167:. Word processing formats may save a revision history of the edited text that still contains the redacted text. In some file formats, unused portions of memory are saved that may still contain fragments of previous versions of the text. Where text is redacted, in Portable Document (PDF) or word processor formats, by overlaying graphical elements (usually black rectangles) over text, the original text remains in the file and can be uncovered by simply deleting the overlaying graphics. Effective redaction of electronic documents requires the removal of all relevant text and image data from the document file. This process, internally complex, can be carried out very easily by a user with the aid of "redaction" functions in software for editing PDF or other files.
357:
underneath the visible appearance and is subject to searching and even simple copy and paste extraction. Proper redaction tools and procedures must be used to permanently remove the sensitive information. This is often accomplished in a multi-user workflow where one group of people mark sections of the document as proposals to be redacted, another group verifies the redaction proposals are correct, and a final group operates the redaction tool to permanently remove the proposed items.
187:
1164:
105:
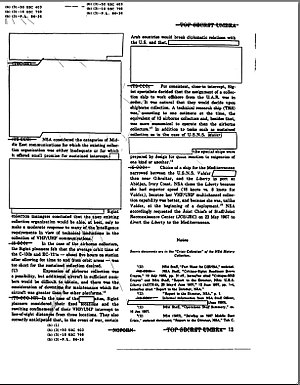
216:, which was declassified and released to the public in July 2003. Classified information has been blocked out so that only the unclassified information is visible. Notations with leader lines at top and bottom cite statutory authority for not declassifying certain sections. Click on the image to enlarge.
324:, an Italian secret agent, at a US military checkpoint in Iraq. The published version of the report was in PDF format, and had been incorrectly redacted by covering sensitive parts with opaque blocks in software. Shortly thereafter, readers discovered that the blocked-out portions could be retrieved by
356:
The two most common mistakes for incorrectly redacting a document are adding an image layer over the sensitive text to obscure it, without removing the underlying text, and setting the background color to match the text color. In both of these cases, the redacted material still exists in the document
148:
This is a simple process with only minor security risks. For example, if the black pen or tape is not wide enough, careful examination of the resulting photocopy may still reveal partial information about the text, such as the difference between short and tall letters. The exact length of the removed
312:
will sometimes be used to edit out the sensitive information. These products do not always show the user all of the information stored in a file, so it is possible that a file may still contain sensitive information. In other cases, inexperienced users use ineffective methods which fail to sanitize
149:
text also remains recognizable, which may help in guessing plausible wordings for shorter redacted sections. Where computer-generated proportional fonts were used, even more information can leak out of the redacted section in the form of the exact position of nearby visible characters.
170:
Redaction may administratively require marking of the redacted area with the reason that the content is being restricted. US government documents released under the
Freedom of Information Act are marked with exemption codes that denote the reason why the content has been withheld.
225:
personnel. The printed document will consequently be sanitized to obscure or remove the sensitive information. Maps have also been redacted for the same reason, with highly sensitive areas covered with a slip of white paper.
91:
In the context of government documents, redaction (also called sanitization) generally refers more specifically to the process of removing sensitive or classified information from a document prior to its publication, during
1063:
220:
Printed documents which contain classified or sensitive information frequently contain a great deal of information which is less sensitive. There may be a need to release the less sensitive portions to
237:, that is removed before the reports are distributed outside the intelligence agency: the initial report may be classified as Top Secret while the sanitized report may be classified as Secret.
48:
from a document so that it may be distributed to a broader audience. It is intended to allow the selective disclosure of information. Typically, the result is a document that is suitable for
273:
Computer (electronic or digital) documents are more difficult to sanitize. In many cases, when information in an information system is modified or erased, some or all of the data remains in
125:
339:
regarding their cooperation with domestic wiretapping by the NSA. Text on pages 12 to 14 of the PDF document were incorrectly redacted, and the covered text could be retrieved.
229:
In some cases, sanitizing a classified document removes enough information to reduce the classification from a higher level to a lower one. For example, raw
17:
507:
137:
Redacting confidential material from a paper document before its public release involves overwriting portions of text with a wide black pen, followed by
1183:
130:
1058:
898:
456:
141:
the result—the obscured text may be recoverable from the original. Alternatively opaque "cover up tape" or "redaction tape", opaque, removable
1146:
492:
63:, redaction attempts to reduce the document's classification level, possibly yielding an unclassified document. When the intent is
255:
report, paper documents are usually sanitized by covering the classified and sensitive portions before photocopying the document.
575:
1096:
381:
716:
1046:
883:
733:
248:(right), the report may be sanitized to remove all sensitive data, so that the report may be released to the general public.
405:
622:
342:
At the end of 2005, the NSA released a report giving recommendations on how to safely sanitize a
Microsoft Word document.
650:
290:
786:
511:
201:
353:
gives an example of a sanitization failure caused by unexpected behavior in
Microsoft Word's change tracking feature.
908:
674:
533:
1208:
285:, etc.) still allows information to be read, despite its nominal erasure. The general term for this problem is
1218:
1167:
1151:
195:
1053:
1116:
706:
293:, and related organizations), "sanitization" typically refers to countering the data remanence problem.
1089:
31:
985:
920:
781:
297:
560:
467:
1193:
791:
615:
406:
Redaction
Toolkit, Guidelines for the Editing of Exempt Information from Documents Prior to Release
175:
158:
Redaction
Toolkit, Guidelines for the Editing of Exempt Information from Documents Prior to Release
160:, "to provide guidance on the editing of exempt material from information held by public bodies."
142:
45:
1213:
980:
956:
878:
527:"Redacting with Confidence: How to Safely Publish Sanitized Reports Converted From Word to PDF"
191:
153:
60:
317:
are designed to effectively sanitize documents by removing potentially sensitive information.
1082:
1041:
776:
728:
711:
547:
314:
230:
1015:
1005:
1000:
961:
946:
818:
691:
662:
532:. Report# I333-015R-2005. Information Assurance Directorate, National Security Agency, via
386:
325:
282:
241:
209:
52:
or for dissemination to others rather than the intended audience of the original document.
417:
8:
951:
669:
608:
584:
346:
178:(NSA) published a guidance document which provides instructions for redacting PDF files.
995:
973:
723:
349:
systems, in which computer users of differing security clearances may share documents.
222:
68:
588:
442:
913:
848:
833:
796:
701:
686:
526:
486:
1010:
681:
274:
93:
941:
888:
863:
853:
838:
771:
761:
657:
645:
321:
205:
113:
1141:
1126:
376:
309:
286:
264:
80:
1202:
1136:
1131:
1121:
1025:
696:
277:. This may be an accident of design, where the underlying storage mechanism (
164:
109:
76:
199:
1105:
903:
858:
756:
751:
371:
278:
268:
124:
968:
893:
843:
813:
806:
766:
336:
138:
75:
was applied to printed documents; it has since been extended to apply to
49:
990:
925:
868:
631:
366:
186:
823:
801:
234:
233:
may contain highly classified information such as the identities of
27:
Removing sensitive information from a document to allow distribution
104:
1020:
828:
332:
331:
On May 24, 2006, lawyers for the communications service provider
194:
that has been sanitized for public release. This is page 13 of a
64:
56:
128:
A heavily redacted page from a 2004 lawsuit filed by the ACLU —
1074:
320:
In May 2005 the US military published a report on the death of
305:
873:
600:
427:. National Security Agency Information Assurance Directorate.
345:
Issues such as these make it difficult to reliably implement
418:"Redaction of PDF Files Using Adobe Acrobat Professional X"
301:
308:, or the like. For example, word processing programs like
438:
145:
in various widths, may be applied before photocopying.
99:
1188:from Vol. 58 No. 2, May 2019, Technology column of
1200:
505:
240:In other cases, such as the NSA report on the
1090:
616:
508:"AT&T leaks sensitive info in NSA suit"
296:However, the retention may be a deliberate
258:
1163:
1097:
1083:
623:
609:
573:
437:
163:Secure redacting is more complicated with
131:American Civil Liberties Union v. Ashcroft
524:
289:. In some contexts (notably the US NSA,
185:
123:
103:
304:buffer, revision history, "trash can",
14:
1201:
491:: CS1 maint: archived copy as title (
382:Freedom of information laws by country
1078:
604:
86:
18:Sanitization (classified information)
577:The Challenge of Multilevel Security
351:The Challenge of Multilevel Security
100:Secure document redaction techniques
24:
587:Federal Conference. Archived from
443:"Readers 'declassify' US document"
25:
1230:
1177:
534:Federation of American Scientists
506:Declan McCullagh (May 26, 2006).
181:
1162:
1104:
1185:Embarrassing Redaction Failures
630:
567:
525:NSA SNAC (December 13, 2005).
518:
499:
449:
431:
410:
398:
13:
1:
1168:List of data-erasing software
1152:Physical information security
392:
196:U.S. National Security Agency
425:Security Configuration Guide
328:them into a word processor.
7:
510:. CNet News. Archived from
360:
44:is the process of removing
10:
1235:
262:
59:, such as in dealing with
32:Redaction (disambiguation)
29:
1160:
1112:
1034:
934:
744:
638:
1194:American Bar Association
792:Content-control software
259:Computer media and files
176:National Security Agency
1117:Anti–computer forensics
1047:Chinese issues overseas
71:. Originally, the term
1209:Classified information
1021:Suppression of dissent
555:Cite journal requires
441:Report (May 2, 2005).
315:Metadata removal tools
251:As is seen in the USS
217:
156:published a document,
134:
121:
61:classified information
787:Conspiracy of silence
777:Collateral censorship
702:Speech and expression
189:
127:
107:
67:, it is often called
46:sensitive information
1219:Classified documents
1064:Muhammad controversy
1001:Naturalistic fallacy
909:computer and network
300:, in the form of an
231:intelligence reports
154:UK National Archives
30:For other uses, see
1190:The Judges' Journal
1059:Internet censorship
574:Rick Smith (2003).
464:www.politechbot.com
347:multilevel security
326:copying and pasting
192:classified document
79:and the problem of
55:When the intent is
996:Moralistic fallacy
734:banned video games
717:banned televisions
218:
204:2004-03-13 at the
135:
122:
87:Government secrecy
69:data anonymization
65:privacy protection
57:secrecy protection
1192:published by the
1174:
1173:
1072:
1071:
1054:Freedom of speech
899:Strategic lawsuit
849:National intranet
797:Damnatio memoriae
514:on July 17, 2012.
120:prior to release.
16:(Redirected from
1226:
1166:
1165:
1099:
1092:
1085:
1076:
1075:
1011:Propaganda model
639:Media regulation
625:
618:
611:
602:
601:
596:
595:
593:
582:
571:
565:
564:
558:
553:
551:
543:
541:
540:
531:
522:
516:
515:
503:
497:
496:
490:
482:
480:
478:
472:
466:. Archived from
461:
453:
447:
446:
435:
429:
428:
422:
414:
408:
402:
94:declassification
21:
1234:
1233:
1229:
1228:
1227:
1225:
1224:
1223:
1199:
1198:
1180:
1175:
1170:
1156:
1108:
1103:
1073:
1068:
1030:
930:
889:Self-censorship
864:Prior restraint
854:Newspaper theft
839:Internet police
772:Chilling effect
762:Broadcast delay
740:
634:
629:
599:
591:
580:
572:
568:
556:
554:
545:
544:
538:
536:
529:
523:
519:
504:
500:
484:
483:
476:
474:
470:
459:
457:"Archived copy"
455:
454:
450:
436:
432:
420:
416:
415:
411:
403:
399:
395:
363:
322:Nicola Calipari
271:
261:
206:Wayback Machine
184:
114:Project MKUltra
102:
89:
35:
28:
23:
22:
15:
12:
11:
5:
1232:
1222:
1221:
1216:
1211:
1197:
1196:
1179:
1178:External links
1176:
1172:
1171:
1161:
1158:
1157:
1155:
1154:
1149:
1144:
1142:Gutmann method
1139:
1134:
1129:
1127:Data remanence
1124:
1119:
1113:
1110:
1109:
1102:
1101:
1094:
1087:
1079:
1070:
1069:
1067:
1066:
1061:
1056:
1051:
1050:
1049:
1038:
1036:
1032:
1031:
1029:
1028:
1023:
1018:
1013:
1008:
1003:
998:
993:
988:
983:
978:
977:
976:
966:
965:
964:
959:
954:
944:
938:
936:
932:
931:
929:
928:
926:Word filtering
923:
918:
917:
916:
911:
901:
896:
891:
886:
881:
876:
871:
866:
861:
856:
851:
846:
841:
836:
834:Heckler's veto
831:
826:
821:
816:
811:
810:
809:
799:
794:
789:
784:
779:
774:
769:
764:
759:
754:
748:
746:
742:
741:
739:
738:
737:
736:
726:
721:
720:
719:
709:
704:
699:
694:
689:
684:
679:
678:
677:
667:
666:
665:
655:
654:
653:
642:
640:
636:
635:
628:
627:
620:
613:
605:
598:
597:
594:on 2009-01-06.
566:
557:|journal=
517:
498:
473:on 2 July 2006
448:
430:
409:
396:
394:
391:
390:
389:
384:
379:
377:Data remanence
374:
369:
362:
359:
313:the document.
310:Microsoft Word
287:data remanence
265:Data remanence
260:
257:
183:
182:Printed matter
180:
165:computer files
116:that has been
101:
98:
88:
85:
81:data remanence
77:computer files
26:
9:
6:
4:
3:
2:
1231:
1220:
1217:
1215:
1214:Data security
1212:
1210:
1207:
1206:
1204:
1195:
1191:
1187:
1186:
1182:
1181:
1169:
1159:
1153:
1150:
1148:
1147:DoD 5220.22-M
1145:
1143:
1140:
1138:
1137:File deletion
1135:
1133:
1132:Factory reset
1130:
1128:
1125:
1123:
1122:Data recovery
1120:
1118:
1115:
1114:
1111:
1107:
1100:
1095:
1093:
1088:
1086:
1081:
1080:
1077:
1065:
1062:
1060:
1057:
1055:
1052:
1048:
1045:
1044:
1043:
1040:
1039:
1037:
1033:
1027:
1026:Systemic bias
1024:
1022:
1019:
1017:
1014:
1012:
1009:
1007:
1004:
1002:
999:
997:
994:
992:
989:
987:
984:
982:
979:
975:
972:
971:
970:
967:
963:
960:
958:
955:
953:
950:
949:
948:
945:
943:
940:
939:
937:
933:
927:
924:
922:
919:
915:
912:
910:
907:
906:
905:
902:
900:
897:
895:
892:
890:
887:
885:
882:
880:
877:
875:
872:
870:
867:
865:
862:
860:
857:
855:
852:
850:
847:
845:
842:
840:
837:
835:
832:
830:
827:
825:
822:
820:
817:
815:
812:
808:
805:
804:
803:
800:
798:
795:
793:
790:
788:
785:
783:
780:
778:
775:
773:
770:
768:
765:
763:
760:
758:
755:
753:
750:
749:
747:
743:
735:
732:
731:
730:
727:
725:
722:
718:
715:
714:
713:
710:
708:
707:Student media
705:
703:
700:
698:
695:
693:
690:
688:
685:
683:
680:
676:
675:circumvention
673:
672:
671:
668:
664:
661:
660:
659:
656:
652:
649:
648:
647:
644:
643:
641:
637:
633:
626:
621:
619:
614:
612:
607:
606:
603:
590:
586:
579:
578:
570:
562:
549:
535:
528:
521:
513:
509:
502:
494:
488:
469:
465:
458:
452:
444:
440:
434:
426:
419:
413:
407:
401:
397:
388:
385:
383:
380:
378:
375:
373:
370:
368:
365:
364:
358:
354:
352:
348:
343:
340:
338:
334:
329:
327:
323:
318:
316:
311:
307:
303:
299:
294:
292:
288:
284:
280:
276:
270:
266:
256:
254:
249:
247:
245:
238:
236:
232:
227:
224:
215:
213:
207:
203:
200:
197:
193:
188:
179:
177:
172:
168:
166:
161:
159:
155:
150:
146:
144:
143:adhesive tape
140:
133:
132:
126:
119:
115:
111:
110:US government
106:
97:
95:
84:
82:
78:
74:
70:
66:
62:
58:
53:
51:
47:
43:
39:
33:
19:
1189:
1184:
1106:Data erasure
921:Whitewashing
904:Surveillance
884:Sanitization
859:Pixelization
757:Book burning
663:banned films
651:books banned
589:the original
576:
569:
548:cite journal
537:. Retrieved
520:
512:the original
501:
475:. Retrieved
468:the original
463:
451:
433:
424:
412:
400:
372:Data erasure
355:
350:
344:
341:
330:
319:
295:
272:
269:Data erasure
252:
250:
243:
239:
228:
219:
211:
190:A page of a
173:
169:
162:
157:
151:
147:
139:photocopying
136:
129:
117:
112:document on
90:
73:sanitization
72:
54:
42:sanitization
41:
37:
36:
986:LGBT issues
981:Ideological
969:Hate speech
894:Speech code
879:Revisionism
844:Memory hole
814:Expurgation
807:Minced oath
767:Censor bars
729:Video games
712:Televisions
337:legal brief
50:publication
1203:Categories
1042:Censorship
1035:By country
991:Media bias
869:Propaganda
632:Censorship
539:2006-05-29
477:14 January
393:References
367:Censorship
263:See also:
1016:Religious
947:Corporate
824:Gag order
802:Euphemism
782:Concision
585:Black Hat
223:uncleared
38:Redaction
1006:Politics
957:Facebook
942:Criminal
935:Contexts
829:Heckling
752:Bleeping
670:Internet
487:cite web
361:See also
335:filed a
333:AT&T
246:incident
214:incident
202:Archived
118:redacted
819:Fogging
745:Methods
724:Thought
306:backups
298:feature
275:storage
253:Liberty
244:Liberty
212:Liberty
208:on the
198:report
174:The US
108:A 1953
974:Online
962:Google
687:Postal
445:. BBC.
387:Lacuna
952:Apple
874:Purge
697:Radio
692:Press
682:Music
658:Films
646:Books
592:(PDF)
581:(PDF)
530:(PDF)
471:(PDF)
460:(PDF)
421:(PDF)
235:spies
914:mass
561:help
493:link
479:2022
302:undo
279:disk
267:and
242:USS
210:USS
152:The
439:BBC
291:DoD
283:RAM
40:or
1205::
583:.
552::
550:}}
546:{{
489:}}
485:{{
462:.
423:.
281:,
96:.
83:.
1098:e
1091:t
1084:v
624:e
617:t
610:v
563:)
559:(
542:.
495:)
481:.
404:'
34:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.