:
185:
183:
179:
175:
171:
167:
163:
159:
155:
146:
140:
136:
133:
130:
128:
124:
117:
116:Packet filter
114:
112:
109:
108:
106:
104:
100:
97:
94:
92:
88:
85:
82:
78:
74:
58:
52:
50:
46:
42:
27:
23:
3288:
3269:
3255:
2985:Linux kernel
2903:Tomoyo Linux
2776:
2498:File systems
2153:
2105:SCO disputes
2066:Organization
2059:Linux kernel
1995:PeerGuardian
1856:PeerGuardian
1666:
1498:. Retrieved
1488:
1477:. Retrieved
1467:
1456:. Retrieved
1446:
1435:. Retrieved
1425:
1414:. Retrieved
1400:
1389:. Retrieved
1379:
1361:
1350:. Retrieved
1322:
1313:
1302:
1293:
1282:Harald Welte
1263:. Retrieved
1253:
1243:15 September
1241:. Retrieved
1238:"Linux 6.11"
1231:
1149:Linux portal
1115:
1060:libnfnetlink
1049:libnfnetlink
1038:libnfnetlink
1025:libnetfilter
1022:
1003:
991:
965:
953:
941:IP addresses
934:
915:
884:
876:
868:
858:
854:
852:
825:
813:
801:
733:
726:
722:
698:
687:
669:
654:
619:
611:
588:
541:
524:
509:
496:
484:
466:, while the
449:
445:
409:
374:arptables(8)
356:ip6tables(8)
318:
313:
309:
306:masquerading
305:
299:
280:
252:Harald Welte
249:
236:
232:
228:
220:
219:started the
215:
195:to register
186:
162:Linux kernel
153:
152:
132:GNU GPL
2990:Linux-libre
2883:Exec Shield
2762:Framebuffer
2465:Video4Linux
2322:System Call
2150:Developers
2090:Linus's law
1983:Open-source
1657:Firestarter
865:NAT helpers
750:ESTABLISHED
633:, improved
559:CONNSECMARK
517:iptable_nat
490:iptable_raw
480:POSTROUTING
392:nftables(8)
365:ebtables(8)
347:iptables(8)
314:redirection
231:(or simply
182:prohibiting
3306:Categories
3077:Hypervisor
3039:PREEMPT_RT
2944:KernelCare
2932:Raw device
2862:SCHED_FIFO
2772:KMS driver
2689:Components
2544:securityfs
2430:Crypto API
2372:Linux-only
2258:System.map
2161:kernel.org
2120:menuconfig
2115:GNU GPL v2
1906:Norton 360
1879:Commercial
1786:ipfirewall
1742:SmoothWall
1500:2018-09-26
1479:2013-12-28
1458:2013-11-05
1437:2013-11-05
1416:2013-11-05
1391:2014-07-04
1352:2013-10-22
1265:2014-07-04
1224:References
971:SYN floods
898:conntrackd
890:conntrackd
716:and other
712:(AH/ESP),
682:See also:
649:See also:
513:filtering.
464:PREROUTING
420:arp_tables
416:ip6_tables
268:injunction
166:networking
80:Written in
54:6.11
35:1999-08-26
3216:LYME-LYCE
2939:initramfs
2908:Linux PAM
2777:Netfilter
2647:libcgroup
2613:libhybris
2585:libraries
2533:hugetlbfs
2484:Userspace
2417:In-kernel
2402:readahead
2324:Interface
2273:initramfs
2230:SystemTap
2203:Debugging
2196:Technical
2135:Criticism
1990:PeerBlock
1974:ZoneAlarm
1752:Zeroshell
1694:Shorewall
1667:Netfilter
1662:firewalld
1385:"IP sets"
1095:utilities
1009:ip_tables
962:SYN proxy
902:conntrack
894:conntrack
794:UNTRACKED
788:TCP state
774:" command
729:conntrack
603:arptables
599:ip6tables
437:arptables
433:ip6tables
412:ip_tables
304:, called
237:netfilter
158:framework
154:Netfilter
143:netfilter
118:/firewall
20:Netfilter
3290:Category
3232:Adopters
3207:Server:
3188:Embedded
3164:Adoption
3057:PSXLinux
2980:Mainline
2973:Variants
2925:graphics
2878:AppArmor
2867:SCHED_RR
2787:nftables
2731:dm-crypt
2726:dm-cache
2672:liburing
2662:libevdev
2620:dietlibc
2509:configfs
2435:io uring
1961:Freemium
1951:WinRoute
1819:OPNsense
1781:IPFilter
1677:nftables
1672:iptables
1179:iptables
1175:ipchains
1121:See also
1099:libipset
1093:iptables
979:SYNPROXY
967:SYNPROXY
956:iptables
945:iptables
930:iptables
922:iptables
735:iptables
704:such as
694:iptables
690:sessions
674:module.
623:iptables
607:ebtables
595:iptables
585:nftables
579:nftables
441:ebtables
429:iptables
424:ebtables
406:iptables
400:iptables
383:ipset(8)
319:In 2017
283:ipchains
270:against
256:embedded
233:coreteam
225:ipchains
197:callback
3223:Devices
3183:Desktop
3144:coLinux
3139:MkLinux
3124:L4Linux
3052:μClinux
3034:Xenomai
3024:RTLinux
2964:Ksplice
2893:SELinux
2888:seccomp
2838:(EEVDF)
2782:Netlink
2711:Console
2706:cgroups
2657:libalsa
2583:Wrapper
2561:systemd
2524:debugfs
2493:Daemons
2455:New API
2397:inotify
2392:dnotify
2296:x32 ABI
2253:vmlinux
2245:Startup
2144:Support
1946:WinGate
1871:Windows
1824:pfSense
1812:Distros
1737:OpenWrt
1714:Distros
1689:Privoxy
1684:MoBlock
1652:FireHOL
1411:LWN.net
1347:LWN.net
1324:LWN.net
1304:LWN.net
1195:Netlink
1165:lawsuit
1084:netlink
1077:libiptc
1073:project
790:diagram
784:invalid
778:INVALID
758:RELATED
572:FORWARD
555:SECMARK
482:chain.
472:FORWARD
460:FORWARD
287:ipfwadm
272:Sitecom
260:routers
204:History
138:Website
127:License
65: (
33: (
3193:Gaming
3175:of use
3129:ELinOS
3120:Other
3114:OpenVZ
3104:Lguest
3048:-less
2959:kpatch
2954:kGraft
2920:802.11
2716:bcache
2667:libusb
2652:libdrm
2640:Newlib
2625:EGLIBC
2608:Bionic
2603:uClibc
2573:Kmscon
2547:sockfs
2540:procfs
2536:pipefs
2519:devpts
2445:kernfs
2387:splice
2342:select
2314:Kernel
2268:initrd
2263:dracut
2215:ftrace
2177:Users
2110:Linaro
2073:Kernel
1801:pfsync
1727:IPFire
1105:libmnl
639:atomic
568:OUTPUT
550:module
542:filter
537:module
519:module
510:mangle
505:module
492:module
476:OUTPUT
456:OUTPUT
439:, and
312:, and
264:German
176:, and
3173:Range
3012:SLURM
2949:kexec
2898:Smack
2832:(CFS)
2812:zswap
2753:(KSM)
2746:evdev
2701:BlueZ
2630:klibc
2598:glibc
2556:tmpfs
2551:sysfs
2514:devfs
2505:bpffs
2382:epoll
2377:futex
2357:close
2337:ioctl
2332:POSIX
2220:kdump
1838:macOS
1699:Squid
1637:Linux
1371:(PDF)
1191:(LVS)
1071:libnl
1013:ulogd
1005:ulogd
1000:ulogd
949:ipset
937:ipset
926:ipset
918:ipset
912:ipset
710:IPsec
564:INPUT
468:INPUT
452:INPUT
189:hooks
156:is a
96:Linux
3211:LAMP
3201:LTSP
3029:RTAI
2807:zram
2802:SLUB
2797:perf
2741:EDAC
2635:musl
2566:udev
2529:FUSE
2425:ALSA
2362:sync
2352:read
2347:open
2306:APIs
2283:ABIs
2210:CRIU
2166:LKML
1774:Apps
1747:VyOS
1732:LEDE
1645:Apps
1245:2024
1184:ipfw
857:and
837:PASV
804:ICMP
772:PASV
665:ALGs
655:The
605:and
557:and
458:and
325:IPv6
323:and
321:IPv4
295:ipfw
145:.org
103:Type
3109:LXC
3087:Xen
3082:KVM
3046:MMU
3002:INK
2767:LVM
2757:LIO
2736:DRM
2470:IIO
2460:RCU
2440:DRM
2235:BPF
2100:Tux
1791:NPF
1766:BSD
1089:API
994:SYN
987:SYN
983:ACK
975:SYN
817:FTP
768:FTP
742:NEW
714:GRE
706:UDP
627:ABI
591:nft
529:NAT
497:raw
302:NAT
293:'s
291:BSD
258:in
3308::
2876::
1796:PF
1409:.
1345:.
1333:^
1321:.
1301:.
1284:,
1274:^
908:.
731:.
708:,
609:.
601:,
597:,
454:,
435:,
431:,
418:,
414:,
308:,
172:,
2821::
2495:,
2406:…
2366:…
2051:e
2044:t
2037:v
1588:e
1581:t
1574:v
1552:"
1545:"
1503:.
1482:.
1461:.
1440:.
1419:.
1394:.
1373:.
1355:.
1327:.
1307:.
1268:.
1247:.
1107:.
770:"
84:C
69:)
37:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.